Before you sell or give away an old iPhone, Find My iPhone, which works in conjunction with Activation Lock (Apple's anti-theft system) needs to be deactivated from your iCloud account. This also applies if you've lost your passcode and are locked out of the device, if you're restoring to a previous iTunes backup, or just want to remove it from your list of iCloud devices.

Fall is the time for comfort foods—and what is more comforting than crusty bread slathered in melted cheese? Owning a fondue pot is both convenient and wonderful, but not all of us have the luxury of space for nonessential kitchen appliances. However, there are plenty of ways to make an absolutely delicious, lump-free fondue without the traditional equipment.
Task Manager got revamped quite a bit in modern versions of Windows. First introduced in Windows NT 4.0, it's become pretty popular among more advanced users. In Windows 10, Task Manager is not just a task manager anymore, it's also a system monitor, startup manager, history viewer, user controller, and the list goes on.
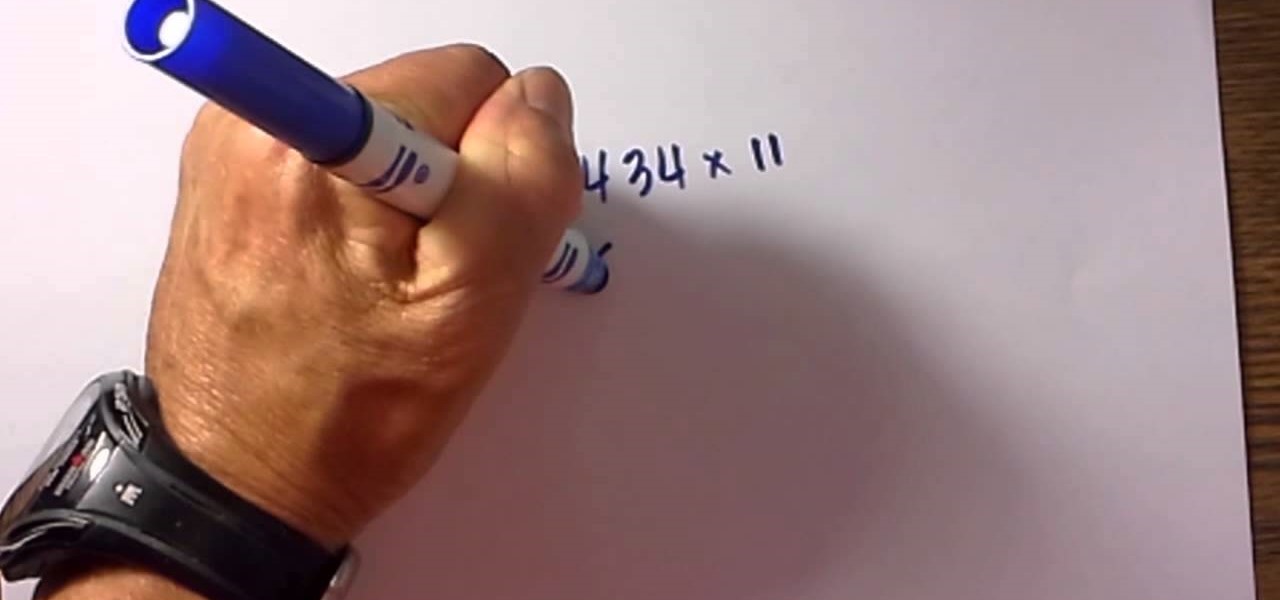
Yes, with this simple technique you can multiply 2 digit numbers in your head. The video also reviews a really easy method for multiplying larger numbers by 11 in a simple fashion.

Piracy, it can be argued, is the scourge of the internet. But when it comes to music, sometimes it's best to give a listen to a track or album before deciding to spend your hard-earned money on fully supporting it.

Cooking Steak directly on the coals with no grill. Given many different names including caveman steaks or dirty steaks, this method involves placing the steak directly on red-hot lump charcoal to obtain a fantastic texture & taste that's as good as most restaurants.

In this tutorial I will be explaining the purpose of unique encryption/decryption scripts ( I will be referring to these at "UEDS" for this tutorial). Then, I will show you how to make one. Finally I will talk about the downsides to the method I use. I will also provide links explaining the concepts and algorithms used in encryption to anyone who wants to see what is going on under the hood.

The telecommunications industry has come a long way since Ma Bell opened the first telephone exchange in the late 1800s. With the advent of fiber optics and wireless broadband technology, we no longer have a need for a dedicated phone connection, as today's data networks can carry much more than a simple voice conversation.

Welcome back, my rookie hackers! In my ongoing attempts to familiarize aspiring hackers with Linux (nearly all hacking is done with Linux, and here's why every hacker should know and use it), I want to address a rather obscure, but powerful process. There is one super process that is called inetd or xinetd or rlinetd. I know, I know... that's confusing, but bear with me.

Applications like Apple Maps, Google Maps, and Waze save every location you visit or search for as a way to speed up future searches and to find commonly-frequented places. But what if you go somewhere unsavory and don't want anyone knowing?

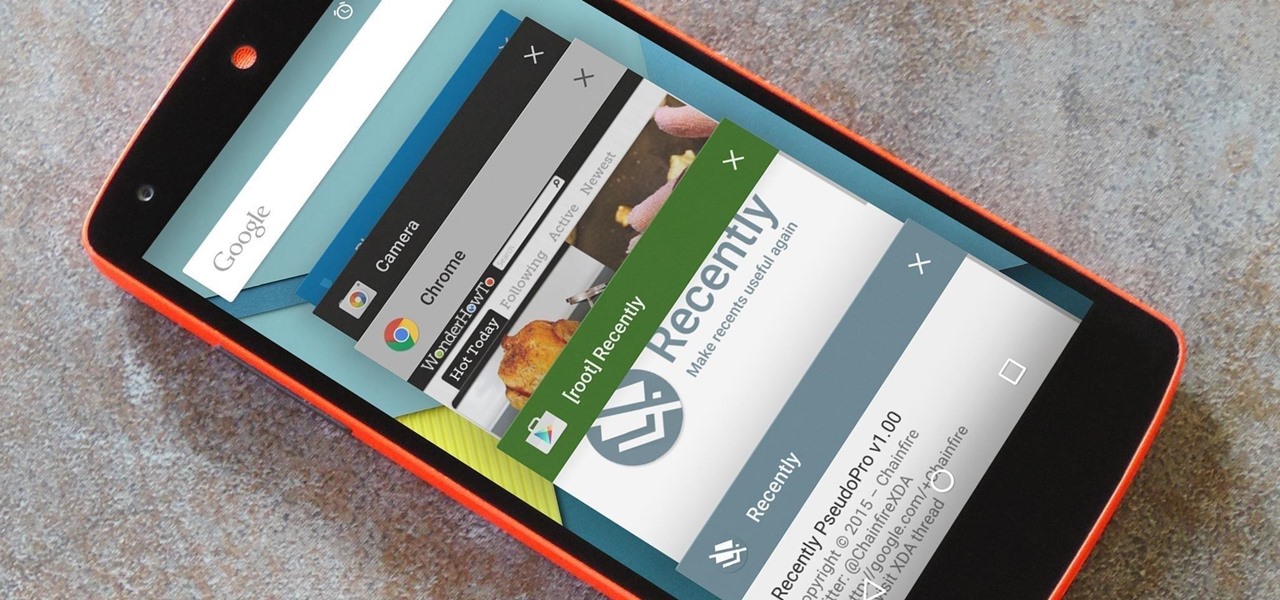
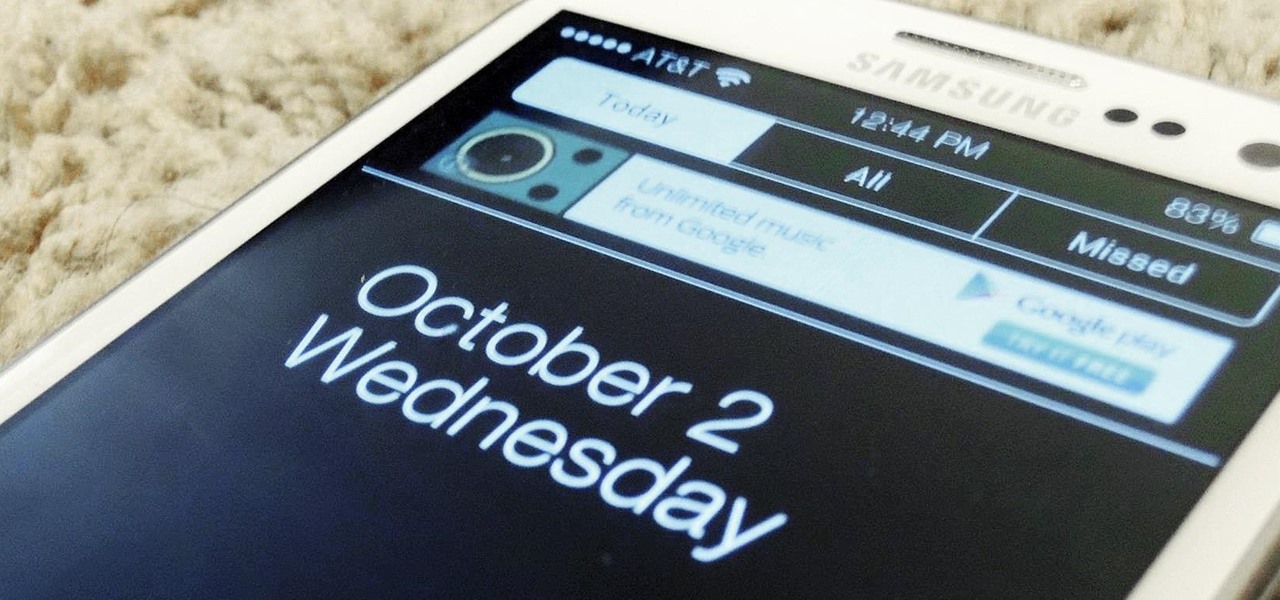
As is the case with most software updates, Android 5.0 brought changes that were viewed by users as somewhat positive and somewhat negative. This generally happens because we're accustomed to the old way of doing things, and changes, no matter how useful, can slow us down.

How to use "we half it,we square,we add it to both sides" when using the complete the square" This method can help make a complex Math problem a little bit easier.

Complex fractions are fractions that contain a fraction in the numerator,the denominator, or both. You can use the Keep,Change,Flip method in order to simply these complex fractions.

A very fast method to change the eye color within Adobe Photoshop. After you have done this one or two times it won't take you longer than 30 seconds.

There are many way to booby trap a bottle of diet cola, most of you already know the most common ones. Well here's another method of doing so, the result is the same. A BIG MESS!!! Watch the video tutorial for further instructions!

This method can be used on any kind of scroll saw pattern. Animals, people, inanimate objects, etc. Done on paper and scanned onto my computer only to clean them up and color them in to display. Three part series.

One of the biggest improvements in Mac OS X Yosemite came to the Spotlight search feature, allowing users to not only search through their applications, but also their emails, text messages, iCloud, and the web.

Welcome back, my novice hackers! Reconnaissance is one of the most important preparatory steps to hacking. As I have emphasized many times before here on Null Byte, you must know the operating system, the ports, the services, the applications, and sometimes even the language of the target to be effective. If you haven't taken the time to gather this info, then you are likely wasting your time.

Believe it or not, but people are actually texting less than they did before, and that's all thanks to Facebook Messenger, Snapchat, WhatsApp, and other split-second communication services. However, one communication method that is still going strong—and dominating—is email.

Security is a priority for many when they first set up their mobile devices. Nobody wants to have a stranger or nosey friend go through their phone and discover risqué photos or embarrassing text messages. These days, the closet is gone—everyone keeps their skeletons in their phones.

This video will show you how to set finger print scanner for phone unlocking in Samsung galaxy S5. The finger scanner option allows you to register your finger print for unlocking your phone. This method of unlocking your phone saves your time over typing password. This way no one can open your phone except you. Watch the video and employ the tricks in your Smartphone.

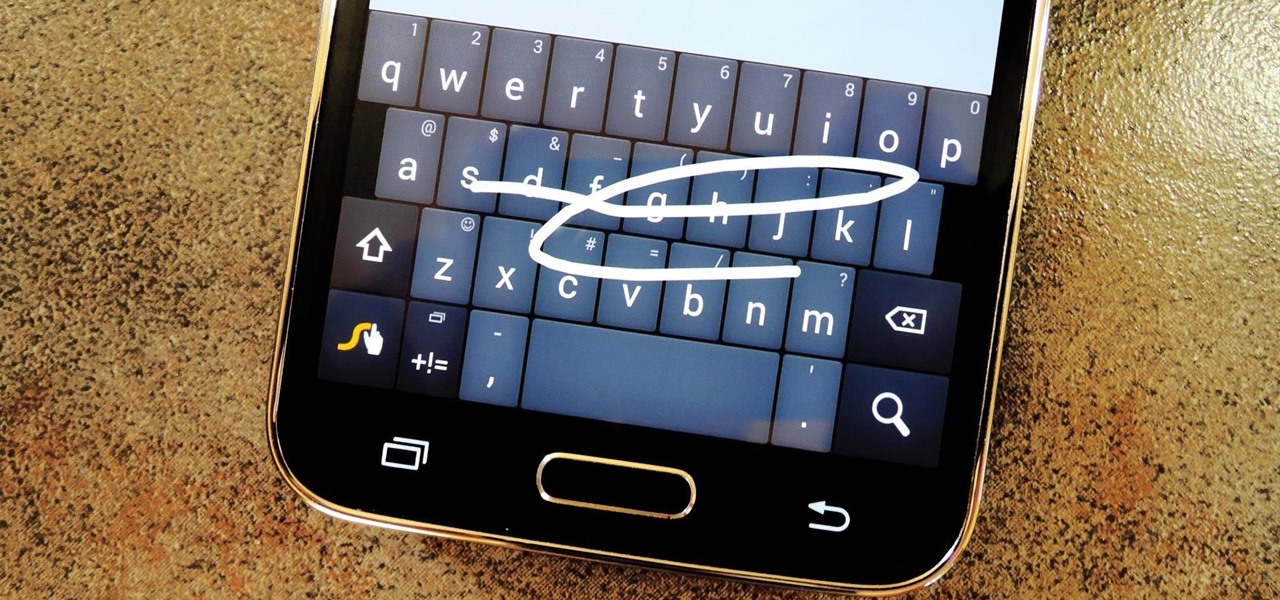
Most variants of the Galaxy S5 come with the gesture-based Swype keyboard preinstalled. If you're into gesture typing, you probably already switched to this input method from the default Samsung keyboard (whose gesture service is nice, but it's no Swype).

A simple method to test any alkaline battery in seconds! Works on AA, AAA, C, D batteries. You can separate good from bad.

As someone who's dependent on glasses to see on an everyday basis, losing or misplacing them is obviously a bad thing. I can't even see clearly enough to find the glasses that I just lost, so I'm pretty much blind now.

There is always an easier way to do something whether you want to clean, organize, freshen the smell, get water into a bucket that won't fit in your sink. The same principle applies when cooking. Sure you could cook food in an oven, microwave it, boil it, fry it, cook it with a solar cooker, but there is an easier and inexpensive method.

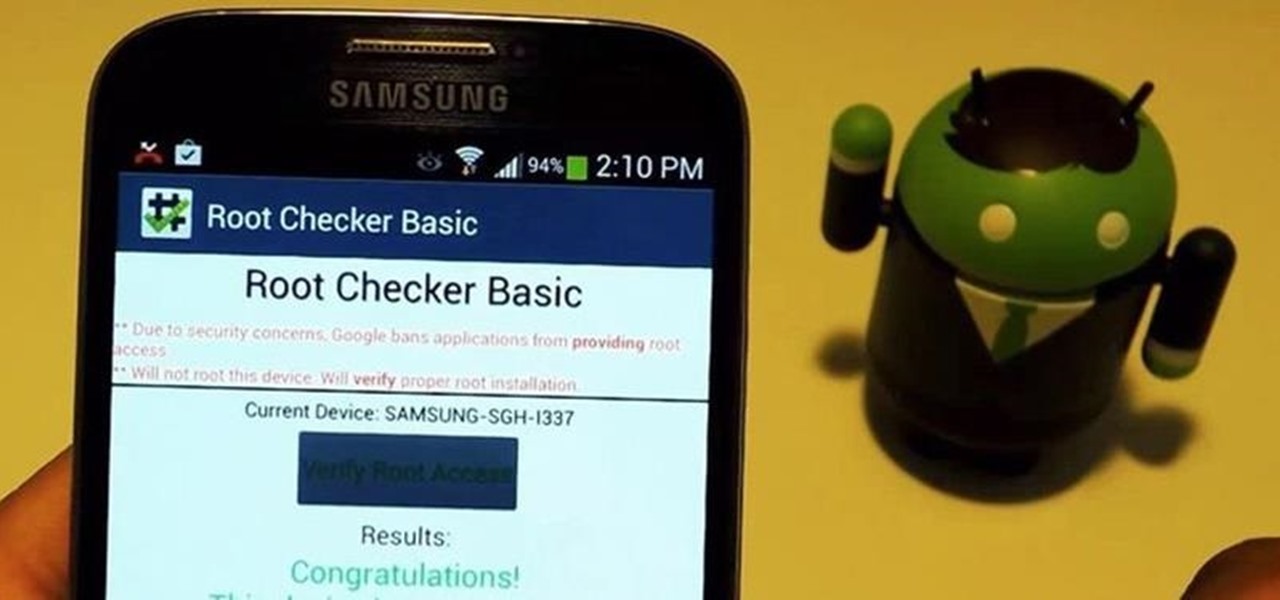
For new Android users, rooting an Android phone can often be an intimidating process, especially since there are so many different ways to gain root access, depending on your model and firmware version.

The design of iOS 7 has its lovers and haters, and if you're an Android user who just happens to love it, there are plenty of ways to make your device feel more Apple-y.

No matter what the clean freaks out there try to tell me, I still drink my Los Angeles tap water without a care in the world. I figure that I've already consumed much more heinous things in my lifetime. Street vendor "steak" burritos comes to mind.

Welcome back, my hacker novitiates! Finding vulnerabilities in systems can be one of the most time-consuming tasks for a hacker. There will be times, though, when you'll find yourself in a position that you know that a particular port represents a vulnerable application or service.

There are quite a few flaws with Apple's mobile products, and one that drives me crazy is their reliance upon iTunes for all your music syncing needs. If you want a song on your iPhone, you pretty much have to use iTunes to get it on there. Either that or buy it directly from the iTunes app on your device.

This video will show you an easy way to siphon the water off of your swimming pool cover with a garden hose.

The advantages of rooting are vast. From free wi-fi tethering, being on the latest and greatest software, theming all aspects of the OS, to ditching Touchwiz for a pure Google experience and much much more.

Prepaid phones are becoming more and more popular, and tons of people can see the benefits of switching now that some companies are offering prepaid services that are on par with the big players. For a lot of folks, the only thing keeping them from switching is the huge early termination fees that service providers charge to break a contract early.

When was the last time you bought a CD? Most of us listen to music through a number of digital channels—MP3s, Internet streaming services like Pandora and Spotify, and satellite radio, to name just a few.

Back in 2010, iOS developer Daniel Amitay developed a camera security app for iPhones that used an unlock screen almost identical to that of the iPhone.

Many marketers are NOT using this powerful strategy to get free traffic and increase their brand exposure. It's as simple as signing up for a free Gravatar account and commenting on blogs in a similar niche. See some good examples and some bad examples...

A few days ago, Russian hacker Alexy Borodin found a way to get free in-app purchases on an iPhone or iPad. In-app purchases include things like items and power-ups for iOS games, as well as subscriptions and "premium" memberships for certain apps.

In this quick tutorial I will be showing you how to install java in CentOS, this method will also work for other linux distros such as Ubuntu, Debian, and Linux Mint.

This kid has great instincts for teaching magic or card tricks as he instructs with multiple camera angles the best methods for shooting cards in the air. He also has different finger and grip techniques for multiple cards and different spins.