
How To: Create a secure password
From email to online banking, you never want someone poking around in your personal information. Learn what to avoid when creating passwords, and try these tips to keep your passwords safe and secure.


From email to online banking, you never want someone poking around in your personal information. Learn what to avoid when creating passwords, and try these tips to keep your passwords safe and secure.
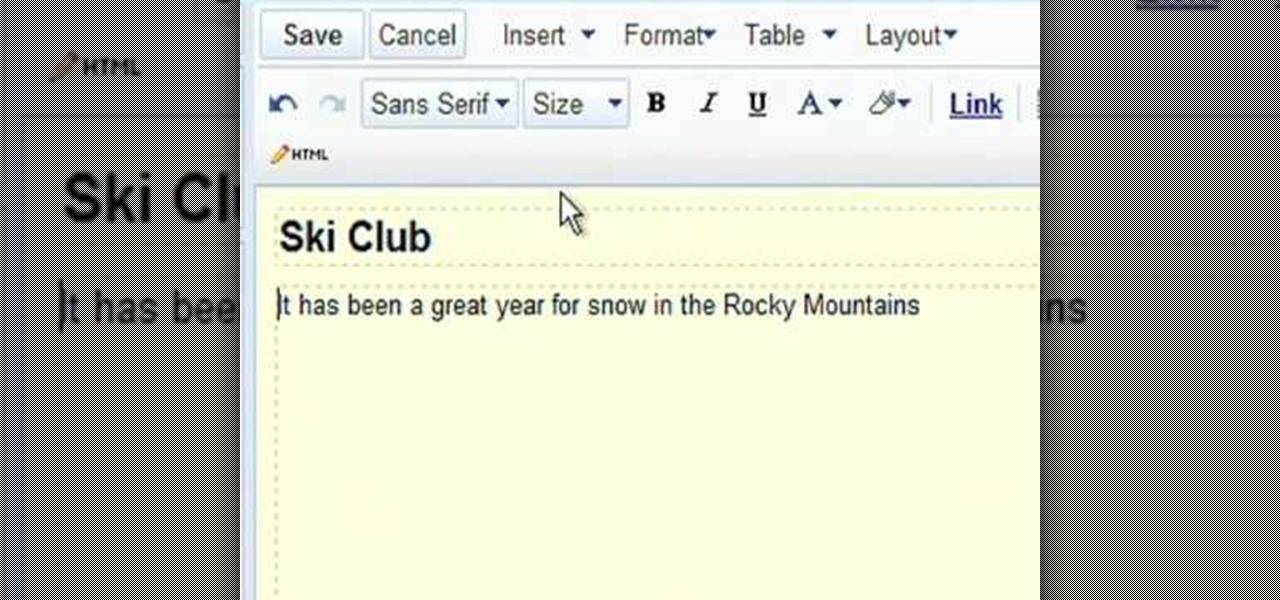
Google Sites makes it easy for anyone to create and manage simple, secure group websites. You can create and publish new pages with the click of a button, edit web pages like documents, and move content and pages around as you please. Information is stored securely online, and you decide who can edit or view the site. Google Sites is powerful enough for a company intranet, yet simple enough for a family website.

This video tutorial will explain you how to secure a USB thumbdrive (or flashdrive) using the free, open-source encryption software TrueCrypt.

In iOS 13, Apple introduced HomeKit Secure Video, which allows smart home devices with cameras to give iPhone users a private and secure way to store recorded videos. Plus, it has benefits such as object detection and activity notifications. Logitech is the first to add support for HomeKit Secure Video with its Circle 2 cameras, and all it takes is a quick firmware update to get started.
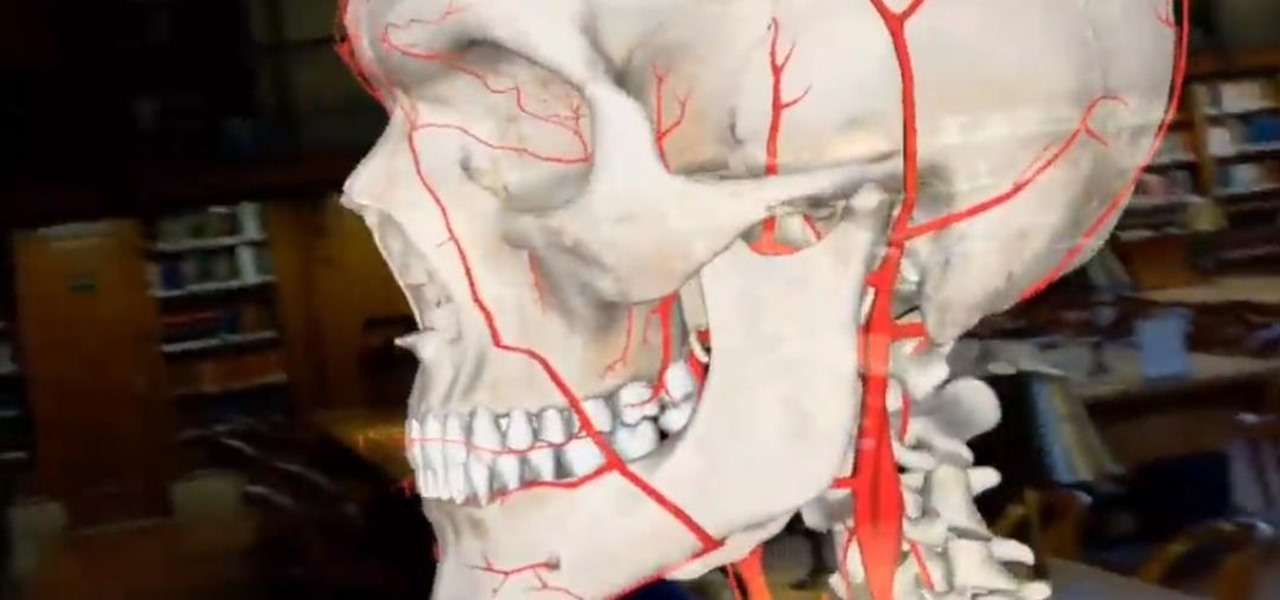
Not content to merely assist surgeons via the HoloLens, Medivis has expanded its augmented reality suite to Magic Leap One with an app for medical students.
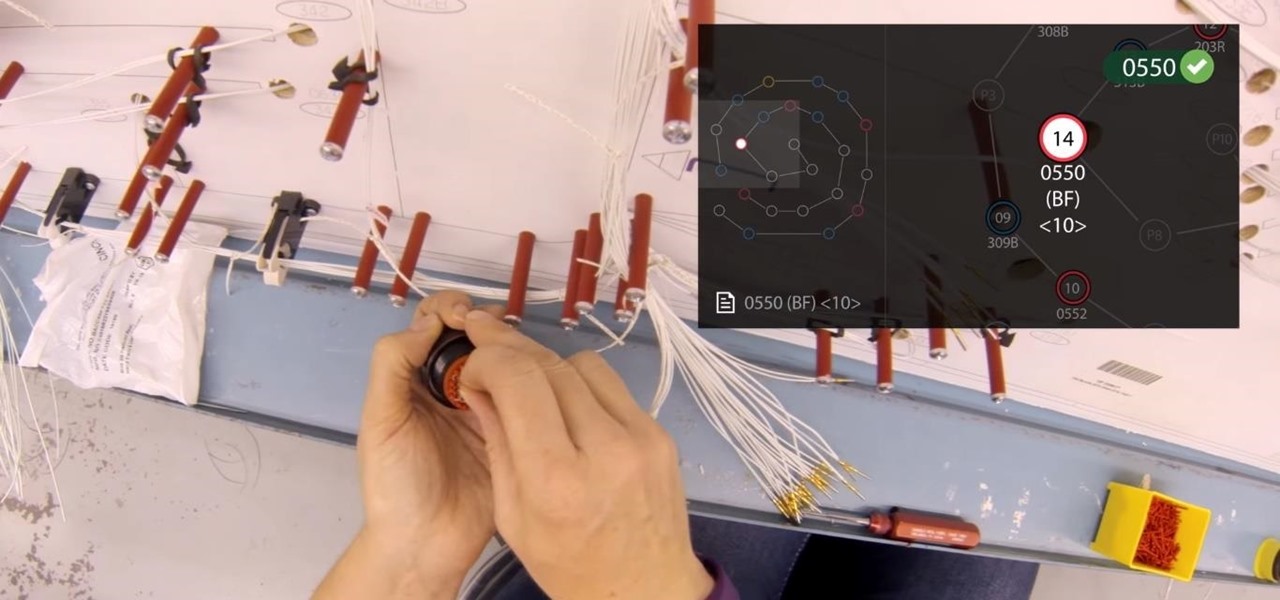
Upskill, an enterprise software developer for industrial augmented reality applications, recently received an influx of funding and a major vote of confidence from two of their top customers.

With more people joining the internet scene each day it's important that it's security is.. well it has to be good. Of course everything can be hacked and that's the way hackers work. They know there IS a vulnerability but they don't don't know the rest. in this article i'll try to explain the big difference between HTTP and HTTPS

Pop sensation Katy Perry has a wonderfully unique sense of style and fashion, from her clothes to her makeup to her hairstyles. And this video will show you one of the latter or the three— a great signature curls hairstyle.

Google is the biggest and best search engine on Earth, and if you are a webmaster and want your website to be a big success it would really behoove you to know as much about how it works as possible. The Google Webmasters series of videos and website were created to teach webmasters, SEO professionals, and others how Google works by answering their questions and giving them insights into how they can best integrate and utilize Google's functionality to improve their business. This video expla...

The Wood Whisperer is Marc J. Spagnuolo, a professional and passionate furniture maker, who also contributes to Fine Woodworking and Popular Woodworking. In this video, Spagnuolo shows us how to build a French cleat storage system. It's a very versatile unit, and gives you plenty of storage space without cluttering up a room.

This video tutorial is in the Computers & Programming category where you will learn how to secure your wireless internet connection. If you don't secure your wireless internet connection you are allowing others to enter in to your network. Open the set up CD and first change the network name from the default name to anything that you like. For this go to step 3 of 'naming your network', type in your network name and click 'next'. Then you enable security on the network by choosing 'WPA2'. Nex...

A tutorial on how to make a paper slingshot gun that shoots. Things you'll need: Bond Paper, Elastic, Scissor and Duct tape. Roll the bond paper half-wise. Secure with duct tape. Get another bond paper and fold it in half. Cut. Roll the cut bond papers length-wise and secure with duct tape. Form a "V" shape using the rolled cut bond papers. Attach to the first rolled bond paper to make a "Y" form. Secure with tape. Attach a rubber band on both ends. secure with tape. Follow these steps and Yo...

Professional truck driver, Yesterday Irmani, teaches us how to tie a time honored, weight sustaining knot, for transportation purposes.

Vines create the perfect look when grown over a trellis, arbor, or arch. You Will Need

My Fat Rocket Hairstyling ideas demonstrates this party hairstyle for long hair. Divide the hair into a few section before beginning. Pull a curling iron through the hair strand in a downward twisting motion. Move the curler through the hair slowly so the hair curls up at the ends. Using the right motion, a hair straightener can also be used to create the curls. Some strands of hair may need to be processed more than once. Use hairspray to secure the look. For a more sophisticated look, after...

Want to forget about always pulling out your credit card to purchase something on your BlackBerry? There's a little application that can do it all for you? But how? Best Buy has answers. The Best Buy Mobile team explains how to use the BlackBerry Wallet application. This application can store personal information such as credit card information and shipping addresses on a secure website for easy access when shopping online.

Increasingly, cutting-edge platforms like blockchain technology and augmented reality are overlapping, forging new digital frontiers that promise to change the way we interact with the virtual and the real world.

Thanks to a couple of photoshopped images that made rounds across Twitter last year, iPhone users were duped into thinking that iOS 8 included a security feature that would lock individual apps. Of course, none of it ended up being true, but we covered other features and apps that could accomplish roughly the same thing.

Bridal Bun Hair Style Tutorial For Beginners!!!! For the ultimate look of an elegant bride, this super cool yet graceful Bridal Bun Hair Style is an ideal adornment. Make your most special day your most cherished one by following these simple and easy steps Step 1:

There are many ways to wraps your hands for Muay Thai or kickboxing. One way is to first attach the Velcro to itself so that it creates a loop, after rolling the hand wraps back up in the opposite direction. Now you want to attach the loop to your thumb then wrap the wrap around your wrist three or four times. Secure the thumbs and come up towards the knuckles them you need to make a knuckle pad. You do this by looping the fabric about four times against your knuckles, securing it with your t...

In this how-to video, you will learn how to make a Jordan almond flower. You will need Almond holders, rose leaves, stamens for the center, a favor card, Jordan Almonds, floral tape, and ribbon. Take five Almond holders and place the Almonds in the center. Fold the Almond holders in half. Take five stamens and fold them in half to make a flower center of ten. Take floral tape and wrap it around the bottom. Attach the group of stamens and attach it an Almond holder. Secure this combination wit...

In this how-to video, you will learn how to make a Jordan almond flower. You will need Almond holders, rose leaves, stamens for the center, a favor card, Jordan Almonds, floral tape, and ribbon. Take five Almond holders and place the Almonds in the center. Fold the Almond holders in half. Take five stamens and fold them in half to make a flower center of ten. Take floral tape and wrap it around the bottom. Attach the group of stamens and attach it an Almond holder. Secure this combination wit...

Contrary to what most people do, letting your dog stick it's head out the window is not a safe way of transporting your animal! Check out this video for some tips on how to safely travel with your dog.

Keep your possessions safe from thieves with these tips. You Will Need

Email is one of the least private and least secure forms of communication, although few people realize this. MixMaster is one way to allow secure, anonymous communication even over the very public medium of email. This tutorial will get you started with MixMaster quickly and easily.

RC Car Action Magazine Editor Paul Onorato uses electrical tape to secure the AA's in your receiver pack. A little bit of electrical tape will keep the batteries in place while off-roading the RC vehicle. Watch this instructional video and learn how to anchor the batteries in the receiver of an RC vehicle.

This video will give you tips on how to secure your cabinets so that things don't come flying out of them in the event of an earthquake.

A tutorial on how to secure and configure a WRT54G Linksys router and also the steps needed to get default passwords and the list link.

Tim Carter demonstrates one technique to secure any book shelf or book case. Great video to learn how to safely secure a bookshelf.

Secure a bookcase without drilling holes in the furniture. Use velcro! Mark the top of the cupboard or bookcase first.

No baby shower is complete without a diaper cake, a gift that can also serve as a beautiful centerpiece. Here's how to make yours extra memorable.
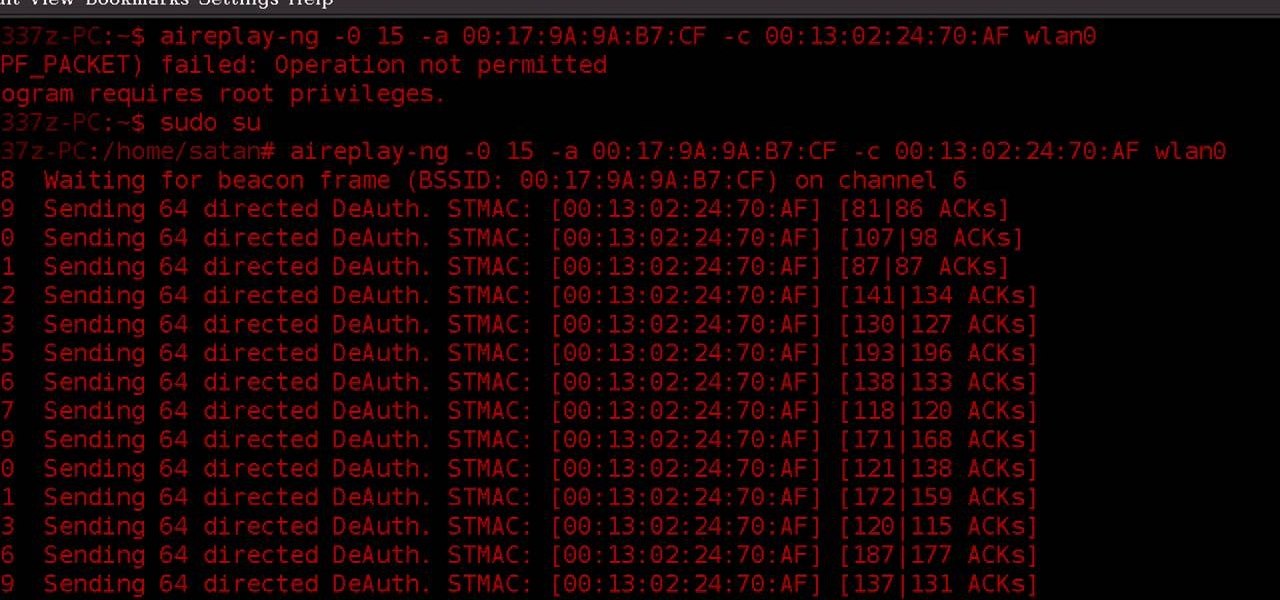
WPA-secured wireless networks, or WiFI Protected Access, is a form of internet security that secures your wireless LAN from being accessed by unauthorized users. Safer than WEP, or wireless equivalent privacy, WPA still has weaknesses that are prone to cracking - IF, that is, you know what you're doing.

Millions of laptop batteries have been recalled because of the risk of FIRE. Get some tips from CNET to learn how to keep your laptop battery safe and secure. First, make sure your battery hasn't already been recalled. Second, don't leave the laptop constantly charging because it heats it up. One way to save your battery is to remove it completely when you plug in directly. Third, treat the battery as fragile. And finally, four, avoid buying knockoff batteries.

If everyone in the world properly secured their email account there would be no spam. But yeah… never going to happen. That's more of a reason to encrypt and digitally sign our emails, but isn't using p2p security really expensive and really hard? Nope. It's actually free and easy with GnuPG. It's demonstrated on Mac OS X, but it's just as easy with Windows.
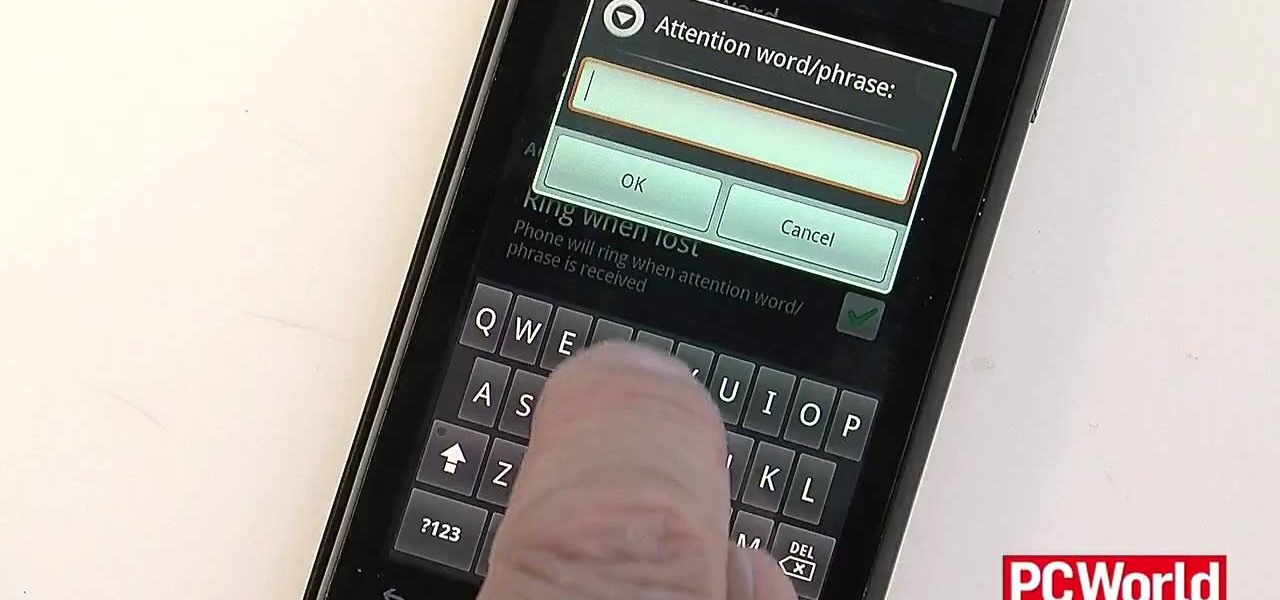
If you've spent a ton of money on your newest smartphone, you will want to make sure it's secure. In this tutorial from the experts at PCWorld, learn exactly how to activate safety mechanisms on your Android. With these options you can set a complicated passcode (so that anyone who does find your phone won't be able to access your files) and you can also set up a locator. By using the location app, you can text your phone from anywhere else and set off a search alarm so you will be able to fi...

This video tutorial shows you how to use a long wrap product to dress yourself while creating a secure carrier for your baby. The long wrap is brought forward from back to front and round your belly button, criss-crossed over your back and brought forward and criss-crossed once more, then tied. The two criss-crosses (in the shape of an X) help hold the babies legs, as the pass through the criss-crosses and support the baby. You should then try to bring the fabric down as far as possible to su...

Hak5 is at it again, with a plethora of somewhat accessible solutions to your technological problems. If you've ever needed to get through your school's firewall, or secure traffic tunneling, or try out applications in a fast, efficient manner? This video has it all and more.

If you want to transfer files to or from your iPhone at ease, check out this video on how to SSH / SFTP into your iPhone. SSH (Secure Shell) and SFTP (Secure File Transfer Protocol) all can be used to safely transfer files to your iPhone!

Many guides on Null Byte require using the Secure Shell (SSH) to connect to a remote server. Unfortunately for beginners, learning to use SSH can become a confusing mix of third-party programs and native OS support. For Chrome OS users, using SSH is even more difficult. We'll fix this by using the Chrome Secure Shell to establish an SSH connection from any device that can run a Chrome browser.

With the FBI getting access to iPhones, and apps like Waze being used to track people's locations, you've got to wonder just how safe and secure your smartphone is... or isn't. When you consider everything you do on your phone, from taking and sharing pictures to mobile banking, keeping your information safe is a crucial step that may seem out of your hands.