While there are a variety of privacy-focused search engines available like StartPage and DuckDuckGo, nothing can offer the complete trust offered by creating one's own search engine. For complete trust and security, Searx can be used as free metasearch engine which can be hosted locally and index results from over 70 different search engines.
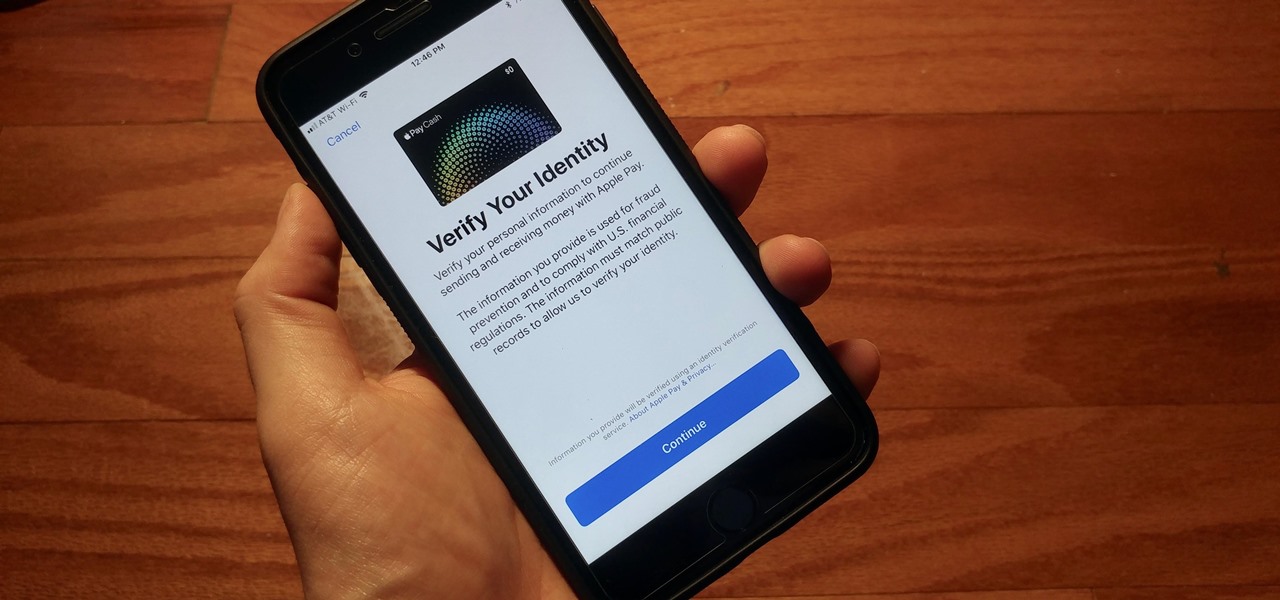
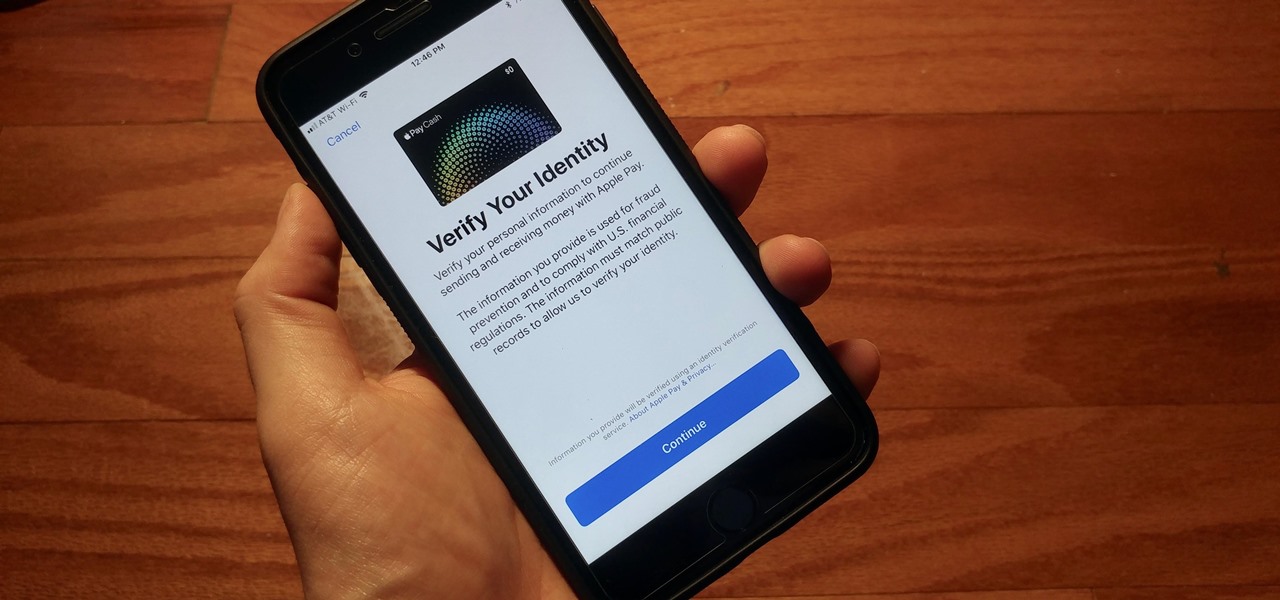
With iOS 11.2's introduction of Apple Pay Cash, you can send and receive money to others directly through iMessage, using the convenience and security Apple Pay is known for. However, if you want to make sure your efforts go uninterrupted, you'll want to make sure you verify your identity with Apple.

After laying off 40% of its staff this month to cut costs, SoundCloud appears to be struggling to stay afloat. While blog posts from the company have assured fans that the music platform is not in danger of shutting down, some people aren't so sure this is the truth. Internet Archive — a non-profit dedicated to preserving websites and services — announced today that they will be conducting a partial backup of SoundCloud to safeguard the site's content in case of closure.

A spokesperson from the Nissan and Renault Alliance told Driverless the group is testing self-driving electric "robo-vehicles" for future mobility services and is "not ruling out anything" for future services the group might offer, as the alliance widens its driverless business model to include both fleets and private sales.

The common thread between this week's Brief Reality stories is that augmented reality is beginning to prove its worth as a technology that improves workflows and processes. From customer service to healthcare to manufacturing, augmented reality is helping companies improve productivity.
Over the past week, we are seeing more companies capitalizing on services leveraging augmented reality. One company secured funding to expand their service, while two other companies grow its own services through acquisition.

Apple is planning to completely overhaul its Apple Music streaming service this summer, and is expected to unveil the changes at its Worldwide Developers Conference in June, according to reports from Bloomberg and 9to5Mac.

The highly anticipated VR headset hasn't been on the market long, but there's an issue that has some consumers, and even government officials, concerned about the Oculus Rift. You probably guessed the issue surrounds privacy and the extensive, not-so-secret way that it's collecting your personal data. The privacy concerns came about as various customers and media outlets took notice of the rather lengthy Terms and Services that pop up once you strap yourself into the Rift headset.

Microsoft decided to give users a free upgrade to Windows 10 if they were previously running Windows 7 or 8—but it came with a catch. Their main motivation for knocking off over $100 from the normal going rate was to get more people using new Microsoft services like Cortana and the Windows Store. To bolster these services, Microsoft implemented a host of new tracking "features" in Windows 10.

T-Mobile's credit-checking system was recently hacked, and this one is about as bad as it gets. The names of 15 million customers, their date of birth and social security number, as well as driver's license numbers and additional information was illegally accessed, meaning the potential for identity theft here is huge.

Imagine this scenario: You exploited a system using metasploit and you want to install a backdoor. You have a few options;

When Google Play Music launched a few years ago, I ditched iTunes and began using the service as my one and only source for listening to my personal music library. While All Access is great, I still prefer the radio feature on Spotify, so I still use that to discover new music.

In direct competition with Pandora, iTunes Radio, and Spotify, Samsung has just launched Milk Music—a strangely named, yet completely free music streaming service for Android.

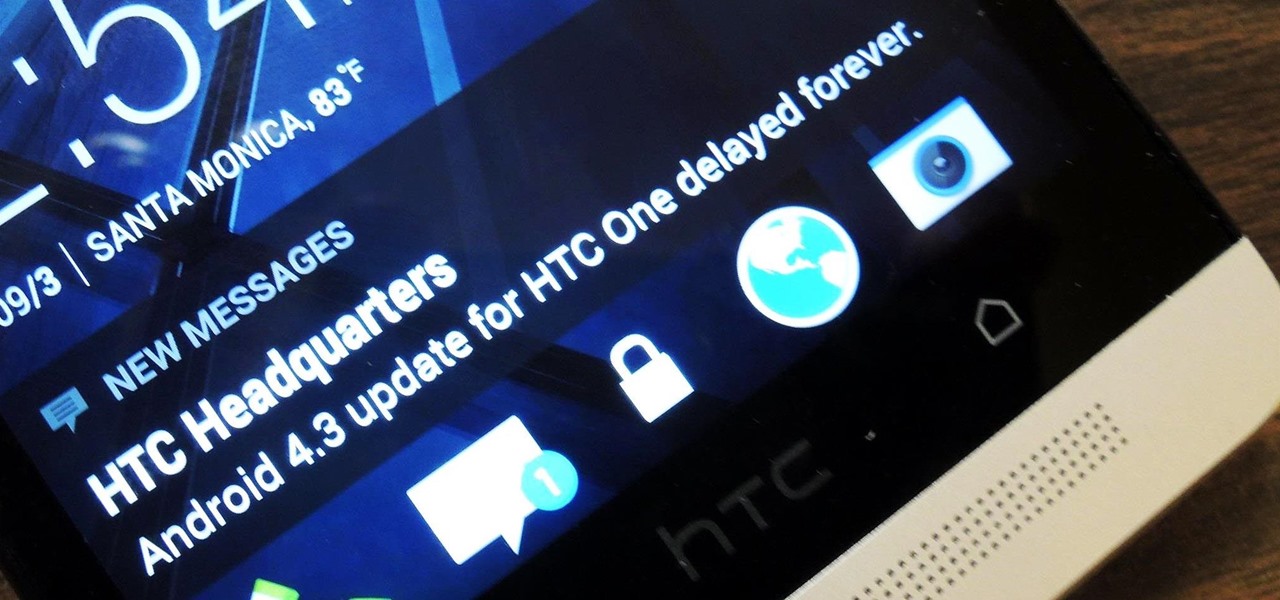
If you're new to Android phones, one of the first things you've probably noticed is how notification alerts differs from Apple devices, especially in regards to getting a text message.

Shave precious seconds off your running time and you just might win your next 5K. You Will Need

If you want to increase your privacy and prevent iPhone apps from gaining access to data containing your location, take a look at this tutorial on turning off the location services in the settings menu on Apple's iPhone 3G devices and above.

In this how-to from Household Hacker, we learn of a number of free proxy services that make getting around your school's Internet filter software a breeze. For all of the details, and to start accessing and using all of your favorite websites when at school, watch this video guide.

Not stretching after a good run will definitively set you up for injury or muscular pain. While stretching before a workout lubricates your joints to prepare them for work, stretching afterwards helps prevent you from building too much bulk so you get long, lean muscles, and so your tensed up muscles can relax again.

You keep all kinds of important and sensitive information and data on your computer, and if your hard drives crashes, you're done for… unless you've backed it up. CNET has some "Insider Secrets" on how you can backup your system with an external hard drive, network-attached storage, and online services.

Google Voice is the newest release from the experts at Google. Google Voice is a low-cost Internet phone service that redirects calls to your home phone and works over your WiFi connection. This service is very exciting and useful for those that are looking to save some money on long distance. Google Voice was in limited use for a while and is now available to everyone, so check out this clip and learn how to use it!

This video demonstrates how to fix the batter length problem on a jailbroken iPod. First, make sure that you have a Wi-Fi connection so you could download the necessary files. Turn your iPod Touch on and locate the Installer icon. Wait until the installer program loads. Then, on the bottom portion of the screen, select the icon Install. In the Packages section, scroll all the way down to letter S and look for Services. Select it and install it. After the installation completes, go back to hom...

Whether you're a World War 2 veteran (thank you), the next-of-kin of a vet, or a member of the general public, there are lots of reasons you could want to look at service records for WW2 vets. Watch this video for tips on acquiring these service records from the US government.

In this automotive maintenance tutorial you will learn how to service the brakes on a Volkswagen Fox. Servicing the brakes involves changing the brake pads and checking the fluid. If your Volkswagen Fox isn't stopping as well as it should, watch this video and learn how to service your front brakes.

With the spread of smartphones and free online games, the "Freemium" model of product distribution and monetization has become prevalent over the last several years. At it's essence, it is handing out software products for free and then allowing customers to pay for in-software services using microtransactions. This video features some businessmen who do business in iPhone apps discussing how they use "Freemium" systems in their apps to make the most money possible while providing great servi...

In a bad economic environment, providing a great customer service experience is even more important than normal. Word of that great experience will spread via Twitter and Youtube, helping your business attract buzz without requiring it to spend cash on marketing. This video features a business technology expert explaining how to create a "wow" experience for your customers and use the ability to do so to improve your business.

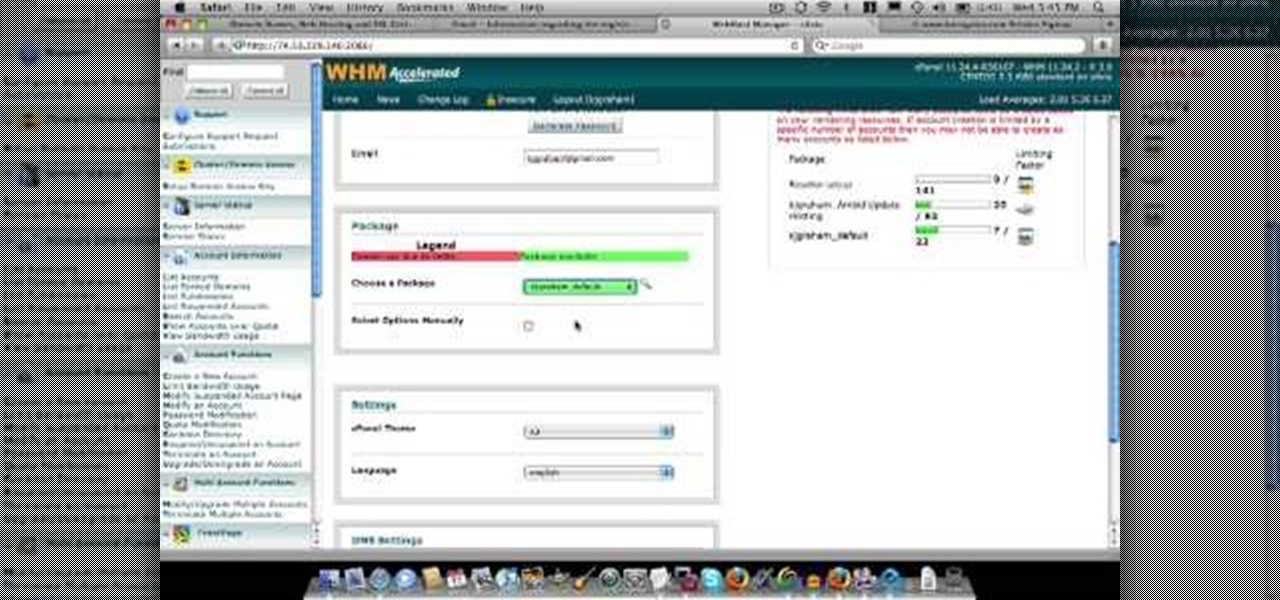
In this video about choosing a web hosting company. The narrator begins by saying that web pages are hosted on servers; the files that make up a web site are hosted or stored on a server. The narrator recommends a service called Host Gator. He indicated they are reliable and provide reasonably priced web hosting services. He briefly discusses the process they charge for their different levels of hosting services. Next he shows the steps to hook your domain name to the host account. He demonst...

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

To share a song or album to family and friends, it's as easy as copying its link in the app and pasting that into a message. However, not everyone uses the same music streaming service, so a link to an Apple Music song won't do a Spotify, Tidal, Pandora, Deezer, or YouTube Music subscriber any good. If you're on an iPhone, though, there's an easy way to convert links from one service to another.

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.

If you have friends who aren't privacy-conscious, you've surely heard the old "What do I have to hide?" excuse. Despite the fact that billions of people are using the internet each day, many of them don't know the dangers that can find them. And many don't know the tools to combat them.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

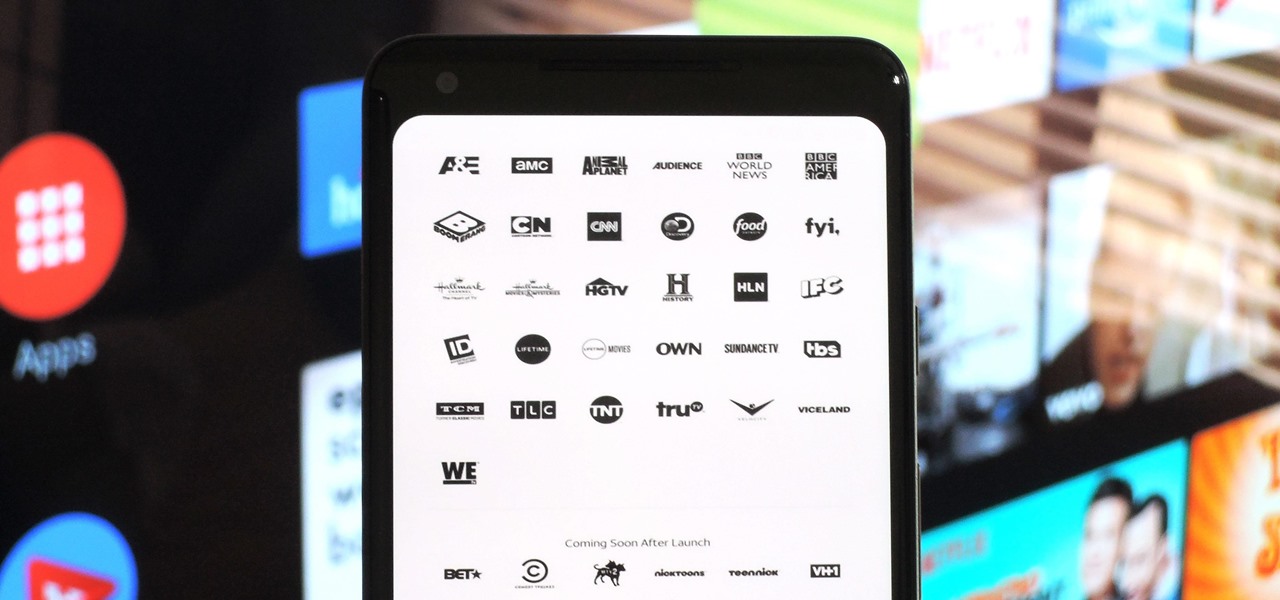
With YouTube TV and DirecTV Now starting at $40/month, and others like Sling TV offering an eye-catching $25/month plan, streaming cable services may sound like a great way to cut costs while cutting the cord. But when you look at all the factors, the price you pay may very well end up being just as high as your traditional cable bill — if not more.

Most companies have services like employee login portals, internal-only subdomains, and test servers they would prefer to keep private. Red teams and white hat hackers can find these obscure and often vulnerable services using a tool designed to help protect users from fraudulent certificates.

After a district judge approved the $85 billion merger between AT&T and Time Warner, we knew AT&T would be quick to reap the rewards of capturing Time Warner's media properties. Today, we get our first look at this with two cellular plans from AT&T. What makes these plans unique is they include a new cord-cutting service called WatchTV.

Local port forwarding is good when you want to use SSH to pivot into a non-routable network. But if you want to access services on a network when you can't configure port-forwarding on a router and don't have VPN access to the network, remote port forwarding is the way to go.

The world is full of vulnerable computers. As you learn how to interact with them, it will be both tempting and necessary to test out these newfound skills on a real target. To help you get to that goal, we have a deliberately vulnerable Raspberry Pi image designed for practicing and taking your hacking skills to the next level.

With the exception of New York, D.C., and maybe San Francisco, public transportation in the United States is downright abysmal. Like it or not, you need a car to get around. This is why Uber and Lyft have seen so much success in recent years. Both ride-sharing services get you from point A to point B in an efficient manner, and they do it without costing an arm and a leg. Well, in most cases.

Welcome back, my rookie hackers! The Golden Fleece of hackers is to develop a zero-day exploit, an exploit that has not been seen by antivirus (AV) software or and intrusion detection system (IDS). A zero-day exploit is capable of skating right past these defenses as they do not contain a signature or another way of detecting them.

If you've been around computers long enough, you've probably heard the phrase "have you tried turning it off and on again?" This trick usually works because it forces your computer to empty out the contents of its RAM and disk caches when you restart.

With new messaging services being pushed out constantly, it can be a pain trying to keep track of them all on your Android device. We had previously shown how to stay on top of them all with a unified "inbox" app, but that still requires you to have each individual app installed. While looking for a true one-stop messenger, I came across Disa.