Take a look at this instructional video and learn how to install the Twilight hack for you Wii. The twilight hack is an exploit that reads a elf file off the root of your secure digital (SD) card. To start up this hack, you'll need to load the Zelda: Twilight Princess game before you can run any unofficial software.

In this how-to, Gary Rosenzweig of MacMost.com takes a look at best practices for making and storing passwords. You should have a different password for every account, for example, use secure passwords and store them in using a security utility. Learn how to store your passwords securely with this tutorial.

Ladies, here's a tip on which shoe size to buy your dance shoes in. A snug pair of shoes is more secure, and will make Latin dancing easier. Watch this video dance tutorial and learn how to pick the right size of shoe for Latin dance.

This instructional violin playing video shows one method of reducing the shaking of the violin when practicing vibrato. Just wrap the scroll with a piece of towel, and then place it against the wall to secure the position. Then practice the vibrato on the violin. This video is great for beginning violinists.

Tired of slipping and tripping on that pesky area rug? You can make any rug in your house non slip with just a tube of silicone adhesive. Watch this how to video and find out how to secure the rugs in your house.

RC Car Action Magazine Editor Kevin Hetmanski shows you how to put thread lock on your wheel nuts. Thread lock will keep the nut from loosening. Watch this video tutorial and learn how to secure nuts with thread lock on a remote control car.

RC Car Action Magazine Editor Paul Onorato shows you how to anchor an antenna tube to keep it from falling out. A piece of fuel tubing will solidly affix the antenna to the chassis of the remote control car. Watch this video tutorial and learn how to secure an antenna tube to the body of a remote control vehicle.

Watch this video jewelry making tutorial and learn how to flatten a crimp tube while making jewelry. Crimp beads when clamped, other beads from sliding around past a marked section,as well as secure closures on earrings, necklaces, or any other kind of jewelry.

This tutorial video will show how to do the typical soft knot used in silk ribbon embroidery, or the preferred method of the quilter's knot. Most ribbon embroiderers do not use a knot and just pierce tails or come back with another needle and thread and secure the tails that way.

This how to video is a tutorial on how to introduce a new color into a crochet project. Changing to a different color yarn is very simple with this instructional video. All you have finish your last row with a slip stitch, pull it through and secure it. Follow by adding you new yarn color with a simple slip knot.

What you need to do is press a certain button when your computer boots (it should say something like press this key to enter setup). Press the specified key and inside the bios find the option that allows you to set a password. Once you create a password then you have to set it so the computer requires the password on boot. Please rate and comment this video.

This "double sheet bend knot" is the same as the sheet bend, except that is has an extra turn to make it extra secure. Use this knot instead of the sheet bend if you have springy or slippery lines.

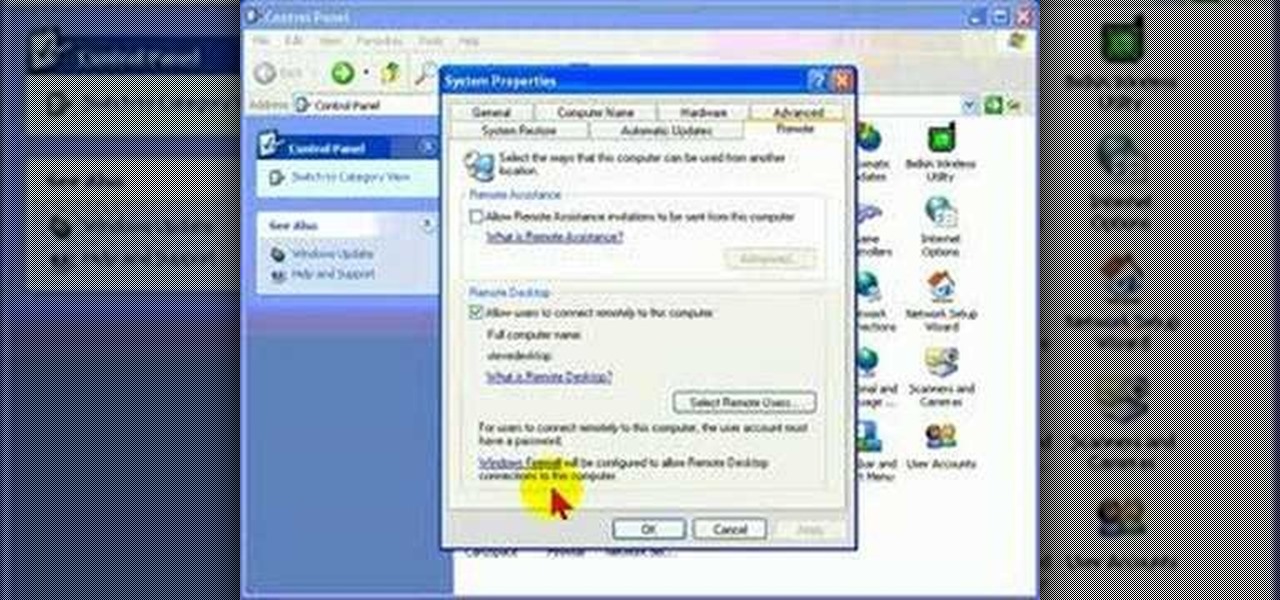
Remote Desktop is a feature of Microsoft Windows, that allows you to access your PC from anywhere in the world, and use it as if you were sat right in front of it.

Patti, the Garden Girl, host of the national PBS show Farmers Almanac TV shows how to brighten up your home and keep it secure with climbing roses.

The half blood knot with a tuck is similar to the improved clinch knot. The half blood knot with a tuck is a multi purpose fishing knot. The half blood knot with a tuck provides one good method of securing fishing line to hooks, lures, or swivels.

The improved clinch knot (overhand knot variation) is as the other clinch knots a multi purpose fishing knot. The improved clinch knot provides one good method of securing fishing line to hooks, lures, or swivels.

Protecting a new or young tree by staking it enables it to grow the strong root system it needs to secure itself in the ground. We will showyou how to stake a tree.

There are tons of quick pop up tents available nowadays, but the classic A-Frame tent still remains one of the most popular. A-Frames are those classic tents with the spikes in the ground that hold it up. They take a little more effort to erect but they are perfect for backpacking or short camping trips.

Before you go out to protest, understand what you are facing. Sometimes these demonstrations become infected with looters and rioters, which could mean interaction with law enforcement and potentially arrest. And if your phone is on you, it can be used as a tool against you.

Automotive augmented reality company WayRay has set its destination for a $1 billion valuation with an estimated time of arrival of 2019, and it has just passed a major milestone towards that goal.

A weak password is one that is short, common, or easy to guess. Equally bad are secure but reused passwords that have been lost by negligent third-party companies like Equifax and Yahoo. Today, we will use Airgeddon, a wireless auditing framework, to show how anyone can crack bad passwords for WPA and WPA2 wireless networks in minutes or seconds with only a computer and network adapter.

Google released its "Android Security: 2016 Year in Review" report last month, and to no one's surprise, included its own flagship phones. However, one surprise on the list was the BlackBerry PRIV, which Google named one of the best Android devices for privacy.

The Pixel and Pixel XL come with an awesome data-saving feature called Wi-Fi Assistant that automatically connects to open internet hotspots, then creates a secure VPN on your device to keep your data safe.

Take a look at this new and contemporary Prom Bun Hair Style which is super cool and exclusive to adorn. Its over the top style has a unique and sophisticated appearance which appends a ritzy accent to your urbane persona. Try out this style following this simple tutorial. Step 1: Comb Your Hair to Make Them Smooth and Tangle Free. Once Done Gather All Your Hair in a

Mermaid Braid Hair Style Tutorial For Beginners!!!!
There has been much talk about how unsecure the cloud is because of PRISM’s newfound ability to demand all of your data without any resistance. This has spin doctors in the Cloud Storage industry losing their mind. They suddenly went from a central hub for 10GB of your files, to an easy window for Big Brother to track you through. Centralized cloud storage is no longer a safe way to keep your files, but we still need a way to access our files anywhere we go.

We share links on an almost daily basis, usually not even thinking twice about it. Whether you're sending a funny cat video to your sister, or letting your coworker know where to go to download relevant files, there are plenty of reasons you might be giving someone a URL.

Today I would like to share a few data about painting on silk with all the creative readers. The knowledge comes in handy if you want to give a homemade gift or even try to sell a few of your masterpieces.

The Pixel 4 and 4 XL are the first Android phones released in the US to support secure facial recognition. You no longer have to hate on your Apple's friends because you now have "Face ID" as well. So I assume you want to set it up right away — here's how.

As smartphone users, we live in dangerous times. The value of phones continues to rise, making them prime targets for thieves. In 2015, the FCC estimated that one million phones are stolen each year, and with several devices starting to hit the $1,000 mark now, these numbers are sure to rise. But what do you do if you fall victim to phone theft?

The photo-centric Instagram app is a great way to share "evergreen" pictures and videos when compared to Snapchat and Facebook's new Messenger Day feature. But like all social media, keeping the account secure is an essential aspect, as it restricts unwanted viewers from seeing your content and can prevent unauthorized users from accessing your account. Instagram has several methods for locking down the account including a new two-factor authentication (2FA) mechanism.

Do you have a file (or many files) that, in the wrong hands, may cause you trouble? Don't worry about it, because I'll show you how to wipe it (or them) from your computer in order to leave no trace behind.

Welcome back, my amateur hackers! As many of you know, Null Byte will soon be re-establishing its IRC channel. In preparation of that event, I want to show how to set up a secure IRC client with OTR, or Off the Record.

If you are anything like me, you have a knack for taking silly selfies of yourself, i.e., taking scotch tape and wrapping it around your face to make yourself look like the blob, or perhaps you like taking selfies of yourself in weird or unusual situations doing weird and unusual things.

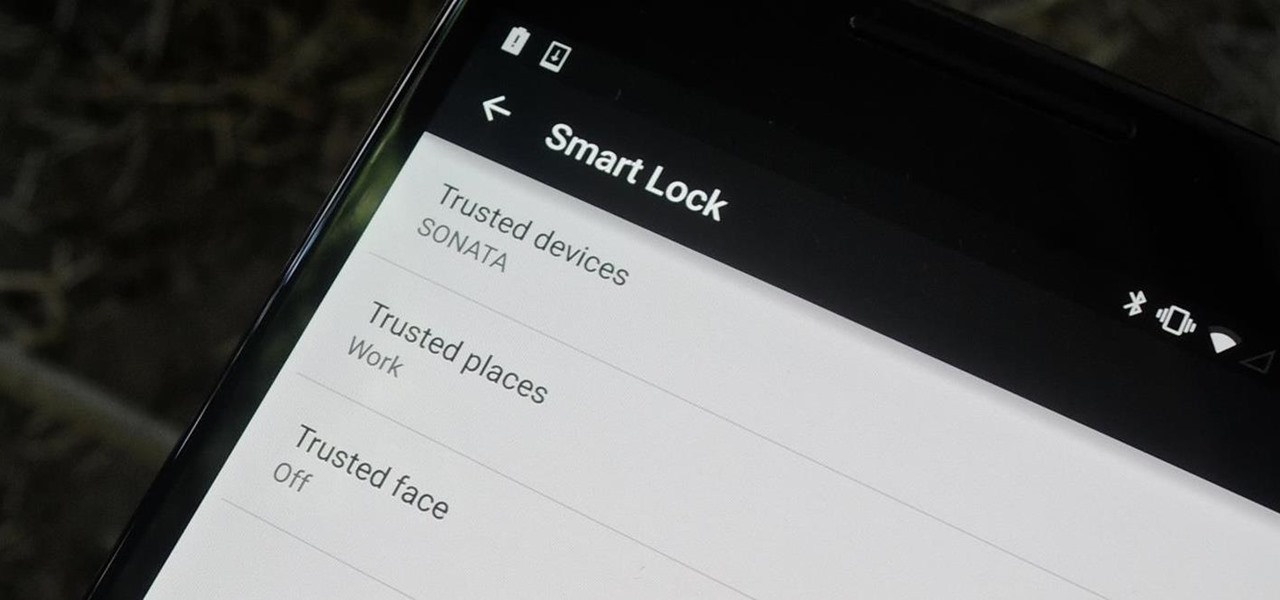
Keeping expensive mobile devices safe and secure is a priority for most of us, but the process of repeatedly unlocking a phone or tablet can seem like a pointless task. This leads to disabling the lock screen altogether, especially when in a safe place (e.g., home, office, car, etc.).

One thing that's always important to have in your home office is a bulletin board, because they let you quickly display papers that you need to see every day, such as schedules, notes and memos.

I always found that those safety lights for bicyclists on the market were never good enough when riding in the dark. That got me thinking about people who use wheelchairs and how unsafe the night could be when they want to go out. So here's what I came up with:

First of all the tutor advises that this is a good idea to do it regularly. It is advisable to drain it out otherwise it shall stop the boiler from working. Before starting your work you have to switch off your boiler. Now allow the water to cool down because it is very hot. First find out the radiator and the drain valve attached to it. Now take a hose pipe which is long enough to drain the water from the radiator to your backyard. Slide the pipe over the inlet and then secure it the link. S...

This video on typhoon preparedness comes from Andersen Air Force Base in Guam, where typhoons are common. The key to surviving a typhoon or other disaster is preparation. Stock up on enough food and supplies to last your family for about a week. Routinely check expiration dates on food, water and batteries and rotate your stock. Be sure window screens are in place and in good condition in the event the power is off for several days.

Wrestling with the whys are wherefores of WiFi? Can't figure out how to secure your network? Take heart: This remarkably thorough, seven-part home networking tutorial will get you up and running faster than you can say `Wireless G.'