As of 2016, there are approximately 1.85 billion Android smartphones worldwide. This growing popularity has led to an increasing number hacks and cyber attacks against the OS. Unfortunately, Android users need more protection than what is offered by Google. The good thing is that there are a number of options available.

BlackBerry's focus on secure software and their new partnership with manufacturer TCL are two of the biggest factors in their recent resurgence. Last year, the company announced two new devices — the KEYone and the BlackBerry Motion. The KEYone has been available for a while, but after months of waiting, BlackBerry announced the Motion will hit US shores in a few days.
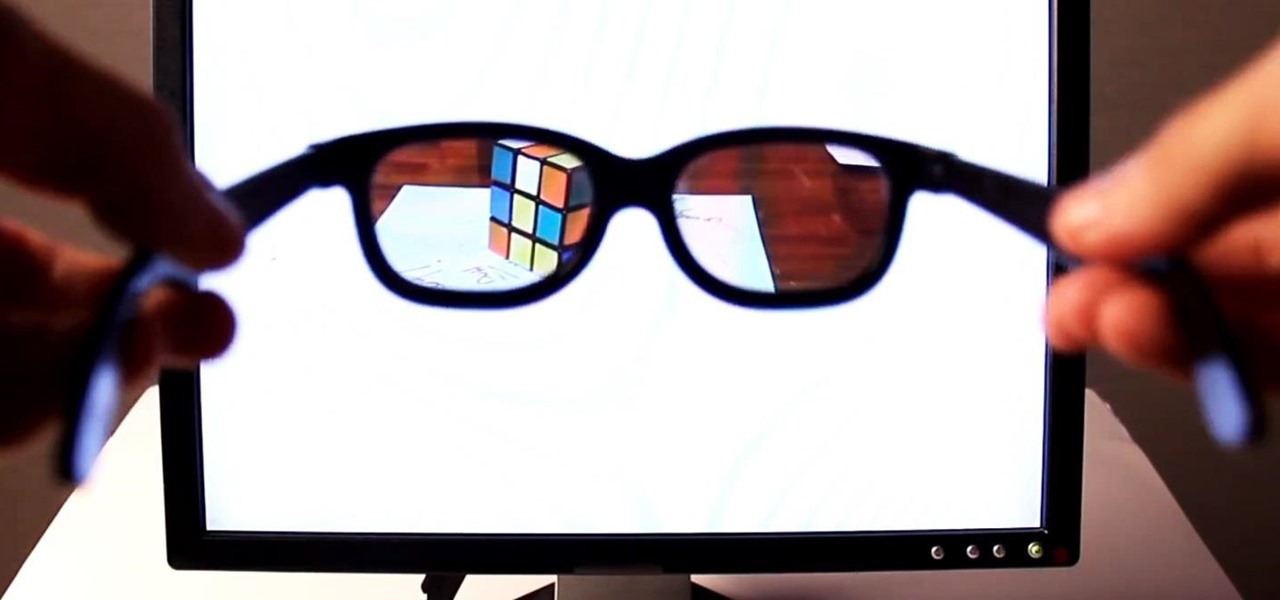
When it comes to making smartglasses that look more like regular eyeglasses and less like sci-fi helmets, Corning International might be among the suppliers to make it happen.

Apple's codec for photos and videos in iOS 11, HEVC (High-Efficiency Video Coding), as well as the container, HEIF (High-Efficiency Image File Format), result in a reduction in size for pictures and movies without sacrificing quality. Seems like a win-win situation, but Windows-users can't open the .heic extension that these files use. In order to open HEIC files on a Microsoft Windows PC, you'll have to turn to third-party apps and tools. One of these tools, CopyTrans HEIC for Windows, essen...

While Snap's third quarter financial reports disappointed Wall Street, China's Tencent took the opportunity to expand its investment in the social media company.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

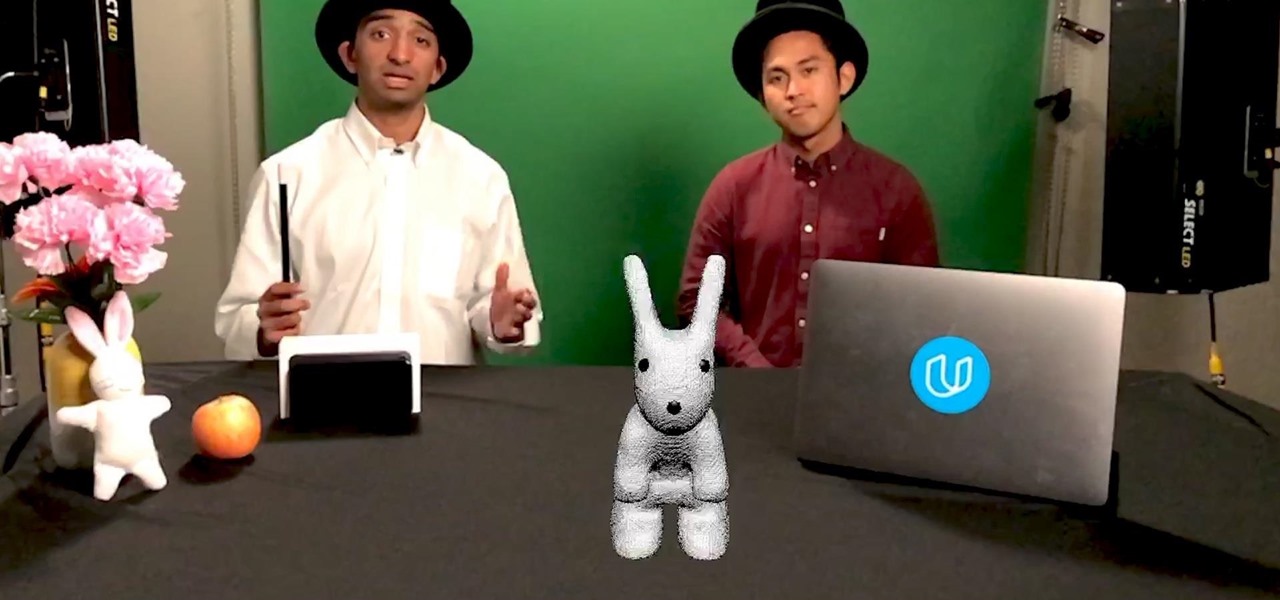
As demand for AR and VR developers continues to increase, particularly with the advent of Apple's ARKit platform, Unity has partnered with online learning company Udacity to help developers sharpen their skills for these jobs.

Apple has billed ARKit as a means to turn millions of iPhones and iPads into augmented reality devices. The refrain is similar for Kaon Interactive, a developer of product catalog apps for businesses.

It seems like it was just last week that AMC and Next Games unveiled their location-based zombie game based on hit TV series The Walking Dead. (Wait, actually it was just last week.)

Think you're a true Star Wars fan? I bet you haven't created a demo using Apple's ARKit that creates a map of the entire Star Wars galaxy. How's that for being a fanatic?

Verizon will be exclusively selling the ASUS ZenFone AR, which supports Tango (Google's mobile AR platform) and Daydream VR.

People fear virtual reality will isolate us, but the right experience can prove it does the opposite.

Microsoft began shipping the Development Edition of its much-anticipated HoloLens—the world's first untethered holographic computer—back in March. As the name implies, it was only available to developers (we got ours near the end of April), but Microsoft has recently opened up the program to anyone who wants one—not just developers.

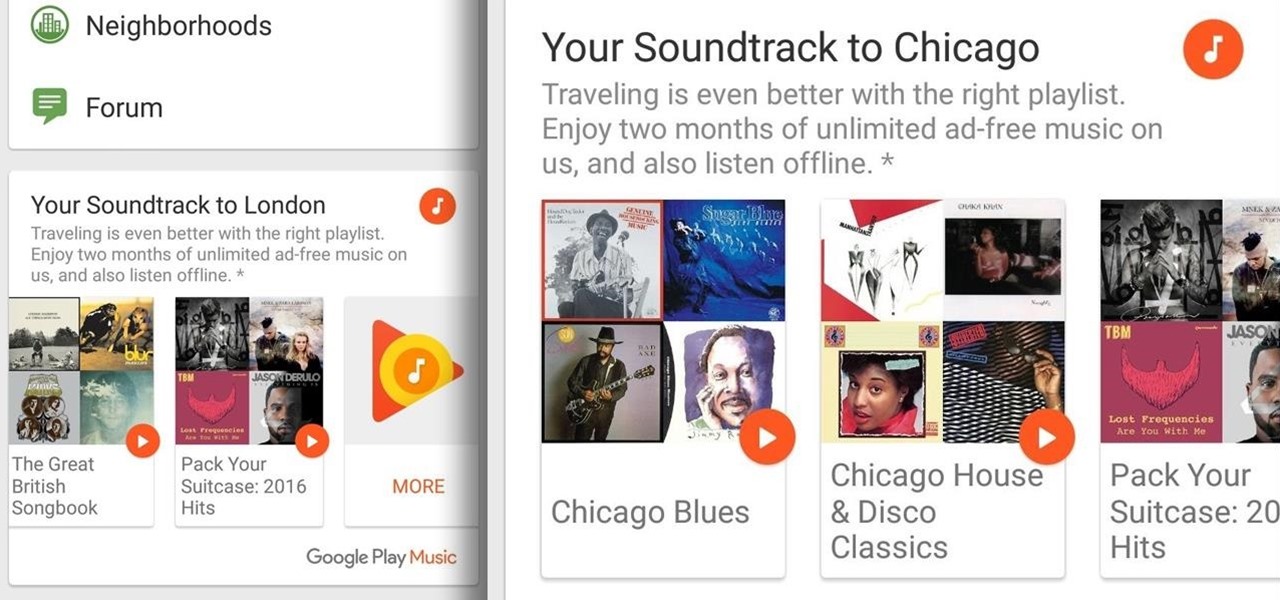
Google Play Music has teamed up with TripAdvisor to make planning your next vacation a little more fun, and they're throwing in a nice deal for good measure.

A lot more people are about to be able to use Android Auto. Google announced at I/O 2016 that you'll soon be able to use the app with only your phone, so you won't need a compatible car or third-party display unit. And if (or more likely, when) Google brings the app to iOS, Apple may lose the precious "infotainment" system battle very early in the game. The update isn't coming until later this year, but once it arrives, you'll be able to mount your phone and use Android Auto the same way that...

This tutorial was written with Windows 7 in mind, but the principle applies to all versions starting from 7.

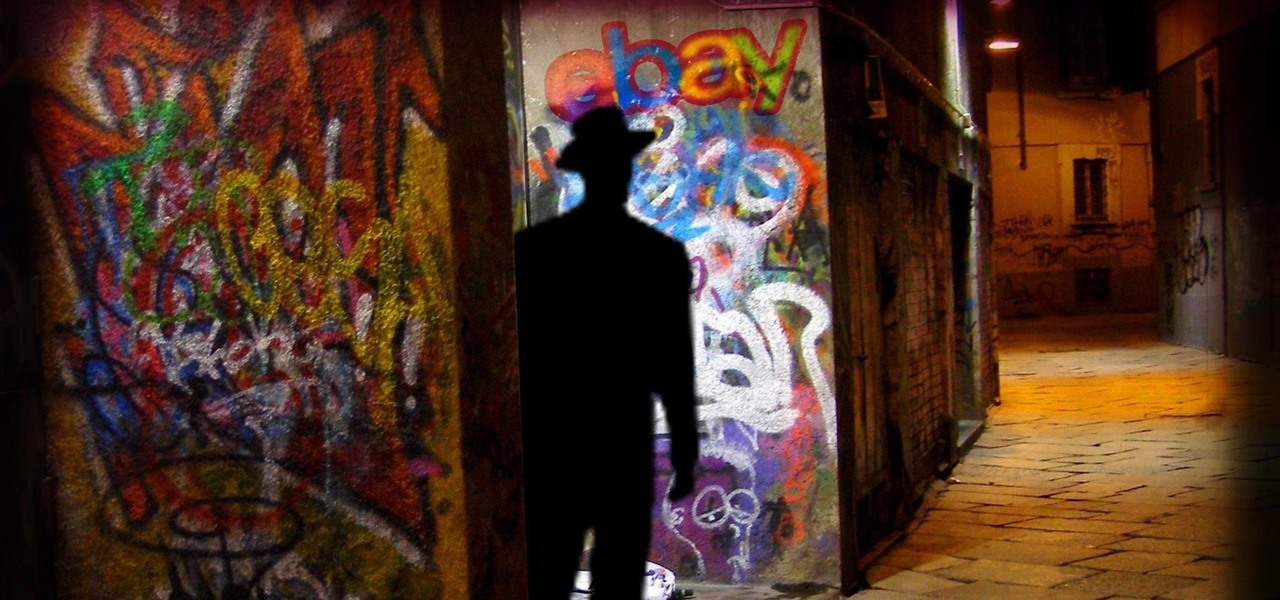
Researchers have discovered a "severe vulnerability" that allows attackers to use eBay to distribute malware, and the online auction company has no plans to fix the problem.

to stay secure, you dont just need Tor, and a VPN. You need good browsing habits. What are Browsing Habits You Ask?

INTRODUCTION Hello dear null_byters here we go again with our third part of this serie.

Paying for someone to get a small dent out of your car can be expensive, especially when you realize that you can just do it yourself. If you've got a bathroom—and you probably do—then it's a surefire bet that you've also got a plunger.

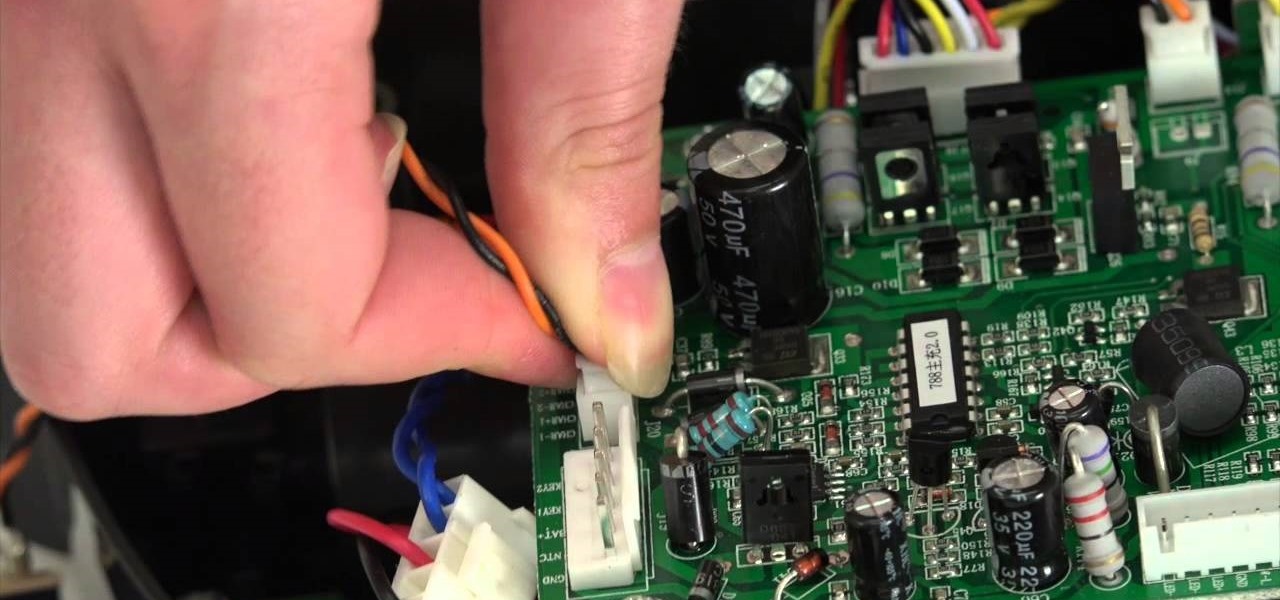
The guide will walk you through a power switch replacement on a bObsweep Standard or Pethair. It includes:

Welcome back, my rookie hackers! In my ongoing attempts to familiarize aspiring hackers with Linux (nearly all hacking is done with Linux, and here's why every hacker should know and use it), I want to address a rather obscure, but powerful process. There is one super process that is called inetd or xinetd or rlinetd. I know, I know... that's confusing, but bear with me.

Welcome back, my rookie hackers! As hackers, we are often faced with the hurdle of cryptography and encryption. In some cases, we use it to hide our actions and messages. Many applications and protocols use encryption to maintain confidentiality and integrity of data. To be able to crack passwords and encrypted protocols such as SSL and wireless, you need to at least be familiar with the concepts and terminology of cryptography and encryption.

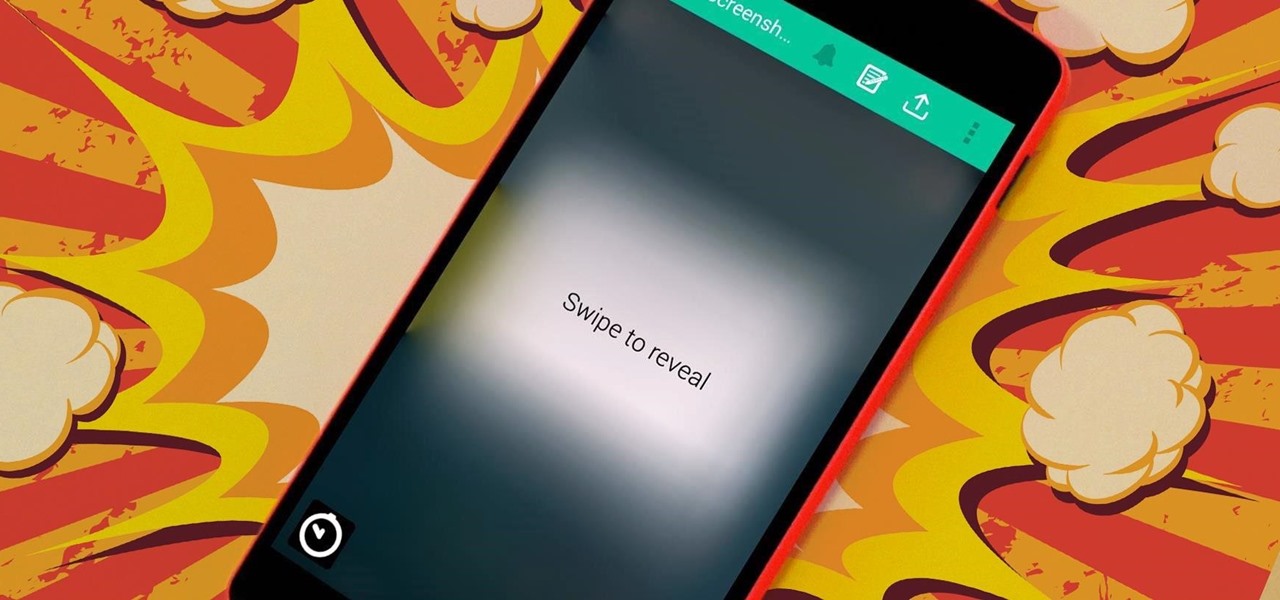
The internet is forever. When you put something out there, it can easily be re-shared, floating from server to server indefinitely with no way of taking it back. It's a scary thought when you consider that a young adult's grandchildren will one day have access to their drunken party pics.

While stickers have long existed in the messages section of Facebook, they've only just recently rolled out sticker capability in comments for events, groups, and timeline posts. That means you can now reply with a cute sticker of a cat eating a slice of pizza on someone's status instead or writing something more thoughtful. While an animated sticker can show off enthusiasm and excitement that words or a too-simple emoji may not be able to convey, you can bet that your comment section will qu...

As great as the Internet is, it is not without its dangers. Hackers at any time may be breaking into your online accounts and compromising your sensitive information. Last year, hackers broke into Facebook, Gmail, and Twitter and made off with 2 million stolen passwords.

With all of the personal data that's stored on our smartphones, it's of vital importance that we have some sort of lock screen security enabled. One of the Galaxy S5's killer features is obviously the fingerprint scanner. It makes the process of dealing with a secure lock screen a bit easier than typing in a password or PIN.

After months of waiting, Google has released the SDK (Software Development Kit) for their Gadget of the Year, the Chromecast. As announced on their blog, the release of the SDK means that any app developer, whether for Android, Chrome, or iOS, can now add Chromecast functionality to their app. And though only a few apps have been released with Chromecast support, that's all about to change.

Welcome back, my rookie hackers! The more we know about a system or network, the better our chances of owning it and not leaving a trace for investigators to follow. One of the often overlooked sources for information is the Simple Network Management Protocol (SNMP). Many rookie hackers are not even aware of it, but it can prove to be a treasure trove of information, if you understand how it works and how to hack it.

No matter your reason, if you want to hide what's on your computer screen from prying eyes, there are plenty of ways to do it. You can get a privacy filter, install a panic button for your browser, or just develop super fast reflexes. But all it takes is the right angle or a too-slow reaction to blow your cover.

Ever since the FBI took down the Silk Road and Dread Pirate Roberts last month, many questions have been raised about whether Tor still provides anonymity or not, and if it's now broken. I'll try to address that question here today succinctly from multiple angles, keeping it as simple and plain-language as possible. The Closing of Silk Road

Having your phone ring loudly in a quiet environment could be potentially embarrassing for you, but also quite annoying for everyone else that didn't forget to put their smartphone on silent. Whether it's in class, at work during a meeting, at the library, or a movie screening—you can bet that someone's phone is going to ring loudly, pissing some people off. You don't really want to be that douchebag that interrupts a movie or the middle of a lecture with their annoying ringtone just because ...

You know that guy who does the cheesy card trick to get the attention of all the girls at the party? Well, we kinda hate that guy don't we? But, if we could be that guy, it might not be so bad.

There's nothing worse than that feeling when you realize you've forgotten something important. Maybe you left an assignment sitting on your desk at home, or forgot to log out of your accounts on the shared family computer.

There are plenty of ways to take double exposure photos, even if all you have is your cell phone. If you have access to a darkroom (or Photoshop), you can do it by stacking negatives. But if you have the right kind of DSLR, you can do it right from your camera by using the multiple exposure setting.

AirPlay is probably one of the most underutilized features in Apple products. It allows users to wirelessly stream photos, music, or video directly from their iPad, iPhone, iPod touch or Mac to their Apple TV or AirPlay-supported speakers. The Apple support page has a complete list of all the supported and needed devices. Mirroring is also available, but only for the iPhone 4S, iPhone 5, and iPad 2, all of which need to be running iOS 5 or later.

Admit it—at some point or another, you've wished that you had your own personal hovercraft. Don't worry, we've all been there. Well, a company called Aerofex wants to make a hovercraft that's way more than your standard leaf-blower-powered one, taking a queue from the swoop and speeder bikes from the Star Wars franchise, building their own sort of repulsorlift. This hover bike may not be quite as fast as the ones from Star Wars, but if the company has its way, it could be on sale by the end o...

André Broessel of rawlemon has developed a solar energy generator that can use both sun and moonlight to create usable power. Oh... and it's gorgeous. The device is essentially a huge glass sphere filled with water that uses a ball lens to refract light in a way that increases energy efficiency by 35 percent. It's completely weatherproof and has an optical tracking device, meaning that it can be incorporated into architecture. Here's a concept design of how it could be used to power buildings...

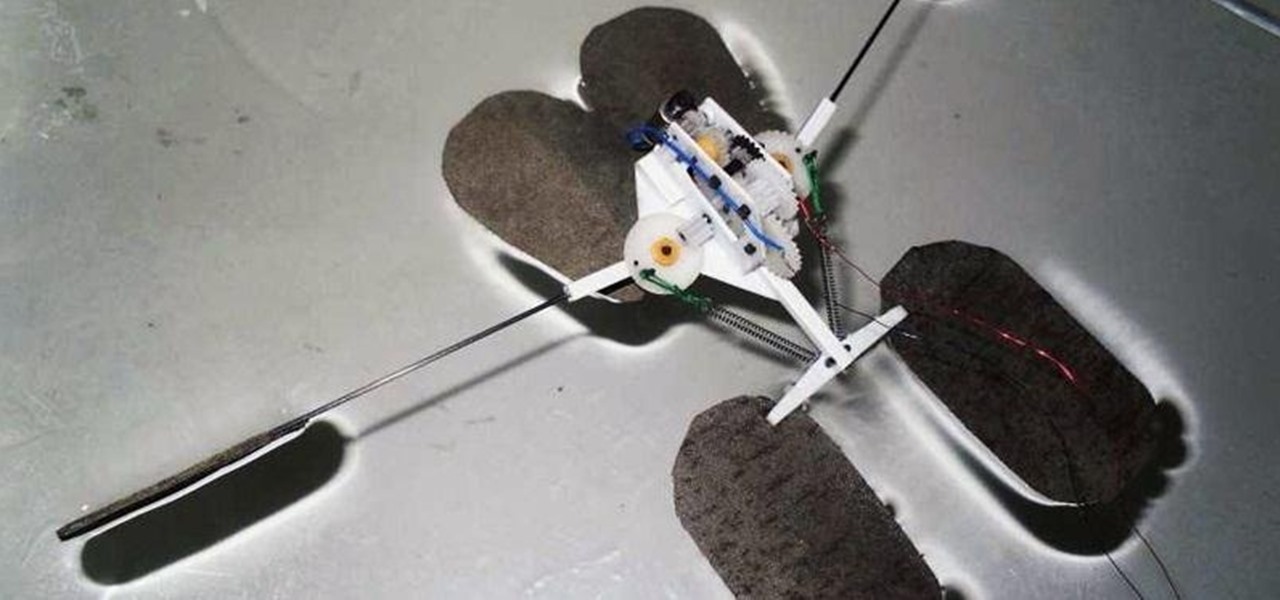
Gerridae—you've probably seen these weird bugs gliding across the surface of the water when you're out swimming or fishing. These insects are commonly referred to as water striders, or more cleverly, Jesus bugs, for their ability to "walk on water". It's a pretty cool trick, but what could it do for science, right? Turns out, quite a bit. Photo by felixtsao

Unless you're living in some weird parallel universe where plug-in light bulbs are the norm for household lighting, chances are you've had to unscrew a light bulb every now and then.