Remote desktop is a very powerful feature using which you can access any desktop from another desktop over an internet. In this video the instructor shows how to enable remote desktop in Microsoft Windows XP. Remote desktop is a system that will allow other users from the internet or your local network to connect and control your computer. As this can be a security hazard be careful while sharing the details of your remote desktop connection. To enable this click on start button, right click ...

Wrapping your wrists for boxing is very important to provide protection and support when you are throwing your punches. This video shows you the right way to wrap your wrists to prevent injury. You'll be putting the seam side of the wrap against your skin, and start by putting the loop at the end over your thumb. You will start by wrapping the wrist a few times, depending on how long your wrap is. Watch to see the correct way to cover the knuckles and secure the wrap against your hand before ...
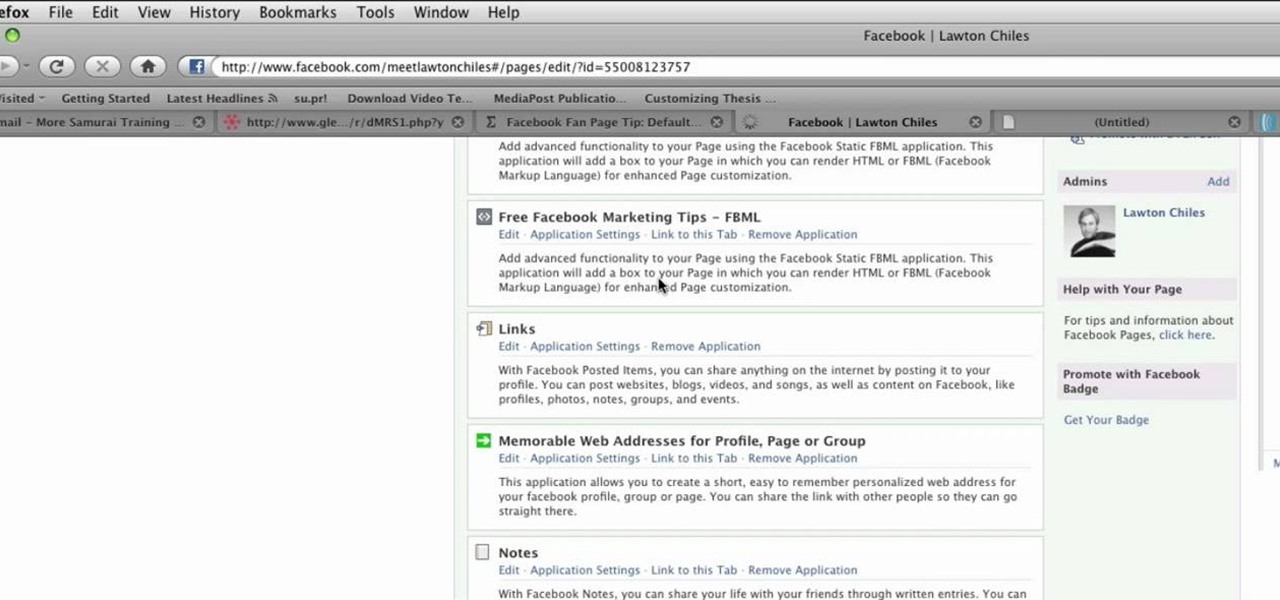
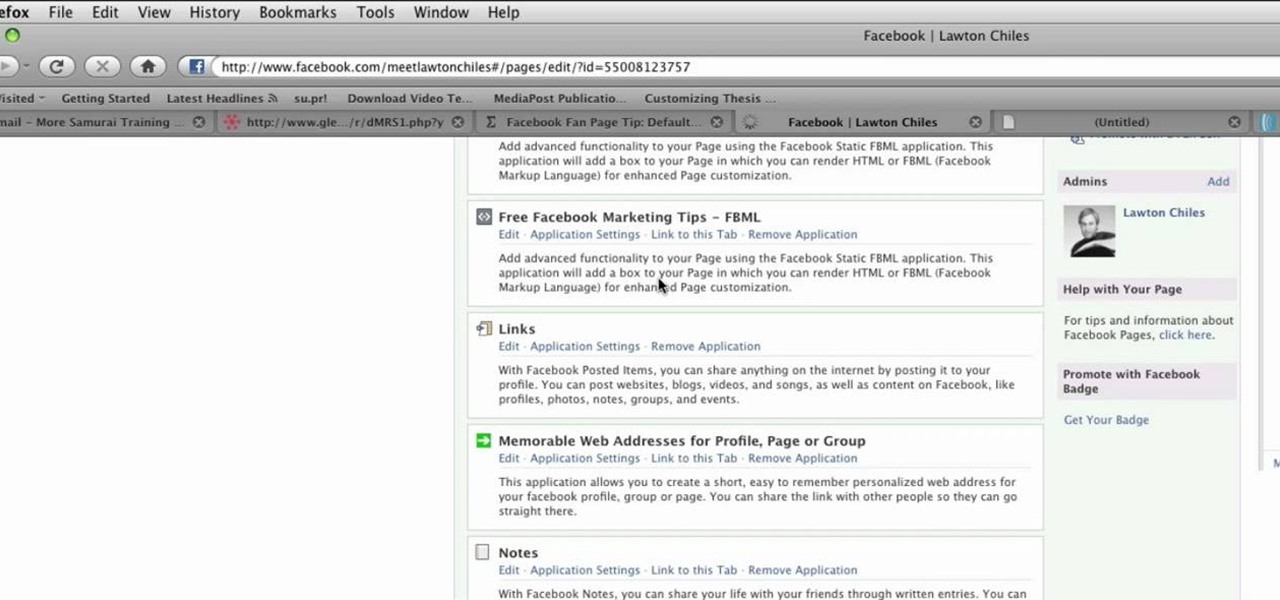
This video shows you how to make a custom Facebook Fan Page for your favorite Celebrity, Club, activity or anything you choose! First thing you must do is activate a Facebook account. Its really simple, just go to www.facebook.com and create a profile. After that type in FBML in your search bar and click on Static FBML. That application will enable you to create many different settings for your Fan page including ads and different looks and security measures for your profile. Now get to creat...

This instructional video by GoogleNexusOne shows you the features and how to set up a recently unboxed Nexus One Android phone. First the functions of the indicators and buttons are explained, and the different ports and jack are highlighted. After that the back of the phone is opened and the locations of the slots for the SIM card and the microSD card are shown, as well as how to insert the battery. Set up the phone as instructed after reading the documentation, sign in with your gmail accou...
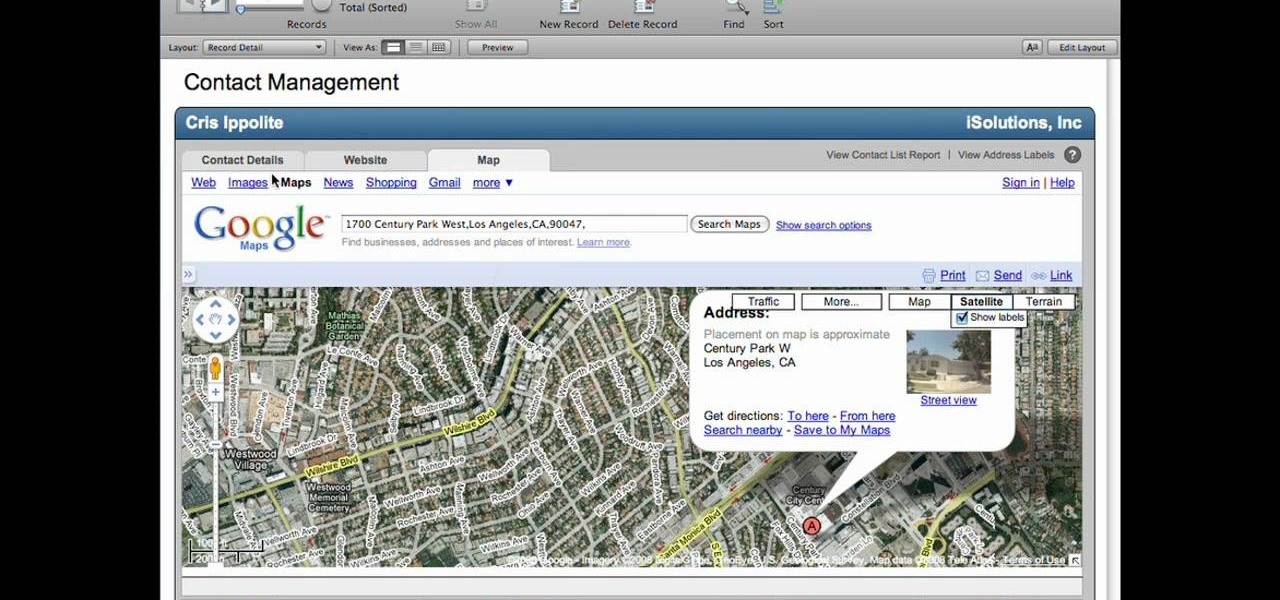
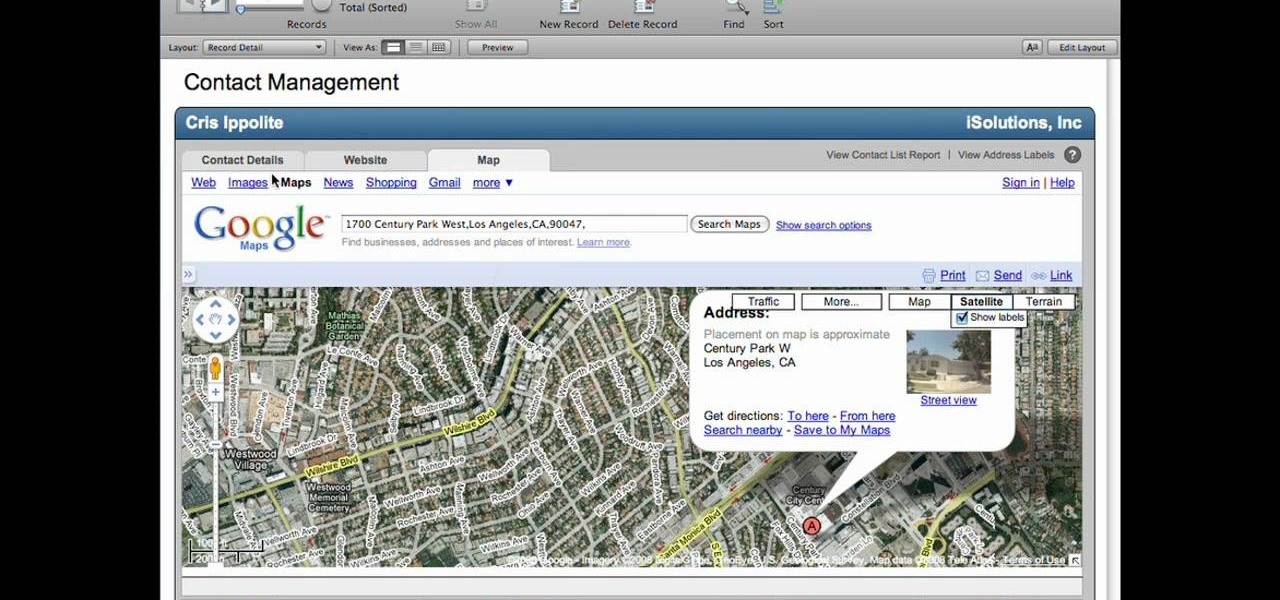
Lyndapodcast teaches you how to create a database using FileMaker Pro 10. You can link one contact with multiple addresses and information and store that into a single database. You can also add content from the web into your FileMaker layout, including maps, pictures and music. You have a security module where you can set permissions for the users using the database. You can also publish the FileMaker database to the web. For this go to File - Sharing - Instant Web Publishing. Another featur...

In this video you will learn how to do a Flair bartend: vertical toss grab reverse grip. Start this trick with an over hand grip, then reverse grip right hand. Reverse grip and pour. Make sure you are holding your bottle security. Your holding the bottle and spinning with the other hand. You might have to practice the end pour so you don't spill as you bring the bottle back up. This video does the sequence many time so you can get the hand work done correctly.

This video will allow you to view your saved usernames and passwords in Firefox. This may be useful for users in case you forget what your user names or passwords are for different sites and would like an easy way to find them. Under the Firefox toolbar, go to "Tools" and then "Options" in order to get a popup which will allow you to view different aspects you can change in Firefox. Go to the security tab and then click on the button which says "Saved Passwords" in order to view all your save...

AntiVirus Live is a fake antivirus software which comes onto your system and asks you to buy it. It doesn't provide any security to the computer. Here is the procedure to remove it: (1) disable the proxy server for your LAN in Internet Explorer. 2) download the process explorer from ms technet. 3) locate and kill the sysguard.exe. 4) finally remove AntiVirus Live. After following all these steps reboot the computer. Protection against future intrusion is mentioned. You should be aware of the ...

The author shows how to bypass SurfControl and access blocked websites at school. He shows how to open the OperaMini website from Google and to access the demo of OperaMini in that website. Now in that demo we can key in the website address and easily access the website from there. In this manner we can easily bypass small security software like SurfControl. If you are having trouble accessing websites because of SurfControl just follow the steps in this tutorial and you will be able to acces...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to install a Wii homebrew hack using the Twilight Hack.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to backup Wii games to SD to play in HD.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to turn a Fon+ wireless router into a network tap.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to get free WiFi by tunneling through DNS.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to build a web-enable remote controlled tank.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to make a Twitter tamagotchi bot with PHP.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to set up SSH tunneling to securely transmit HTTP traffic.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to session hijack with a pineapple.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to boot Windows from a USB flash key.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to configure Cisco and iptables firewalls with a utility.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to map networks with Spiceworks.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to packet sniff networks with the fundamentals.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to break down IP and TCP header with Wireshark.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to turn any Windows application into a service.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to organize your desktop with Microsoft Scalable Fabrics.

Beat the Level 2-3 Boss in Resident Evil 5 via this walkthrough and gameplay. Resident Evil 5 (RE 5) is the sequel to 2005's Resident Evil 4. This game guide shows you BSAA emblem locations, treasures, and includes strategies for all 6 missions and boss fights.

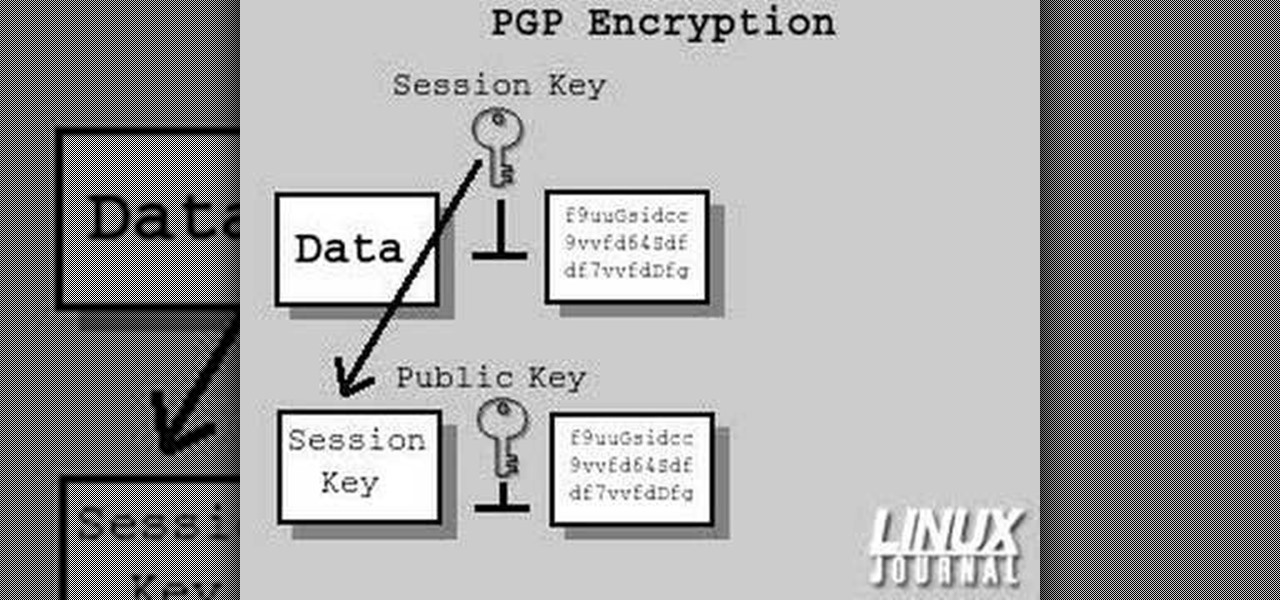
In today's time of rampant information crimes, including identity theft, security is more important to the average computer user than ever. This tutorial from Linux Journal Online shows how you can use GnuPG to secure and verify data on your Linux box. (This video was created using only free and open source software tools: TightVNC, pyvnc2swf, ardour2, audacity, jackd, LAME, kolourpaint, cinelerra-cv, mjpegtools, and ffmpeg.)

Check out this video tutorial to see how to construct an alarm system, that's based on the principle of motion detectors, which work by touch. It's very useful to catch unpleasant visitors red-handed. So make sure your chocolate bar never gets snagged again, catch the bandits with a motion detector alarm! Or just keep you kids away from the birthday present closet where peeping is not allowed.

This is a tutorial that shows you how to view and control your computer screen from your iPhone/iPod Touch. But this method is for people who have a jailbroken iPhone/iPod Touch. This works on Edge and Wifi. If you are having problems connecting try going to control panel then security center then turn your firewall off. Also try turning off anything like virus protection.

In this episode, Brandon Jackson shows how to merge two images with the Photoshop gradient tool to create a banner montage. Doug Grammar joins D.Lee Beard again, this time to explain spyware, adware, and keylogging. They explain what these threats to your privacy & computer speed are as well as how to prevent and get rid of them. Speaking of security, Jason Rybicki shows one way to tell if your privacy is being compromised on a Mac using a free widget.

Isaac gives some helpful tips on keeping your camcorder steady.

The first step to getting your life together? Getting your online security together. After all, security when you're shopping, video calling, and more means more than ever in a digital age when anyone can copy your info or try to pose as you on the web. This Premium Privacy Bundle featuring Zenmate and StartMail will give you a secure VPN and encrypt your emails, all at a bundled price. The security duo is on sale for 60% off for a limited time, which means it's just $44.99 (regularly $113).

After updating to iOS 14 or getting a new iPhone with iOS 14 preinstalled, you'll notice orange and green dots that occasionally appear at the top of your iPhone. These dots appear on all supported iOS 14 devices, from the iPhone 6S to the iPhone 12 Pro Max, and are there to protect you, but how?

If you're an avid programmer or developer, your time is likely spent creating apps and perhaps the occasional website. And while these go-to coding endeavors are exciting and occasionally lucrative, more and more coding pros are turning to careers in cybersecurity and ethical hacking — thanks to the high pay, flexibility, and unparalleled opportunities.

The iPhone 11 series models have sophisticated camera systems that include both a wide and ultra-wide lens. On top of that, the Pro models also have a telephoto lens. So you can zoom anywhere between 0.5x optically to 5x or 10x digitally, depending on the one you have. While you can pinch in and out on the screen to control the zoom, there's a way to get more granular control for photos.

Since its founding in 1984, Cisco Systems has been a global leader in information technology. From networking hardware and software to domain security and energy management, the company dominates the IT field.

Night mode on the iPhone 11, 11 Pro, and 11 Pro Max is a godsend if you want clearer photographs in dimly lit environments. But if you want to keep the image dark or full of shadows as an effect of sorts, it's not immediately obvious how to disable Night mode, which turns on automatically when the app thinks you need it. But it can be turned off.

If you've tossed around the idea of turning your interest in white hat hacking into a career in cybersecurity or IT, now's as good as time as ever to invest some time and energy into improving your skill set.

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.

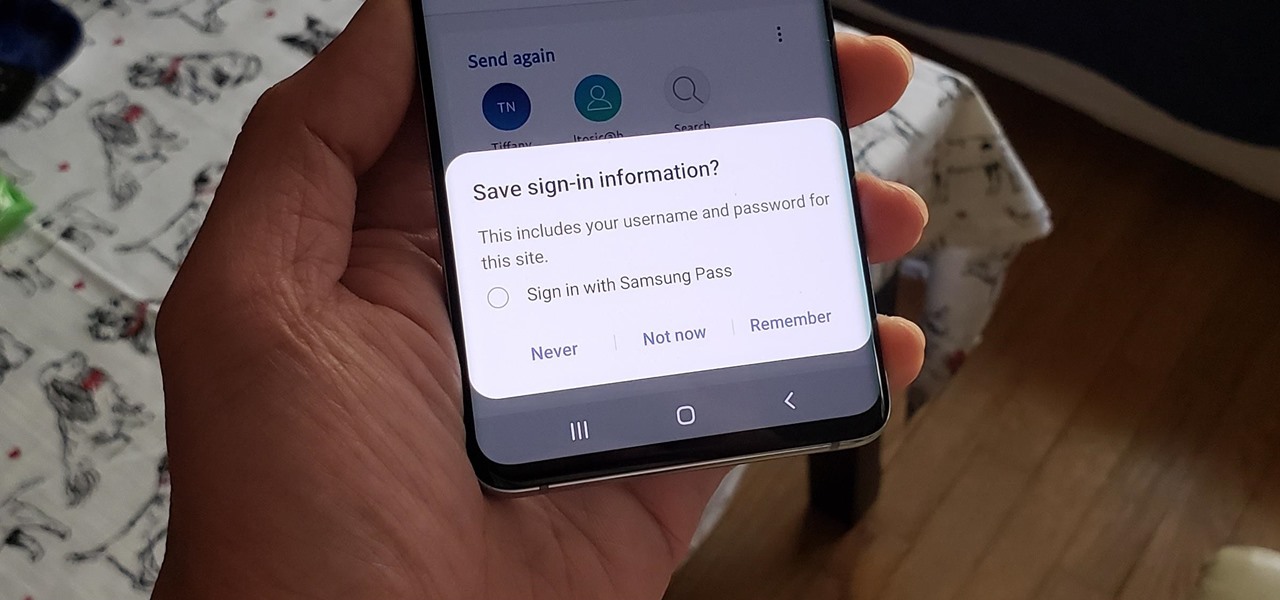
If you use Google Chrome on your computer, you've undoubtedly saved a ton of passwords since the browser always prompts you to. But Samsung uses their own password service on their phones by default, so you'll have to change a setting if you want to use your Chrome passwords to log into apps and sites on your Galaxy.

Using a strong password is critical to the security of your online accounts. However, according to Dashlane, US users hold an average of 130 different accounts. Memorizing strong passwords for that many accounts is impractical. Fortunately, password managers solve the problem.