
How To: Make an infrared pen to use with the Wiimote
Here are some step-by-step instructions on how to make an IR LED Pen to use with a Wiimote to create an inexpensive interactive whiteboard. It's a student video production of the WHS Tech Club.


Here are some step-by-step instructions on how to make an IR LED Pen to use with a Wiimote to create an inexpensive interactive whiteboard. It's a student video production of the WHS Tech Club.

You know what they say, when you have straight hair, you want curly and vice-versa. I have wavy hair, so I crave curly AND straight. Here's a simple and inexpensive way to curl your hair. No curling iron or hot rollers needed. Your hair is less damaged and more healthy looking.

Use inexpensive materials to create your own photographic studio equipment for product photography. The DIY set up is simple and useful.

Finally, here's a quick tutorial on how you can mix your own homemade mixing medium! It's quick, easy and inexpensive. The challenge is finding glycerin, but its out there.

Painting kitchen cabinets is an easy and inexpensive way to bring old cabinets back to life. Meghan Carter shows you how to paint kitchen cabinets and offers a few inspirational decorating ideas for really dressing up your kitchen cabinets.

The Woodworking Underground shows in this video tutorial a quick and inexpensive way to repair the slot in your Festool MFT (multi-function table) work table, from pro Joseph Fusco. This how-to video is a must watch for all furniture and woodwork enthusiasts.

The Canon Powershot A460 is a relatively inexpensive digital camera. It is aimed at someone looking for a point and shoot digital camera who does not want to break the bank. It has five megapixels and a four times optical zoom lens. Watch this video to learn how to use it.

This new episode of Full Disclosure shows you how to use a SSH Tunnel to secure your data when you are on an untrusted LAN (ex. Coffee Shop, School's network, or Defcon). Furthermore, you can use the SSH Tunnel to bypass the LAN's internet filters. The SSH tunnel protocol works by encapsulates your data into an encrypted payload and transmitting it to the SSH Server which is setup on a trusted LAN.

Scooters have been out for a while now, but they're still an excellent, inexpensive way to commute if you're not going too long a distance. But scooters, like bikes or cars, need their regular maintenance too.

How to inflate soap bubbles using helium and pressurized air: inexpensive and easy to do.

HippyUrban teaches viewers how to make inexpensive tortilla chips from scratch! First you will need to buy some MasaMix at your local Spanish market! It really is just corn flour. First, you need two cups of corn flour, 1 quarter teaspoon of salt and 1 quarter cup of water. Mix this up and add a tablespoon of water at a time to get it just right. Divide this in three and roll the dough on parchment paper. You want it to be thin and as thin as pie crust. With thicker chips, they can hold the s...

Pigs in a blanket are the perfect appetizer for any occasion. They are great snacks at Super Bowl parties, family functions or birthdays. They are easy to eat finger foods and with only 3 ingredients, require very little work or clean up! In this tutorial, Betty shows us how to make inexpensive pigs in a blanket with Vienna sausages. Enjoy!

In this video tutorial, viewers learn how to secure a home wireless network. There are 3 types of security protocols for connecting devices. The 3 types of security protocols are: OPEN, WEP and WPA. Users should use passwords that are secure but no so obscure that they are unusable. The password should not be dictionary words. They should be mixed with casing and contain the user's phone number. Go to your router's website and log into the website. Find the setting for wireless security and e...

Have important files that you want to put on a USB drive but do not want anyone else to be able to access them? Put a password on it using USBSecure.net free resource.

Use three tools to create a simple ponytail. Use a hairbrush, a bobby pin, and a bungee band holder for this look. Using a bungee band instead of a standard ponytail holder eliminates some of the issues typically caused by pulling hair through ponytail holders. Start by using a bristled brush to brush the hair to one location on the head. Secure one hook of the bungee band in the ponytail and wrap the tail around the rest of the hair. Wrap it around again, and secure the other bungee band hoo...

Using ASP.NET Secure Services and Applications Services

Need to know how to tie a Bowline with a few ways of securing it? This way shows you how to secure it with a seizing so that it won't accidentally come undone. Included is a little variation of the bowline with a built-in seizing. If you don't have electrical tape to secure the bowline feed the bitter end back through the hole. It also makes it so you don't have a tail line dangling if you're towing something.
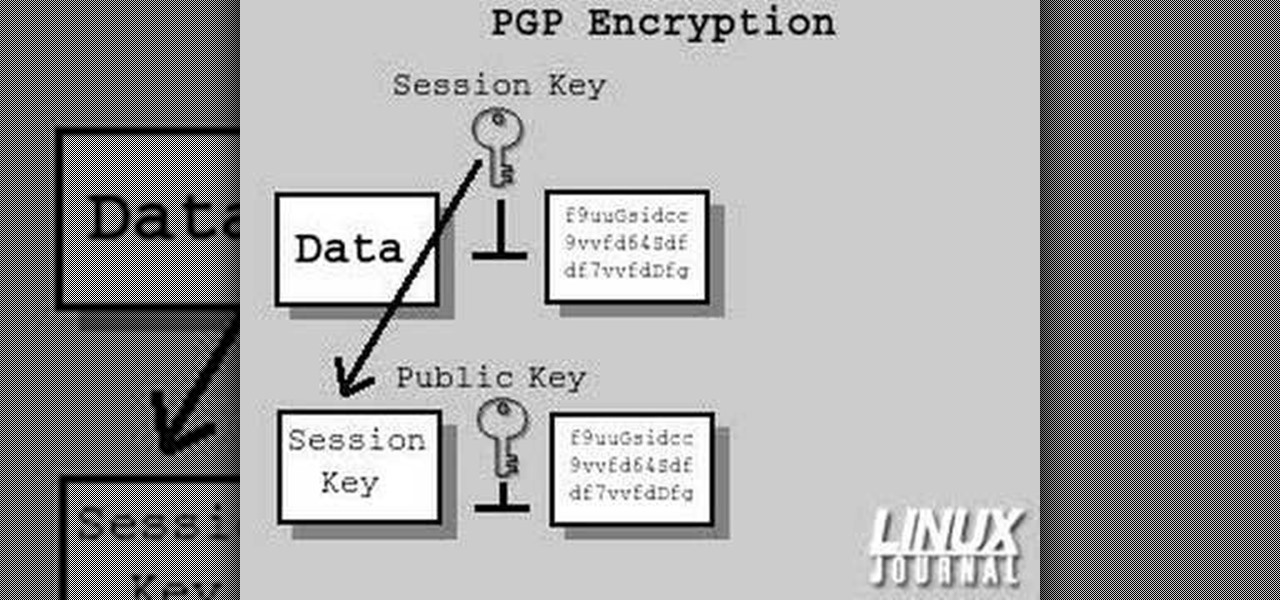
In today's time of rampant information crimes, including identity theft, security is more important to the average computer user than ever. This tutorial from Linux Journal Online shows how you can use GnuPG to secure and verify data on your Linux box. (This video was created using only free and open source software tools: TightVNC, pyvnc2swf, ardour2, audacity, jackd, LAME, kolourpaint, cinelerra-cv, mjpegtools, and ffmpeg.)

In this clip, you'll learn how to get started using Secure Computing's Secure Web Protection proxy service. It's easy! So easy, in fact, that this helpful how-to can present a complete overview of the app in just over five minutes. For more information, including detailed, step-by-step instructions, take a look.

How to Use Your Mac as a Server: Turn your Mac Mini into a server! Yes, that's right, with a little know-how and a little spunk, you can turn an inexpensive Mac Mini computer into a server to provide services over you network. You won't even need the Mac OS X Server, just the Mac OS X Client, so there is no extra software to buy, just the Mac Mini and it's operating system.

Don’t play Russian roulette when it comes to your wheels. Keep your bike secure with these precautions.

A formal occasion calls for a classic look. You Will Need

Secure a square knot with tips from this video.

Buns and updos are gorgeous hairstyles, with one caveat: If they're not pinned perfectly and securely in place, all your hard work braiding and curling will go to waste as your hair slowly unravels.

Are you secure when downloading security software? Sounds like quite the conundrum, but CNET has answers. See if you're really secure when getting that software, and telling the difference between a rogue antivirus website versus a legit site. See how not to get scammed and destroyed!

Candles floating in a luminous vase filled with water, surmounted on a bed of evergreen sprigs and pinecones...what could be a more beautiful natural celebration of Christmas than this inexpensive centerpiece?
Using just a few inexpensive pieces of hardware, you can construct your own rack designed for storing and organizing spools of wire. Bolt a dowel to a wall or another rack, then thread your spools on the dowel. You can still get the wire, and now they won't move!

In this clip, you'll learn how to make a RAID (or redundant array of inexpensive disks) with the Disk Utility on a Mac OS X computer. For more information, including a complete demonstration and detailed, step-by-step instructions, and to get started making your own arrays, watch this handy home-computing how-to from the folks at CNET TV.

The ukulele is a beautiful and unique stringed instrument that is perfect for the traveling musician because it is so portable and relatively inexpensive. The ukelele is a version of a small guitar that originated in Hawaii. In this how to video, Aldrine shows you how to make a makeshift humidifier for your ukulele case with sound effects and 5x action. With this DIY humidifier you can keep your ukulele in beautiful condition.

In this tutorial, we learn how to lash a bamboo tripod. First, you will tie a clove hitch by taking one piece of bamboo and wrapping the rope around it, then crossing the two sides of the string together to make a hitch. Next, you will secure the clove hitch around the third piece of bamboo. Now, you will rap all the pieces of bamboo together with the rope. Continue to do this until all the pieces feel secure together. Wrap the rope several times around each of the pieces, then wrap it in the...

In this clip, learn how to make a warm and cheap costume that is still adorable. This video will show you how to take a piece of fabric and sew it to a sweatshirt to make a lion mane for your little girl or boy. This is a super cute way to make an inexpensive costume that your kids can wear for years.

Picking a secure password is not only important for protecting your privacy, it's also very easy. Provided, that is, that you know how to go about it. This free video lesson from CNET TV will walk you through the process. For more information, and to get started creating and using high-security passwords yourself, watch this video tutorial.

Kandee, a makeup, artist demonstrates a Gwen Stefani up do that was from an Elle magazine cover. Rub hair paste into your hands and smooth it through your hair. Then section crown to forehead and twist it counterclockwise until it starts curling up. Keep twisting and wrap it around into a tight knot. Use a bobby pin to secure it at the base. Then take another section of hair and repeat. Split the bottom section of hair that is left asymmetrically and twist each of those sections halfway and t...

TrueCrypt is a free application that lets you encrypt designated programs on your Ubuntu system to prevent unwanted access. Provided you select a strong password, intruders will not be able to open your personal files and documents. This instructional video walks you through the process of installing TrueCrypt on your Ubuntu operated machine and demonstrates an example on how to create an encrypted volume within a select partition.

The Clinch Knot is used to secure your fishing line to your fishing lure. In this video, learn how to tie a secure clinch knot, step by step. You can't fish without a sturdy lure, so watch the video and practice until you master the knot on your own. Once you've got it, attach your bait and you are on your way! Happy fishing!

One of the great innovations of Canon's DSLR technology is the relatively inexpensive ability it gives to any filmmaker to make professional quality video. This video is a great demonstration of a Glidecam and Steadicam mod designed to carry the Canon 5D Mark II and give any image a slick, professional look.

Learn how to add memory (RAM) to a Apple MacBook Pro notebook computer. Upgrading your MacBook Pro laptop memory is easy to do and an inexpensive way to improve the performance of your MacBook.

This experiment is very easy and inexpensive. It can be done at home. You will need a bowl, some water, some pepper, and some soap. You can use your finger to repel pepper, to the sides of the bowl. Simple, but fun.

Email is one of the least private and least secure forms of communication, although few people realize this. MixMaster is one way to allow secure, anonymous communication even over the very public medium of email. This tutorial will get you started with MixMaster quickly and easily.

The ukulele is a beautiful and unique stringed instrument that is perfect for the traveling musician because it is so portable and relatively inexpensive. The ukelele is a version of a small guitar that originated in Hawaii. In this tutorial, ukulele master, Gordon Mark shows us one of his techniques for playing classical music on his KoAloha ukulele. Once you get a hang of this technique you will be able to play some easy songs on the uke.