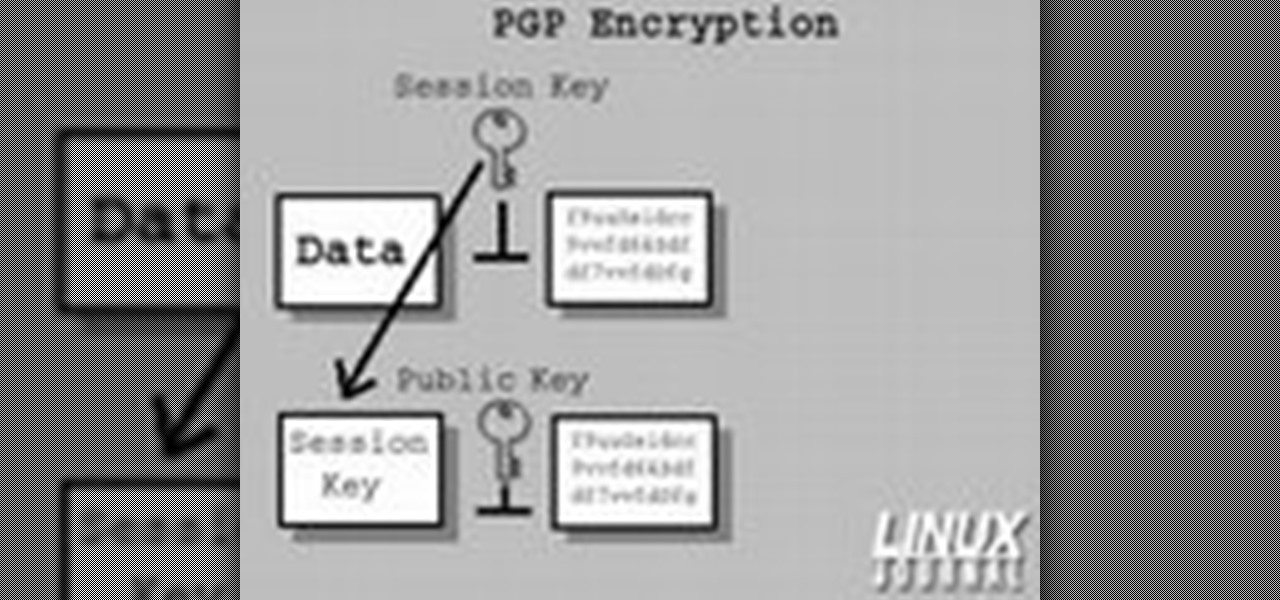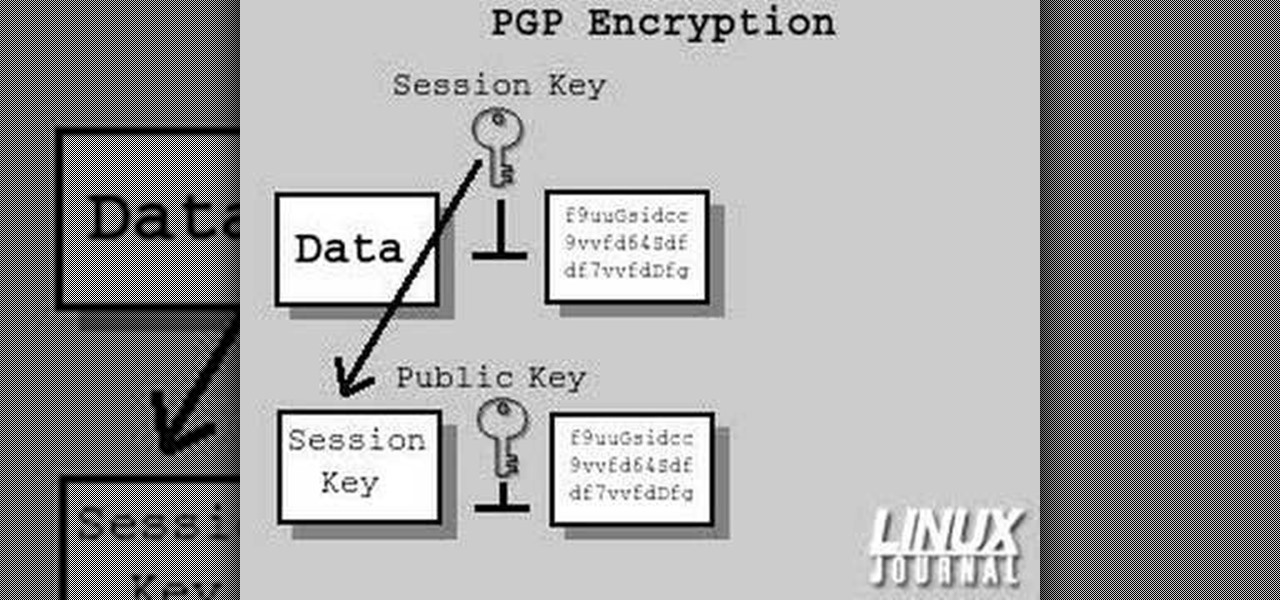
In today's time of rampant IT crimes, including identity theft, security is more important to the average computer user than ever. This tutorial, which was recorded and encoded for the Internet usingly only open source tools, demonstrates how you can use GnuPG to secure and verify data on your GNU/Linux box. Secure your Linux computer with this how-to.

Every dollar that comes your way is a blessing, especially when it comes to trading in the volatile world of bitcoins. Thankfully, Coinbase rewards you for sending much valued customers their way, giving you more money to feed your cryptocurrency trading needs.

While Black Friday shoppers found countless deals on all kinds of smartphones, one device was overtly left out of the price cuts — the iPhone X. Walmart was the only store to offer a promotion on the newest Apple device, and even then, it was difficult to find. Cyber Week appears to have repeated recent history, with only one store offering a special on the iPhone X, but it's not Walmart this time.

Thousands of Android users have been disappointed to learn that getting the latest firmware update isn't as easy as it sounds. Some really popular phones like the Samsung Galaxy S III just started getting the Jelly Bean upgrade, with the update continuing to roll out over the next couple of weeks overseas. All of the stateside S3 users will have to wait even longer for Android 4.1.

As with any investment, putting your money in foreign markets requires due diligence and the willingness to take risks.

In this tutorial, we learn how to use salty hashes to keep passwords secure. A hash is stored in a database that is hashed with an algorithm, so not everyone can see exactly what your password is. When you type your password into a website, it doesn't actually register as words, it registers as a hash. This keeps your passwords secure so not everyone can see them. Salting is when you use random pits and attaching them to your regular hashes so not every password is the same. The salt is what ...

Finding all of the rare trade objects in Assassin's Creed: Brotherhood can be infuriating, what with random item drops and quests to juggle. Watch this video for a guide to farming trade objects by killing bandits along a particular route.

Apple is set to unveil the iPhone 6 on September 9th, and shortly thereafter carriers like AT&T and Verizon Wireless will begin selling them online and in stores. So, if it's time in your contract for a device upgrade, it's time to start thinking about trading your current iPhone in for up to $400 in value.

Having a secure password is essential in today's interconnected world. Hackers are just around the corner, and if you have an easy to guess or hack password that you use for all of your accounts, someone can login to all of your websites very easily. Look at this guide on how to create a strong password by following the right password rules so that your accounts stay secure.

In this clip, you'll learn a few tricks of the trade for making your title text pop. Whether you're completely new to Sony's popular nonlinear editor (NLE) or are a seasoned digital video professional simply looking to pick up a few new tips and tricks, you're sure to be well served by this free video software tutorial. For more information, including detailed, step-by-step instructions, take a look.

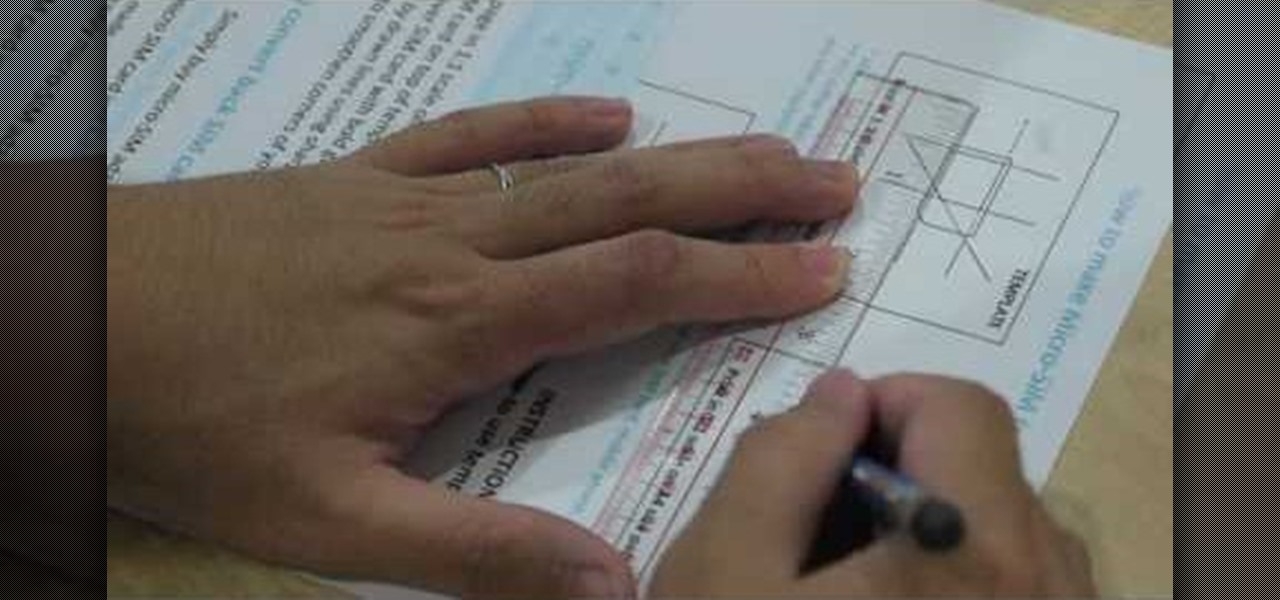
In this clip, learn how to trade phones and iPads back and forth by customizing your SIM card. This video will walk you through how to size and cut your SIM into the right shape for different devices. By customizing your chip, you will be able to move your data from one device to another with no problem. Use your old 3G SIM in your new iPhone 4 with this awesome hack.

Do you have a mirror that needs fitting in your bathroom, living room, or bedroom? From My Glass Trades, a video on how to cut mirror. Learn about the tools and techniques used to cut mirror and how to use an oil filled glass cutter and neophenolic L square. Get your project done the right way, and study up before you begin!

Sometimes you find ideas from the most unlikely objects. This video gives proof. Here are easy instructions for making a small box to hold business cards, ATC's (artist trading cards), gift cards, etc. Watch this video tutorial to learn how to make a small business card-sized box out of an old Orbit gum package.

This new episode of Full Disclosure shows you how to use a SSH Tunnel to secure your data when you are on an untrusted LAN (ex. Coffee Shop, School's network, or Defcon). Furthermore, you can use the SSH Tunnel to bypass the LAN's internet filters. The SSH tunnel protocol works by encapsulates your data into an encrypted payload and transmitting it to the SSH Server which is setup on a trusted LAN.

Meta Company filed suit today against a former employee and his startup DreamWorld USA, Inc. for the misappropriation of trade secrets and confidential information.

Time to trade in that rainbow guitar strap from something that fits your rock n' roll attitude. Well, nothing screams grunge louder than a guitar strap made out of duct tape. This simple tutorial shows you how to wrap it up, then strap it up. Rock on!

Are you thinking of trading in your 6mpg Hummer for something a little more efficient? Well, if you've got an electric or hybrid car in mind, this video will show you how to make a choice that works for you. With a little program called Electric Car Calculator, you can determine if the savings are worth it for you to get into one of today's hybrid or electric cars.

With this, you can trade worlds with your friends, or bring a save game from one machine onto another. All you need is to make sure that both computers have Minecraft installed, then find your save game file and move it around!

Internships can be a time when you obtain a vast amount of knowledge in a field that is close to what you wish to do in the near future. You come across many individuals who are able to teach you the tricks of the trade and can become very helpful allies. In this video, find out how to obtain letters of recommendation after your internship is long and over. So sit back, take notes, and enjoy!

In this video tutorial, viewers learn how to secure a home wireless network. There are 3 types of security protocols for connecting devices. The 3 types of security protocols are: OPEN, WEP and WPA. Users should use passwords that are secure but no so obscure that they are unusable. The password should not be dictionary words. They should be mixed with casing and contain the user's phone number. Go to your router's website and log into the website. Find the setting for wireless security and e...

Have important files that you want to put on a USB drive but do not want anyone else to be able to access them? Put a password on it using USBSecure.net free resource.

Use three tools to create a simple ponytail. Use a hairbrush, a bobby pin, and a bungee band holder for this look. Using a bungee band instead of a standard ponytail holder eliminates some of the issues typically caused by pulling hair through ponytail holders. Start by using a bristled brush to brush the hair to one location on the head. Secure one hook of the bungee band in the ponytail and wrap the tail around the rest of the hair. Wrap it around again, and secure the other bungee band hoo...

How to make a great green apple martini. First we start with the tools of the trade, you will need a glass, champagne or martini glass will do, next a set of tumblers, a speed pour-er, and a martini strainer. Now that all of those are laid out we need to chill the glass down, so take the larger tumbler and fill it 3/4 full of ice. Add the ice to the glass and set aside. While the glass is chilling out, we need to get our liquor out and ready to mix, these are the liquors needed:

Using ASP.NET Secure Services and Applications Services

Does your man run every time he sees a dance floor? It's common. Luckily, YourTango put together this advice video on how to get your man out on the dance floor with you! By enrolling in a class, sparking up a low-key dance session in your living room, or implementing small trade-offs, you might just see a change of your heart from your better half in no time at all!

Trampolines are just for backyard fun… there's skill involved, so let Trampoline Tricks 1080 show you some cool trampoline tricks.

Need to know how to tie a Bowline with a few ways of securing it? This way shows you how to secure it with a seizing so that it won't accidentally come undone. Included is a little variation of the bowline with a built-in seizing. If you don't have electrical tape to secure the bowline feed the bitter end back through the hole. It also makes it so you don't have a tail line dangling if you're towing something.

You can smash cars and entertain hundreds as a demo derby driver! Learn how to skillfully drive in a demolition derby. Filmed at the 2008 San Diego County Fair, this video will show you the tricks of the demolition derby driver trade and show you how to destroy everyone else while keeping your derby machine running.

In today's time of rampant information crimes, including identity theft, security is more important to the average computer user than ever. This tutorial from Linux Journal Online shows how you can use GnuPG to secure and verify data on your Linux box. (This video was created using only free and open source software tools: TightVNC, pyvnc2swf, ardour2, audacity, jackd, LAME, kolourpaint, cinelerra-cv, mjpegtools, and ffmpeg.)

Watch this video and learn beginner information for drink mixing and cocktails. This video explains the tools of the trade like glass and metal shakers.

In this clip, you'll learn how to get started using Secure Computing's Secure Web Protection proxy service. It's easy! So easy, in fact, that this helpful how-to can present a complete overview of the app in just over five minutes. For more information, including detailed, step-by-step instructions, take a look.

Attention jewelry makers! When making your own unique jewelry designs, one must learn how to secure the end crimp beads with crimping or chain-nose pliers. Crimp beads can be used for finishing off your strung jewelry or as "stoppers". In this tutorial, learn how to hone your jewelry-making skills!

Don’t play Russian roulette when it comes to your wheels. Keep your bike secure with these precautions.

A formal occasion calls for a classic look. You Will Need

Secure a square knot with tips from this video.

Buns and updos are gorgeous hairstyles, with one caveat: If they're not pinned perfectly and securely in place, all your hard work braiding and curling will go to waste as your hair slowly unravels.

Are you secure when downloading security software? Sounds like quite the conundrum, but CNET has answers. See if you're really secure when getting that software, and telling the difference between a rogue antivirus website versus a legit site. See how not to get scammed and destroyed!

In a legal brief entered on Monday, Florida-based startup Magic Leap has filed suit against the founder of Nreal, a former employee of Magic Leap, claiming that the company's Nreal Light smartglasses were built using Magic Leap's intellectual property.

While the consensus among some in the augmented reality community is that the Microsoft HoloLens is the best device available at present, it also remains the most cost-prohibitive option, with the development edition costing $3,000.

While the technology continues to mature, businesses from various industries continue to adopt augmented reality to improve the efficiency of business processes. In this edition of Brief Reality, as conference season continues, we see examples of augmented reality applied to logistics processes and marketing of industrial supplies, as well as the topic of discussion at another trade show.