Apple just released public beta 2 for iOS 14 today, Thursday, July 9. The good news comes two days after Apple released the second iOS 14 developer beta, and 17 days after the release of the first developer beta. While this is the first public beta for iOS 14, it's called "public beta 2" to keep in line with developer beta numbering.
Apple just released the second developer beta for iOS 14 today, Tuesday, July 7. The update comes 15 days after Apple seeded developers the first iOS 14 beta, which introduced home screen widgets, picture-in-picture, and 4K YouTube support, among more than 200 other features.

Apple officially unveiled iOS 14 on June 22 at its first all-virtual WWDC. After months of beta testing, iOS 14 hit iPhones on Sept. 16, but that doesn't mean that Apple is done beta testing iOS 14. There will be new features to try out right up until iOS 15 comes out next year.

What appears to be an ordinary MP4 may have been designed by an attacker to compromise your Linux Mint operating system. Opening the file will indeed play the intended video, but it will also silently create a connection to the attacker's system.

If you have a modern iPhone, you have an excellent video recorder at your disposal. Every iPhone since the 6S has the ability to shoot in 4K resolution, and each new iteration has brought new capabilities to the table. But even the best mobile shooter can use a little extra help. That's where these video recording apps come into play, to ensure the footage you capture is as good as can be.

SSH is one of the most common protocols in use in modern IT infrastructures, and because of this, it can be a valuable attack vector for hackers. One of the most reliable ways to gain SSH access to servers is by brute-forcing credentials. There are a few methods of performing an SSH brute-force attack that will ultimately lead to the discovery of valid login credentials.

With smartphone cameras and software getting better and better every year, more and more users are getting passionate about photography. So when you're shopping for a gift to get someone, if they have a smartphone, chances are they'll more than appreciate some tools and accessories for taking better photos with their pocket friend — and we've got some gear ideas they'll love.

Internet Relay Chat, or IRC, is one of the most popular chat protocols on the internet. The technology can be connected to the Tor network to create an anonymous and secure chatroom — without the use of public IP addresses.

A mention of the deep web can bring to mind images of drugs, hackers, and other criminal activity. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and any hidden services can be as simple as downloading the Tor Browser.

No more Internet Explorer 9 Beta. Not today. Now you can explore the web with Microsoft's new Internet Explorer 9 Release Candidate (RC). It wasn't supposed to be released until tomorrow, February 10th, but it's been leaked a little early, WinRumors reports.

The new Import Reference feature in modo 301 allows you to import meshes or entire projects into a master project. This is a powerful and efficient workflow enhancement for modo 301. The import reference system provides a powerful assembly based workflow as you will see in this tutorial. Import reference in modo 301.

If you are using, or plan to use Camtasia Studio 5 software to record screencasts, you definitely want to check out this tutorial. It covers the options to optimize your recordings so you get clearer video, smaller file sizes, and other enhancements like removing black bars, and dealing with camera video. Get the best quality & smallest file size in Camtasia.

In modo 301 3D painting has really "come of age". One powerful enhancement is the ability to paint across multiple images of varying resolution with a single stroke. It's very nice. Why are you reading this? Watch the modo 301 clip! Paint across multiple UVs in modo 301.

This video shows the enhancements made to the QuickTime export feature in Flash. You learn how to effectively export content for broadcast, DVD, or video editing applications such as Premiere. Export QuickTime files from Flash CS3 Professional.

In this tutorial, learn about applying and removing security options in Acrobat 9. For more Adobe software tutorials from Layers Magazine, search Layers Magazine on WonderHowTo. WonderHowTo indexes all Layers Magazine tutorials for Illustrator, InDesign, Photoshop, Acrobat, After Effects, Premiere Pro, Dreamweaver and Flash.

This tutorial shows a variety of tools within Frantic Films' Awake plug-in package for eyeon Fusion, including the lens distortion, digital film noise and workflow enhancements for stereoscopic imaging. Use the Awake plug-in for Fusion 5.

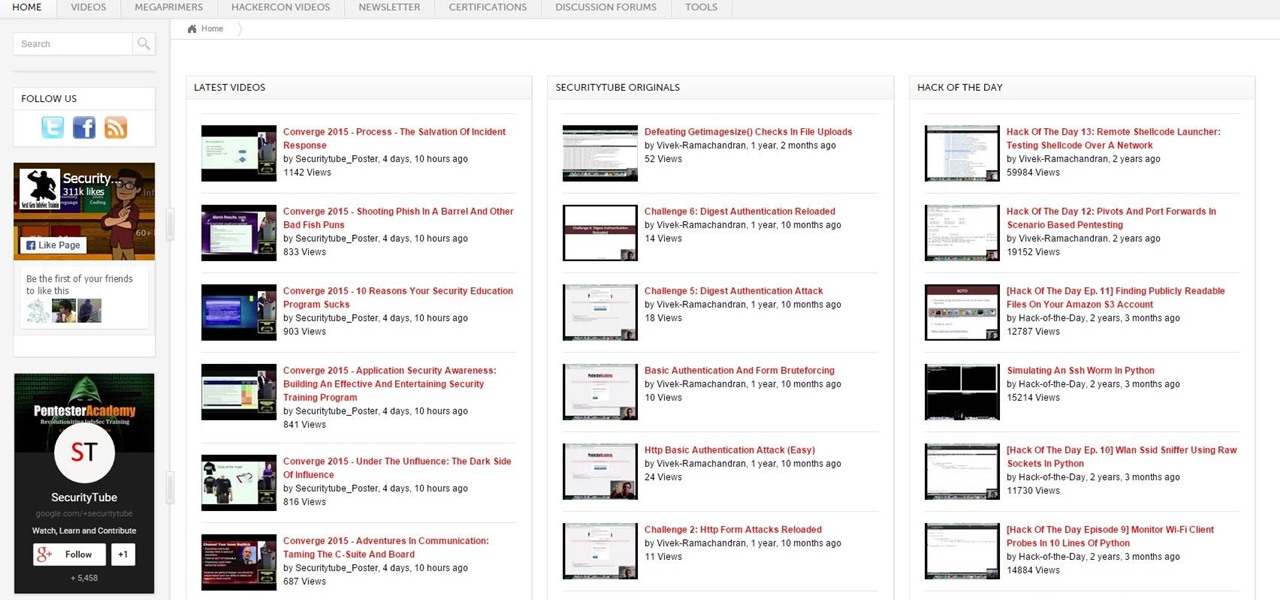
This hour-long hacking tutorial looks at the Nmap security scanner. In particular, this Nmap tutorial looks at port scanning concepts, TCP three way handshake, stealth scans, idle scans, bounce scans, version detection, OS detection, NSE/LUA scripting and firewall logs. To get started using Nmap, watch this video tutorial. Use the Nmap security tool.

The shift to remote working in response to the COVID-19 pandemic has not slowed Google's efforts to fulfill its annual Android update cycle, as the third developer preview of Android 11 dropped on Thursday.

You've all probably heard about Apple's attempts to thwart iPhone 4 users from opening up their own devices, thanks to their sly maneuvers in switching out everyone's screws with those funky pentalobular screws. But one thing Apple will never learn— they will never have complete control. Where there's a will, there's a way. And if someone wants to fix their own iPhone or modify it slightly, they're going to do it, regardless of what screws bind it together.

The Ironkey is a high security thumb drive designed to provide strong AES encryption, tamper resistance and other security services. Some of the topics covered will include: How is the drive mounted without admin privileges in Windows? How is it mounted in Linux? How does the "Self Destruct" feature work? What is Secure Sessions? How is the Ironkey better than just using Truecrypt? For answers to these questions, take a look. Use the Ironkey High Security Flash Drive.
he Senate Appropriations Committee on Tuesday moved forward with legislation to increase airline passenger security fees, beating back a GOP attempt to keep them at current levels.

Waiting in line at the airport can be a drag, but here are a few tips for catching your flight hassle-free. See how to get through airport security in a snap from this how-to video. Airport Security Tips - Fly Through Airport Security Video.

In this video tutorial, viewers learn how to set and encrypt the wireless password using WEP Apple Airport. Begin by opening the Apple Airport utility program. Then find the network's name and double-click on it. The Configure "Apple Airport Express" opens, click on the Airport tab. Then click on the Wireless Security button. Now click on the Wireless Security drop-down menu and select 128-bit. Click on the Set WEP Password button, type in the password and verify it. Finish by clicking on Upd...

In this video tutorial, viewers learn how to set and encrypt your Wi-Fi password using WPA on a Linskys router. Begin by opening your web browser and type in the address: Click Enter. Now type in your user name and password, and click OK. Then click on the Wireless tab and select Wireless Security. In the Security Mode drop-down menu, select WPA Pre-Shared Key and then type in a password under WPA Shared Key. Finish by clicking on Save Changes. This video will benefit th...

Adobe Photoshop CS4 and Adobe Photoshop Lightroom 2 software work together so you can efficiently manage thousands of images — or perfect just one. Photoshop CS4, the industry standard in digital imaging, now provides improved access to its unrivaled editing power through a more intuitive user experience, greater editing freedom, and significant productivity enhancements. Lightroom 2 streamlines your photography workflow, so you can easily import, manage, and showcase large volumes of photogr...

Installing a deadbolt is a relatively quick and simple do-it-yourself project. You can make your home much safer – and less attractive to thieves --- with a little effort and a few simple tools.

PostSharp is an free, open-source and extensible platform for enhancement of .NET assemblies, that is: PostSharp transforms assemblies after compilation. Pretty abstract, isn't it? Not so much. It has great applications. PostSharp Laos, a Lightweight Aspect-Oriented Solution, provides aspect-oriented programming (AOP) to .NET Developers without the learning curve. This tutorial presents an introduction to the PostSharp programming language, one that's more than sufficient to get you started. ...
Ok, now lets introduce myself i am also a newbie but conducted many pentests.This is the tutorial for customizing kali linux

Hi everyone. I'm relatively new here and I have learned a great deal from many of you already and would like to try and give a little something in return.

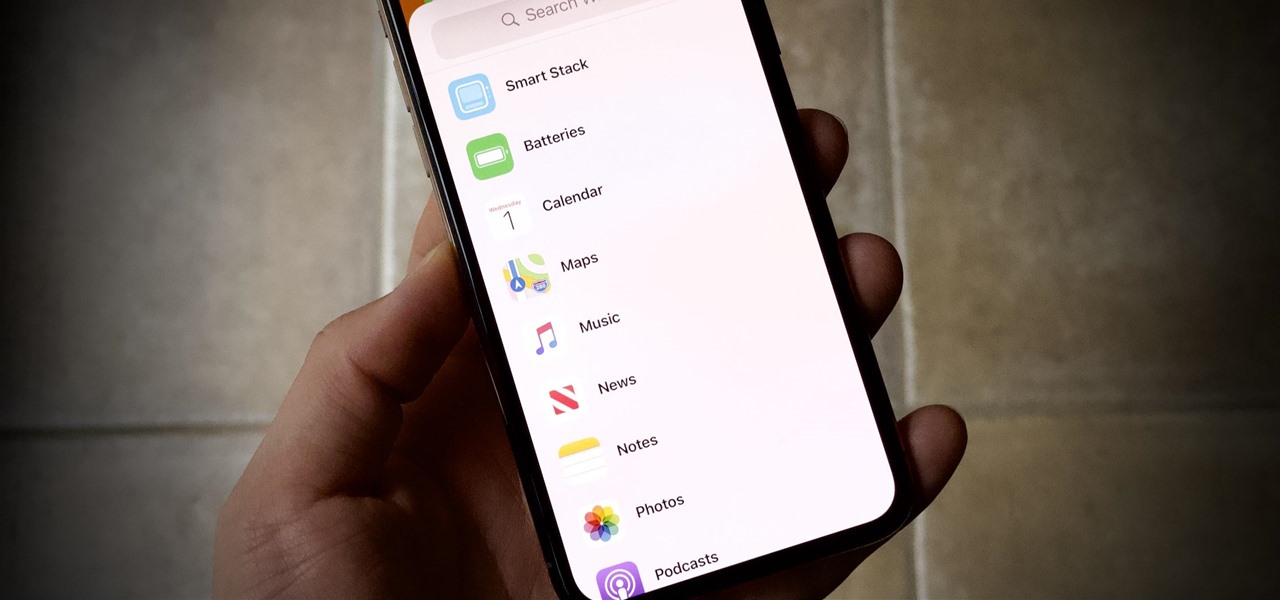
How many of you have or know people who have a smartphone? There's a lot of you, right? Well, depending on how most of you use those smartphones, there could be all kind of sensitive information stored on it, and that doesn't just mean sensitive personal information, but it could also contain all sorts of sensitive corporate data for work.
Multiple airport screeners have been arrested for allegedly taking handsome bribes to look the other way while loads of illegal drugs slipped through security at Los Angeles International Airport, federal officials announced today.

Check out the winner from Beyond the Still's Chapter Two: Job Security. "Job Security" written & directed by Josh Thacker.

Hi fellows! I finally decided to join this forum, which I find very interesting and has some great contributions into the tech and security space, appreciate it!

The great thing about security apps (other than the obvious) is that there is an abundance of them littered throughout the Google Play store. Cerberus, Got Ya!, Avast! Mobile Security, Norton Security & Antivirus, and Android Lost Free are just a few of the gems you can find in the plentiful sea of security apps for Android. Once in awhile, though, a new security application comes along that stands out from the rest, like AeGis.
In late 2011, representative from China, Russia, Tajikistan and Uzbekistan submitted a proposal called the International Code of Conduct for Information Security (ICCIS) to the UN Secretary General Ban Ki-moon that called for international consensus of a global set of rules and regulations that standardize information flow on the internet.
The department of Homeland Security released a list of 'words and phrases' it uses to search social media for terrorism, and whatever else they decide they are looking for that day. Read some of these. A few are obvious "bomb, nuke" and some "target, event" are just down right vague. More reasons to watch what you do on the Internet. You are not the only one watching!

UK-based artist Matthew Nicholson is a man of many talents: designer, photographer, professional free runner and papercraft engineer—and in the latter of which, he generously posts free downloadable DIY kits for your folding pleasure.

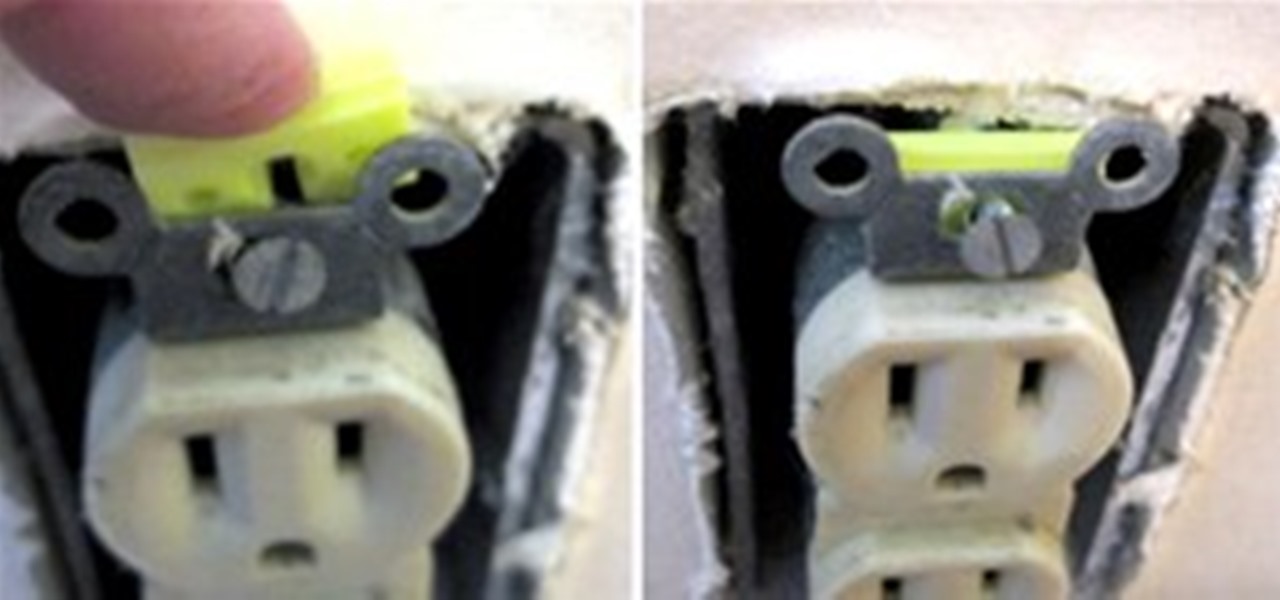
Normally the idea of messing with an electrical outlet makes me squirm, but Apartment Therapy's quick fix for a loose wall outlet means skipping out on a costly electrician bill. Not only is a wiggly wall outlet unsightly, but it can also be a fire hazard. The solution is simple:

The end of Daylight Saving Time means two things: a little less light and, as a result, a little less security. This CCTV lamp will give you more of both. And in the nick of time! We fall back to Standard Time at 2 AM on Sunday, November 7th. Better get building!

New buildings, decorations, wasabi crop and asian pear tree. Inside the mystery box we have: