
How To: Secure kitchen cabinets for an earthquake
This video will give you tips on how to secure your cabinets so that things don't come flying out of them in the event of an earthquake.


This video will give you tips on how to secure your cabinets so that things don't come flying out of them in the event of an earthquake.

A tutorial on how to secure and configure a WRT54G Linksys router and also the steps needed to get default passwords and the list link.

Tim Carter demonstrates one technique to secure any book shelf or book case. Great video to learn how to safely secure a bookshelf.

Secure a bookcase without drilling holes in the furniture. Use velcro! Mark the top of the cupboard or bookcase first.
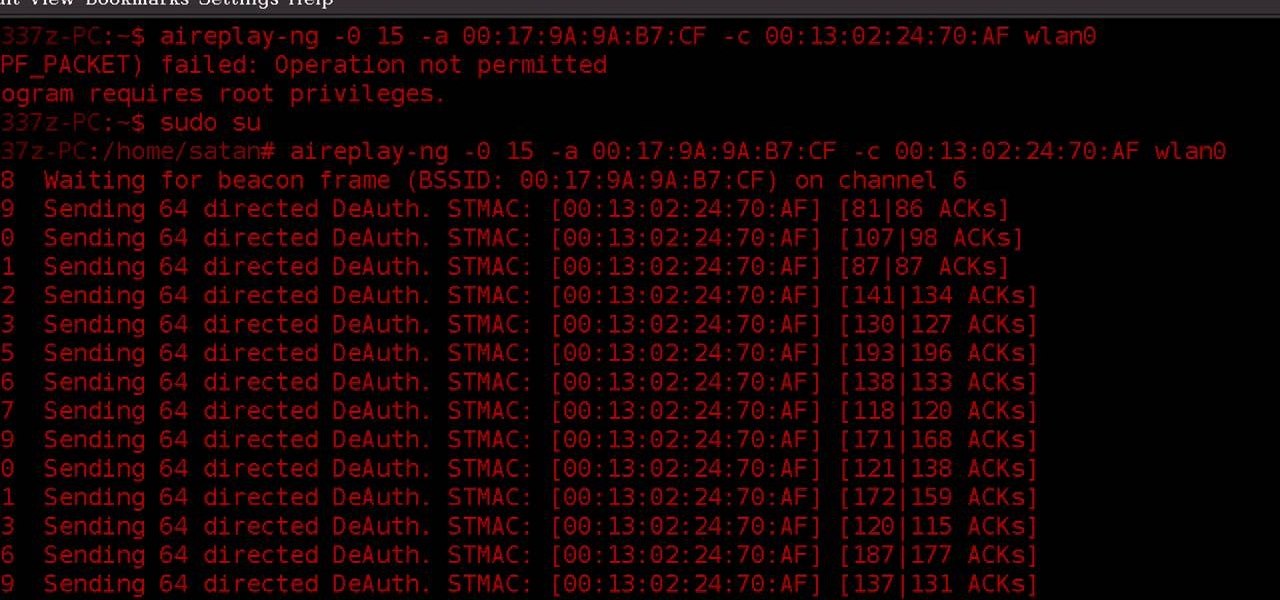
WPA-secured wireless networks, or WiFI Protected Access, is a form of internet security that secures your wireless LAN from being accessed by unauthorized users. Safer than WEP, or wireless equivalent privacy, WPA still has weaknesses that are prone to cracking - IF, that is, you know what you're doing.

Millions of laptop batteries have been recalled because of the risk of FIRE. Get some tips from CNET to learn how to keep your laptop battery safe and secure. First, make sure your battery hasn't already been recalled. Second, don't leave the laptop constantly charging because it heats it up. One way to save your battery is to remove it completely when you plug in directly. Third, treat the battery as fragile. And finally, four, avoid buying knockoff batteries.

If everyone in the world properly secured their email account there would be no spam. But yeah… never going to happen. That's more of a reason to encrypt and digitally sign our emails, but isn't using p2p security really expensive and really hard? Nope. It's actually free and easy with GnuPG. It's demonstrated on Mac OS X, but it's just as easy with Windows.
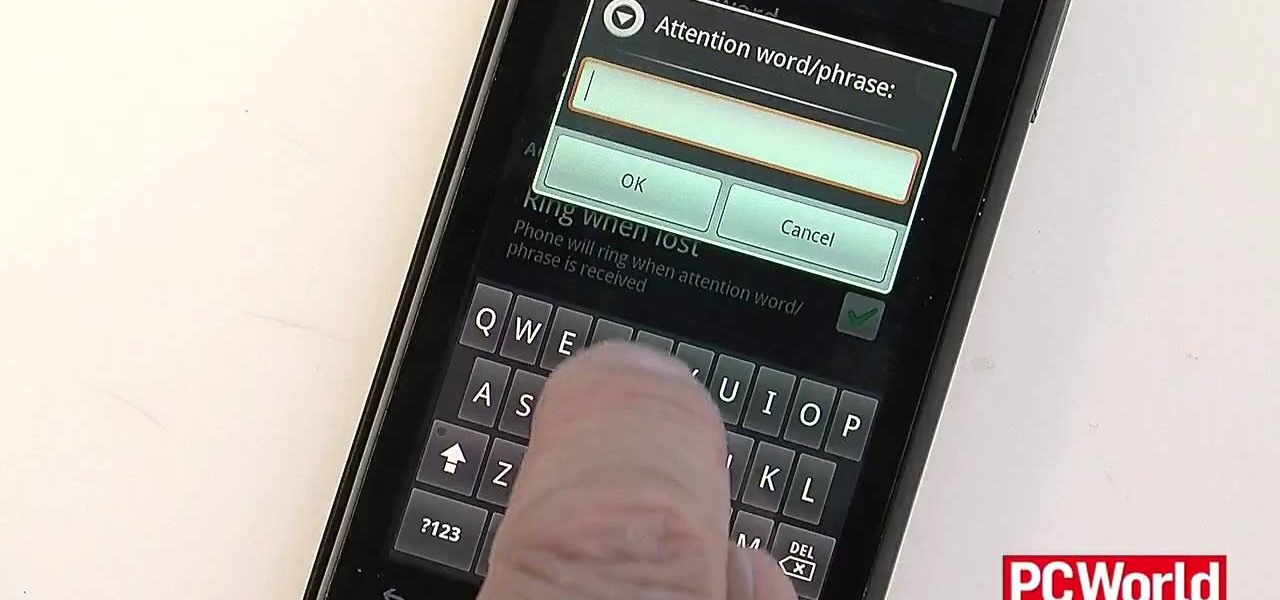
If you've spent a ton of money on your newest smartphone, you will want to make sure it's secure. In this tutorial from the experts at PCWorld, learn exactly how to activate safety mechanisms on your Android. With these options you can set a complicated passcode (so that anyone who does find your phone won't be able to access your files) and you can also set up a locator. By using the location app, you can text your phone from anywhere else and set off a search alarm so you will be able to fi...

This video tutorial shows you how to use a long wrap product to dress yourself while creating a secure carrier for your baby. The long wrap is brought forward from back to front and round your belly button, criss-crossed over your back and brought forward and criss-crossed once more, then tied. The two criss-crosses (in the shape of an X) help hold the babies legs, as the pass through the criss-crosses and support the baby. You should then try to bring the fabric down as far as possible to su...

Hak5 is at it again, with a plethora of somewhat accessible solutions to your technological problems. If you've ever needed to get through your school's firewall, or secure traffic tunneling, or try out applications in a fast, efficient manner? This video has it all and more.

If you want to transfer files to or from your iPhone at ease, check out this video on how to SSH / SFTP into your iPhone. SSH (Secure Shell) and SFTP (Secure File Transfer Protocol) all can be used to safely transfer files to your iPhone!

There's a new trend on Instagram Stories: People are making viral AR filters where images of popular characters from TV shows, movies, and other mediums shuffle above your head until one sticks. The filters range from Disney and Pokémon characters to Harry Potter and Friends, but you're not limited to just that because you can create your own "which are you?" filter.

In keeping with its focus on loading the Magic Leap One with content at launch, Magic Leap has inked a creative partnership agreement with augmented reality production studio Square Slice Studios.

These days, that pocket-sized computer we call a smartphone is home to your entire digital life. But with the onset of mobile payments and online banking, the line between your virtual world and the physical realm is becoming increasingly blurred.
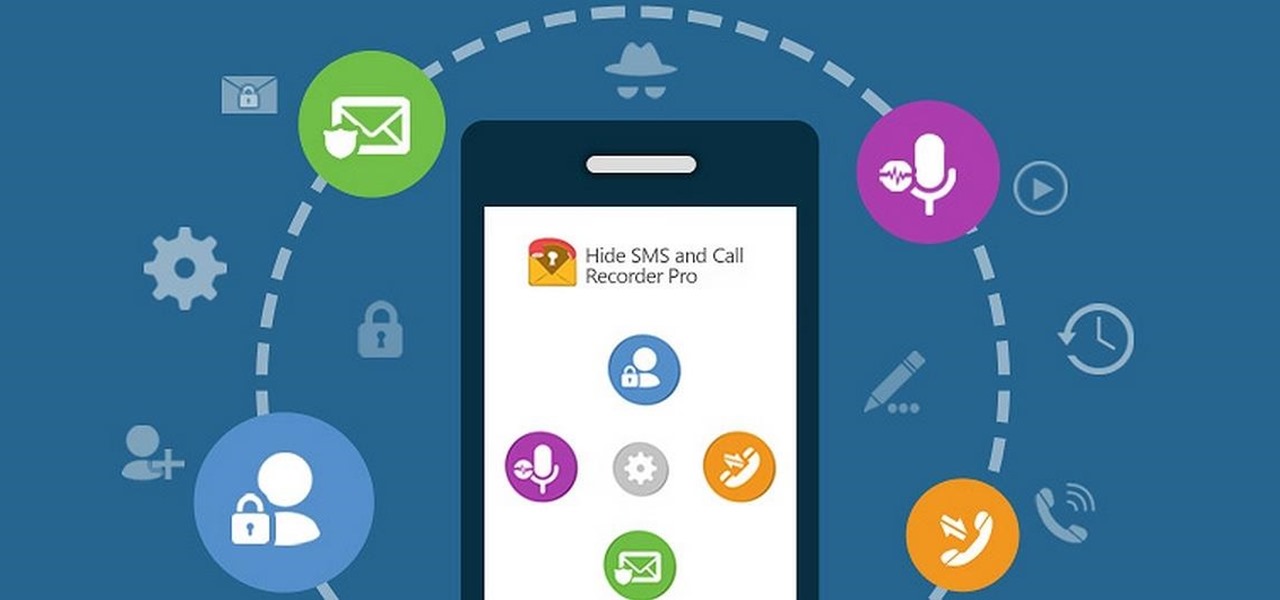
Some people are of extremely secretive nature. They do not like sharing their personal events in their lives with anyone. Thus people around that person wont be able to figure out details on their life's personal matters. It is not like they want to hide some mysterious secrets from the world, but it is just their nature that they do not want others to know much about them or are too shy to share their feelings with others. Being secretive is neither good nor bad, it is just how they are.

This video will show you how to secure your GoPro camera to your motocross, Snowmobile, Motorcycle, Skiing helmet so that it will not loosen up and fall off.

This video will explain how to safely weight down and secure a basket ball hoop with a water filled base that has a hole in it.

Every day it seems like new information comes to light about how the National Security Agency creeps into our lives. Knowing that they can backdoor into our seemingly private devices is a scary thought, whether you have information to hide or not.

Julia, AKA Hairbeauty4you, gives detailed instructions on how to do a quick half up-do with a twist in under 10 minutes. She notes that this style is best for medium to long length hair. Julia starts with straight hair, then sections off the top part and clips temporarily. She then separates another section on either side of the top part- from the ear to the clipped section- and pulls it back into a high pony tail and repeats identically on the other side, securing each with clear rubber band...
In this video, we learn how to install dry acoustic flooring with Fermacell. To start, you will level the floor and apply compound if you need. Next, you will lay the Fermacell around the room on top of the leveling compound. Push the flooring tightly together so there are no spaces in between them. You may need to cut the flooring to make sure it's the correct shape for the wall. After this, apply flooring adhesive to the seams to make sure they are secure as they are laid down. After this, ...

In this video, we learn how to use secure online passwords. There are a ton of things to consider when creating a password. A weak password is something that someone can easily guess. If you are using a birthday, common dictionary word, child's name, or something common then you are at risk. Your password should combine letters and numbers, and be at least eight characters long. It should also be completely random and have upper and lower case letters. You can use a password assistant if you ...

The way to wear hijab shown in this demonstration with a simple wrap around the head, securing the hijab with bobby pins at the back of the neck. The ends of the hijab are pulled forward to the chest. Then a thin scarf in a contrasting color can be wrapped around and tied at the nape of the neck as well. A portion of the hijab is pulled forward over it and pinned over the ear. Then one of the ends is pulled under the chin to the opposite ear and pinned to the head. The other end is wrapped ar...

Several Tanzanian girls demonstrate how to tie a kanga (an African sarong). The first method is to wrap the kanga around the waist and tuck the end in at the waist to secure. The second method is to wrap the kanga into a cylinder to use it as a base for carrying a parcel on the head. Another way to wear the kanga is to wrap it around the neck like a shawl or wrapped under an armpit and tied over the shoulder for a fancier look. To wear the kanga as a scarf, fold it into quarters the long way,...

To create an apostolic or pentecostal hairstyle, start with a poof in the front of the hair. It can be ratted behind for stability. Use two bobby pins to secure the back corner of the poof. Squirt the hair with hairspray before moving on. Then create a low ponytail in the back of the hair, pulling the top up and out slightly while forming the ponytail so it creates another poof in the back of the head. Spray the ponytail with hairspray then smooth out the hair on the top of the ponytail. Wrap...

This video illustrate us how to make a light bulb oil lamp. Here are the following steps; Step 1: Take all the things required that is bulb, socks,adhesive tape,scissors,kerosene, rim with a hole in the center.

In order to secure a PDF with a password when opened in Adobe Acrobat 9 Pro, press the secure button and go into password security settings. Here you can change on what versions of this software the file will run on, the next option asks which portion of the document is to be encrypted when a password is placed. Further below here is where you actually choose the password, this ensures that only people who know the password will be able to see the contents of the document. Below this is the d...
Securing Microsoft Office Word 2007 documents with Digital Signatures - When you receive a document that has been signed by someone you know, you are more likely to trust the contents than those of a document that has not been signed, or has been signed with an unfamiliar signature. Signing a document validates it to someone who recognizes your signature, now add the same degree of integrity to your documents in Microsoft Office Word 2007 thanks to the new Digital Signatures feature. For more...

GameGuru was created for game enthusiasts who are not programmers or designers. By offering catalogs with thousands of royalty-free assets, GameGuru lets design novices bring their visions to life.

While sheltering at home orders are lifting, companies are still conducting most business online. Case in point, hackers have been having a field day over the last few months. Securing your identity has always been important, but never as much as it is at this moment.
Have you ever seen pictures or videos of balloons being let go into the sky and randomly floating away in all directions? It's something you often see in classic posters or movies. Well, guess what? Now you'll be able to do that without having to buy hundreds of balloons, all you'll need is ARKit!

This half-hour episode of Hak5 covers several topics: Using a DSLR camera to create HD footage, building your own Google TV, unlocking & copying locked files with Lock Hunter, using PicPick for screen capture, using WinDirStat for analyzing & cleaning your hard drive, setting up a secure FTP server with Ubuntu Server, and secretly copying data from USB drives with USB Dumper.

Justice might not have produced any new material in a while, but their place in electronic music history is already secured due to their filthy electro-house beats that have become ubiquitous in the years since they first broke out. Watch this video to learn how to make a dirty electro bass synth line like theirs in Reason 4.

The Lab Rats, Andy Walker and Sean Carruthers, explain Media Access Control (MAC) addresses. Filtering MAC addresses allow you to very specifically control access to your wireless network.

Tie a clove hitch knot again, again, and again.

In this two-part tutorial, J. Schuh demonstrates how to animate a flying bird using Illustrator and Flash. In Part 1, he goes over the process of creating the vector assets in Illustrator. In Part 2, he brings the illustrator assets into Flash to animate the movement of the wings. For more information, including detailed, step-by-step instructions, watch this free video software tutorial.

You don't want anybody to have access to your cell phone. Nobody. Well, instead of the standard unlock mechanism, the one anybody can unlock your cell phone with, the Motorola DROID, and Android enable mobile device, allows you to create your own unlock pattern, secret to anyone else, which wakes it from sleep mode. Best Buy has answers. The Best Buy Mobile team explains how simple it is to set up a secure lock on a Motorola DROID cell phone.

In order to begin, you will need the following: Three hair tiesBobby pinsHair spray or spray gelRat tail combHair net
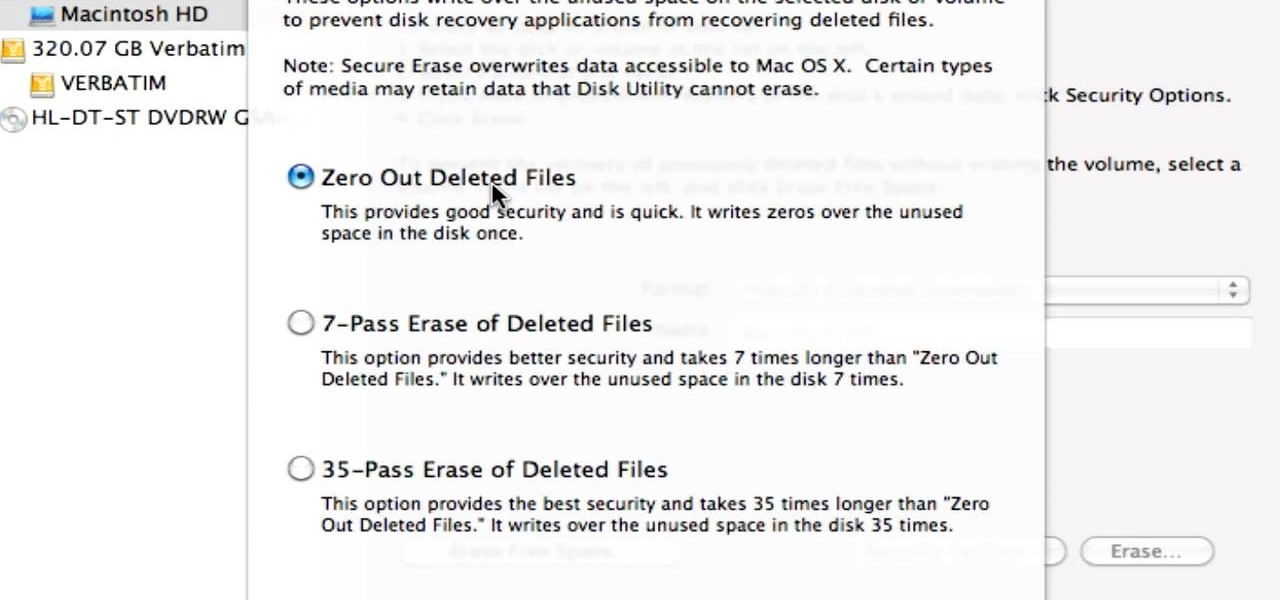
Did you know that even after you've emptied your Mac's trash can, the data still has not been permanently removed from your system? Anyone who knew where to look could easily unearth this data. You can prevent this by using the secure empty trash option on your Mac. Whenever you put something in the trash, instead of pressing delete, go into 'finder' up top and press 'secure empty trash'. What this will do is replace the data that is left behind on your hard drive with random ones and zeros. ...
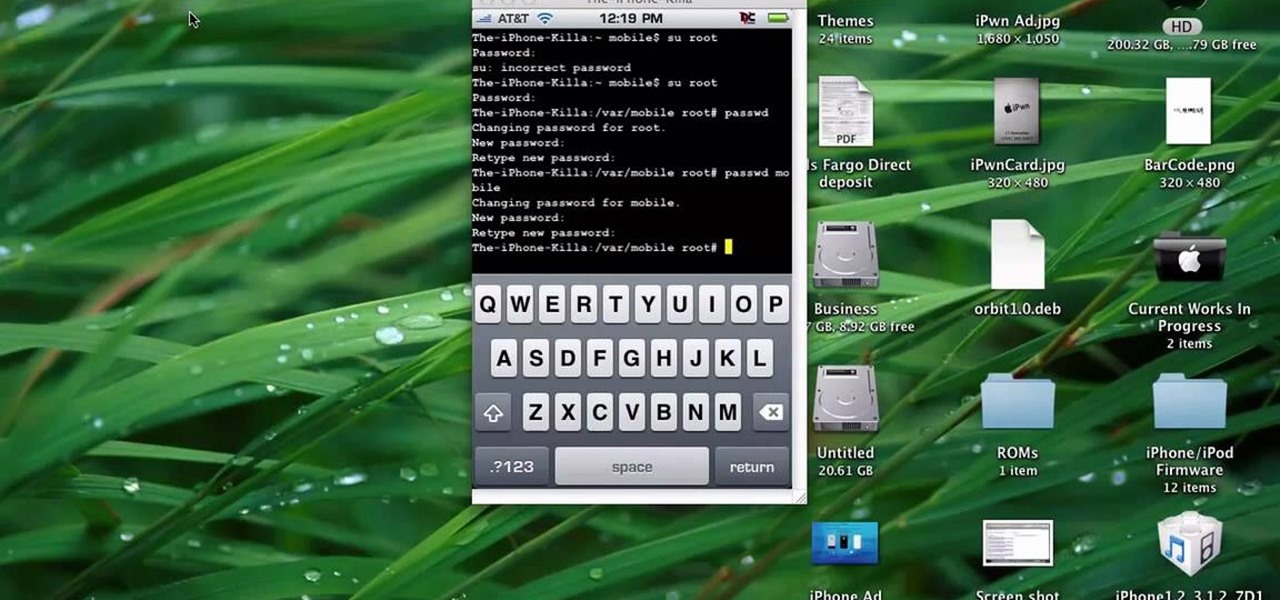
This quick tutorial runs you through a fast and easy way to make your iPhone or iPod Touch more secure. However the best security is abstinence. Just don't run the programs that leave your devices vulnerable unless you need them.

The UK has officially exited the European Union, completing the long and tumultuous Brexit story and putting the storied nation once again on its own on the international stage.