
How To: Automate in FL Studio 7
In this music production tutorial you will learn how to automate in FL Studio 7. Get a quick overview of 5 methods of automation using FL Studio 7.


In this music production tutorial you will learn how to automate in FL Studio 7. Get a quick overview of 5 methods of automation using FL Studio 7.
These two Houdini 9 lessons illustrate a valuable and efficient means of modeling an animated surface in a manner not generally considered. It provides an explanation of the advantages to this approach and compares it to a more traditional means of animating a surface. So watch the tutorial and learn how to animate a stingray in Houdini 9 using newer style animation methods.

Jordan shows us a simple way to remove the red eye created by the flash of a camera using Adobe Photoshop. No matter where the red eye came from, you can remove it easily from any picture after watching this Photoshop tutorial. There are many ways to remove red eye and some are dirtier than others, but this method will give you a nice natural looking pupil in the end.

Watch this winds tutorial video to learn several different ways to play sharps and flats on your pan flute. You can push the flute into your lip, tilt the instrument, lower your jaw, or push your top lip out to cover part of the opening. These four methods allow even beginners to easily play sharps and flats on the pan flute.
There are a lot of ways to keep your camera from shaking. Most of these involve expensive devices known as tripods. If you're super stingy and don't want to spring from a tripod, this video tutorial will show you how to make one using only a rubber band. The method shown in this cinematography video is small, simple, and very effective for keeping your camera from shaking.

This is how to make a DIY aquarium or fish tank background. Some people's methods may differ from these, but this is the easiest, most inexpensive way. You may want to listen to the Incubus song "The Warmth" while you are doing it. (Wait--is that Brandon Boyd?)

Although rare, sometimes a purchased song or video doesn't download properly. If this happens, there are methods iTunes provides to look for the lost music.

Learn about all the different types of numbers, like integers, irrational numbers, and real numbers, in great detail. Also includes how to use a number line, a dichotomist tool, and other methods of number manipulation.

Having trouble with your chess game? Well, try this "double attack" method to do a simultaneous attack of one piece against two opponent pieces. This is also referred to as the "fork."

This video will show you how to replace a wick in a standard Zippo lighter. This method can also be used in many other similar style lighters. As you will see in the video, you might not even need to change it, but rather just use what's left. There's a lot hidden in there!
The split stitch is another easy hand embroidery stitch, perfect for beginners and used often by advanced embroiderers. Here's a tutorial from Needle 'n Thread that will teach you two methods of using the split stitch.

In this soldering tip video brought to you by BEST, Inc. Norman Mier explains how to prepare through-hole components for installation using lead-free solder.
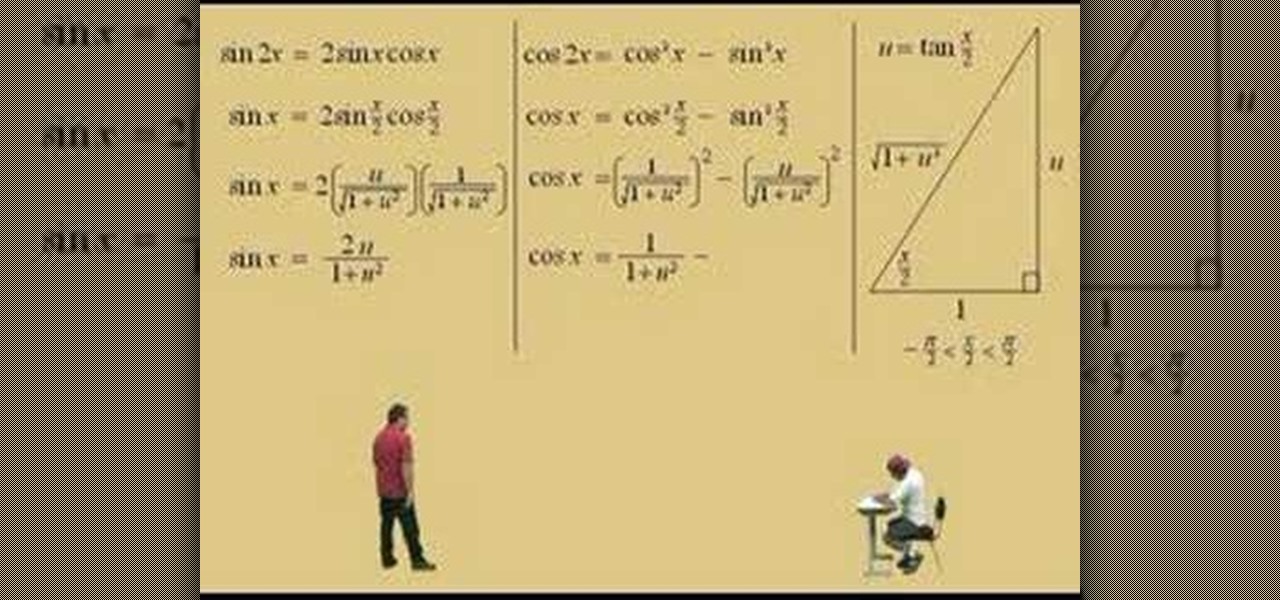
Lawrence Perez, from Saddleback College, and his assistant Charlie, give this two-part calculus lesson on integrating with special substitutions; rational functions with sine and cosines: Karl Weistrass method.

Learn how to perfect that upstrum and ghost-strum on your acoustic guitar with Charles Sedlak. What's a ghost-strum? Why don't you stop asking questions and just watch and see for yourself?
Violin Lesson #40 -- Legato Bowing (Smooth Bow Changes). Todd Ehle shows how to accomplish smooth bow changes with the legato method in this lesson.

Be green and eco-friendly by learning about compost. This video shows the basics of compost, composting materials, and the different methods of composting.

We may not all be Macgyver, but we can certainly channel our inner detective by bolstering our lock picking skills. And some of the hardest locks to crack open are combination locks, which have several disks are require advanced lockpicking skills.

This video shows basic kendo footwork (ashi-sabaki). In this video, very basic ashi-sabaki are introduced such as suri-ashi (gliding/sliding) and okuri-ashi (very basic footwork). There are also some basic training methods of ashi-sabaki.

This video demonstrates how to make a glass hummingbird bead with the lampworking method. Watch for efficient instructions and a very clear view of the process!

Barry Fahr, an associate professor of drawing at Otis College of Art and Design, demonstrates how to create a still life drawing of a red delicious apple.
No website will be inaccessible and no web filter will deny you content once you learn the skills presented in this internet hacking video.

Crunches on the Swiss ball offer several advantages over more conventional methods and machines. When done correctly the Swiss Ball crunch is super effective.

Jeff Schell walks you through simple yet effective methods to show two people having a phone conversation on screen at the same time. Jeff starts by showing you how to quickly make a picture-in-picture effect in Premiere Pro CS3, and then adds on a cross-dissolve transition to fade the video in and out. Jeff then demonstrates how to use the Position property to slide a clip to one side, so the people on the phone are side by side.
Did you know that malicious people can use scanners to read the Radio Frequency Identification (RFID) chips in your credit cards and identification documents and steal your personal information? Learn to protect your personal information from hackers and scammers with this simple method involving aluminum foil.

People are terrified of cooking rice for some reason, and claim that it never comes out right. They say it’s either a big gluey mess, or crunchy and under-cooked! Well, this method should fix all those problems.
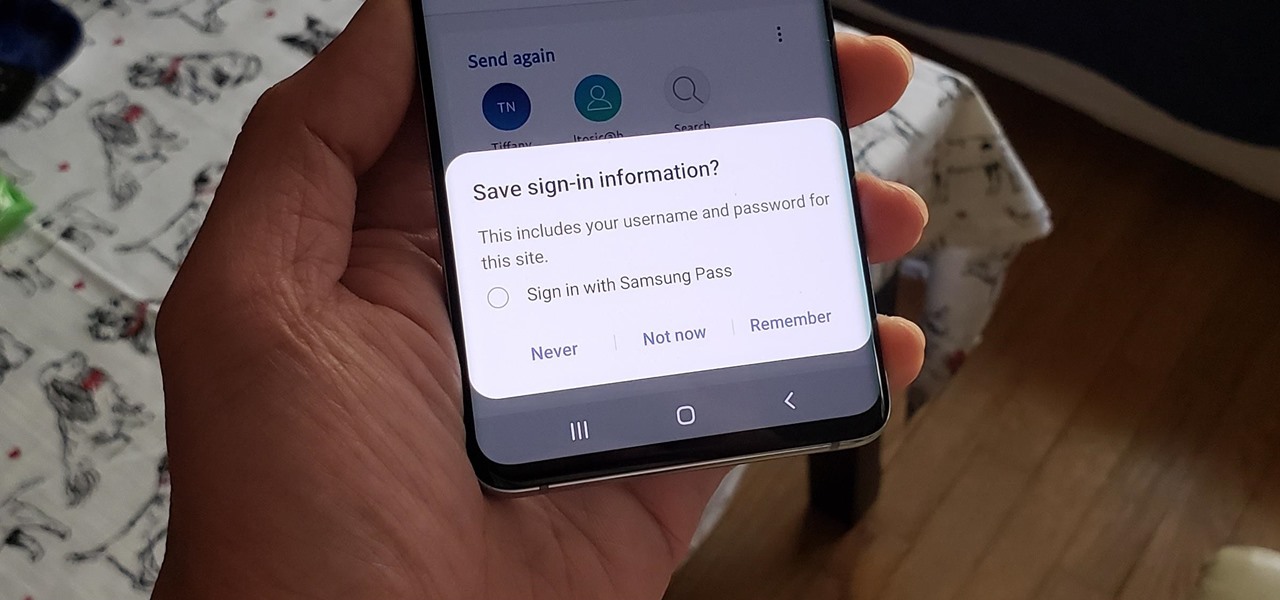
If you use Google Chrome on your computer, you've undoubtedly saved a ton of passwords since the browser always prompts you to. But Samsung uses their own password service on their phones by default, so you'll have to change a setting if you want to use your Chrome passwords to log into apps and sites on your Galaxy.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

The spatial computing world of Magic Leap is no longer limited to the rarefied tones of Sigur Rós and Sennheiser's Ambeo Augmented Audio app. Now, the entire music universe will be at your augmented reality fingertips.

Trying to figure out which music streaming service to subscribe to can be a difficult task when the playing field is so crowded. Each has its benefits, as well as downsides, so finding the right one for your needs and wants can take a lot of overwhelming research. But we've done all the research for you to help you find the best music subscription your money can buy.

Whether you're used to 3D Touch or Haptic Touch, deleting and rearranging apps and folders on your iPhone is a little bit different in iOS 13.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

Gathering information on an online target can be a time-consuming activity, especially if you only need specific pieces of information about a target with a lot of subdomains. We can use a web crawler designed for OSINT called Photon to do the heavy lifting, sifting through URLs on our behalf to retrieve information of value to a hacker.

By far the most significant development for AR in the coming months and years — the development that will drive AR adoption — will be our reliance upon the AR cloud.

The augmented reality industry has an insatiable lust for 3D content, which makes an investment of $48 million into Matterport a no-brainer for investors.
Open TikTok, and you might find yourself spending hours watching video after video. While each video is usually pretty short, it's highly possible to binge-watch hundreds at a time. It's even more fun to create your own. But as a parent, you may not want your children falling into this same trap, and it's easy to limit how much time they spend watching TikTok videos on their iPhone.
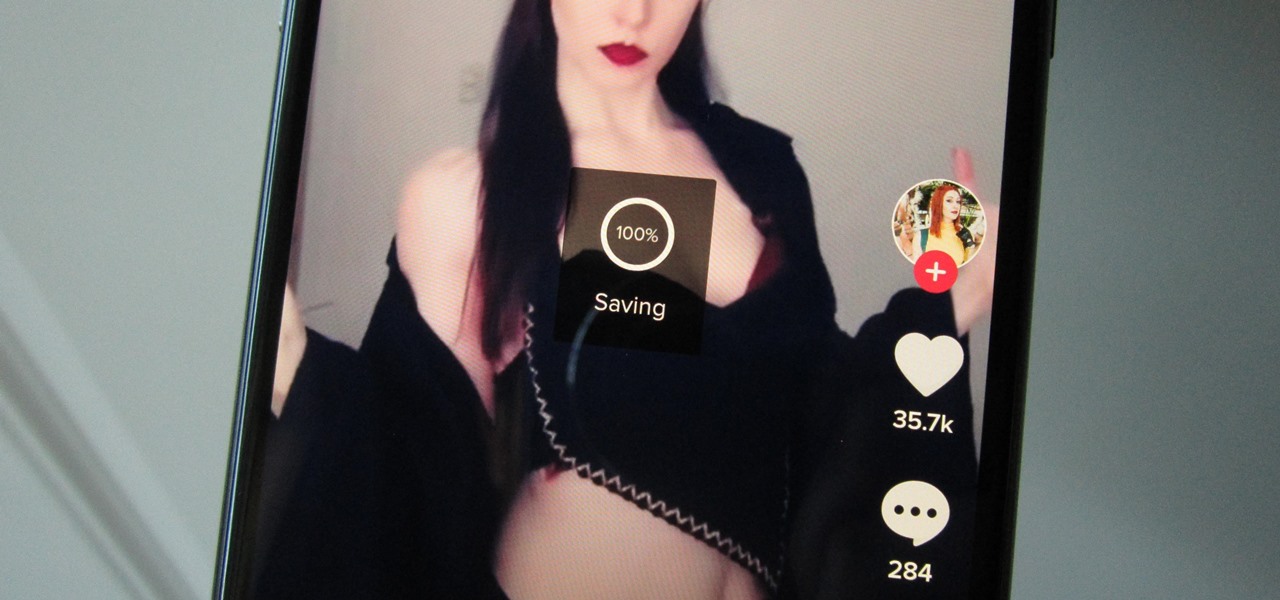
Many apps, including Facebook, Twitter, and Facebook, do not let you download videos, even if they are living on your own account. Saving these videos usually requires a third-party app or screen recorder, which is inconvenient and can result in loss of quality. However, TikTok, the newish popular short-form video platform, makes it easy to download videos — even if they're not yours.

The ability to stay organized and be resourceful with data gathered from recon is one of the things that separates the true hackers from the script kiddies. Metasploit contains a built-in database that allows for efficient storage of information and the ability to utilize that information to better understand the target, which ultimately leads to more successful exploitation.

It's no secret that MoviePass is a shell of the service it once was. The primary $9.95/month plan for three movies each month is inconsistent and can change drastically depending on your location. Thankfully, MoviePass isn't the only movie ticket subscription service available. We've compared all the best plans on the market to help you find the one that's right for you.

In the world of technology, there's often a trade-off between convenience and security. The Java Remote Method Invocation is a system where that trade-off is all too real. The ability for a program written in Java to communicate with another program remotely can greatly extend the usability of an app, but it can also open up critical vulnerabilities that allow it to be compromised by an attacker.
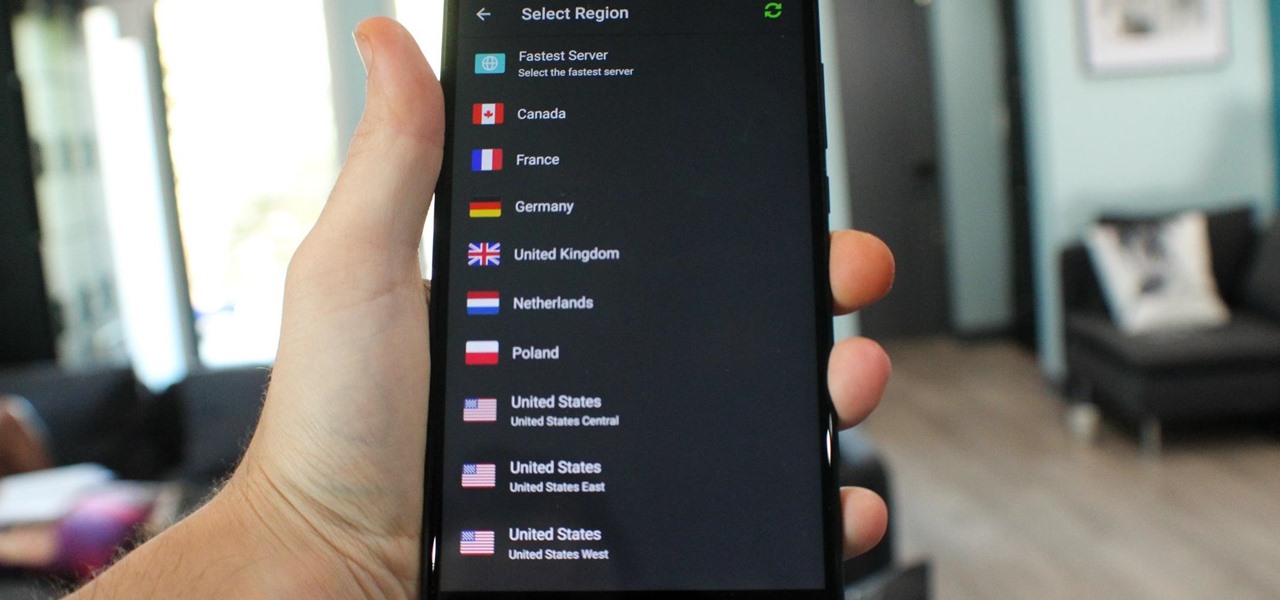
What you see when you open the Play Store is completely dependent on your country settings. Search results and top charts are specific to each region and there are lots of popular apps and games that simply won't show up unless your Play Store country matches up.