With a simple social engineering trick, sudo passwords can be captured in seconds without the target's knowledge. The passwords can then be saved to a file or exfiltrated to another computer on the network.

There's a lot of misinformation about VPN services, and it stems from the fact that not all of them are created equal. Some focus on privacy, others on security, and a few VPNs are seemingly even purpose-built for the polar opposite: data collection. We made this guide to help clear the air on some of these issues while objectively ranking the best of the best.

Every step in the evolution of computing brings an in-kind leap forward in user input technology. The personal computer had the mouse, touchscreens made smartphones mainstream consumer devices, and AR headsets like the HoloLens and the Magic Leap One have leveraged gesture recognition.

Directory traversal, or path traversal, is an HTTP attack which allows attackers to access restricted directories by using the ../ characters to backtrack into files or directories outside the root folder. If a web app is vulnerable to this, an attacker can potentially access restricted files that contain info about all registered users on the system, their permissions, and encrypted passwords.

Apple released iOS 12.1.3 beta 4 to software developers on Thursday, Jan. 10, just three days after beta 3 came out. Public beta testers also received the update. In general, iOS 12.1.3 fixes a VoiceOver issue with ECG and Irregular Heart Rate notifications, as well as a fix in audio quality on the latest iPad Pro models.

The Federal Communications Commission (FCC) has cleared a path for Google to move forward with hand-tracking technology that could pose a major threat to Leap Motion.

First, there was SnapCat. Now, we have DogChat! Or SnapBark? In October, Snapchat took social media by storm with its Lenses for cats. But the latest addition to the camera app has given dog lovers an augmented reality Christmas gift they won't want to return.

Users are often the weakest link when probing for vulnerabilities, and it's no surprise they can be easily fooled. One way to do this is called clickjacking. This type of attack tricks the victim into clicking something they didn't mean to click, something under the attacker's control. Burp Suite contains a useful tool called Clickbandit to generate a clickjacking attack automatically.

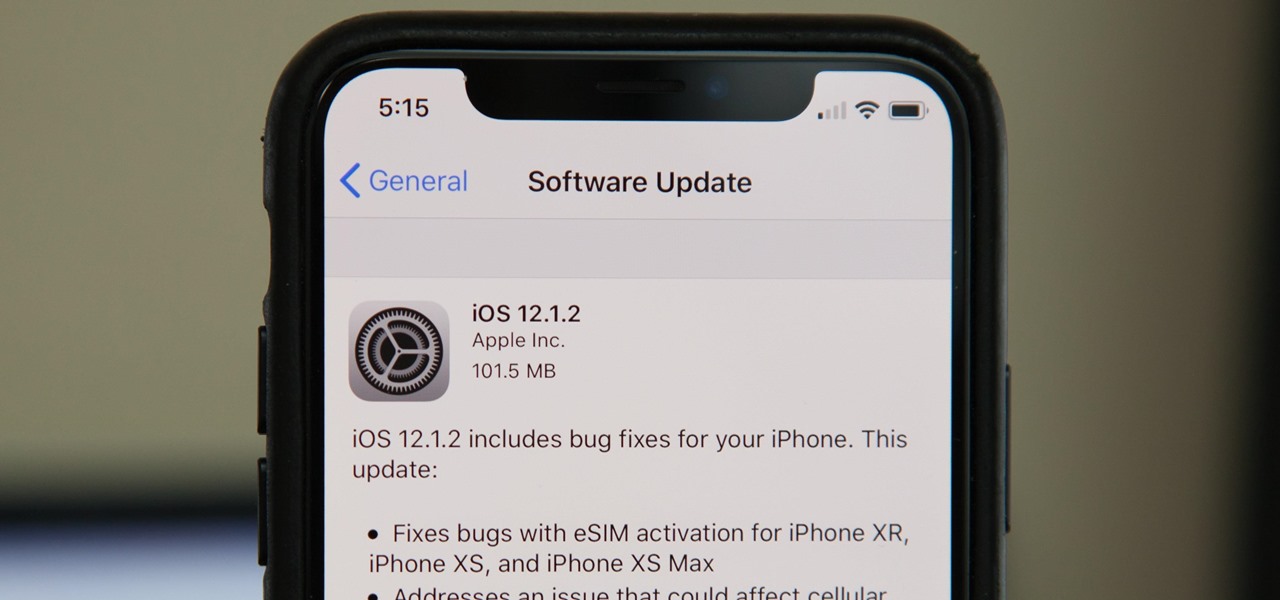
Without a second beta like most other beta versions, Apple released iOS 12.1.2 to all iPhone users on Monday, Dec. 17. The update comes just one week after the iOS 12.1.2 beta went live, so why did it have such a quick turnaround? The answer likely revolves around eSIM issues on newer iPhone models, as well as legal issues with Qualcomm.

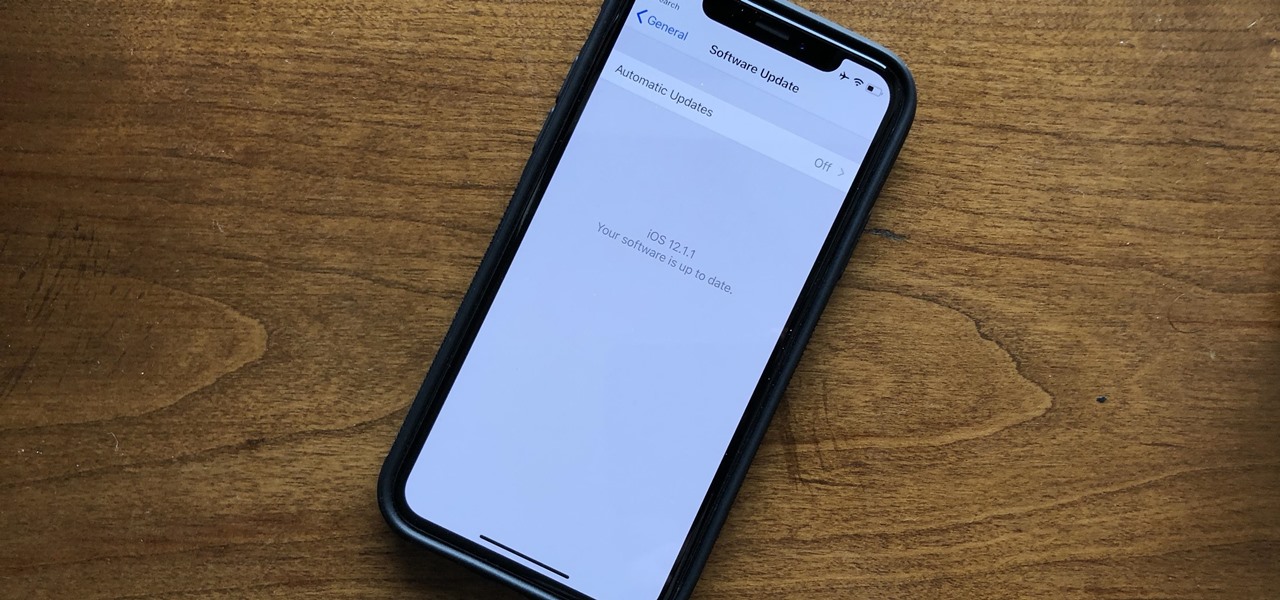
Apple released the latest update for iPhones, iOS 12.1.1, on Wednesday, Dec. 5. It introduces a few new features to iOS 12 as a whole. The software has been in beta testing since Halloween of this year, spending just over one month in the hands of beta testers.

When computers have vision but people don't, why not have the former help the latter? That's the gist behind the Cognitive Augmented Reality Assistant (CARA), a new HoloLens app developed by the California Institute of Technology.

With barely a whisper of augmented reality during the first day of its developer's conference, Samsung came out swinging on day two with the introduction of its version of the AR cloud and a partnership with Wacom that turns Samsung's S-Pen into an augmented reality magic wand.

The dream of Google Glass lives on via North's stylish and normal-looking smartglasses that bring text messages and navigation prompts into the user's field of view and Amazon Alexa integration for voice-activated assistance.

Microsoft has informed HoloLens users that the company will begin rolling out a mandatory update for HoloLens as part of its Windows 10 October 2018 release that brings a number of new features and quality-of-life improvements to the headset.

Good news for beta testers — Apple released iOS 12.1 beta 4 to public testers Monday, Oct. 15. The update comes just hours after the company seeded beta 4 to developers and only six days after all beta user received iOS 12.1 beta 3.

It only takes a few commands to manipulate a MacBook's secure HTTPS traffic and pluck login passwords out of the encrypted data. Let's take Facebook and Gmail hacking to the next level by intercepting Safari and Google Chrome web traffic in real time.

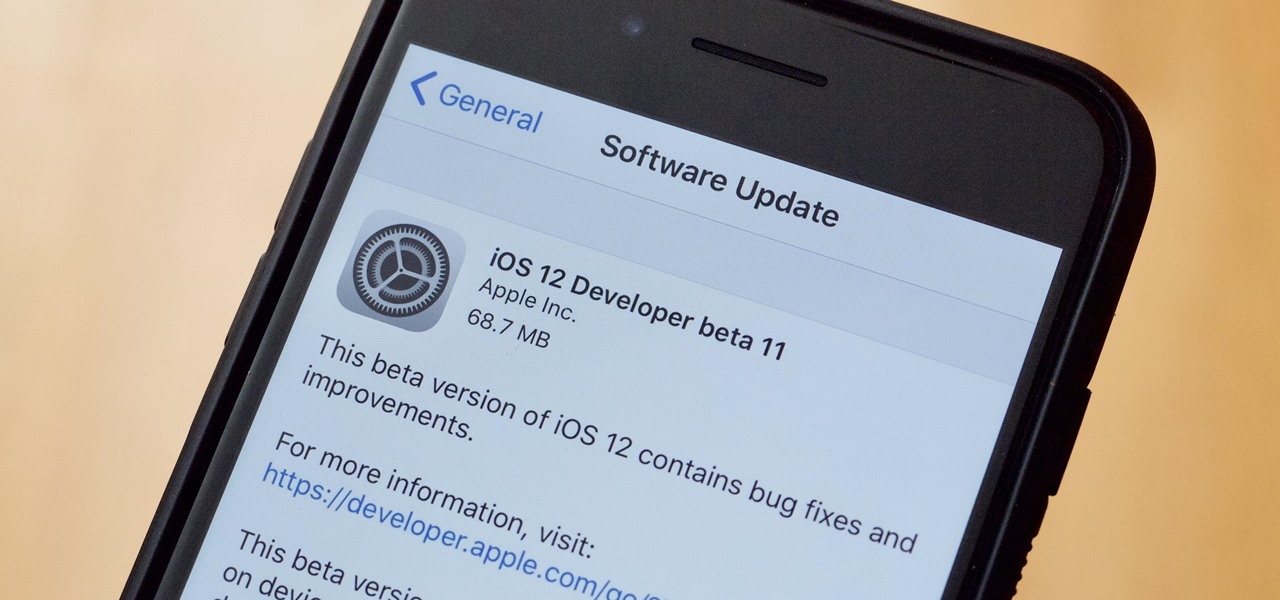
Apple released the eleventh developer beta for iOS 12 to registered software testers on Monday, Aug. 27, only four days after the company unexpectedly released both dev beta 10 and public beta 8. Apple has ramped up its beta release schedule as of late, offering minor updates twice a week in the lead-up to iOS 12's official debut in a few weeks.

It looks like Snapchat is becoming the MTV of augmented reality. On Thursday, Ariana Grande, with her new album Sweetner, joined Drake and Nicki Minaj and other artists who are pushing new releases through Snapchat's Shoppable AR e-commerce platform.

To promote Battle of Azeroth, the latest expansion for the World of Warcraft franchise, Blizzard Entertainment has conjured a Shoppable AR Lens that is now available in Snapchat's app carousel.

Computer vision company Blippar has already dabbled with outdoor AR navigation, but now it wants to make it easier for people to make their way through indoor spaces with augmented reality.

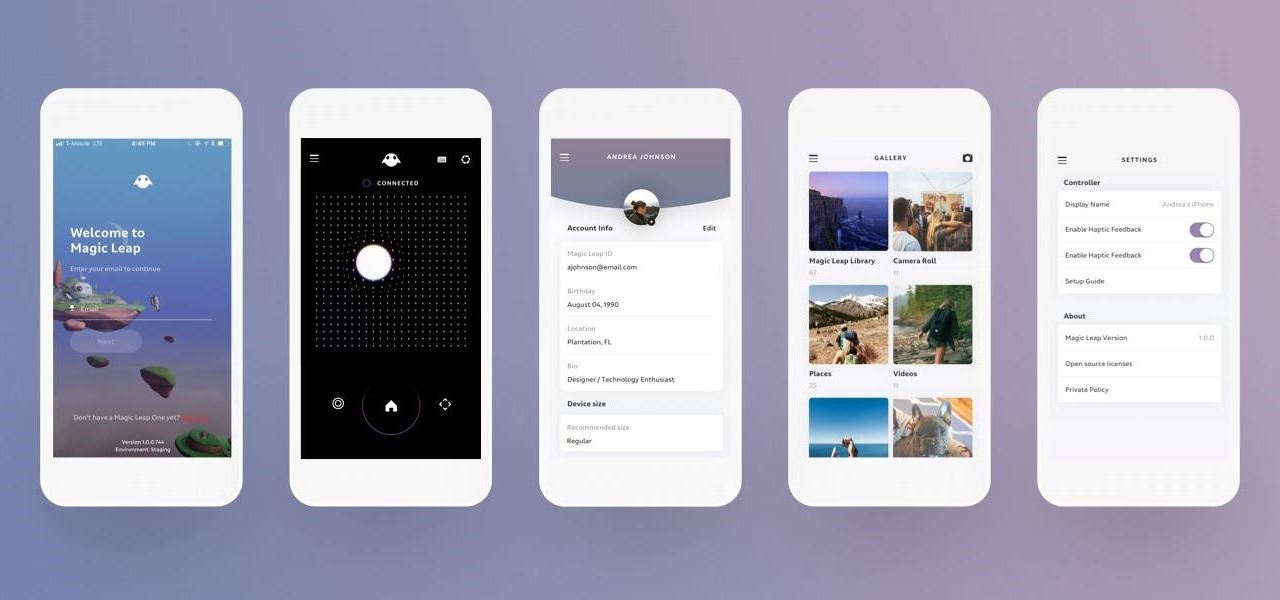
Among a treasure trove of new developer information on the Lumin OS that Magic Leap recently published on its Creator Portal appears to be the official confirmation of the Magic Leap Mobile Companion App.

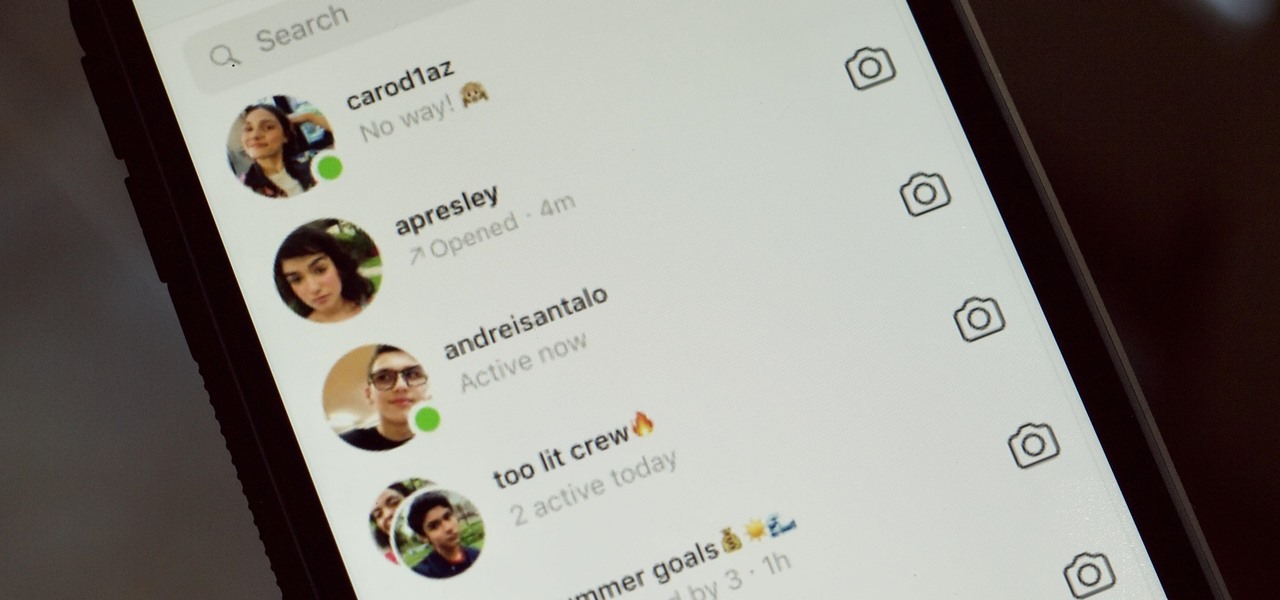
While it might be more common to chat with friends on apps like Twitter, Messenger, or WhatsApp, direct messages on Instagram are becoming more and more sophisticated. Case in point, the app is rolling out a new feature to users that shows a "green dot" next to friends who are online. Luckily, you don't have to let your followers know when you're browsing photos if you don't want to.

Voice-activated digital assistants from Amazon, Apple, and Google currently have the upper hand for home automation integrations, but a new augmented reality mobile app promises to give homeowners and renters visual control over their connected appliances.

Another entrant into the do-it-yourself AR content creation market has emerged, as Zappar has updated its ZapWorks Studio software to include features for development newbies.

With the 2018 FIFA World Cup underway in Russia, soccer (aka "football") fans worldwide can show support for their favorite teams and players in augmented reality via Snapchat and Facebook.

There's always an iPhone in our list of top phones for privacy and security, due in large part to advanced security measures like Face ID, consistent iOS updates, and easy ways to prevent unwanted access and excessive data sharing. However, some of those options actually do the opposite and hinder security. It all depends on how you use your iPhone, but you should at least know everything available.

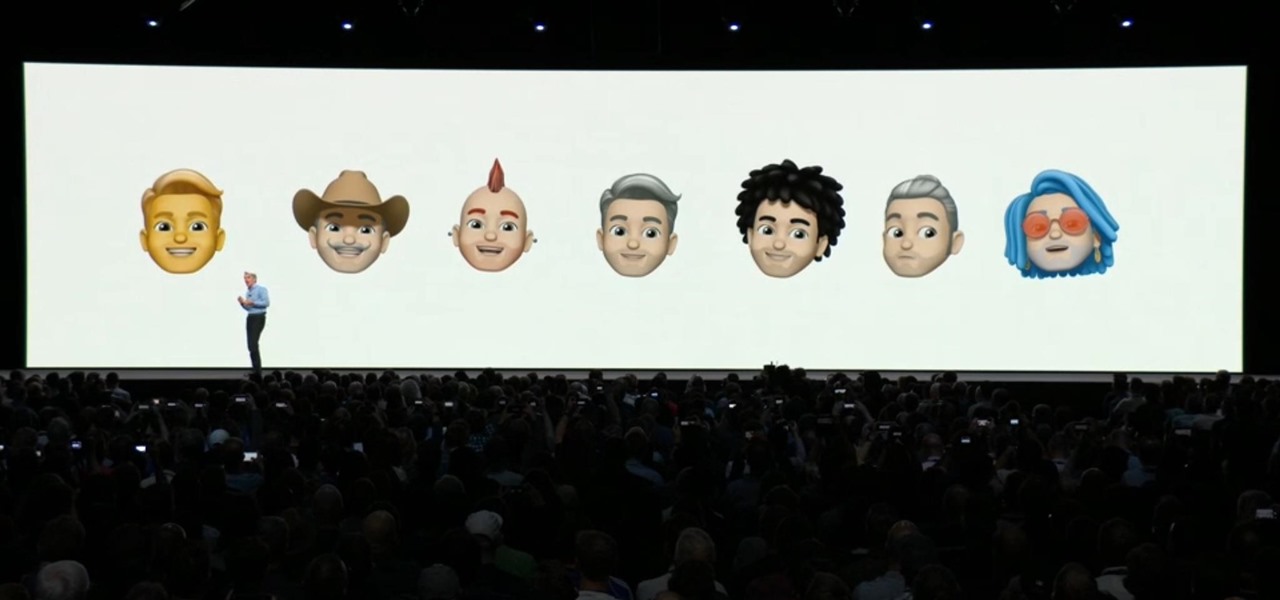
Alongside ARKit 2.0, Apple revealed new Animojis alongside new Memoji virtual doppelgangers that compete with functionality quite similar to that of Samsung's AR Emoji.

This time last year, computer vision company uSens introduced a stereo camera module capable of hand tracking. Now, uSens can achieve the same thing with just a smartphone's camera.

As Facebook, Apple, Samsung, and others offer augmented reality selfie effects and content that challenge its platform, Snapchat has continued to innovate with its augmented reality capabilities.

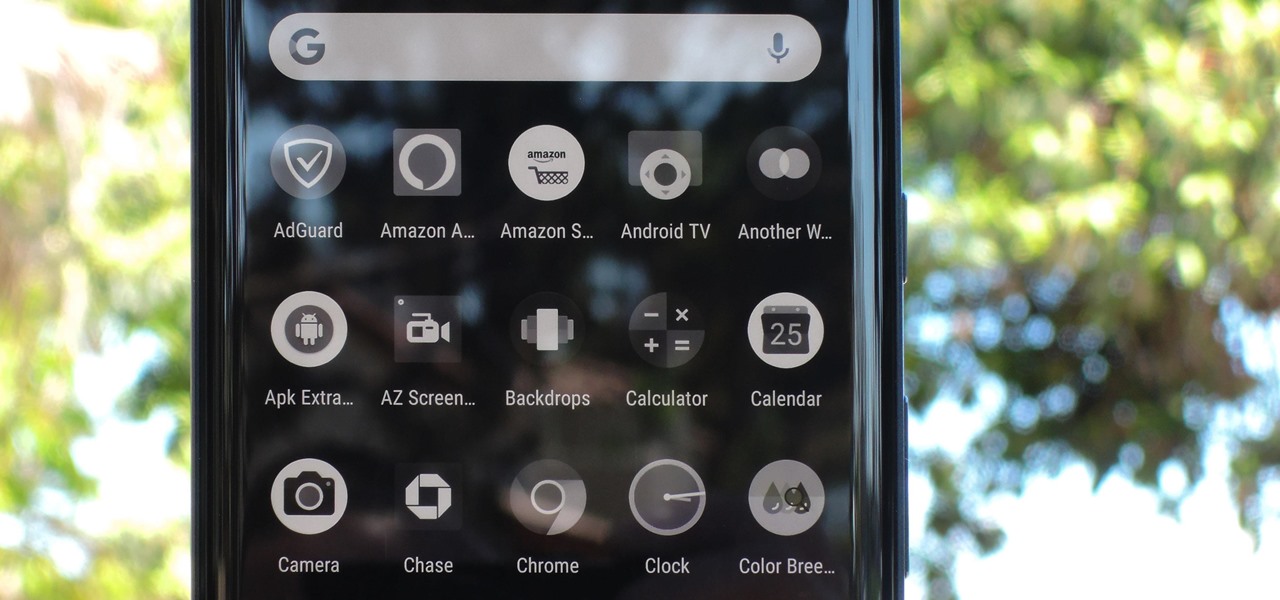
Thanks in large part to our phones, many of us don't get the recommended eight hours of sleep. In Android Pie, Google introduced a feature called "Wind Down" that aims to help combat this. However, thanks to a creative app developer, we don't need to wait for Android 9.0 to enjoy this feature.

It will likely take a few more years before smartglasses are ready for primetime as component makers achieve the innovations necessary for consumer-centric device designs. Nevertheless, two technology companies are making steps in that direction as Qualcomm is rumored to be working on a chip dedicated to AR & VR headsets, while DigiLens has reduced the size of its waveguide displays for motorcycle helmets.

New Balance is helping Liverpool Football Club (FC) fans see how they look in the team's new kits with an augmented reality experience in Snapchat.

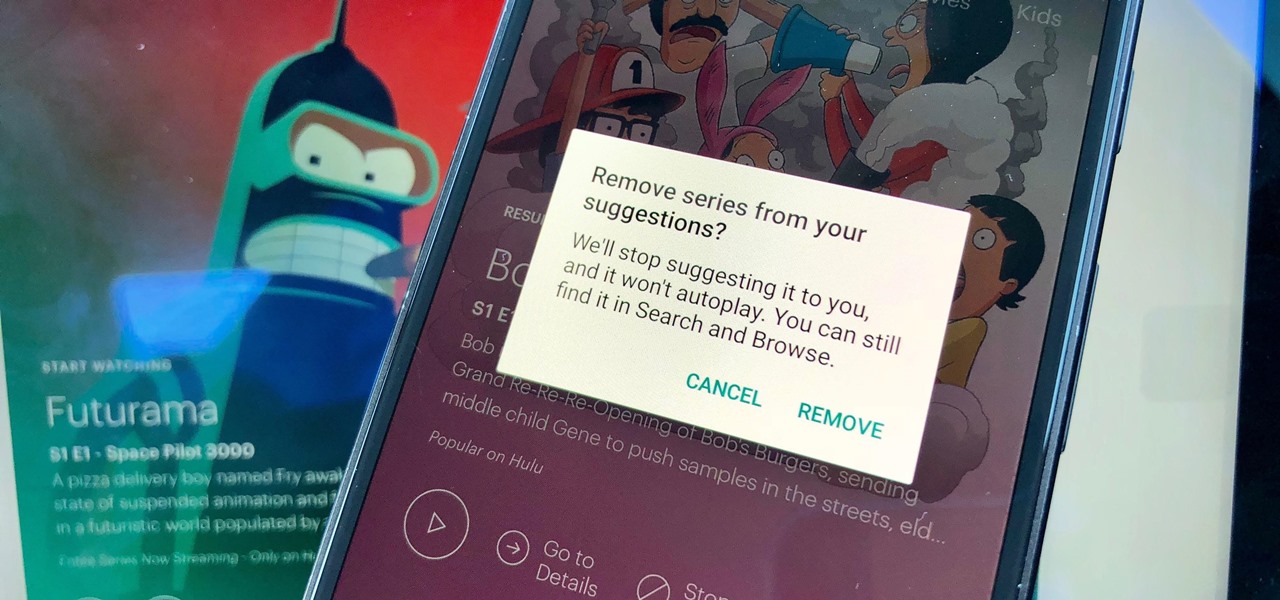
Hulu has a lot of content — with thousands of movies and TV series, there's bound to be a few titles here and there you simply don't like. If Hulu is inexplicably recommending garbage you don't want to watch, there's a new way to stop that from happening.

Thanks to its intuitive interface that makes sending and receiving money a breeze, Venmo has become the go-to app for millions in the US. In fact, you've probably heard the term "Venmo you" being tossed around between friends. But before you take the plunge and sign up, it's always a good idea to read the fine print and know what you're getting into. Money is involved, after all.

On this, the most cherished day for Star Wars fans, May the fourth, Lenovo has released a significant new update to its Star Wars: Jedi Challenges app: real person versus person lightsaber battles.

French automaker Renault is tapping into the promotional machine for Solo: A Star Wars Movie by deploying an AR experience through Shazam that's triggered via synergistic advertising.

Beginners learning brute-forcing attacks against WPA handshakes are often let down by the limitations of default wordlists like RockYou based on stolen passwords. The science of brute-forcing goes beyond using these default lists, allowing us to be more efficient by making customized wordlists. Using the Mentalist, we can generate millions of likely passwords based on details about the target.

Another AR cloud candidate has emerged in YOUAR, a startup that has developed a new system that enables persistent augmented reality experiences on iPhones and Android devices.

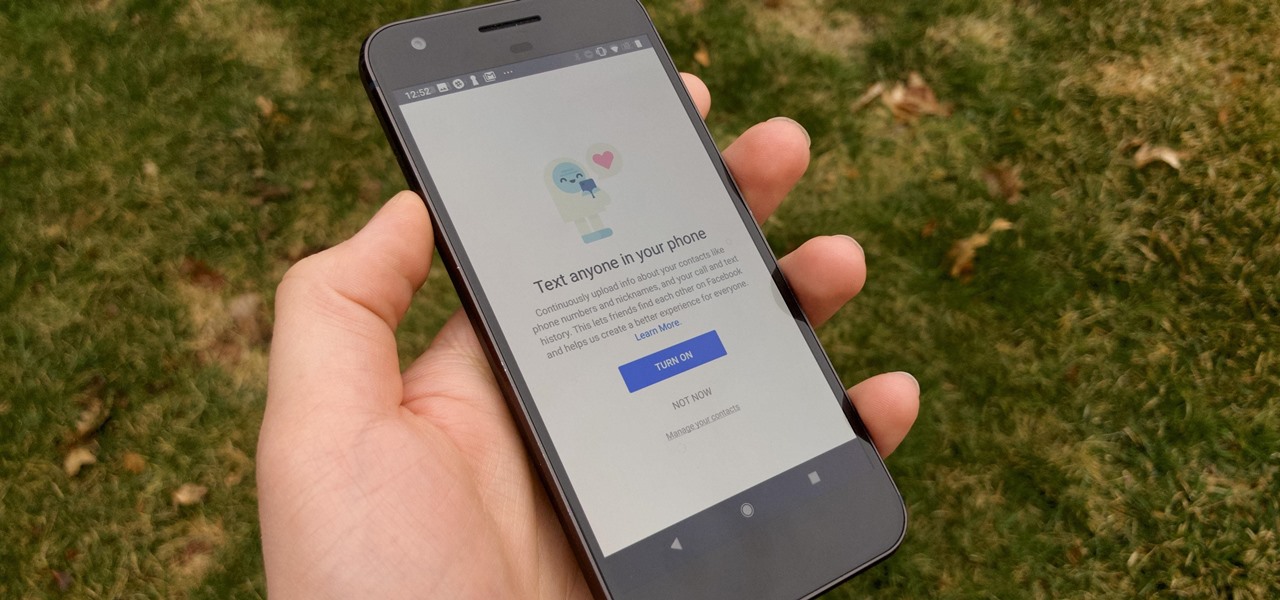
It hasn't been a great year for Facebook. Recently, Android users had to discover on their own that the company was logging their calls and texts in Messenger. However, according to Facebook, all users did approve of the data collection, and as such, all affected users can disable logging as well.

Space might be the final frontier, but NASA is making a detour into augmented reality first. The Spacecraft AR app, developed by NASA's Jet Propulsion Laboratory (JPL) in collaboration with Google, debuted exclusively for Android this week (an iOS version is also in the works).