One of the best-received features of the OnePlus 5T was the relatively secure face unlock, which made it quick and easy to get into the phone. Unfortunately, this feature wasn't included with the slightly older OnePlus 5 at first, but now, face unlocking is finally out of beta and available to everyone with a 2017 OnePlus.
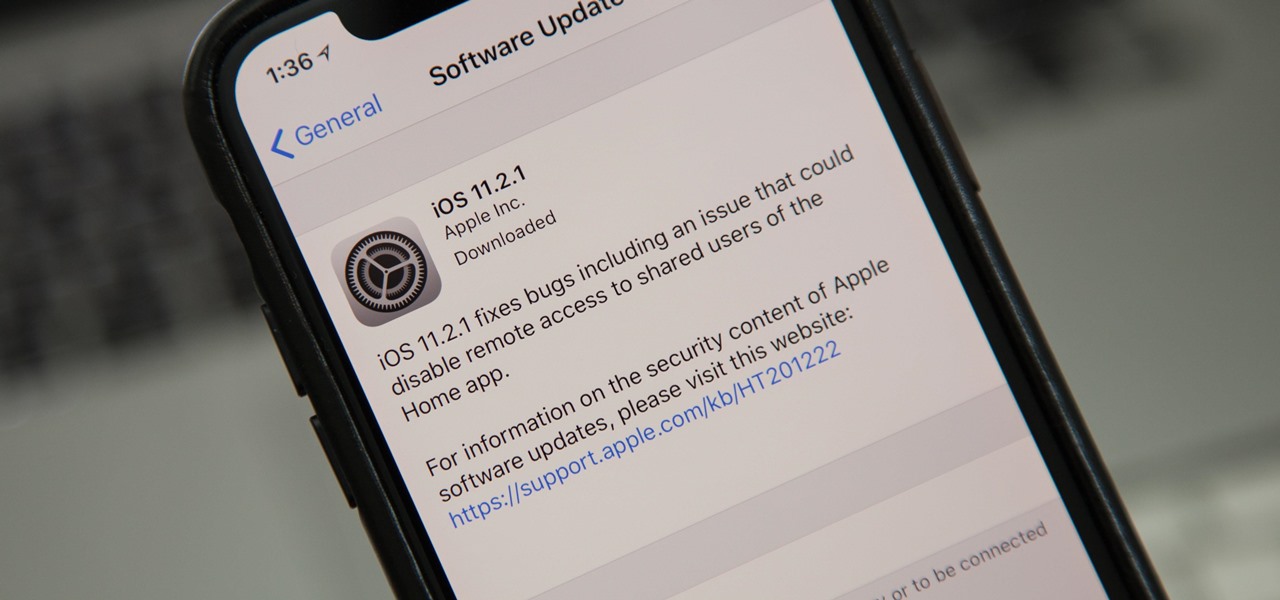
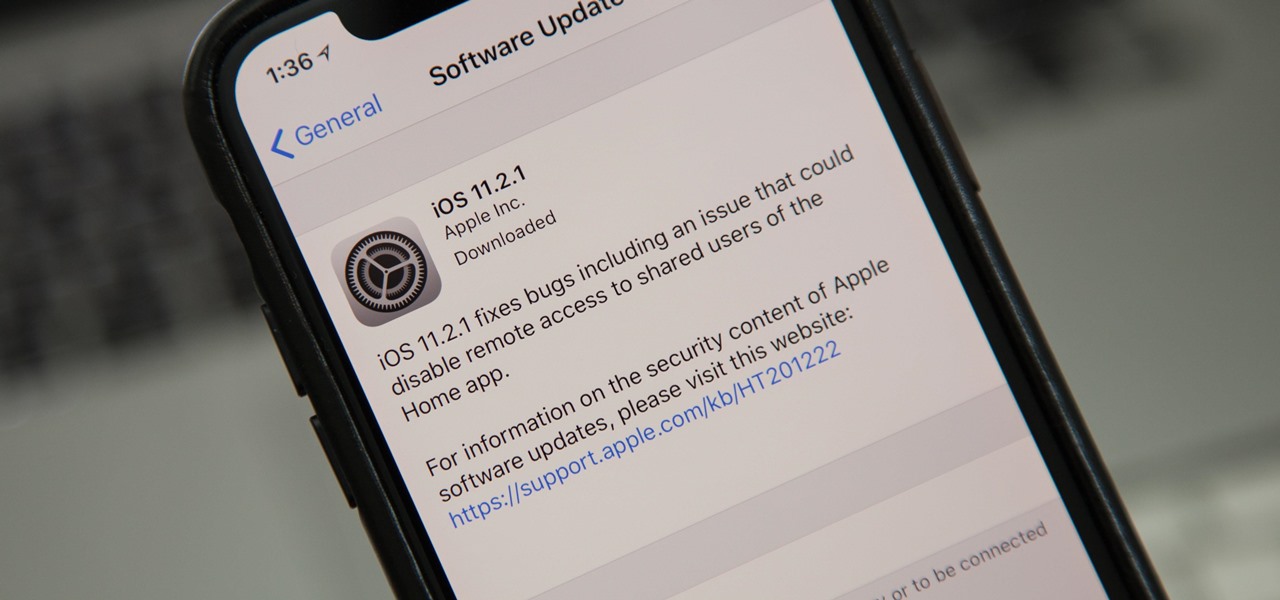
Just nine days after the official release of iOS 11.2, Apple has released iOS 11.2.1. The update initially seems to have been seeded to only a handful of users and is intended to fix bugs in 11.2.

Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.

When we are building programs that communicate over a network, how can we keep our data private? The last thing we want is some other lousy hacker sniffing our packets, so how do we stop them? The easy answer: encryption. However, this is a very wide-ranging answer. Today we're going to look specifically at how to encrypt data in Python with dynamically generated encryption keys using what is known as the Diffie-Hellman key exchange.
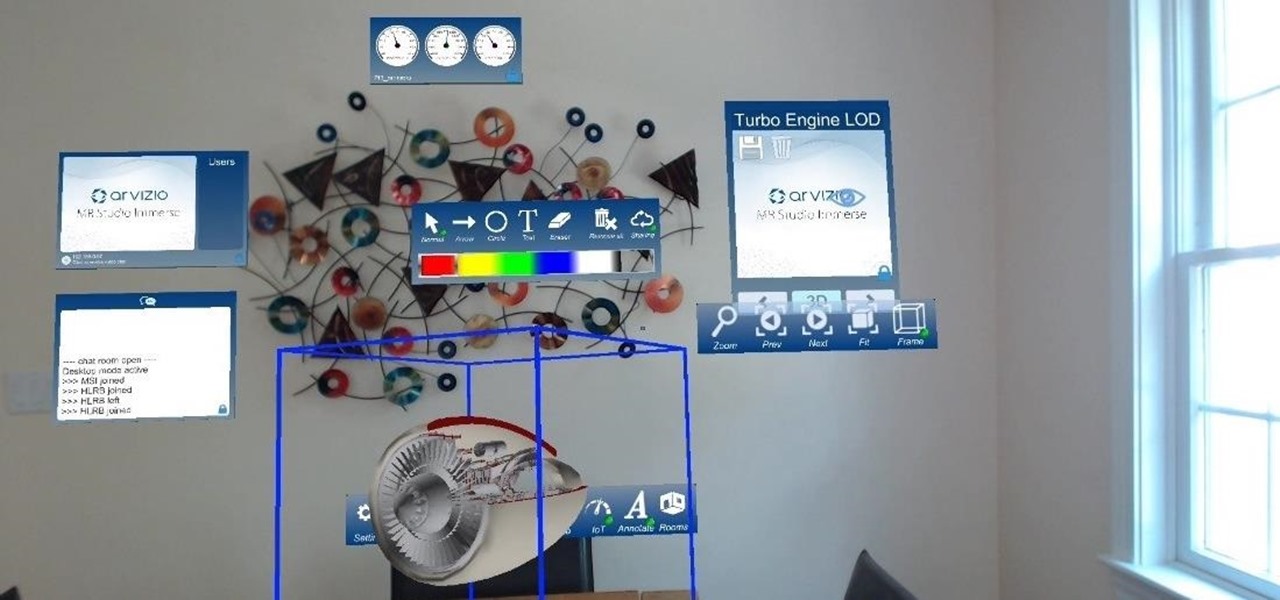
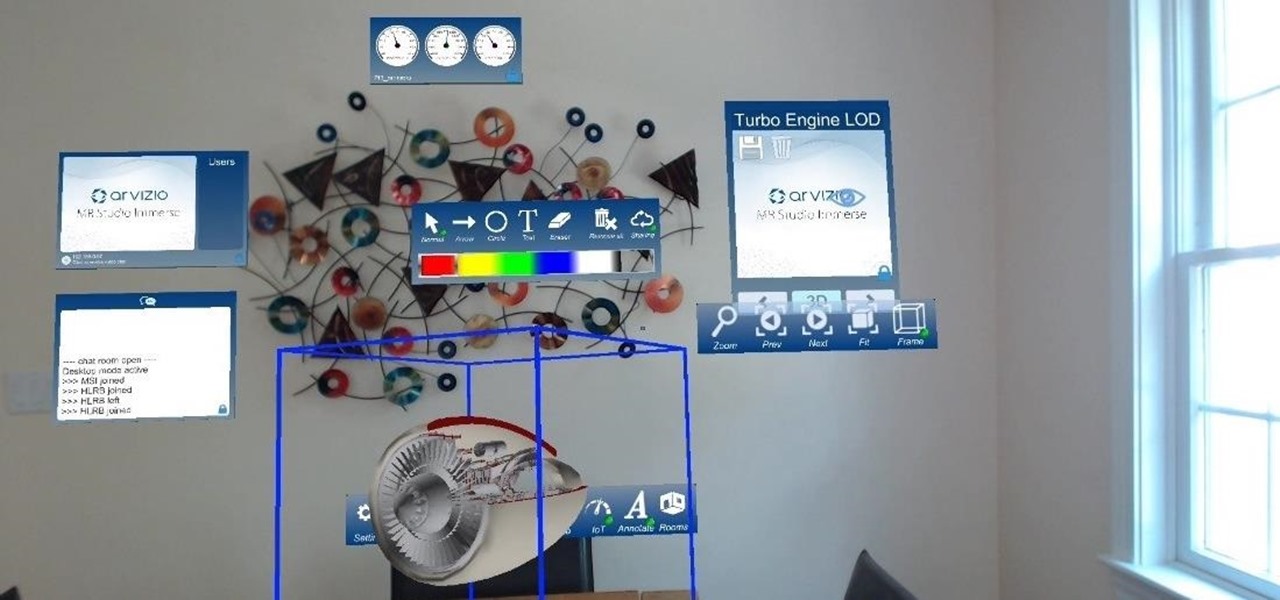
HoloLens developer Arvizio has expanded its collaboration suite of tools for enterprises with a device that can stream and record mixed reality experiences in high-definition for local and remote audiences.

If you've received a spam message in Signal Private Messenger, you know that anyone can contact you as long as they have your linked phone number. But when it comes to the people you're actually trying to have a private conversation with, how do you know it's really them?

Our smartphones are full of personally-identifiable information. So much of what we do with these devices is tracked and recorded to make our experience more streamlined and personalized. For many users, that's a fair trade — but for privacy-minded folks, it's a raw deal.

Augmented and virtual reality motion tracking leader Leap Motion, Inc. announced that it has secured $50 million in Series C funding to fund expansion into new territories and industries.

The peaceful, pastel and doily-filled world of Pinterest is my oasis. My account conveys who I want to be and what I want to accomplish, so the idea of someone hacking it and ruining my favorite escape for me is heartbreaking. Fortunately, Pinterest has updated its security, implementing three new features to hack-proof your account.

Firefox Focus is Mozilla's effort to make your internet experience a little more secure. Originally released in November 2016 for iOS, Focus blocks internet trackers, search history, anything that gets in the way of a clean, private browsing experience.

With the British exit from the European Union looming, the UK is looking to the auto industry to help boost their economy and secure jobs through the upcoming years. Today, Business Secretary Greg Clark and Transport Minister John Hayes announced the government investment of $136.7 million (£109.7 million) across 38 different automobile projects, as a part of the Plan for Britain.

Independent game developer PlayFusion announced today a partnership with NEXON Korea Corporation, resulting in a Series A preferred share round to fund development of their entertainment platform. PlayFusion's platform applies augmented reality, Internet of Things (IoT), and audio recognition to Lightseekers, an original property that combines mobile gaming with smart action figures, trading card games, and other media.

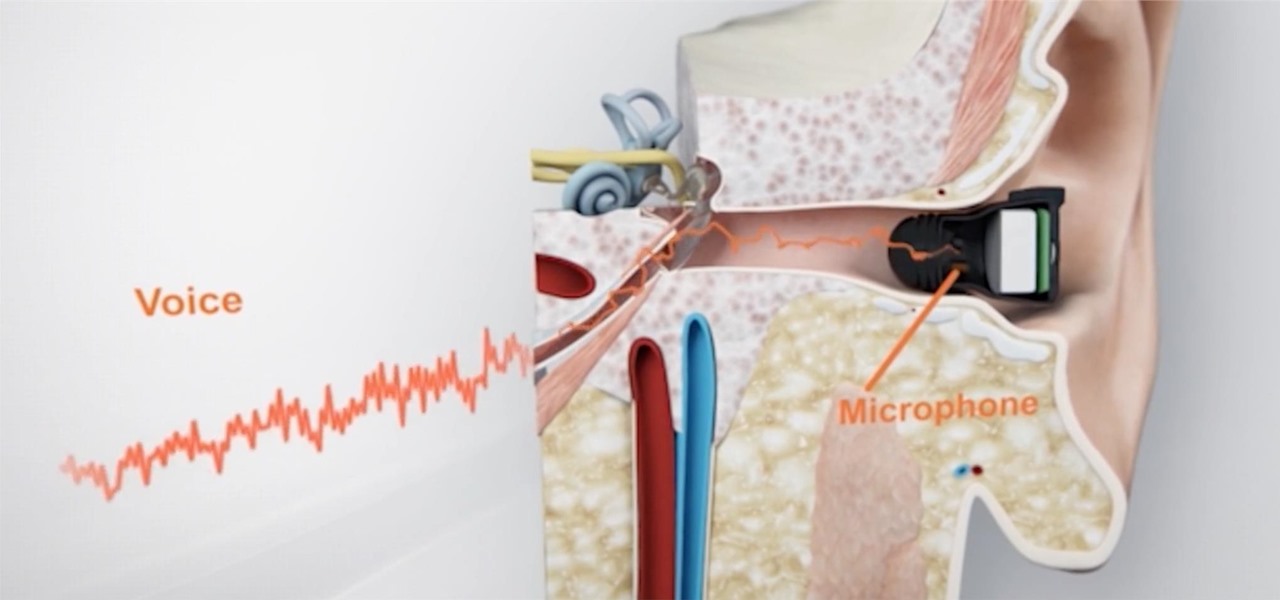
What's better than wireless in-ear headphones with noise-canceling technology? Giving them a microphone to hear you talk from inside your head. And that's exactly what you get with RippleBuds; its inside-facing mic helps keep your voice crystal clear over phone calls, and makes sure Siri, Cortana, and Google Now will always get the right command.

If you want to make some money from catching bugs and are sick of pentesting Facebook, Google, and Microsoft's products, Uber may be your new favorite playground.

Recently the newly famous ProtonMail service was under attack by DDoS attack. This attack was believed to be the hacking group Armada Collective.

In this tutorial I am going to show you how to change some file metadata, this could be very useful if you want to edit or access a file and remove any evidence of your changes.

Hello Everyone! I wanted to share a free and open source note taking tool that I've been using for quite some time now.

Welcome everyone to the second part of the How To Become Anonymous online series. Today I will (briefly) introduce you to what has been defined "The most secure OS" : Tails a Debian based OS. (Official website: https://tails.boum.org/)

This is a really tasty "scary" snack as it incorporates a lot of the flavours you'd usually put together (along with the almonds)

Making the bed is a challenging task, but trying to put a duvet cover over top your comforter is a challenge on a whole different level.

This is a simple process for those wanting to capture a circular view of an object with their smartphone or other type of camera.

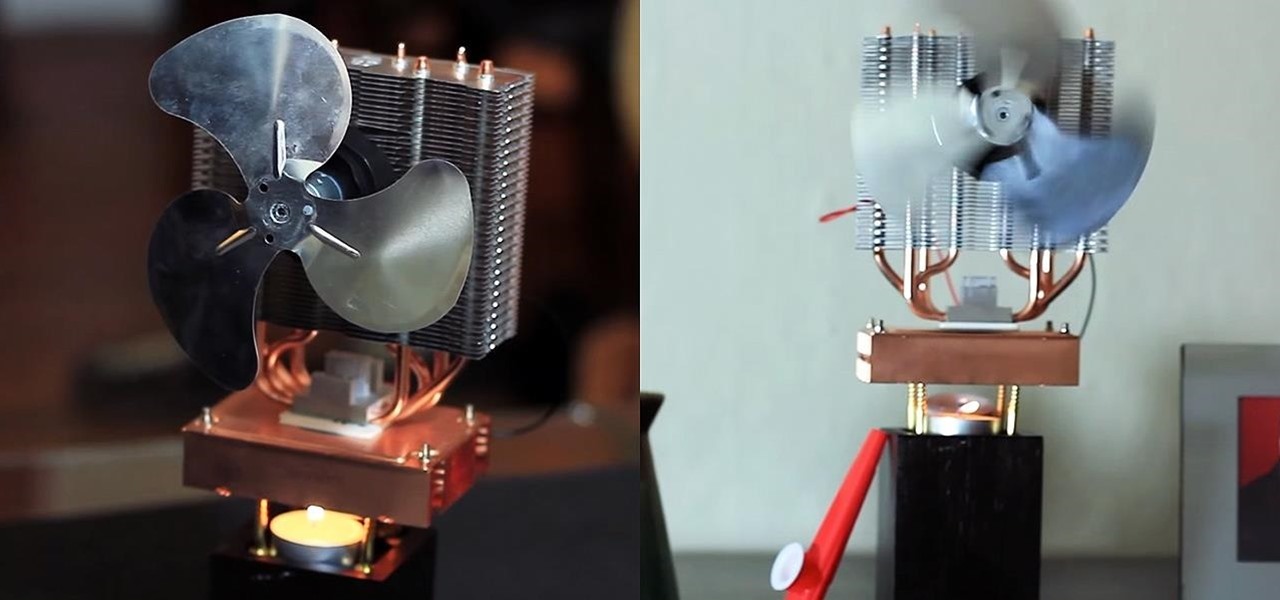
Staying cool in the summer heat sometimes feels like it takes all the energy in the world. But what about a fan using no-cost electrical energy? If you're looking to keep cool during a power outage, or if you don't want to break the bank by running your DIY air conditioner all day long, you can use candlelight to power a fan!

It has been a long while since I last came here to write an article. Graduate school keeps you busy. After I looked over what I had written previously, I decided that I should introduce another fun topic from cryptography. In this case, steganography.

This is an easy step by step tutorial how to lock your jewels in a hotel room or in a public safe. Be aware that in a public safe it is more secure to use the second method of locking by a magnetic card, not by a PIN code that can be easily seen by someone nearby.

Adding to the recent recent slew of bugs and issues within iOS 7, it now seems that emails sent with attachments are not encrypted, despite Apple's claims that they are.

Locking up your iPhone with a passcode prevents mischievous friends from looking at your pics and emails, and makes it harder for thieves to access your data before you get around to wiping it. For even more security, there's the password option, which gives you more than just 4 lonely digits.

Impeccable is the word for this distinctive and exclusive Ladder Hair Style. Extremely elegant and graceful, girls with long hair will be going to love this. Follow these simple steps and just with a little effort arrive at special and distinguished look. Step 1: Comb Your Hair to Make Them Smooth and Tangle Free. Gather All Your Hair and Tie Them in a Pony. Step 2: Take a Small Chunk of Hair from One Side of Pony and Braid It Leaving a Small Strand of Hair Before Each Weave at Inner Side Onl...

The new year is just around the corner so it is the perfet time to make an easy DIY calendar that will keep you organized on 2014!

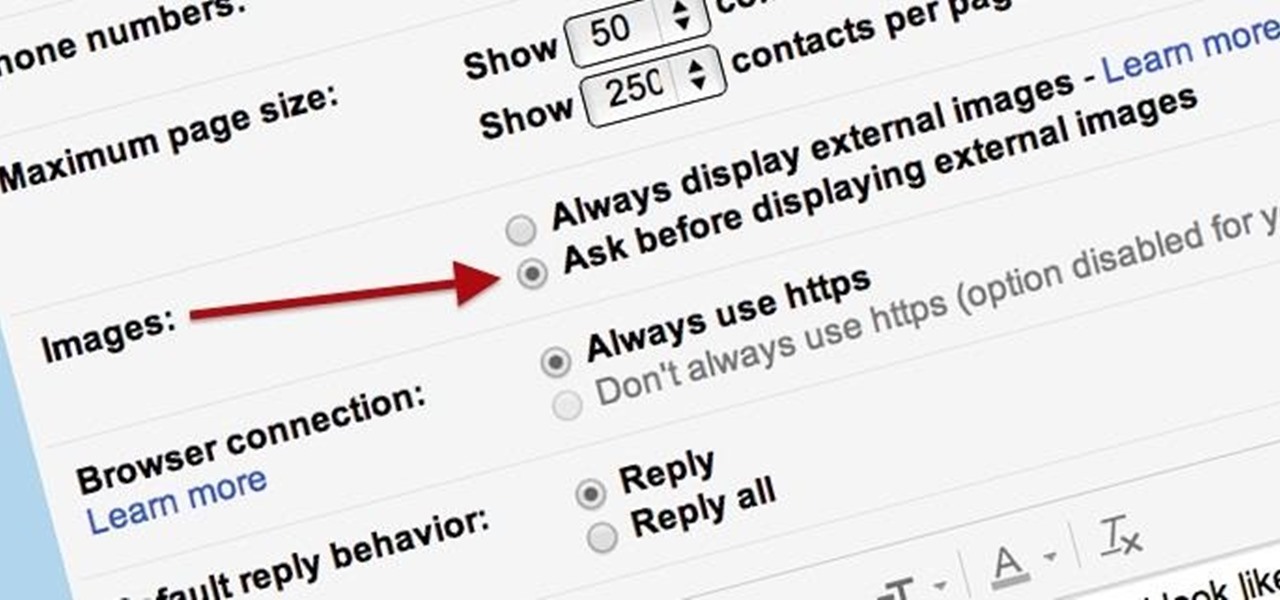
Securing your email address is one of the most important things you can do on the internet. Hackers, spammers, and overly aggressive marketers can turn your Gmail inbox into a heap trash if you're not careful.

Gmail is a free, advertising-supported email service provided by Google. Users may access Gmail as secure webmail, as well as via POP3 or IMAP4 protocols. Gmail initially started as an invitation-only beta release on April 1, 2004 and it became available to the general public on February 7, 2007, though still in beta status at that time. The service was upgraded from beta status on July 7, 2009, along with the rest of the Google Apps suite.

This is a create creation as a toddler toy. My girl loves this toy, she even wanted to take it to bed at night ... Sometimes, some of the most simple toys are some of the most like toys. This toy is cheap and can be completed in 10 minutes at most.

How to easily unclog your bathroom sink or kitchen sink and for zero dollars! Over time the bathroom sink or kitchen sink will get clogged up with gunk that will lead to poor drainage. Follow the steps outlined below for a hassle free unclogging solution.

Taking photos in the dark or in low-light settings can be tricky. Just using your normal flash can make your subject look washed out, but not using it can result in a totally dark photo with no subject at all.

A quick way to revamp an old dresser is to change out the knobs for some new decorative ones. Here’s an easy and budget-friendly way to make your very own DIY dresser knobs using shells – perfect if you’re looking to add a little bit of the beach to your decor: What you’ll need: shells (I got mine from the Dollar Store), nuts & washers, bolts (about 1 to 1.5 inches longer than the thickness of the shell), scrap rigid cardboard, rubber bands and epoxy glue.

Want to secure your home? There are plenty of ways to go about it. You can make your doorbell send you a text if someone rings it while you're not home, or build a motion-triggered security camera. Even better, you can beat potential crooks at their own game by installing a door they can't even find.

As practically the entire Steampunk world knows by now, IBM has predicted that Steampunk will be the big new trend from 2013 to 2015. They based this prediction on their computers, which sift through broad swathes of the internet in order to see patterns that may help commercial industries. According to them, Steampunk has been on the rise for the last few years, and they predict that it will explode into peak popularity within the next two years. But what does that mean and how will it impac...

You've seen security cameras everywhere in the public space. How many are there? Where are they? This is information that can be difficult to come by. It's not just criminals that are interested in information on this. It's your fundamental human right to be able to go about your daily life without being monitored and watched at every step. You might think that these cameras are for safety, and they can certainly help make people feel secure. Then it automatically follows that these people sh...

These three videos will show you how to build a rustic, distressed kitchen table. I'll be walking you through the process of selecting some recycled timber from a junk pile, and with a little care and some simple joinery techniques, transform that waste timber into a distressed timber kitchen or dining table. In fact, you could use the table for whatever you wanted really.

One of the biggest downsides to the iPhone is that it isn't as easy to customize as other smartphones. It's true that this makes Apple products more secure in some ways, but it also means that you have to jailbreak your phone and void your warranty if you want to change certain things.

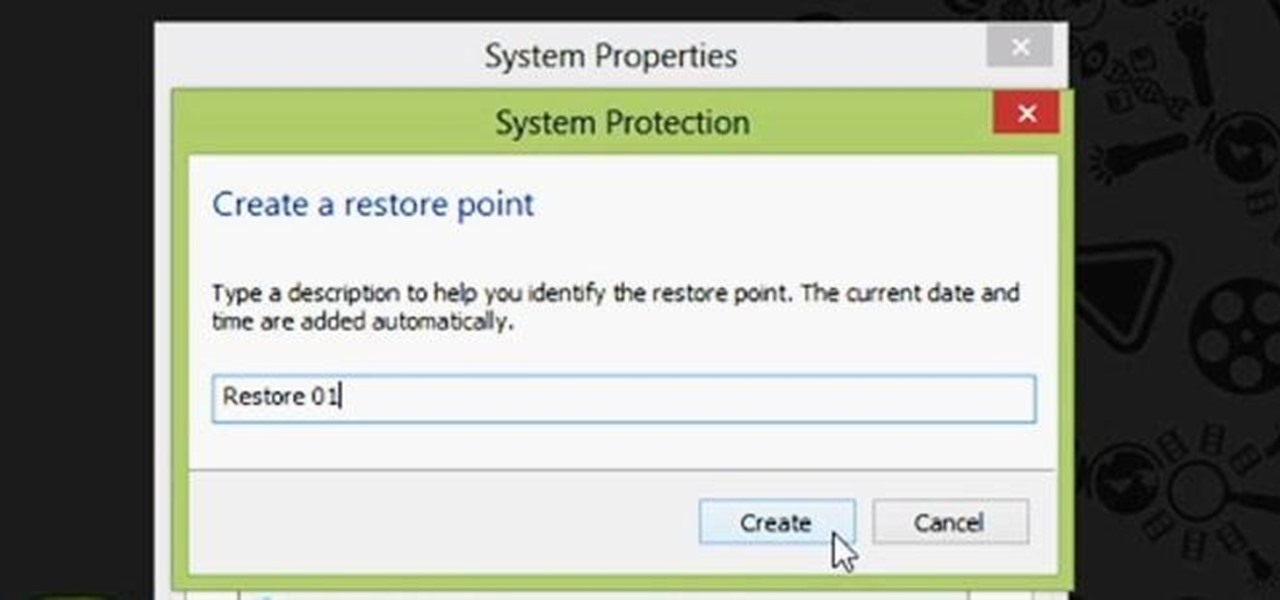
Restoring your computer to a previous point is an extremely important thing if something goes wrong. I've restored my computer at least a dozen times after downloading some suspicious software or running into an error I couldn't remedy on my own.