While there are a variety of privacy-focused search engines available like StartPage and DuckDuckGo, nothing can offer the complete trust offered by creating one's own search engine. For complete trust and security, Searx can be used as free metasearch engine which can be hosted locally and index results from over 70 different search engines.

Tossing an old Android smartphone with a decent battery into your hacking kit can let you quickly map hundreds of vulnerable networks in your area just by walking or driving by them. The practice of wardriving uses a Wi-Fi network card and GPS receiver to stealthily discover and record the location and settings of any nearby routers, and your phone allows you to easily discover those with security issues.
Dr. Michael Pound, a computer science researcher and professor at the University of Nottingham, uses hashcat and 4 GPUs in parallel to go through 1o billion hashes a second in this Computerphile video. He calls his deep-learning server the "Beast." If you're new to cracking passwords, he does a great job breaking down the process of what's going on as hashcat does its magic.
Hello everybody. I'm back with Part-2 of this series. In this part we will be programming in C our server and i will be explaining one more "key concept" so everybody got a better understanding on this.

I am very new to Null Byte but I find much of its content and community incredibly interesting. I spent quite a bit of time just chronologically going through the posts and I noticed a common theme in many of the beginner posts. Many people seem to want to know the 'secret' or a paragraph on "How to Hack" and become a hacker in a few minutes. I started off this post as a reply to a question from a beginner but thought it might be beneficial to have for those stumbling across this site.

Welcome back, my fledgling hackers! One of the first issues any hacker has to address is reconnaissance. Before we even begin to hack, we need to know quite a bit about the target systems. We should know their IP address, what ports are open, what services are running, and what operating system the target is using. Only after gathering this information can we begin to plan our attack. Most hackers spend far more time doing reconnaissance than exploiting.

An internet connection has become a basic necessity in our modern lives. Wireless hotspots (commonly known as Wi-Fi) can be found everywhere!

Stay secure on public wireless networks by making your own FREE virtual private network (VPN). This tutorial shows you how to set up an OpenVPN server and connect to it from your laptop.

Here's a small-medium sized PvP arena that I made with my friend a few days back on my personal bukkit server.

In this video we learn how to use EyeTV to stream live TV on your iPhone. This will allow you to watch TV on your Mac and your iPhone as well as on a 3G network for free. To get started, plug one end of the EyeTV into the USB plug and then into the jack on the hybrid with a cable line. Now, download the most recent version of the software from the update menu. Then, go to preferences and select iPhone. After this, make sure all the buttons are selected, then exit out. Now go to your iPhone an...

Add a chat program to your website and allow the logged in users to talk to each other! You can write this program using Adobe Flash CS3, PHP and MySQL. This tutorial shows you how to write your own Flash chat program incorporating all three systems.

In this tutorial, we learn how to use the left handed column options in Gmail. First, log into your Gmail account, then click on your different emails. Open an e-mail by clicking on it, then click reply to respond to it. You can also save this, and it will save to your account. If you want to delete a message, simply select it and click on the delete button. It will now be moved to your trash, where you can keep it, or you can delete that, which will remove it forever. If you want to write an...

In this tutorial, we learn how to delete your YouTube account. First, log into your account on YouTube, then delete all your videos. Next, click on "account" at the top of the screen. Next, click on "manage account", then find where it says "delete account" and click on that. After this, you must type a reason why you are deleting your account and click on "save". Now, you will be shown a message from YouTube on deleting your account and you will be set! This is the only way to delete you acc...

In this tutorial, we learn how to set up a group on Facebook. First, log into your Facebook, then click on "groups", then click "create a new group". Now, give your group a name, description, news, email address, and contact information. When finished, click on "create group". Now you will be able to customized your group by adding images. Once you do this, you can add a website and change your different options. Allow only instructors to upload photos, because students may decide to upload i...

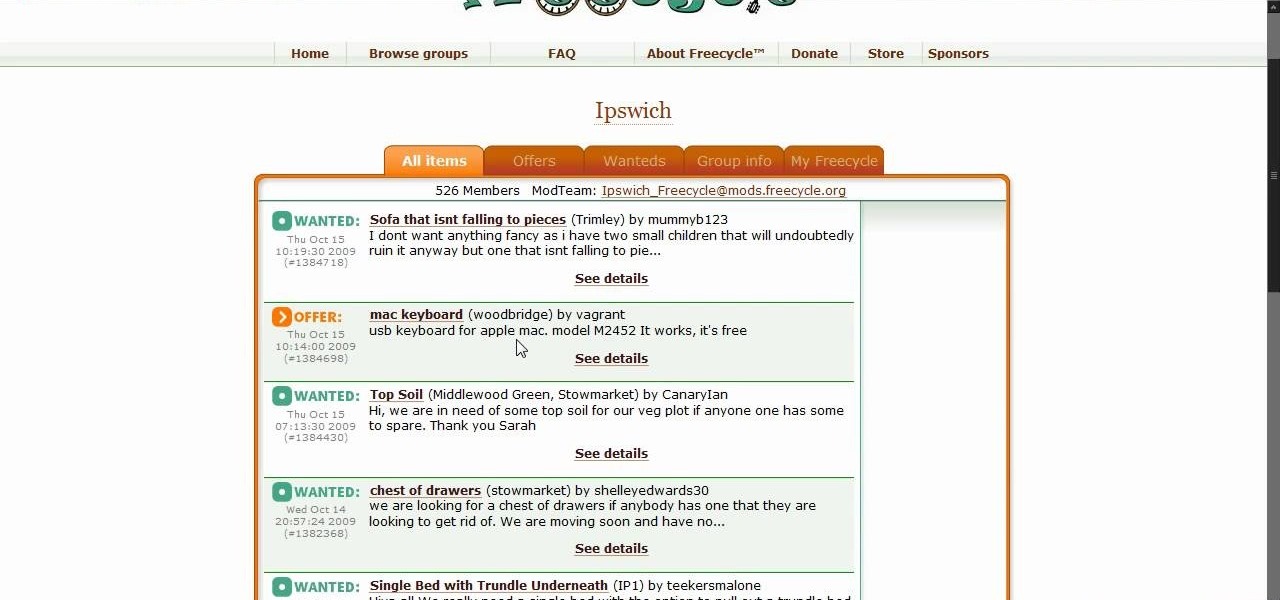
In this tutorial, learn all about Freecycle and see how you can join and get virtually anything you need for free. Moving into a new home? Nab a free sofa, fridge, TV and everything else online. Looking for a replacement part for your electronics, boxes for moving, lumber, a car.. anything? This website is extremely easy to use and is completely free and if you are willing to haul away the goods you can find many fantastic items.

In this video tutorial, viewers learn how to unsend emails with the help of Google. Users will need a Google email account. Begin by logging into your Gmail account and click on Settings. Then click on the Labs tab under Settings and scroll down the page until you see "Undo Send". Now click on Enable and click on Save Changes. Now when users send an email, they can undo the email by clicking on Undo once they have sent the mail. Users will only have 5 seconds to undo an email after it has bee...

In this tutorial, you will learn exactly how to use the Trapster app for your iPhone or iPod Touch. This app is similar to maps, but holds a ton more features. Most importantly, Trapster will give you a heads up for all of the police trap points that are currently on your route. Trapster works because users submit the locations of known traps so you can log in and find them. Stay safe, and avoid tickets with this handy iPhone application.

Use Microsoft Windows 7? Miss the old Ctrl-Alt-Delete log-in prompt? It's easy to restore. So easy, in fact, that this home computing how-to from the folks at CNET TV can present a complete overview of the restoration process in just over a minute's time. For more information, and to get started restoring this useful security feature on your own Windows 7 PC, watch this free video tutorial.

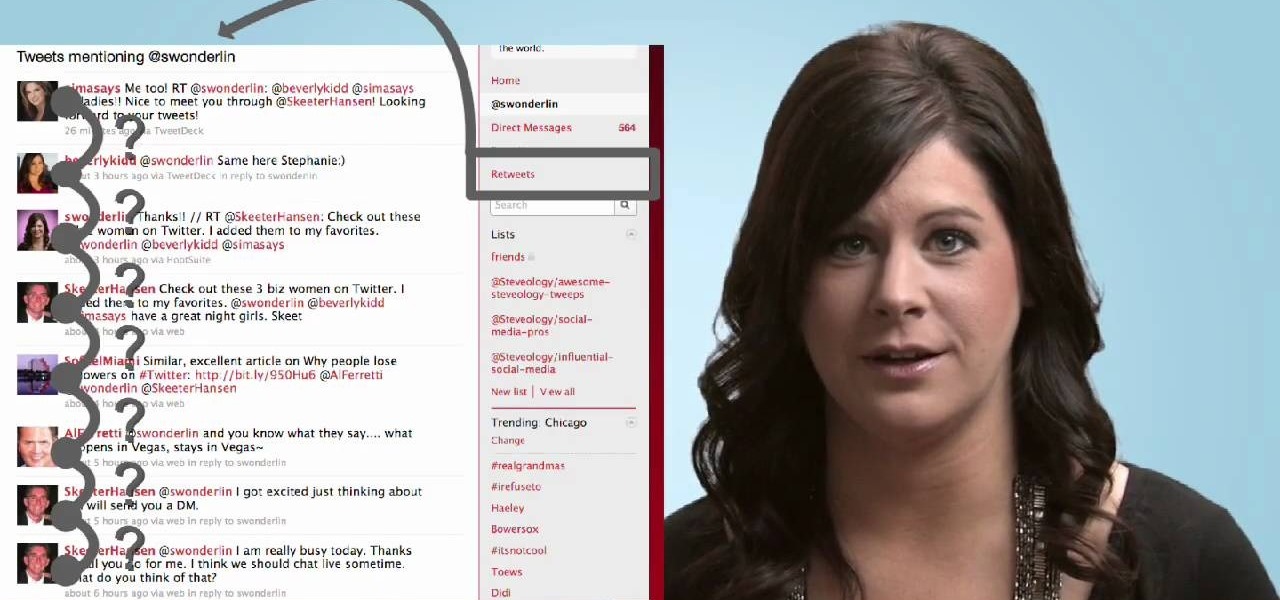
In this video, we learn how to retweet in Twitter with Stephanie. There is a new layout on Twitter which may look confusing, but is very user friendly. First, log into your Twitter account and go to your home screen. On the right hand side you will see a button that says "retweets". Click on this and you will see three selections. Click on "your tweets, retweeted" and you will see which users have retweeted something that you wrote! From here, you can also go and thank those people for retwee...

In this tutorial, Christopher Prince Boucher shows us how to suggest a friend to another friend on Facebook. First, log into your Facebook account and look through your friends. Find the person you want to suggest to your friends and click on their page. On the left hand side will be a button named "suggest to friends". Once you click on this a new window will pop up and you can choose which friends you'd like to suggest this friend to. Once you pick out all friends, click "suggest" and it wi...

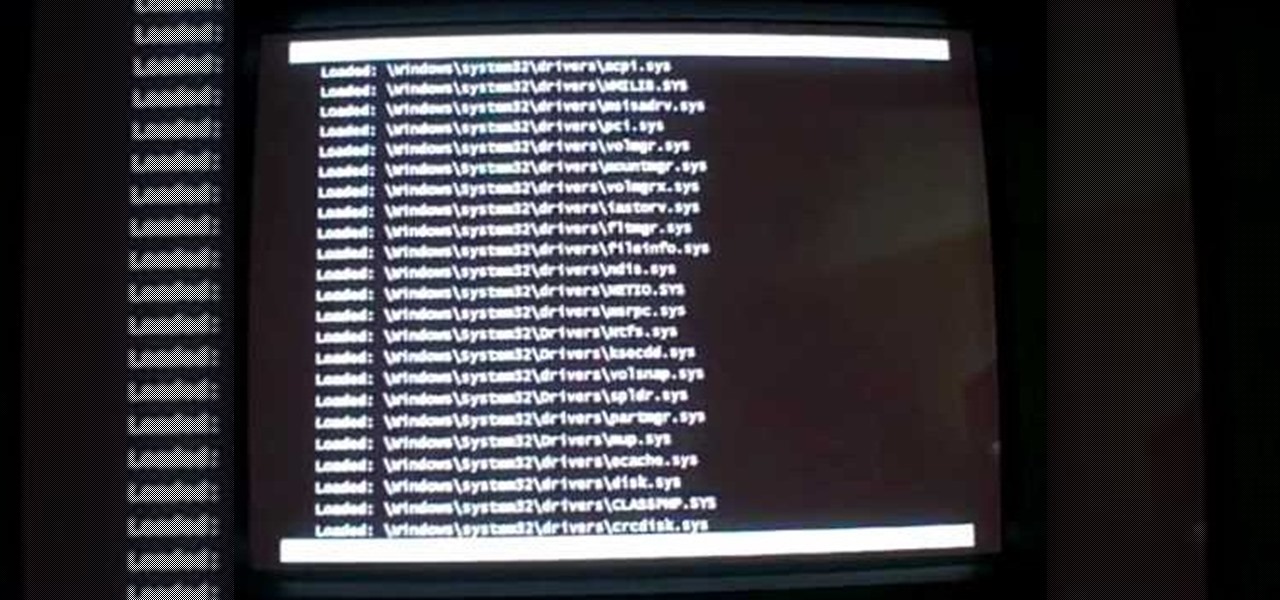
In this video tutorial, viewers learn how to start a Microsoft Windows computer in safe mode. Begin by turning on your computer. As your computer starts up, press F8 before Windows launches. Tap the F8 key slowly (about 1 second apart) as soon as the computer starts up. Keep tapping until the Windows Advanced Options Menu appears. The use the arrow keys to select the appropriate safe mode option and press ENTER. You may need to log into your User account. This video will benefit viewers who u...

This video describes the process of changing the audio on a YouTube video that you have already uploaded. The video is presented by Helplines.com and is in their technology series. We start out logged into YouTube and click on Uploaded Videos, then choose the video you would like to change. Click on the Audio Swap button that is just below the video. You can then choose the I'm Feeling Lucky button to have YouTube pick the audio for you. Or browse through the selections to find an appropriate...

This helpful video explains how to use letters when dialing on a Blackberry. Many companies have words in their phone numbers so Darci Larocque shows us how to dial those letters. All you have to do is go to the call log, and hold the key in, and type in whatever word you are trying to dial. She also shows us another tip: if you are calling an office and you need to enter in someone's last name, you can do that the same way. Blackberry users should definitely view this video.

In the GetConnected TV show BlackBerry expert Darci Larocque from Swirl Solutions gives an easy tip on how to call voicemail directly with one (1) key. This option can be seen in other cell phones also, but in a BlackBerry you can set a password for this. Hold the green button or call log , go to menu - Voice Mail, set your password, click escape and save. Now when you dial No.1 or hold it down you go directly to your voicemail.

The application the makes Apple's Final Cut Studio is the film editing app Final Cut Pro. With its ability to log and capture video onto your hard drive for editing, you can easily edit and process your indie film, or maybe even a professional movie. Final Cut Pro is a non-linear editing program that even the best editors use.

The application the makes Apple's Final Cut Studio is the film editing app Final Cut Pro. With its ability to log and capture video onto your hard drive for editing, you can easily edit and process your indie film, or maybe even a professional movie. Final Cut Pro is a non-linear editing program that even the best editors use.

The application the makes Apple's Final Cut Studio is the film editing app Final Cut Pro. With its ability to log and capture video onto your hard drive for editing, you can easily edit and process your indie film, or maybe even a professional movie. Final Cut Pro is a non-linear editing program that even the best editors use.

My how-to on Post and Dowel Fencing. My buddy Sven and I, with the help of landowner Rex, installing a massive post & dowel Fence. You need a level, post hill driller, rock bar, and stakes. There are terminator, corner and line posts that have holes specifically for its position in the fence. It's like Lincoln logs that snap together. Lengths of the post vary, but you want 1/3 of the post underground. This is great for lining your property or farm.

All the files you need are in a free download on DevelopPHP. PHP has to be on a server. It will not run on a local machine. Type your name. There are two variables which show up in the dialog boxes (which are stacked.) You can change the user name. It sets up a URL request and a URL loader and sends some URL variables and are placed into the value of names and pairs. They get posted to the PHP file. Place the URL reference location of where the PHP files are on your server in the line that sa...

This video tutorial from iTouchMaster2 shows how to SSH to iPod or iPod Touch using FileZilla application.

Nowadays many schools and colleges have blocked the social community sites from accessing them through school computers. The video shows how one can access to these sites using a command prompt.

Have you ever thought of building your own social networking site? Before you get to making websites like Facebook, you need to start off smaller, and this 29-part video series is where to begin with developing a social networking community website . Before you start with these lessons though, make sure you have all the following:

When you need a file on your Mac as soon as possible, you usually have to get your MacBook or hop on your iMac, Mac mini, Mac Pro, or Mac Studio. But that's too much work if you're in bed, lying on the couch, or outside in the fresh air. Why even bother when you can access that file directly on your iPhone or iPad — without moving an inch?

There's a tool on your iPhone that can help you with your overall emotional well-being, one that can help you be more aware of your emotions throughout the day and build resilience against the stressors in your life.

Compromised uTorrent clients can be abused to download a malicious torrent file. The malicious file is designed to embed a persistent backdoor and execute when Windows 10 reboots, granting the attacker remote access to the operating system at will.

Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

If you don't want the large and permission-hungry Facebook app on your phone, the perfect solution is to create an app icon for the Facebook mobile site on your home screen. The website version of Facebook doesn't run background tasks, has no distracting notifications by default, you won't be giving Facebook as much data, and your phone's battery life will be improved.

Automating port scanners, directory crawlers, and reconnaissance tools can be complicated for beginners just getting started with Kali Linux. Sparta solves this problem with an easy-to-use graphical interface designed to simplify a penetration tester's tasks.

EternalBlue was a devastating exploit that targeted Microsoft's implementation of the SMB protocol. Metasploit contains a useful module that will automatically exploit a target, as long as it's vulnerable. But what if we wanted to exploit this vulnerability without Metasploit holding our hand? It can be done using a Python file to exploit EternalBlue manually.

When you don't want certain friends viewing your account or just need to take a break from social media, Instagram lets you do so. While you can completely delete your Instagram account, then start over when you're ready again, it makes much more sense to just disable your account temporarily. Doing so will hide your profile, photos, comments, and likes from everyone, including your friends.