Use the Sew a Button presser foot to sew flat buttons on your garments or craft projects. It's easy, and fun once you've got the method down. The Singer sew a button presser foot comes both as a screw-on foot or a clip-on foot for the slant shank adapter. Great for those of us who always poke ourselves hand sewing buttons. Learn how to sew on a button with a Singer sewing machine by watching this video sewing tutorial.

Grilling corn on the cob is easy with this quick method from Chef Tips host Jason Hill. Before cooking corn on the grill, remove the husks and season with salt and pepper. This grilled corn on the cob is wrapped in foil for easy of preparation and heat retention while you prepare your other dishes. It's perfect for summertime barbecues and good times with friends. Learn how to prepare this grilled corn on the cob recipe by watching this video cooking tutorial.

Convert your bike to tubeless using the "ghetto" method. You will need a sealant, a tire, a rim, a metal tire lever, a knife or scissors to cut the tube, a tube a size smaller than your rim, an air compressor, and soap and water. You will need a sweet, doggy mascot as well.

With a few simple steps, you can change your motor oil yourself -- no need for an expensive mechanic to do it for you.
This is a tutorial that shows you how to view and control your computer screen from your iPhone/iPod Touch. But this method is for people who have a jailbroken iPhone/iPod Touch. This works on Edge and Wifi. If you are having problems connecting try going to control panel then security center then turn your firewall off. Also try turning off anything like virus protection.

Using Maya you'll learn to produce an alpha to use in Zbrush. Very easy method to make a controlled alpha without using Zdepth tools in Zbrush. In part two, Using Zbrush tools to make a tileable texture. Texture sculpting techniques and the 2.5d tools within Zbrush. Part three covers setting up the Maya render for the texture and attaching maps to the node.

Wrapping meat or fish in foil and then baking it is a whole lot like steaming vegetables: Both methods are healthy and help intensify the flavor of whatever's wrapped inside. This video presents a way to bake white fish along with delicious vegetables in foil.

One way for a middle-aged person to look better than ever is to sit on a patio surrounded by well-aged pots. Flaking, lichen-covered clay pots give the impression that they’ve been around a lot longer than you have. And because antiqued pots look expensive, everyone will think that your investments are doing well and your children have moved out. There are three methods of giving your pots the beauty of antiquity. Two of these techniques take minutes, and the other one takes months.

The camera shake method of filming is used in many popular TV shows including 'The Office,' 'Glee,' and 'Modern Family.' Typically the camera shake - or a wobbly, unstable frame - contributes a sense of urgency, unease, and interest to a shot, making it more dynamic and unpredictable. Quite like the plot of the shows mentioned above.

A killswitch is exactly what you think it is: A switch that kills an operation in an emergency situation when the operation can't be shut down in the usual manner. It shuts your operation no matter what the consequences.

In this video, Chad West shows you some more precise color correction methods and explains a little bit about the dodge, burn and sponge tools. Those of you who already know your way around Photoshop should probably not waste your time watching this video. It's meant for beginners.

Joe Bluhm goes over exaggeration and cartooning while sketching a digital caricature of Bill Murray. These principles will also apply to traditional drawing methods.

Are you serious about becoming a bonafide hacker? Then you simply must learn how to hack SSL passwords using ARP poisoning. ARP poisoning, also known as ARP spoofing, involves attacking an ethernet wireless network by looking at the data frames on a LAN (local area network). Resultingly, you can sniff plaintext passwords, SSL passwords, and even manufacture denial-of-service attacks.

This shows you how to create a custom character in Mugen (the custom PC game engine), it shows you how to make one with a hand drawn character, but the same method applies for using ripped sprites. You'll also see how to animate your character. Programs used are MSPaint and Fighter Factory.

Don't be too disappointed if you don't have the spiffy new Kindle Touch, there is an up side. The benefit to owning the older (duller) models is that the firmware remains the same throughought generations, so the hacks retain their usefulness. This has given the modding community for Kindle a bunch of time to flourish, with tons of great code, hacks and homebrew. Today's Null Byte is going to show you how you can root, and then remove the crappy original screensavers that come installed on th...

Has you rent check bounced again for no apparent reason? It happens to everyone, but if you're roommate needs the money fast, you need to fix it fast, and wire transfers are the fastest way to give money to someone else. Executing a wire transfer is as easy as making one phone call.

If you have just purchased a new Ford Taurus, you may have noticed the new SYNC feature. SYNC is a GPS built right into your dashboard. If this is your first time using a global positioning system, you may need a few pointers. Check out this video and learn how to access step by step directions and get where you need to go.

Need to know what kind of oil your car needs? How about your vehicle load capacity? What about the standard maintenance procedures for you specific make and model? All of this and more can be located inside your owner's manual. If you don’t have an owner’s manual for your used car, you may still be able to find one even if your car is an antique.

If you're a Firefox user and frequently use free image hosting services à la ImageShack & Photobucket, then you've no reason not to check out the ImageBot Firefox extension, which does quite a lot to streamline the picture uploading process.

This video tutorial is all about recovering the deleted files in Windows Vista. If you are using the Windows Vista and you have unknowingly deleted a file and emptied the recycle bin, then you can recover it. This can be done by using the Shadow Explorer. Shadow Explorer is a Vista program that accesses the Vista Volume Shadow Copy Service. In Vista, the shadow copy service is turned on by default. It creates backups of files on a regular basis. Shadow Explorer provides access to these backup...

Many streaming services offer user profiles for different people in your household, some of which also include profile images. In most cases, you can set a custom profile image to better differentiate and personalize your account from the others, and HBO Max lets you do the same, albeit, with limited options.

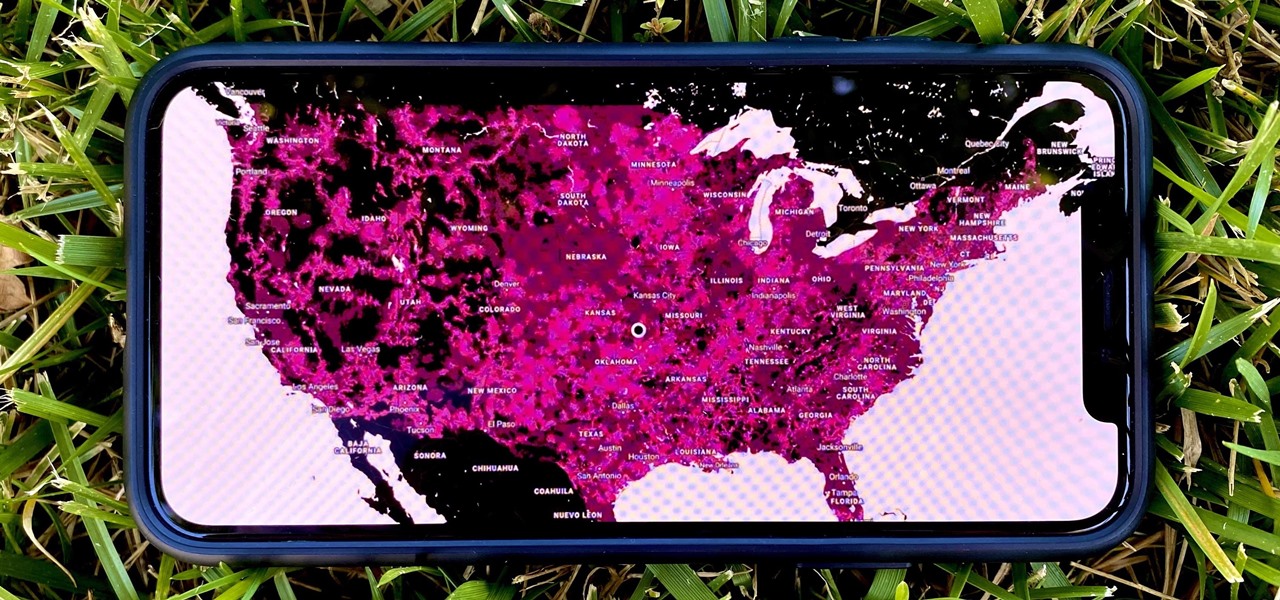
In 2009, 4G LTE networks rolled out in Stockholm and Oslo, replacing 3G as a better upgrade to the mobile data technology that gives us the broadband speeds we have on our mobile devices. Over a decade later, and we have the latest, next-generation wireless network technology among us, 5G, but can you even use it?

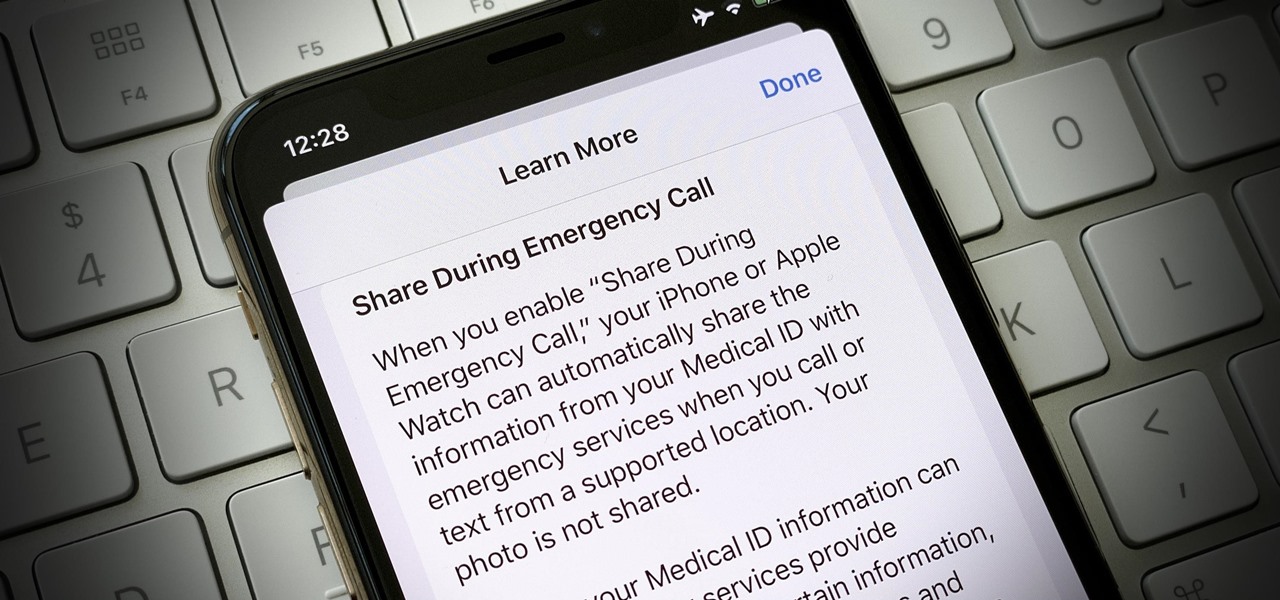
In the event of an emergency where you can't answer for yourself, trained professionals can view your Medical ID on your iPhone to learn about your medical situation, granted that you have created one. But that's not all your Medical ID can do. With a new feature, iOS can share your Medical ID data automatically with first responders when you place an emergency call.

Web application firewalls are one of the strongest defenses a web app has, but they can be vulnerable if the firewall version used is known to an attacker. Understanding which firewall a target is using can be the first step to a hacker discovering how to get past it — and what defenses are in place on a target. And the tools Wafw00f and Nmap make fingerprinting firewalls easy.

You may not have thought of dorks as powerful, but with the right dorks, you can hack devices just by Googling the password to log in. Because Google is fantastic at indexing everything connected to the internet, it's possible to find files that are exposed accidentally and contain critical information for anyone to see.

Reconnaissance is one of the most important and often the most time consuming, part of planning an attack against a target.

London-based developer Andrew Hart has been working on AR navigation since Apple's original ARKit tool was still in beta preview. Now, he's ready to unleash his technology on the world.

After reviewing the international plans for major US wireless carriers, it became obvious they're all pretty bad. Your data is heavily restricted, requiring a daily fee which can cost an extra $100+ on a seven-day vacation. That's when I learned about Google Fi, and how for most travelers, it's the best option.

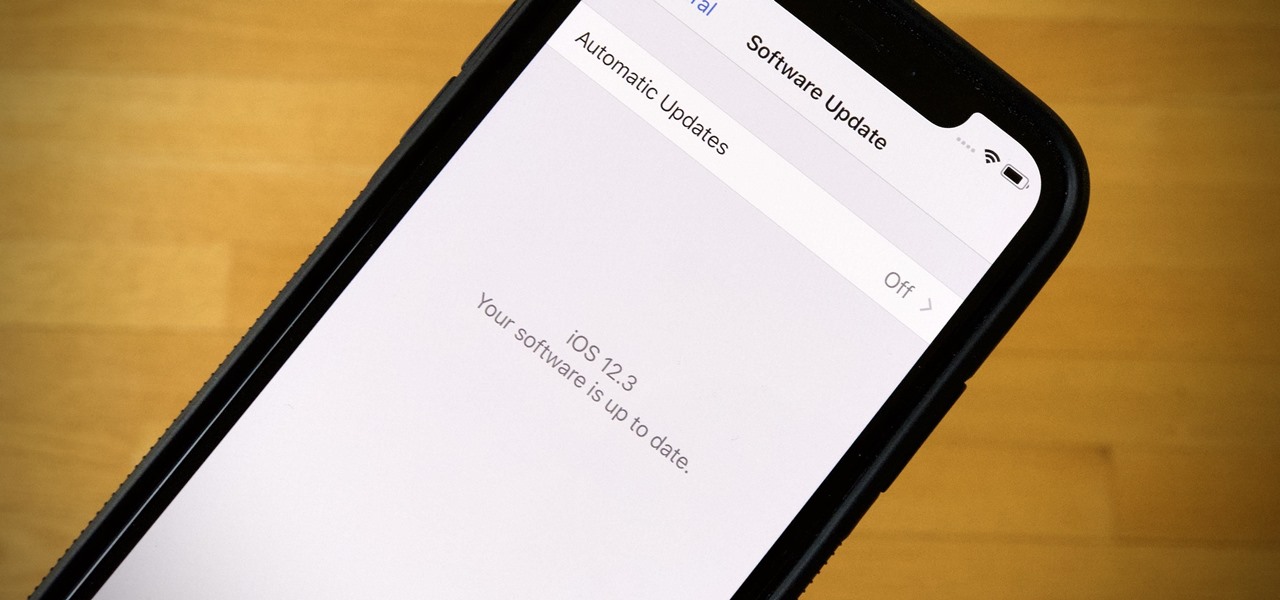
If you're a public beta tester, your Thursday just got awesome. Apple just released the first public beta for iOS 12.3 today, March 28. This update comes right on the heels of the first developer beta for 12.3, which itself released just one day ago. Thanks to that release, we know that this update contains a new TV app with updated layouts, Apple TV Channels subscriptions, a new logo, and more.

It's an exciting time to be an Apple fan. Monday saw not only a major announcement of new Apple services and subscriptions but also the official release of iOS 12.2. If you're a beta tester, you probably watched 12.2's evolution over the last two months. Well, get ready to do it all over again — Apple just released the first developer beta for iOS 12.3 today, Wednesday, March 27.

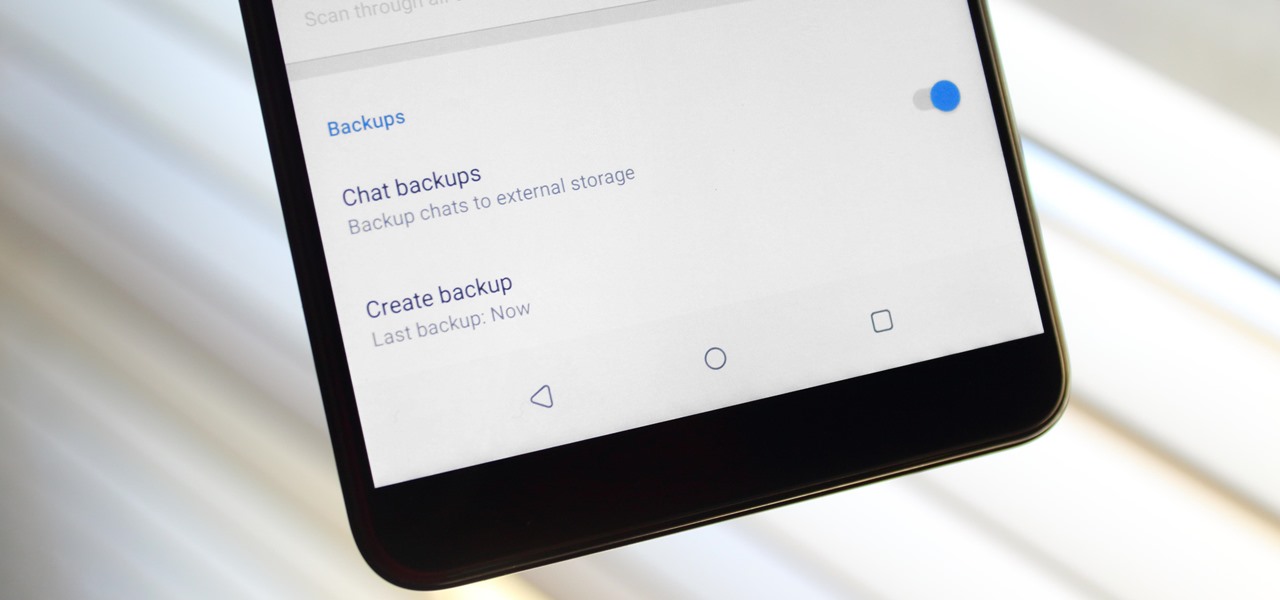
Switching phones has never been easier. Google backs up most of your app data on the cloud, which can then be restored onto your new phone. Sadly, Signal doesn't use this feature since it could compromise your security. Instead, Signal stores encrypted backups locally, requiring a bit of work to restore these messages.

Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

With new iPhone models out, you'll have updated cameras to try out, a faster processor, and new colors to choose from. The only thing that could stop you from picking one up yourself is, well, your current iPhone. Here's how to check if you're eligible to upgrade to iPhone 11, iPhone 11 Pro, iPhone 11 Pro Max, or any other iPhone still being sold.

Like an overbearing mother, Apple will constantly nag you through annoying red bubble alerts about iOS updates that are ready to install. Fortunately, you don't have to take this issue lying down, as there are ways to prevent your iPhone from receiving OTA updates and their corresponding prompts, regardless of whether your device is jailbroken or not.

The gig economy is thriving, and if you aren't already making money with your phone, you could be missing out on easy residual income. Some people just want extra cash, and some even manage to completely ditch the 9–5, enabling them to work at their own pace and set their own hours.

Since early March, iOS users have been able to enjoy the most popular video game sweeping the rounds. Android users have been left envious as they wait for a "few months," the only vague release date given by Epic Games. In the meantime, there are a few ways we can still satisfy our urge to play.

Magic Leap's recent flurry of patent applications prompted us to look around for any trademark movements from the company, and it turns out that the Florida-based company has been quite busy.

As the third-largest smartphone manufacturer in the world, Apple devices are a constant target for hackers everywhere. While iOS has seen fewer common vulnerabilities and exploits (CVEs) in recent years, iPhones still aren't hack-proof. Fortunately, you can strengthen your security with the help of a few apps.

While flying can be a frustrating and sometimes nerve-racking experience, Airbus is banking on augmented reality features in its new iflyA380 app for iPhones and iPads to help passengers learn to love the ordeal.

Threats to your privacy and security are everywhere, so protecting your data should be the highest priority for anyone with a smartphone. However, one threat many people overlook is the company who supplies the operating system your Android phone runs — Google.