
How To: Prevent bike theft
Don’t play Russian roulette when it comes to your wheels. Keep your bike secure with these precautions.


Don’t play Russian roulette when it comes to your wheels. Keep your bike secure with these precautions.

A formal occasion calls for a classic look. You Will Need

Email is one of the least private and least secure forms of communication, although few people realize this. MixMaster is one way to allow secure, anonymous communication even over the very public medium of email. This tutorial will get you started with MixMaster quickly and easily.

A little precaution can go a long way to securing your online banking experience. Use these tips from Tekzilla.

Secure a square knot with tips from this video.

Video: . This video will show you how to secure your kayak to a J bar roof rack carrier.

Welcome back, my budding hackers! In my continuing effort to build your basic Linux skills for hacking, I want to show you how to build a secure "tunnel" to MySQL.

Like everyone, you're on Facebook. And, also like everyone, you'd like to control the access your Facebook apps have BEFORE you even install them. Well, you can, with a sweet little Firefox add-on called FB-Secure. Take control of Facebook app privileges before they read your secret diary.
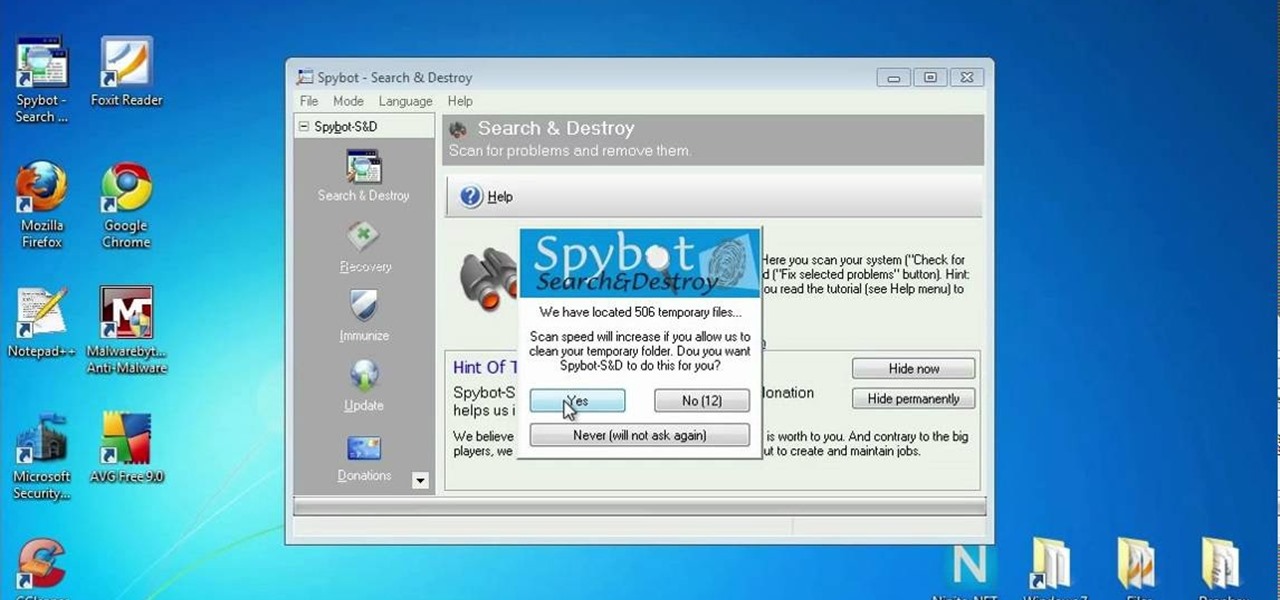
In this clip, you'll learn how to secure a new Microsoft Windows desktop or laptop computer. For more information, including a complete demonstration, and detailed, step-by-step instructions, as well as to get started protecting your own new Microsoft Windows PC, take a look.

If your home has a garage with a fairly standard garage door opener, that garage door is probably the easiest way for a burglar to gain entrance to your house. If you want to secure your home against such breakins, watch this video. It offers tips for securing your garage door so that thieves cannot gain access to your property and your family.

Looking for a guide on how to secure your public Facebook profile? This clip will show you how it's done. Whether you're completely new to the Facebook's popular social networking site or simply require a small amount of clarification on how to perform a particular task on Facebook, you're sure to benefit from this helpful video guide. For more information, including detailed, step-by-step instructions, take a look.

In this video, we learn how to wear a beret securely. This is used to keep the beret on your head so it doesn't fly away. To do this, you will need the beret and bobby pins. First, place the beret onto your head and style your hair around it so it looks how you prefer. Next, grab your pins and place then inside the beret holes onto your hair. Use a couple of the pins to make sure the hat and hair are connected and secured tightly. When finished, move the hat slightly to make sure it is secure...

Learn how to create & secure applications with BIG-IP v10. Whether you're new to F5 Networks' popular network appliance or are a seasoned administrator just looking to better acquaint yourself with BIG-IP, you're sure to benefit from this free video software tutorial. For more information, including detailed instructions, take a look.

This video is a tutorial on how to make a baby diaper cake. To begin, you will need to roll all your baby diapers from the waist down and secure them with rubber bands. Your top tier will have 8 diapers, the middle tier will have 19 diapers, and the bottom tier will have 40 diapers. Use rubber bands to secure all your tiers together. Next, glue thick ribbon around the tiers over your rubber bands. Follow up with decorations such as bows and extra ribbons. Use a cake stick to secure the tiers ...
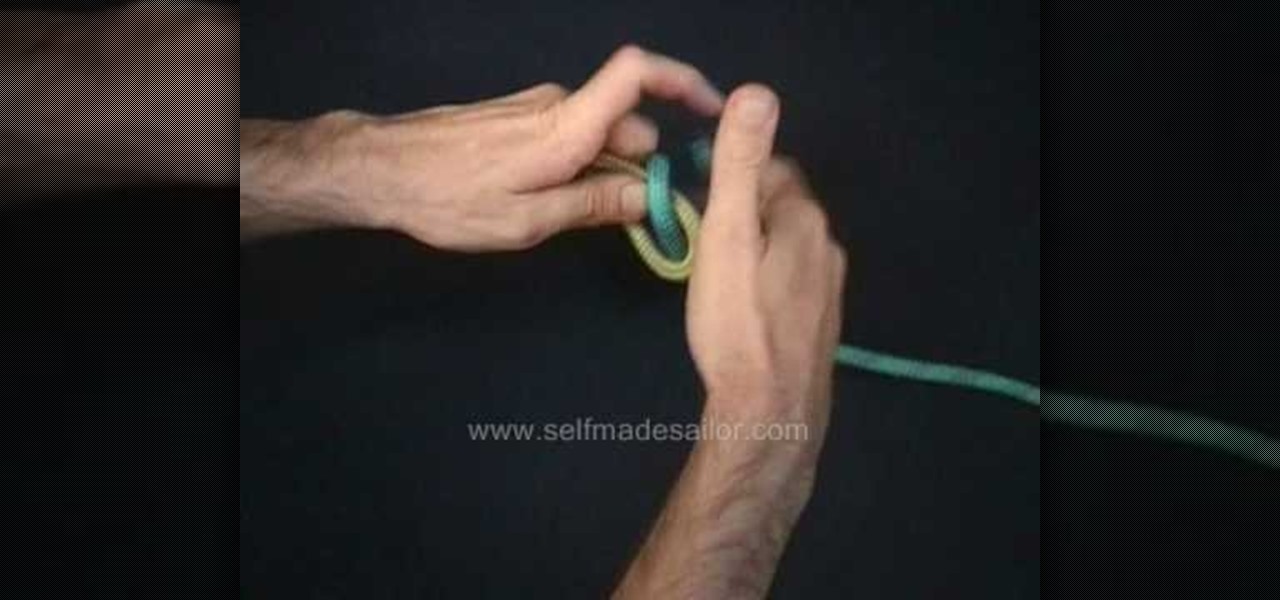
Need to know how to tie a Double Sheet Bend? This is a more secure version of the standard sheet bend, and an excellent way of joining two ropes of equal or different diameter. He's using flex rope, but it's a generally good way of securing two lines together.

Studying to be a nurse? Then one important part of nursing involves making your patient comfortable. This nursing how-to video demonstrates how to attach Foley catheter tubing to the leg to avoid pulling. Our nurse uses a catheter securement device to secure the catheter in place. Follow along and learn how easy it is to use this device to secure the Foley catheter to avoid pulling.

From email to online banking, you never want someone poking around in your personal information. Learn what to avoid when creating passwords, and try these tips to keep your passwords safe and secure.
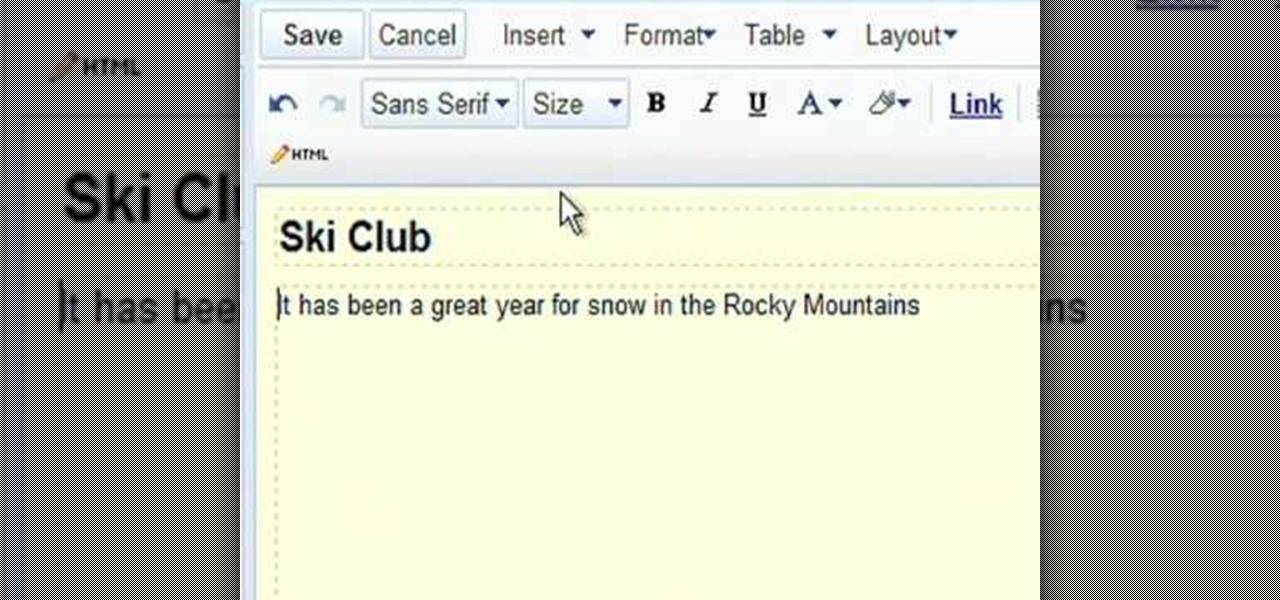
Google Sites makes it easy for anyone to create and manage simple, secure group websites. You can create and publish new pages with the click of a button, edit web pages like documents, and move content and pages around as you please. Information is stored securely online, and you decide who can edit or view the site. Google Sites is powerful enough for a company intranet, yet simple enough for a family website.

This video tutorial will explain you how to secure a USB thumbdrive (or flashdrive) using the free, open-source encryption software TrueCrypt.

Pop sensation Katy Perry has a wonderfully unique sense of style and fashion, from her clothes to her makeup to her hairstyles. And this video will show you one of the latter or the three— a great signature curls hairstyle.

Google is the biggest and best search engine on Earth, and if you are a webmaster and want your website to be a big success it would really behoove you to know as much about how it works as possible. The Google Webmasters series of videos and website were created to teach webmasters, SEO professionals, and others how Google works by answering their questions and giving them insights into how they can best integrate and utilize Google's functionality to improve their business. This video expla...

The Wood Whisperer is Marc J. Spagnuolo, a professional and passionate furniture maker, who also contributes to Fine Woodworking and Popular Woodworking. In this video, Spagnuolo shows us how to build a French cleat storage system. It's a very versatile unit, and gives you plenty of storage space without cluttering up a room.

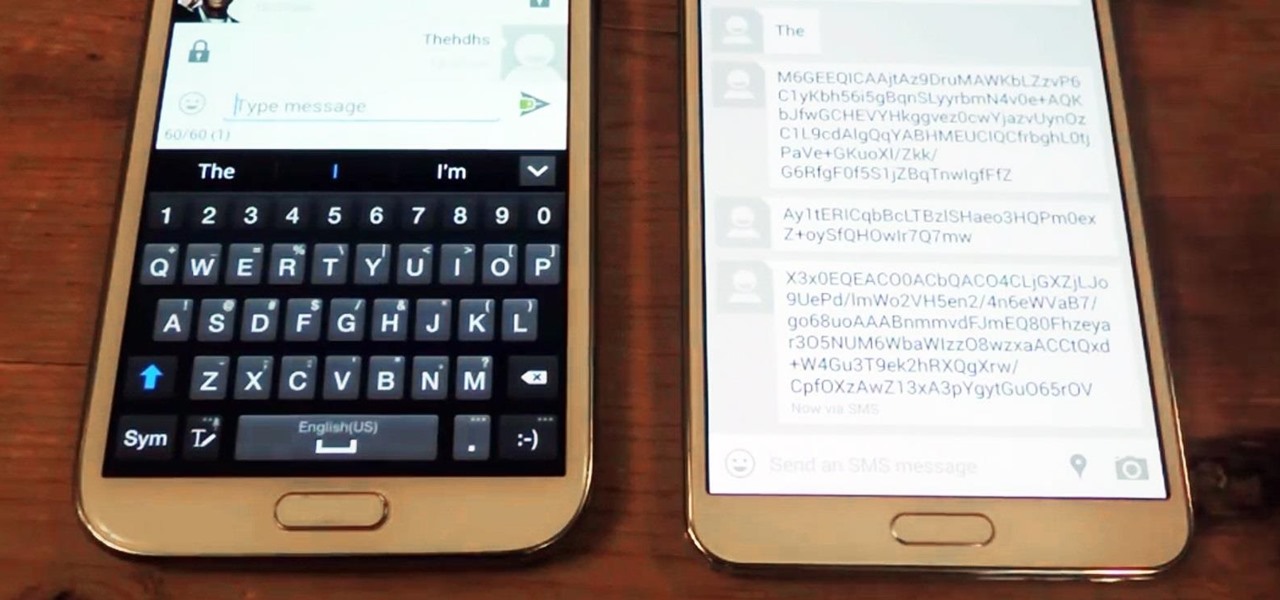
Smartphones are still "phones," which means communicating with others is usually a primary use. Ranging from a simple "hi" to a more personal conversation and even sharing passwords, our messages should remain private so that only the intended recipient sees their content. While many apps tout end-to-end encryption, not all apps prioritize security and privacy.

Many guides on Null Byte require using the Secure Shell (SSH) to connect to a remote server. Unfortunately for beginners, learning to use SSH can become a confusing mix of third-party programs and native OS support. For Chrome OS users, using SSH is even more difficult. We'll fix this by using the Chrome Secure Shell to establish an SSH connection from any device that can run a Chrome browser.

Like its predecessor—and probably every device in the future—the Samsung Galaxy S6 comes with a fingerprint scanner that allows for a more secure lock screen, web sign-ins, and account verification. But unlike its brethren, the sensor on the S6 has been vastly improved. No longer does it require a clumsy swipe—all you have to do is place your finger on it for less than a second, much like Touch ID on iPhones.

In the wake of the NSA controversy and its subsequent fallout, many dashed towards finding means of secure communication—using private internet browsing and encrypted text messaging applications—out of fear of being spied on.
In spite of the degree of difficulty it is to install, CyanogenMod has steadily climbed the ladder to become one of the most popular third-party firmwares for Android devices.

With more people joining the internet scene each day it's important that it's security is.. well it has to be good. Of course everything can be hacked and that's the way hackers work. They know there IS a vulnerability but they don't don't know the rest. in this article i'll try to explain the big difference between HTTP and HTTPS

Windows users have been getting a lot of bad news about their security lately. First, we found out that passwords in Windows 7 and 8 can easily be exploited if password hints are enabled, and now, Russian password-cracking software developer Elcomsoft has found another huge vulnerability.

In this video tutorial, viewers learn how to properly shoot and sight in a compound bow. It is recommended that users use a release. Your body should be perpendicular to the target. Hold the bow vertically, and hold it with a relaxed and secure grip. When you are ready to begin shooting, learn a technique that will help you relax and steady the bow. When you draw the bow string back, you should be looking through the peephole on the bow string and where the target and pins come into view. Thi...

In this video tutorial, viewers learn how to make a guerilla spotlight using household items. Users will simply need a cardboard cylinder and a light source. Te materials used in this video were a toilet paper roll, piece of aluminum, gaff tape and a lamp. Begin by cutting a couple of 90 degrees slots in the middle of the foil, slide in the tube ad secure it with tape. It should be a bit longer than the tube. Now wrap it around the light source. This video will benefit those viewers who produ...

Professional truck driver, Yesterday Irmani, teaches us how to tie a time honored, weight sustaining knot, for transportation purposes.

Vines create the perfect look when grown over a trellis, arbor, or arch. You Will Need

This video tutorial is in the Computers & Programming category where you will learn how to secure your wireless internet connection. If you don't secure your wireless internet connection you are allowing others to enter in to your network. Open the set up CD and first change the network name from the default name to anything that you like. For this go to step 3 of 'naming your network', type in your network name and click 'next'. Then you enable security on the network by choosing 'WPA2'. Nex...

A tutorial on how to make a paper slingshot gun that shoots. Things you'll need: Bond Paper, Elastic, Scissor and Duct tape. Roll the bond paper half-wise. Secure with duct tape. Get another bond paper and fold it in half. Cut. Roll the cut bond papers length-wise and secure with duct tape. Form a "V" shape using the rolled cut bond papers. Attach to the first rolled bond paper to make a "Y" form. Secure with tape. Attach a rubber band on both ends. secure with tape. Follow these steps and Yo...

As smartphone users, we live in dangerous times. The value of phones continues to rise, making them prime targets for thieves. In 2015, the FCC estimated that one million phones are stolen each year, and with several devices starting to hit the $1,000 mark now, these numbers are sure to rise. But what do you do if you fall victim to phone theft?

In this video tutorial, viewers learn how to winterize their home. Users should begin by cleaning the gutters on the side of their house. Scoop out all the debris and seal it with caulk. Then change the batteries of the smoke detector and clean it. It must be replaced if it is over 10 years old. Prepare the lawn mower for the spring season by sharpening the blades, clean it and drain all the gas out. It is a good idea to trim off the shrubs and trees. This video will benefit those viewers who...

In this video tutorial, viewers learn how to create a red carpet look with the undone bun hairstyle. Begin by bringing all your hair to one side and apply a band around the bun to secure it. Then take a clip and randomly pin it to the ends of the ponytail. Continue doing this for the rest of the ends of hair in the bun. Users may use up to 30 pins. Make sure the pins don't move and don't overdo the pins. This video will benefit those viewers who are interested in beauty and fashion, and would...

In this video tutorial, viewers learn how to strap down large items to the bed of a truck. Users will just need a long rope. The rope should be long enough to wrap around the back of the truck. Take the rope and make a loop. Then wrap around it and pull. It should look similar to a rope noose. Make sure it is tight. Then take the other side of the rope and put it through the loop. Pull on it to tighten. Then wrap around it and pull. Do this several times to secure it. This video will benefit ...
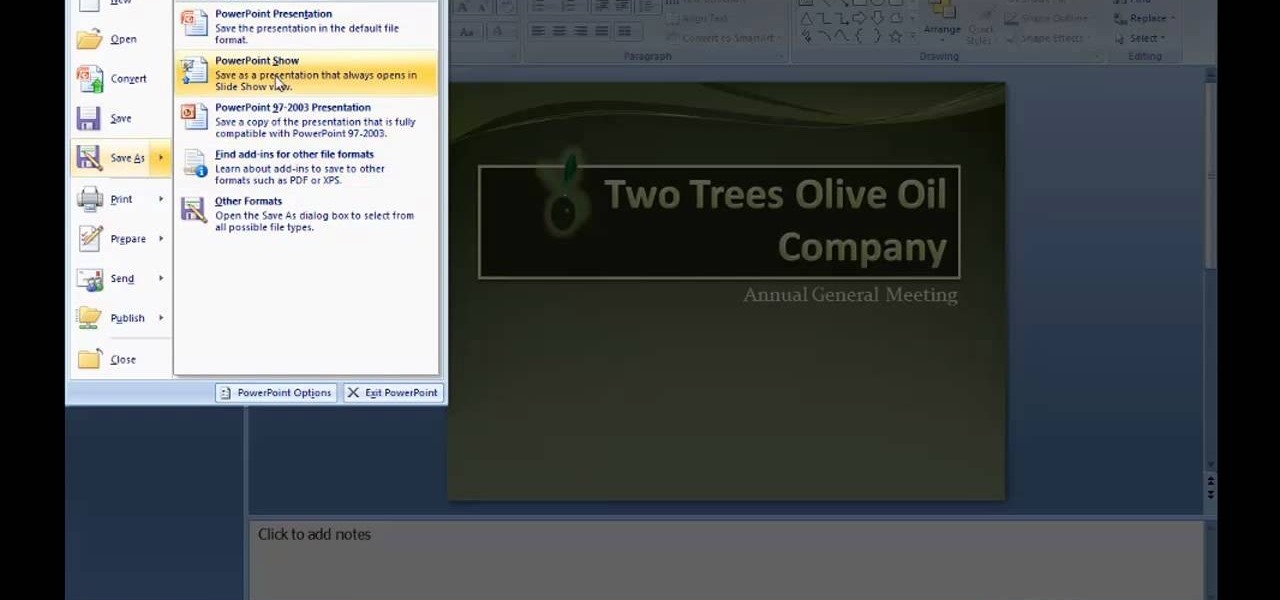
There are many new features which will make you more comfortable in doing your work in PowerPoint 2007 which will force you to switch from PowerPoint 2003 to PowerPoint 2007. There are number of new features in PowerPoint 2007.