Protect your email account from would-be hackers and crackers with this free video tutorial from the folks at MacMost. If you have a Gmail, HotMail, Yahoo! Mail or other web-based email account, this video is much recommended. For more information, and to secure your own online free email account, watch this helpful guide.
Board Games With Scott presents the boardgame Settlers of Catan. Scott talks about how to play the popular board game and covers some strategy for securing the win.

Learn how to tie a Tack Knot - a secure way of attaching a rope to a fixed object such that it won't come undone even if shaken and flogged. This is a fine knot for camping, climbing, sailing or Boy Scout training.

Learn how to tie an Anchor Hitch (also known as a Bucket Hitch) - A very secure means of attaching a rope to an anchor or any other object that you can't afford to loose (like a bucket down a well, I suppose - thus the alternate name). I actually do use this hitch for temporary anchor attachment (preferring to permanently splice instead) as well as for my bucket lanyards when washing down my boat's deck.

Learn how to tie a Draw or Thief Hitch - a means of securing a rope with two standing ends - one end is load bearing, and the other can be pulled to release the knot. I used this knot extensively for raising the mast on my first trailor-sailor - Tie this above the spreaders, stand the mast up, then pull on the release line to untie it without having to climb aloft. This knot can be used in sailing, boating, general use, camping and bondage.

This video shows you how to tie a Thief Knot. This knot looks a Reef Knot to the casual observer and so can be used to determine if a thief is tampering with your belongings bag - secure it with a Thief Knot, and if you find it re-tied with a Reef Knot, you know someone has been messing with your stuff. This is used in sailing, boating, general use, camping and bondage.

Jared of the TechCentric crew gives you the lowdown on the basics of keeping your VoIP conversations secure and, on the other side of things, how to use the Cain VoIP sniffing application. For detailed instructions on keeping your VoIP conversations private, watch this hacking how-to.

Mike Lively of Northern Kentucky Universtiy demonstrates how to grab a website's resources for reconstruction in Flex using HTTRACK and Wireshark. This tutorial is especially helpful for sites you want to grab that think they are very locked down and secure. All with the free softwares HTTRACK and Wireshark.

Battlestations: Midway for the XBox 360 takes place at the very start of America's involvement in World War II, beginning with Pearl Harbor. Take a look at this instructional video and learn how to win the Battle of Tulagi and secure the strategic islands with these tips from G4TV.

Watch this quick instructional cinematography video that shows how to balance a Canon XL2 professional HD digital camera on a GlideCam 4000 Pro. Learn how to secure the camera using this handheld camcorder stabilizer to prevent unwanted swaying, shoot fluid traveling shots, and produce professional works.

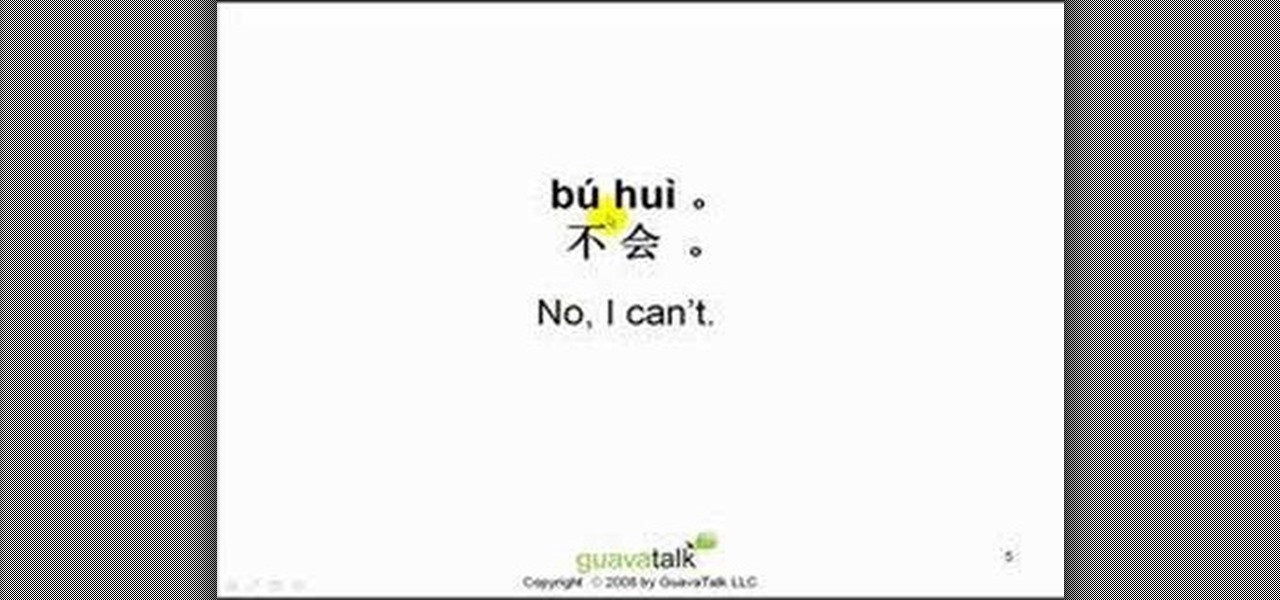
If you can find people who speak English in China, you'll probably get where you want to go faster. Memorize this basic Chinese phrase and feel a lot more secure once you get to China!

This knot is common in the climbing world. We use it to secure two ropes together. Often used to form a loop on a prussik (cordalette) to construct an anchor. Can also be used to connect two ropes to rappel. This knot has many applications in the real world not just climbing.

In this tutorial, we learn how to make your home safe and secure with tips from Lowe's. You should do a safety check on your house at least once a year. Start with the entryway, making sure you have an insulated wood door in the doorway. Make sure there is a lock and a deadbolt lock on the door as well. Once inside, make sure you have timers to control your lighting, so it can come on even when you're not at home to detract any robbers. In the garage, make sure you have an electronic door ope...

In this video, we learn how to do some easy hairstyle for school. To do an easy bun, take a hair tie and put it in the hair in a side twist bun. Let some of the hair stick out, then take bobby pins and stick them in the bun to secure it, then you're done! The next look requires you to take your bangs and braid them together. After this, pull the braid behind your head and secure it with a bobby pin. The next look requires you to braid a section on the side of your hair, then put it into a pon...

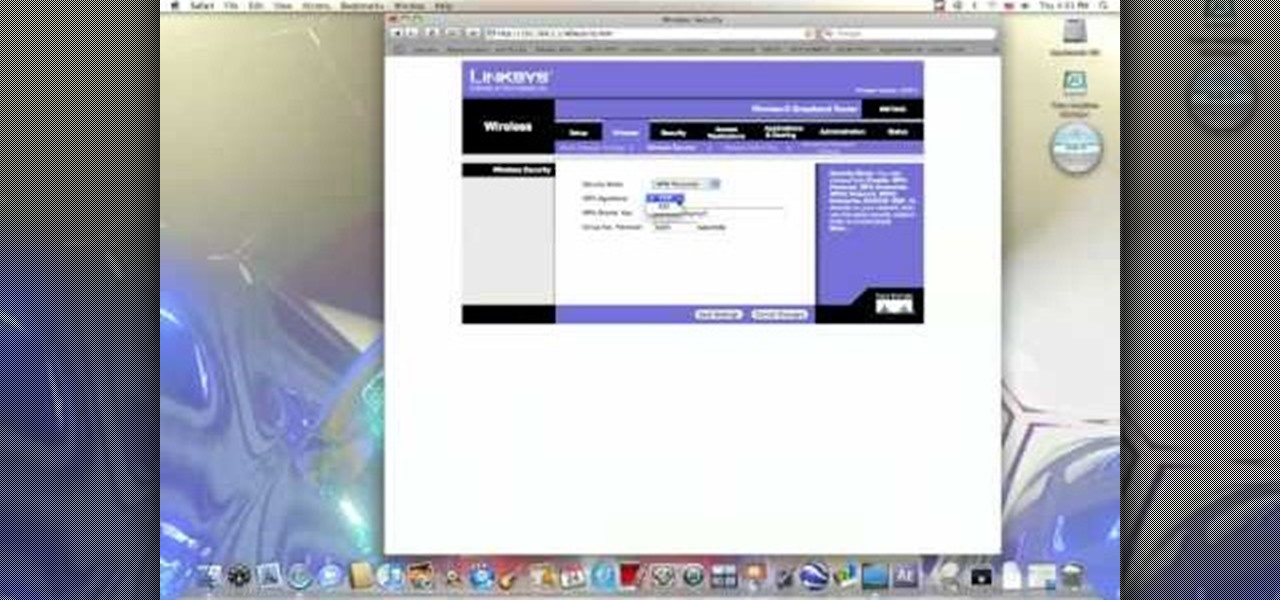
In this video from benjamoon we learn how to secure a linksys wifi network from a Mac. First type in your IP address in your browser bar which is 192.168.1.1 then press enter. If it asks for a password it is admin. Click on Wireless and here you can edit your name and who can access your wifi network. Under wireless security, go to WPA personal from the drop down menu. When you make your password, make it very challenging. He recommends just banging your hand against the keyboard, as long as ...

This video is a tutorial on how to make a diaper cake. The cake is not edible. To begin, you will need a pack of diapers and rubber bands. Roll up the diapers from the waist down and secure them with the rubber bands. Put several rubber bands around a bottle of wine and secure the diapers in tiers around the bottle of wine. Cover each tier with tissue paper before adding the next one. Wrap each tier in blankets. Top off the cake with a can of formula wrapped in a decorate blanket. At this poi...

Have some files you don’t want anyone to see? Or maybe it’s just been a while since you’ve emptied your trash bin. The trash bin function is not a permanent delete but you can erase files off your Mac with this tutorial.

A massive leak appeared the web today, and it's got some huge security implications for every iPhone on the market. On the plus side, it also has some potential for enabling deep-level modifications and jailbreak tweaks.

JavaScript is one of the most common languages used on the web. It can automate and animate website components, manage website content, and carry out many other useful functions from within a webpage. The scripting language also has many functions which can be used for malicious purposes, including stealing a user's cookies containing passwords and other information.

An internet connection has become a basic necessity in our modern lives. Wireless hotspots (commonly known as Wi-Fi) can be found everywhere!

Materials: Scrap fabric, elastic thread, cardboard, scissors, cellophane tape, and other bits and bobs ie feathers, buttons

Want to hack a LAN? Well, hacking local area networks is easier than you'd think. And by watching a few short videos, you can become a master hacker, something every techie wants to achieve. And what's the best way to hack a LAN? Ettercap, a password sniffing program.

Need to secure your track to the road bed for your model railroad? Well, this video tutorial will show you how to do it, not to mention show you how to weather your flex track.

Looking a for a secure and secretive entryway to your Minecraft base? Check out this video to learn a great design that uses pistons to make a trap door. With this trap door you can control who gets into your base, and who gets sent to the lava pit.

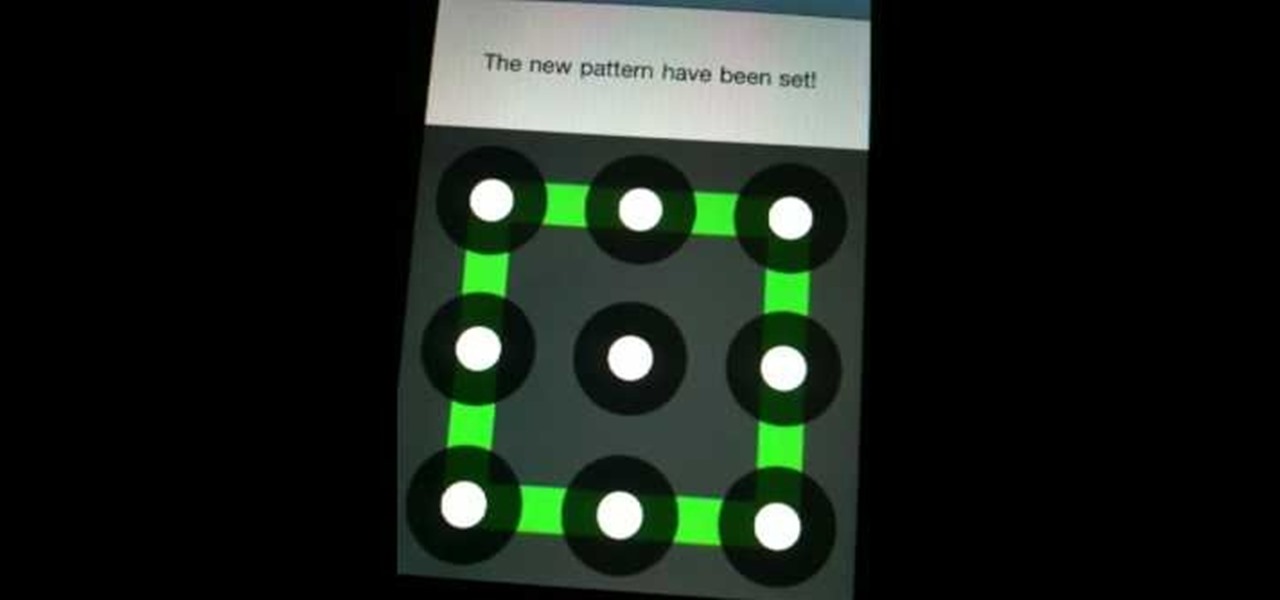
Concerned about unwanted eyes setting upon the information in your Android phone? This video will show you how to turn on the screen lock feature of your Android smartphone. Keep the information on your Android device to yourself with a lock screen.

Check out this Minecraft building guide to learn how to build a machine gun that can fire 25 arrows a second. If you need to secure your home from mobs, or you just want to have an awesome machine gun, watch this video.

iPhone and Android both have a lot of great features. Enjoy the best of both worlds when you install Android lock on your iPhone. This is a great way to secure your iPhone. Use Android lock to get an extra layer of security.

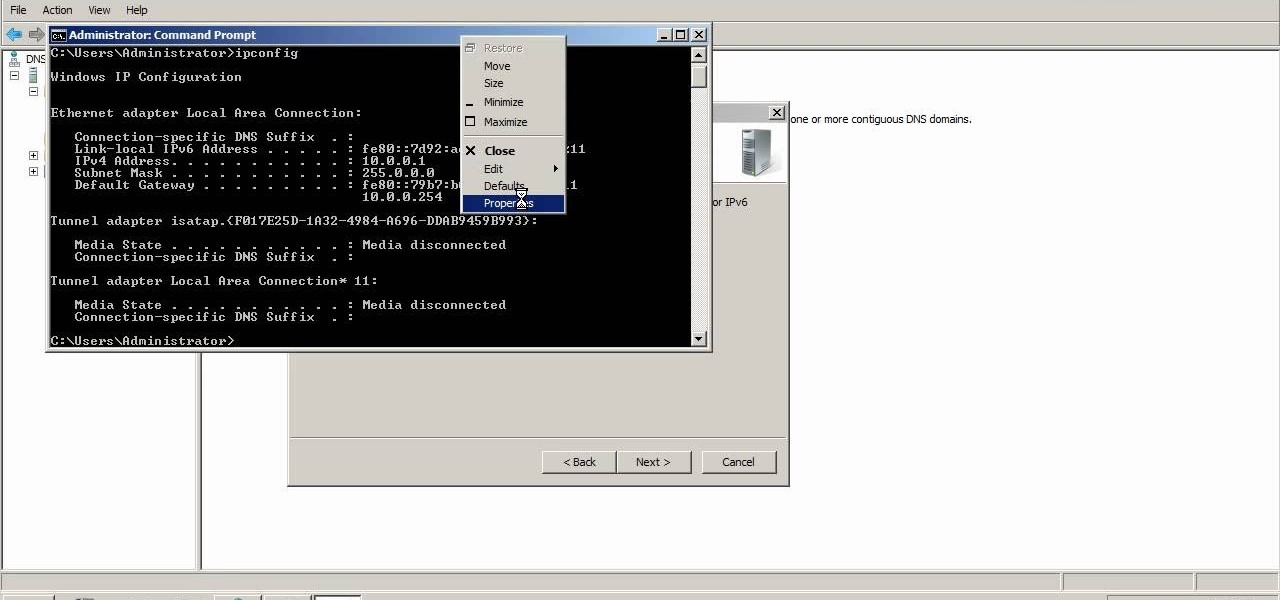
A reverse lookup zone will allow you to translate IP addresses to fully qualified domain names (FQDN). This can be a tremendous help against phishing in large organization. Keep your network secure by creating a reverse lookup zone in Windows Server 2003 or 2008.

First, make sure that your image is hosted on a secure place online (such as your own Photobucket account). Then go to ImageMaps.com and use this free site to create your own image map that can now be added to your website.

Adding a SIM card to your Samsung Galaxy Tab is easy! If you have this new Android tablet and are looking to see how to install the SIM card, this video will clearly show you how it's done. Simply remove the slot's cover, insert the SIM card, making sure it's secure and snug, and then closing the cover. That's it!

If you have the chance to briefly talk and sit with a literary agent (such as at a convention), you only have so much time to impress them and pitch your book to them. These tips are the best ways to get an agent and secure representation.

MetaRL is a site you can sign up with that will let you accrue points that you can cash in for free online currency in your favorite online game. It's a very secure and perfectly legal way to get game currency without having to hack your games.

You can create some lovely and cute cloth pumpkins to decorate your house for Thanksgiving! All you need is some scrap material in fall or pumpkin colors, and a few rolls of toilet paper. Wrap the fabric around the toilet paper, tuck and secure!

When you film at home with just a regular camera using the built-in microphone, the quality can be bad to worse at best. If you are looking to improve the sound the best that you can with low budget solutions, check out this video. You will get tips on how to secure your locations and also how to monitor the sound going into your camera.

Interested in finding out just how secure your WEP-protected wireless network is? Let this video be your guide. It's a simple process and this home-networking how-to will teach you everything you'll need to know. For specifics, including detailed, step-by-step instructions, and to get started cracking WEP networks with BackTrack yourself, watch this helpful video guide.

Looking for an easy way to make certain that your sensitive personal information is secure? With Identity Finder, it's easy! So easy, in fact, that this home-computing how-to from the folks at TekZilla can present a complete overview of the process in just over three minutes. For more information, including step-by-step instructions, take a look.

VPN's are an invaluable set up for small business', and larger business', when it comes to keeping your information secure with remote employee's. This video details all of the info that you need to know about setting up and maintaining a great VPN!

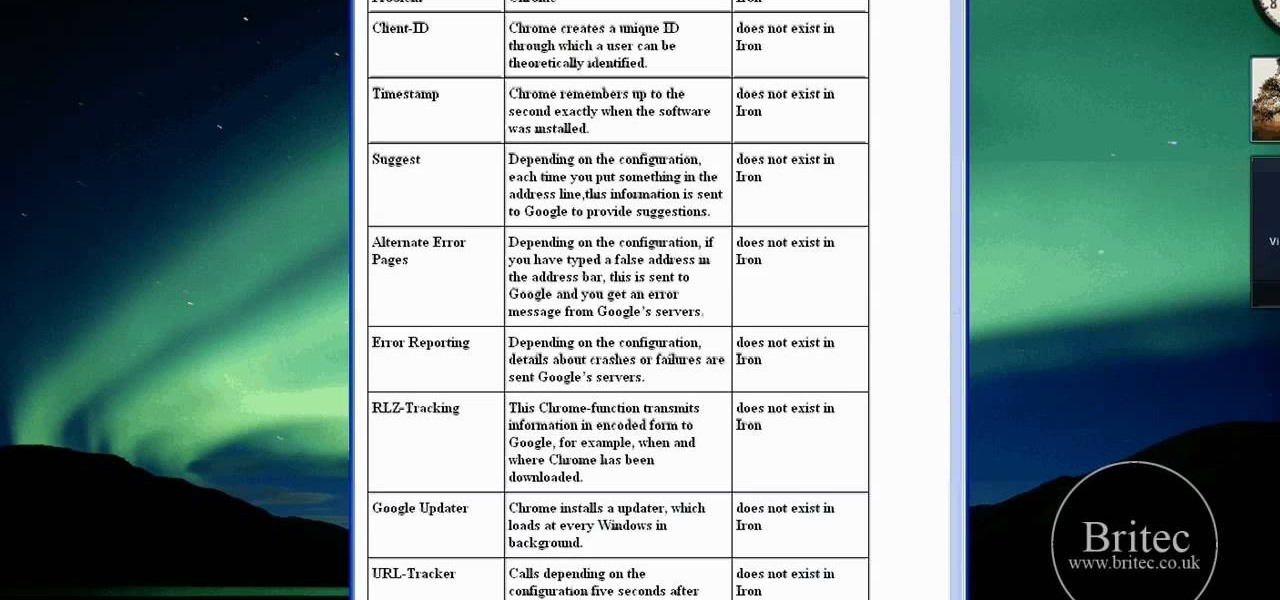
Interested in using Google Chrome but concerned about protecting your privacy while surfing the web? Meet Iron Browser, a secure but otherwise identical clone of the Google Chrome web browser. This clip from Britec will teach you where to find it, how to install it and how to get started using it.

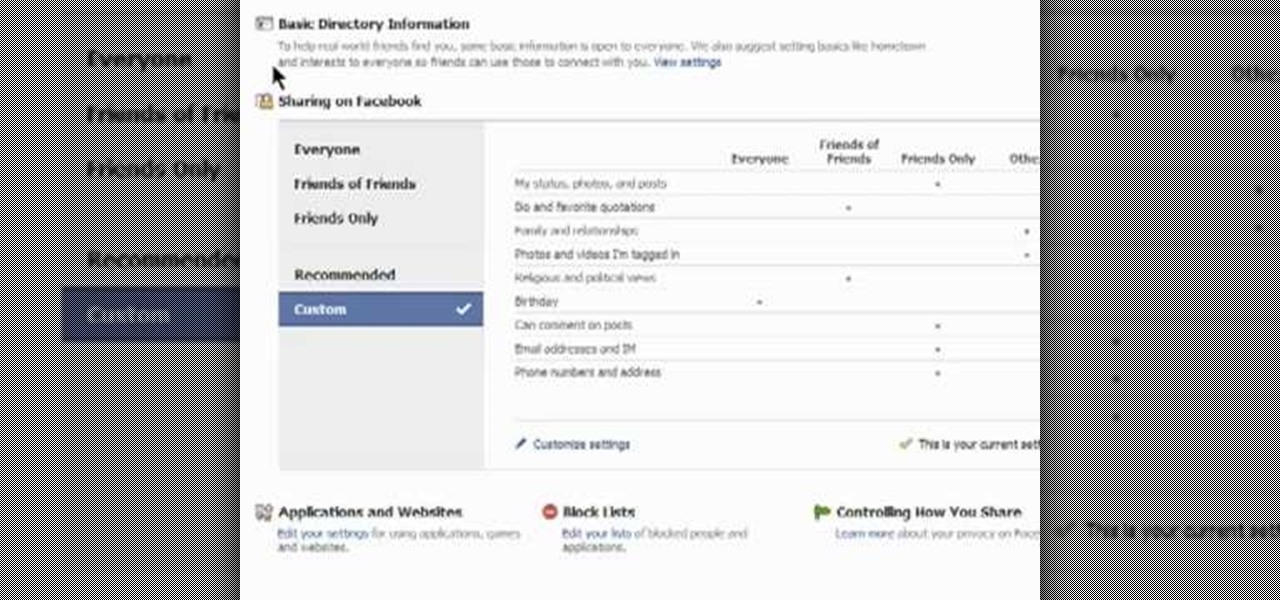
This clip presents an overview of the most important privacy settings on Facebook. Fortunately, with the right knowledge and the new Facebook Privacy Settings regime, protecting your data can be easy. So easy, in fact, that this video guide can present a complete overview of the process in about two minutes. For more information, including step-by-step instructions, take a look.

Installing beadlocks in your tires can help make sure that the wheel is secure and won't be going anywhere. There are many different types od beadlocks that can be purchased, but for this tutorial, you'll be finding out how to install one in an RC tire.