Many windows users, if not all, run into a virus infection once in a while. This is unavoidable when using Microsoft's operating system. Without digressing too much, the fact that Windows is such a popular OS with no controlled software sources makes it easy for viruses and malware to spread. And while there's a plethora of antivirus tools for Windows, sometimes infections (such as certain scareware) can disable the install and/or use of antivirus systems and render your OS unusable until cle...

I want to write this article because in my childhood, I had experienced internet stalking which ultimately ended in physical stalking which then lead to several attempted abductions. I have now learned how to use the internet safely, who to communicate with and I've learned how stalkers work.

In this article, I'll show you how to send SMS messages with Python. You'll need Python 2.7 or later, urllib and urllib2. The code basically uses an online text messaging service to "POST" html data, as if a person was entering the data themselves. The uses for something like this are unlimited. For example, I modified the basic code so I would receive a text message letting me know every time someone rang my doorbell. The program could interface with Arduino through a serial port, and send d...
Shortening URLs has become a necessity in this age of Twitter and limited-character status updates. It not only allows us to cram more words into our oh-so-important Twitter statuses, but it also helps us with a few other things.

Welcome to the Goodnight Byte for HackThisSite, Basic Mission 4. In Friday's session, we tackled some coding in Gobby. Nothing special, just a few modifications to the NullBot script we made a few session ago, and some education on regular expressions. Apart from coding, we did our scheduled HackThisSite mission. We had to take on some JavaScript, which was a new thing for Null Byte. This mission taught us about client-side HTML manipulation through JavaScript injections. This just means that...

This is Null Byte's fourth part in a series about fully securing our computers (Part 1, Part 2, Part 3). In our last Null Byte, we went over how to encrypt an entire operating system to protect our data, however, this doesn't fully protect us. In the case of legal extortion, the government can actually make you give up your cryptographic key to your computer so that they can look through it.

Natural processes often create objects that have a fractal quality. Fractal branching patterns occur in plants, blood vessel networks, rivers, fault lines, and in several electrical phenomena. Many of these processes take lifetimes, or even occur on geological timescales. But this is not the case for electrical phenomena. They often occur near instantaneously. One example would be the branching patterns that sometimes occur in lightning.

This is the first of a multi-part series on steganography techniques. Steganography, the art of hiding things in plain sight, has existed for a long time, and in many forms. When you manipulate the alphabet to have your own cipher and decipher, this is considered steganography.

This Null Byte is the first part in a mini-series on the art of Social Engineering. I will be teaching you how to effectively defend yourself against it.

Since PDF files are so popular in both our daily life and work, we see them everywhere. And sometimes we find there are terrfic images or text in the PDF files and we want to save them as seperate files for future use, such as in a presentation or post. Here's the question: how can we save those elements from the non-editable file formats?

The artwork for Minnesota's Land O' Lakes butter packaging is classic, dating back to 1928 when it was first created by Brown & Bigelow illustrator Arthur C. Hanson. The logo was updated ("modernized") once in 1939, again in the '50s, and has undergone minor modifications here and there since. The legendary packaging is good for two rather nerdy tricks: A) a very trippy optical illusion and B) a very infantile boob illusion.

More than a year ago, Twitter rolled out the first phase of its Promoted Tweets ad service, which consisted of selected tweets from advertising partners like Best Buy and Sony Pictures receiving "promoted" exposure in the search results pages on Twitter and in the trends lists. These ads were clearly labeled as such, so it was never any real bother to Twitter users.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.
To go Open Source or go proprietary? There is a common conception that open-source is unsafe and insecure and therefore companies should rather go for proprietary solutions. They think that because software is termed "open-source", that the world can see the vulnerabilities of the software and might exploit it, and less informed people tend to think that open-source software can be modified while it is running.

These are the KGB Agent Guidelines as taken from 542542.com/guidelines. kgb Guidelines
On Thursday, March 9, there was a news story on the evening news about Khan Academy (NBC News). The story began when Sal Khan started tutoring his cousin in 2004. Since he was in Boston and she was in a different city, he decided to make and post videos on YouTube so anyone could watch the videos. Later he added videos for her brothers and for people that contacted him with requests for other videos. During this time Sal had a job that he later replaced with another job. Today Sal has 2010 vi...

These impressions are coming from a person completely new to the Final Fantasy Online world. Never played FF 11 or the FF 14 Beta. This game is not friendly to new people. The account creation is a Kafka like experience in things that don't make sense. For the game itself, the beginning tutorial is awful and does not really teach you the basics of combat. Here is a small breakdown of my opinions, with the good points first so that they don't get overshadowed by the negatives.
Microsoft Ribbon hero is an application that turns the office into game. It is designed to boost skill and knowledge in Microsoft Office’s latest version. It is released with office 2007 as a social game for increases productivity in office applications. It is compatible with Microsoft Excel 2007, Microsoft Word 2007, and Microsoft PowerPoint 2007 as well as those three programs in Microsoft Office 2010, available as a beta download.

Go to http://yourguitarsage.com/ to find out how to order my ebook containing charts for over 170 tunes and constantly updating.

This method is easy, intuitive and requires very little math. You will need:

WikiLeaks. In recent weeks, it's been the hottest topic on the web. It's been attacked on a multinational level by political influence peddling.

A cell phone is capable of all kinds of tricks, but you can use your cell for more than just photos, texts, and phone calls. Here are some of our favorite mobile phone services, such as Shazam and AQA. Use 5 different cool services on your cell phone.

Microsoft's new mobile operating system is officially out on the market, and programmers are hard at work developing new mobile apps for Windows Phone 7 devices. But there's a lot going on in this new platform, which means there's a whole lot to be learned, and the only man in the world with a Windows tattoo is here to help— Charles Petzold.

Help your non-active friends remove the FarmVille application. We all have friends who have installed Farmville at one time or another and then end up quitting the game. But since they might be real life friends, we do not want to delete them from our friend list. Here are some directions to remove the application.

To create an elegant WordPress blog or website from scratch without being noticed that you're a complete beginner, you need that drive and pairs of eyes and ears. It may seem difficult at first but it can truly be fun and exciting.

On June 23, 2003, Linden labs created a free client program known as Second Life. This program allows users, or residents, to interact with each other in a virtual world by using avatars. Thanks to this program, residents are able to explore, socialize, and create and trade virtual property, and services with each other. Second Life has become one of the most popular programs used by various age ranges from 16 to 60, but how do you enter this world and get your own avatar?

In my recent Darknet series, I attempted to connect the dots on the Deep Web. I covered the two largest anonymity networks on the Internet today, Tor and I2P. While my initial four articles were meant as an introduction, I ended up receiving a lot of interesting comments and messages asking the technical differences between the two. I'd like to thank all of you for letting me know what was on your minds, as you should always!

Since the internet is becoming more and more important all the time in regards to overall marketing plans for many companies, it’s imperative that the company website be up to the task of attracting visitors and converting them into customers. There are many methods and techniques to do this and for that reason it’s usually preferable to hire a company that focuses on online marketing or search engine optimization (SEO) to do this work.

It's been a long journey for Netflix users. At first, it was a rough ride as Netflix struggled to find its place in the homes and hearts of movie watchers everywhere. Once monthly subscriptions bumped off the pay-per-rental charges, Netflix soared to great heights, known for their flat-fee unlimited rentals without due dates, late fees, or shipping and handling fees. And it was smooth sailing when streaming services were incorporated into monthly plans, with customers being able to rent DVDs ...

If you've gained entry into Google+, one of the first things you should do is adjust your Google account settings. Your settings will now look quite different, and you can adjust your notifications, password retrieval methods, and more. There are many settings that you may not have been aware of before.
International Pet Travel: Taking Your Pet Animal to a Foreign Country If you are taking a pet to another country (permanently or for a visit), contact that country's consulate or embassy for information about any requirements that you must meet. A list of consulates can be found at Foreign Consular Offices in the United States

There are so many different ways to cast on knitting. I have my own favorite. It's the way I learned when I first started knitting. My way is called TWO NEEDLE CAST ON. I like this 2 needle method because you don't have to guess how much you need to measure out a length of yarn at the beginning. I also think it makes a tighter and straighter edge.

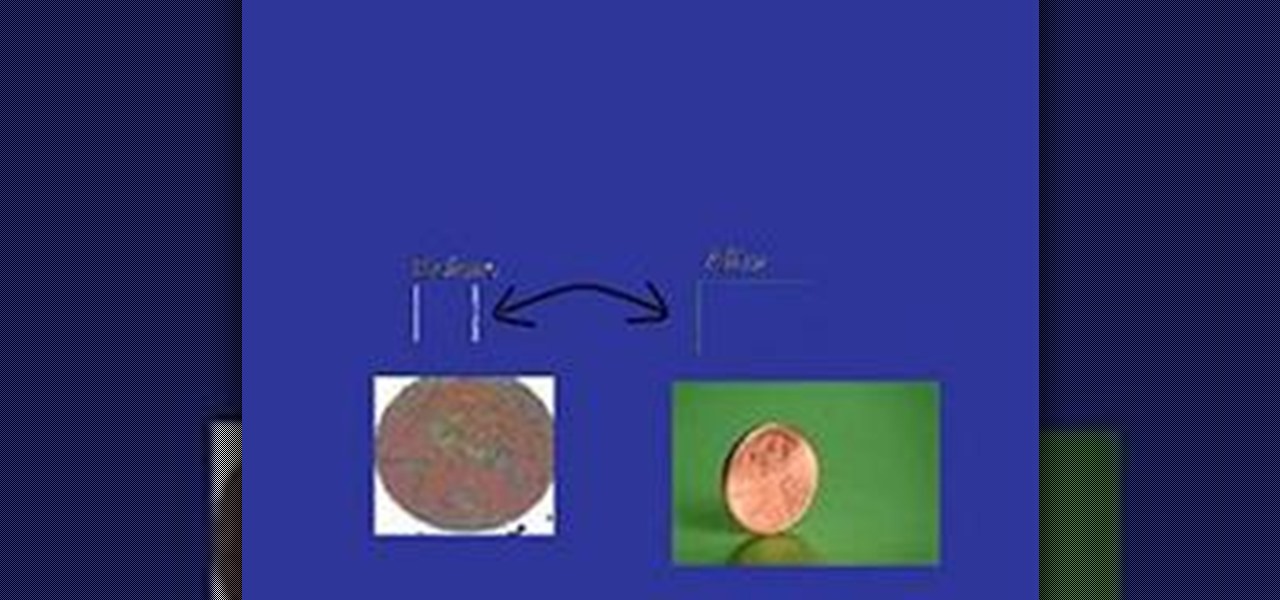
Do you want your old, dirty pennies to be shiny and glistening again? This article will demonstrate how to return their lovely allure using only three items: salt, lemon juice, and a jar.

Banana bread has always been a favourite treat whether it was fresh from nanna's oven or from the local bakery. The addition of Mars Bars or another one of your favourite chocolate bars can be a great addition for the kids as long as they eat their vegetables first.

If you've seen my basic sounds tutorial (and if you haven't, you should!) you'd know a rimshot sound instead of a snare. The classic snare, while considerably more tricky, is far more versatile.

Shave Your Pubic Area Things you will need:

Installing the Software Download the PC/Mac client from Dropbox for your computer. When installing the software you will also be prompted to create an account. Please do so at this point. This account gives you free access to 2 gigabytes (gb) of cloud storage that can be accessed from any PC/Mac or Dropbox Enabled Device.

Three-dimensional printing is one of the many wonders of modern technology. It's the first step towards real life Star Trek replicators and Timeline-esque teleportation chambers. While we aren't at the level of reconstructing strands of DNA, it's already possible to make tons of fun and useful designs on a 3D printer.

As discussed earlier, there are many ways to view the upcoming solar eclipse, whether it be with actual eclipse glasses, welder's lenses, eclipse-approved filters, or a solar telescope. If you can't get your hands on any of those, the safest way to view the solar eclipse this Sunday, whether it be annular or partial, is with a projection method.

Last time, we looked at archaic cryptography, so you should have a basic understanding of some of the concepts and terminology you'll need. Now, we'll discuss one of the most important advances in computer security in the 20th century—public key cryptography.