With this how-to, you'll learn how to mount an SSH server on your Mac as part of the file system. The key is a third-party program called MacFuse, which is available, free of charge, through Google Code. To get started running SSHFS, or the secure shell filesystem, on your own Mac, take a look!

While the clove hitch is not a particularly secure knot, it's useful in situations when the knot requires a little bit of give. The steps to tying this knot are demonstrated in this how-to video, and are shown at a fast pace so you can see how quick and easy it is to do. Watch this video knot-tying tutorial and learn how to tie a clove hitch knot quickly.
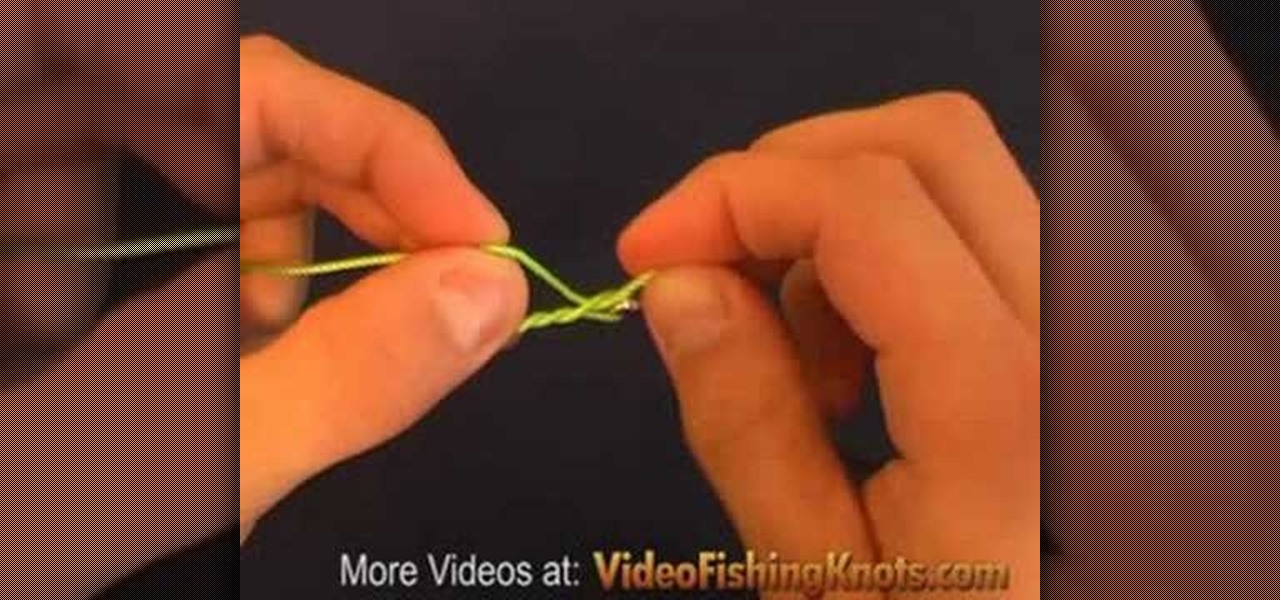
The Improved Half Blood Knot is basically a half blood knot with a little improvement. To make the knot more secure the end tag is locked in the final step when tying the knot. The Improved Half Blood Knot is a popular knot for attaching hooks, swivels and lures to the the fishing line. Watch this video fishing tutorial and learn how to tie and improved half blood knot on a fishing line.

RC Car Action Magazine Editor Matt Higgins explains how to modify your antenna cap for better wire protection. Make sure that antenna cap doesn't go flying off. Watch this video tutorial and learn how to secure the antenna cap on an RC vehicle.

In this roofing video Bob Schmidt shows you how to use the foam padding from a sofa cushion to say secure and not fall while doing roof repairs.

This video walks through basic security configuration for a WRT54G Wireless Router. Also provides a default password list.

Check out this video to learn what kinds of tools to use to secure your furniture during an earthquake. You may want to use straps and stud finders.

Ori Livney shows you how to secure your newly inflated balloon with a simple knot at the tip.

Are you a Gmail user? Listen up, cause here's a snazzy tip from Tekzilla to help protect your emails.

Install acoustical wall panels using adhesive to secure the panel to the wall.

Check out this video to learn how to install acoustical wall panels using pins to secure the panel to the wall.

Check out this video to learn how to install acoustical wall panels using impale clips to secure the panels to the wall.

Motorcycle expert Chris Kelly is here to show you how to transport a motorcycle. As long as your bike fits, the vehicle won't matter but pay attention to how to tie down and secure the bike.

There are countless ways in which you can turn your love of tech and coding into a full-fledged career — from developing apps and websites as a freelancer to working in the IT departments of small startups or major tech companies. But one of the best ways that you can put your programming skills to good use is to join the increasingly important world of cybersecurity.

The Pixel 4 and 4 XL are the first Android phones released in the US to support secure facial recognition. You no longer have to hate on your Apple's friends because you now have "Face ID" as well. So I assume you want to set it up right away — here's how.

With the upcoming Memorial Day weekend serving as the unofficial start of summer, Pepsi is turning to Instagram to help sell its soft drinks to quench the thirst of beachgoers and BBQers.

Location-based gaming pioneer Niantic has been preparing its flavor of AR cloud, the Niantic Real World Platform, to bring more realistic and interactive augmented reality experiences to mobile apps. And now the company is looking for a few good developers to help execute its vision on the platform.

For years, Skype has been synonymous with video calling and messaging. However, as the industry moved toward encryption and privacy, Skype usage was discouraged by experts due to its murky encryption. To combat this, Skype has introduced true end-to-end encryption.

Computer vision company Blippar has already dabbled with outdoor AR navigation, but now it wants to make it easier for people to make their way through indoor spaces with augmented reality.

Location-based gaming pioneer Niantic has offered a preview of its augmented reality cloud platform that could change the immersive content game yet again.

We need to take our privacy and security much more seriously. Whether it's malware-infected apps or the mishandling of our data by companies like Facebook, there are threats all around us in this digital world. Fortunately, some smartphones are simply designed to protect us better.

Following up on a preview of the deal we reported during last week's CES, Dell has officially announced the details around its role as the first company to resell the Meta 2 augmented reality headset.

Leading tier-one supplier Continental has confirmed it will sell driverless platforms developed from BMW, Mobileye, and Intel's previously announced alliance, giving the company a potential edge over competitors by widening the range of technologies it offers directly to OEMs.

This week's Market Reality covers a variety of business news from acquisitions and partnerships to competitive and technology assessments to quarterly financial results.

During his opening address on April 18 at F8, Facebook's developer conference, CEO Mark Zuckerberg launched the company's augmented reality platform centered on artificial intelligence-powered cameras.

Android has several features built into the platform that improve user experience but require extra attention to prevent a security breach. By modifying these settings, you can drastically reduce the possibility of someone exploiting your device or intercepting information.

Do you have a file (or many files) that, in the wrong hands, may cause you trouble? Don't worry about it, because I'll show you how to wipe it (or them) from your computer in order to leave no trace behind.

Welcome back, my amateur hackers! As many of you know, Null Byte will soon be re-establishing its IRC channel. In preparation of that event, I want to show how to set up a secure IRC client with OTR, or Off the Record.

If you are anything like me, you have a knack for taking silly selfies of yourself, i.e., taking scotch tape and wrapping it around your face to make yourself look like the blob, or perhaps you like taking selfies of yourself in weird or unusual situations doing weird and unusual things.

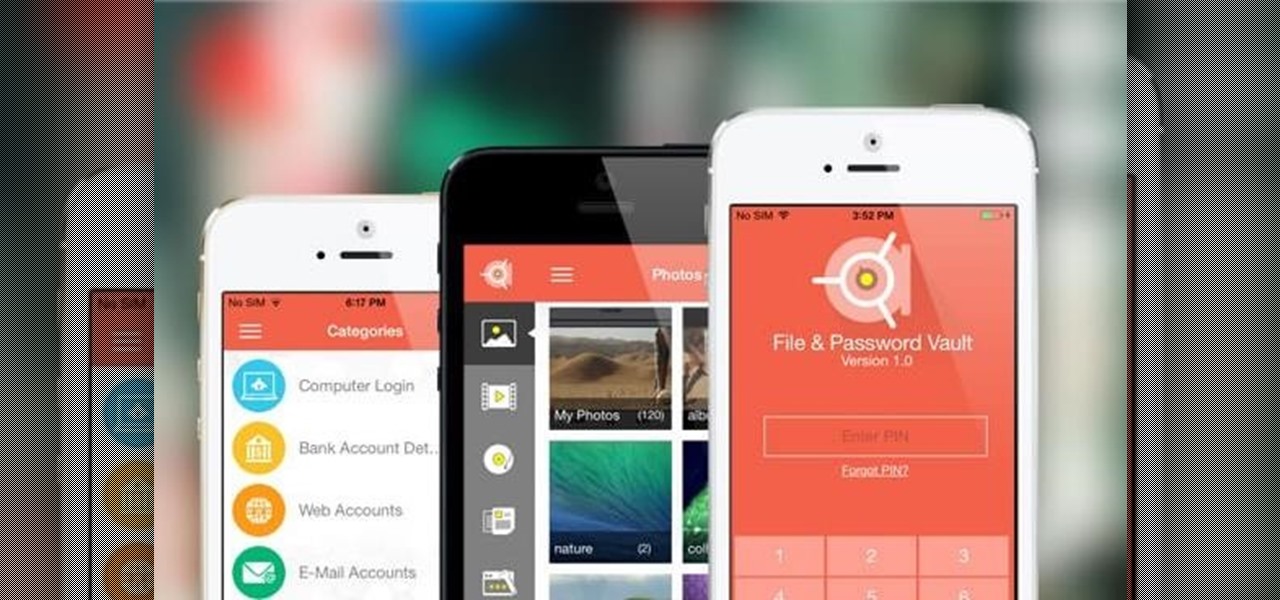
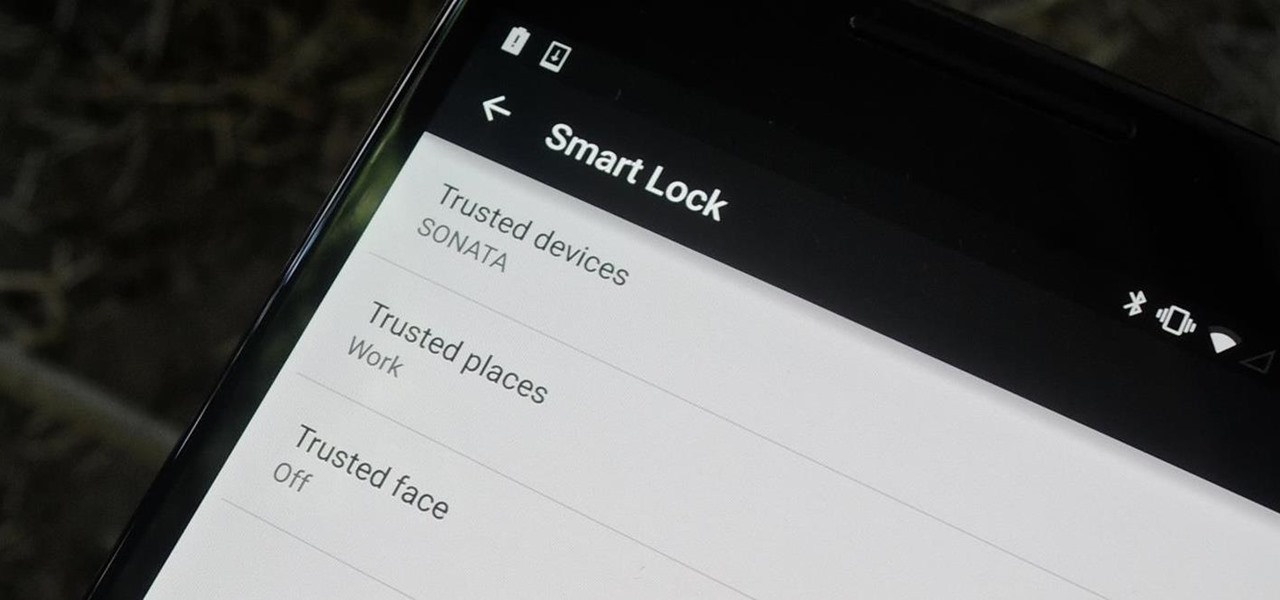
Keeping expensive mobile devices safe and secure is a priority for most of us, but the process of repeatedly unlocking a phone or tablet can seem like a pointless task. This leads to disabling the lock screen altogether, especially when in a safe place (e.g., home, office, car, etc.).

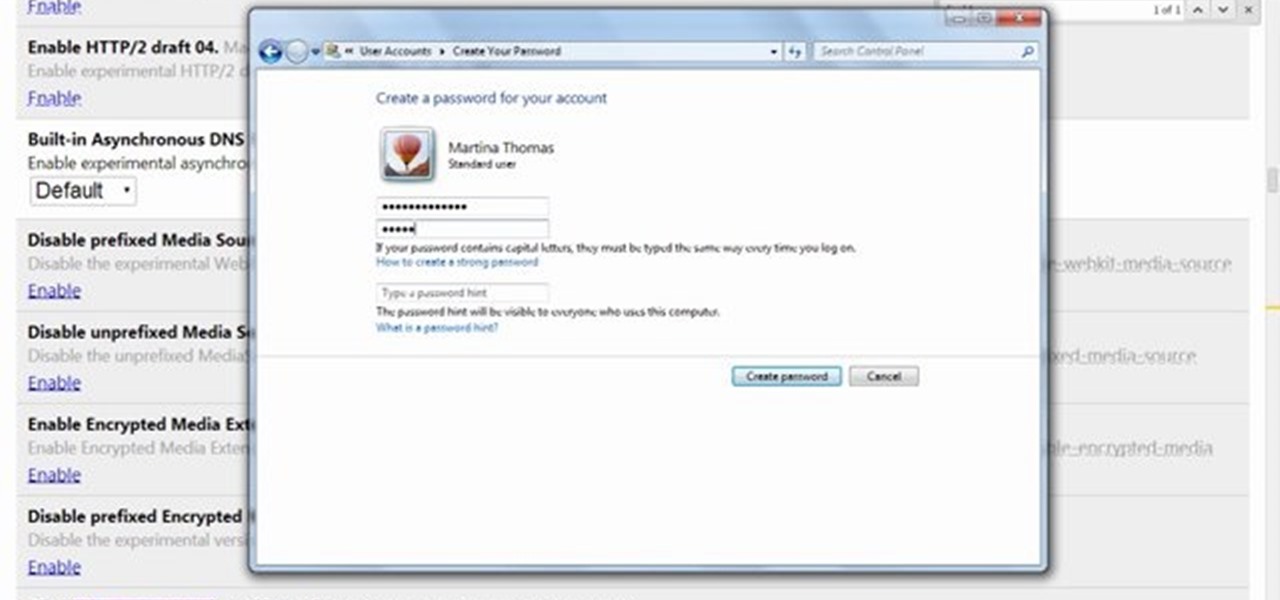
This video will show you how to protect others from accessing saved password on Google Chrome. Saving account passwords in browsers are useful for time saving as well as threatening for malicious activity. This is dangerous for security. So you must protect your accounts detail from others to secure your browsing. Watch the video and follow all the steps carefully.

This video will guide you how to make digital signature in MS Word. The digital signature will allow to secure your document from tampering. When you set digital signature in your word text then you can't insert anything in the document anymore. You could add your image of signature with text.

If you want to protect your word doc from other, you can give it a password. When anybody wants to open, it will ask a password. This way your valuable document will be secured from unauthorized access.

Make sure your private documents are completely secure. This episode by Tinkernut deals with not only encrypting your files, but also hiding them in a hidden volume.

Stay secure on public wireless networks by making your own FREE virtual private network (VPN). This tutorial shows you how to set up an OpenVPN server and connect to it from your laptop.

One thing that's always important to have in your home office is a bulletin board, because they let you quickly display papers that you need to see every day, such as schedules, notes and memos.

First of all the tutor advises that this is a good idea to do it regularly. It is advisable to drain it out otherwise it shall stop the boiler from working. Before starting your work you have to switch off your boiler. Now allow the water to cool down because it is very hot. First find out the radiator and the drain valve attached to it. Now take a hose pipe which is long enough to drain the water from the radiator to your backyard. Slide the pipe over the inlet and then secure it the link. S...

This video on typhoon preparedness comes from Andersen Air Force Base in Guam, where typhoons are common. The key to surviving a typhoon or other disaster is preparation. Stock up on enough food and supplies to last your family for about a week. Routinely check expiration dates on food, water and batteries and rotate your stock. Be sure window screens are in place and in good condition in the event the power is off for several days.

Wrestling with the whys are wherefores of WiFi? Can't figure out how to secure your network? Take heart: This remarkably thorough, seven-part home networking tutorial will get you up and running faster than you can say `Wireless G.'

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.