So you want to create a meterpreter virus, but you keep getting caught by AV. How do you create one that will go undetected? In this tutorial, I'll teach you how to code your own simple virus that will download a powershell payload from an apache webserver and execute it - bypassing antivirus.
This video will show you how to make Ramen noodles in your Keurig Coffee brewer, and the correct setting to use.
Greetings null-bytians. Firstly, I would like to apologize for the no images thing. I guess I can't upload them.
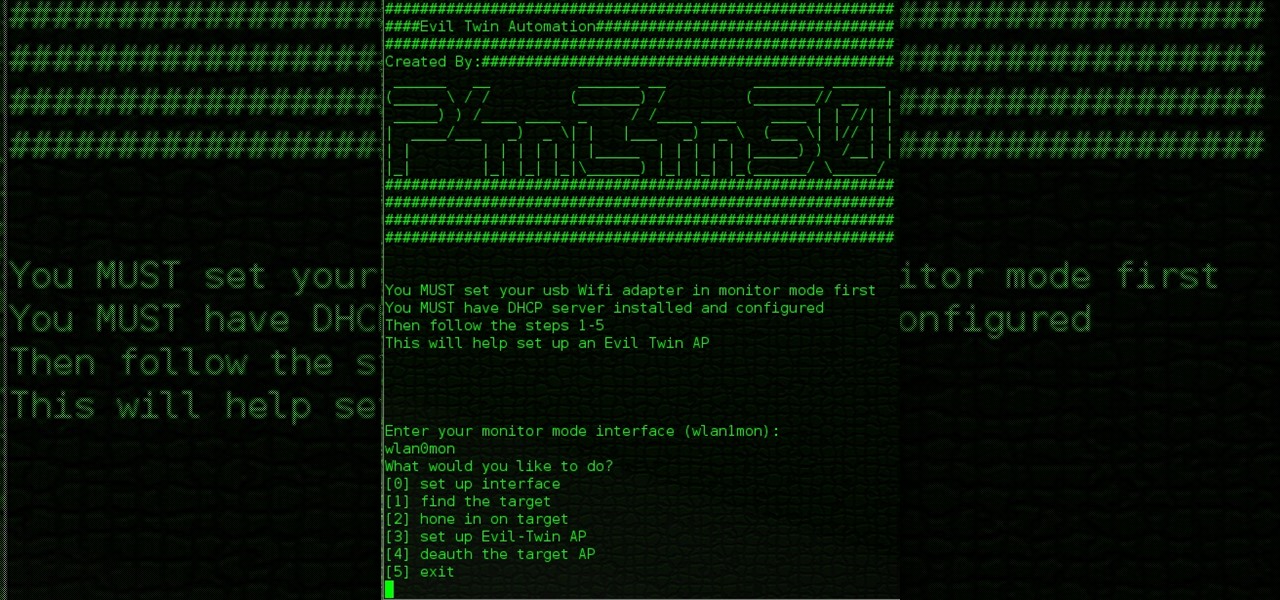
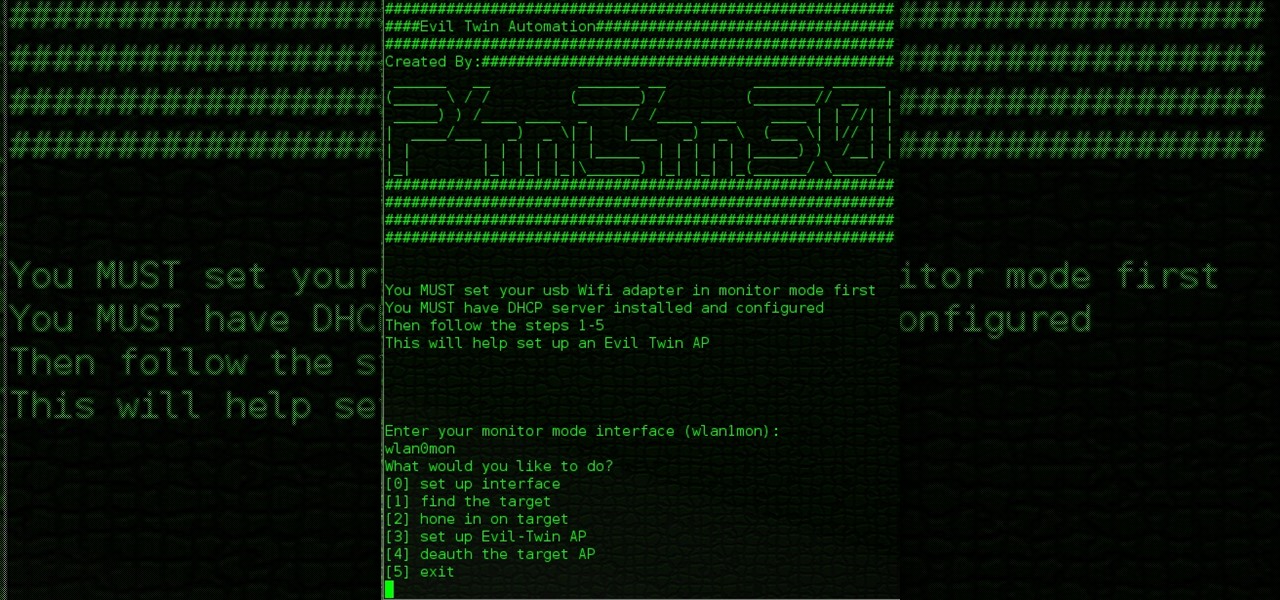
Hello All, So to recap in part 1 I went through setting up the dchp server. Part 2 detailed the bash script. Now in part 3 I will post the entire bash script. I am doing this in its own post because Part 2 is just way to much info on one post IMO.

Hello again, ***UPDATE: Adding links to the other Two articles****

When attempting to compromise a target, we want as much control as possible over the victim. Metasploit's meterpreter allows us to have immense control over the victim, the only issue is that sometimes we can't land a meterpreter. We may only be able to land a standard shell, but fear not, there is a way to upgrade our shell into the all powerful meterpreter!

In part one of this tutorial we found out that your English teacher is a paedophile, by using a Man in the Middle attack to intercept his internet traffic.

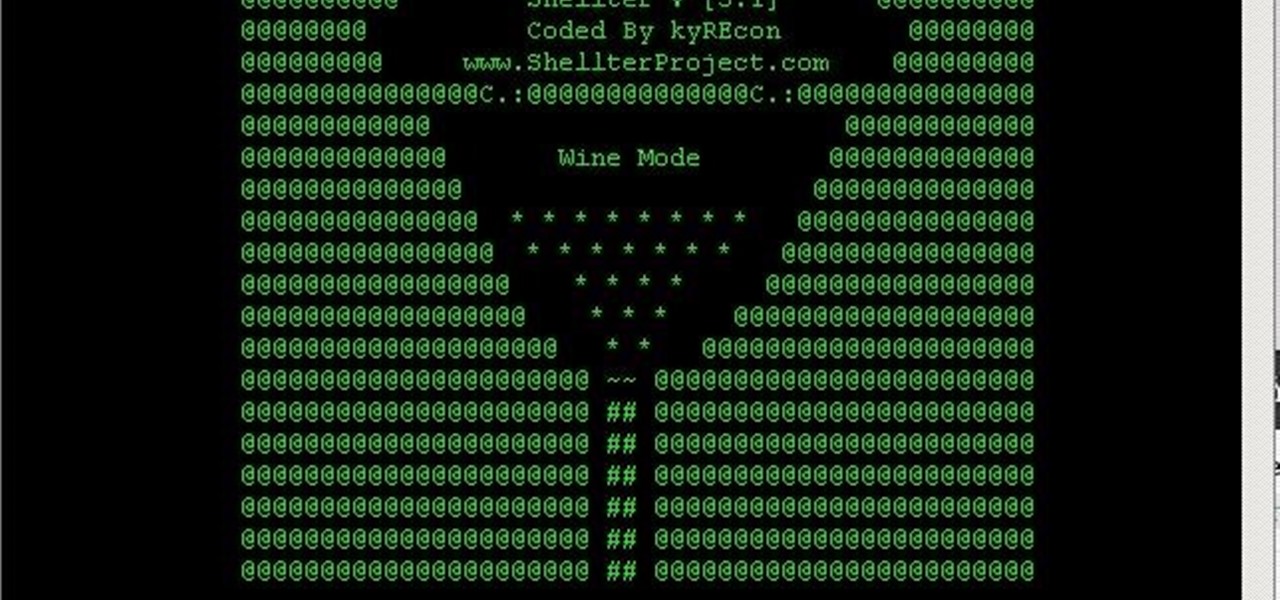
You always wanted to make an undetected payload and make it look legit, Well this is what this tutorial is about, You're going to learn how to backdoor any (Unfortunately only 32-Bit) software, Let's get into it

G'day, Knuckleheads, and welcome to Episode 22 of my Owner Builder Series. In this video we look at cutting and setting up Verandah / Decking Posts. It's really important that you get thuds right as nothing looks worse than badly set up posts. Check it out and let me know what you think!

When I tried to set up an eviltwin for a MitM-constelation in kali 2.0, I couldn't provide internet to the victim. The origin was the brctl bridging. I have read many tutorials but all of them where explained in backtrack and older versions of kali. So i was searching for a solution without using brctl and this solution will be explained now. This will just work on unencrypted wireless-environments.

Welcome back, my tenderfoot hackers! In this series, we are exploring the myriad of ways to hack web applications. As you know, web applications are those apps that run the websites of everything from your next door neighbor, to the all-powerful financial institutions that run the world. Each of these applications is vulnerable to attack, but not all in the same way.

Out of the box, Windows 10 allows you to search the web right from the taskbar. However, the search engine is set to Bing, and there is no option to change it like you can in the Edge browser.

Do you remember my last article on how to hook any web browser with MITMf and BeEF? Well, we are using the tool once again, but this time for auto-backdooring....

As you might know, there are a multitude of tools used to discover internal IP addresses. Many of these tools use ARP, address resolution protocol, in order to find live internal hosts. If we could write a script using this protocol, we would be able to scan for hosts on a given network. This is where scapy and python come in, scapy has modules we can import into python, enabling us to construct some tools of our own, which is exactly what we'll be doing here.

bObsweep robotic vacuums automatically clean whenever instructed to do so by an owner or because of a pre-programmed schedule.

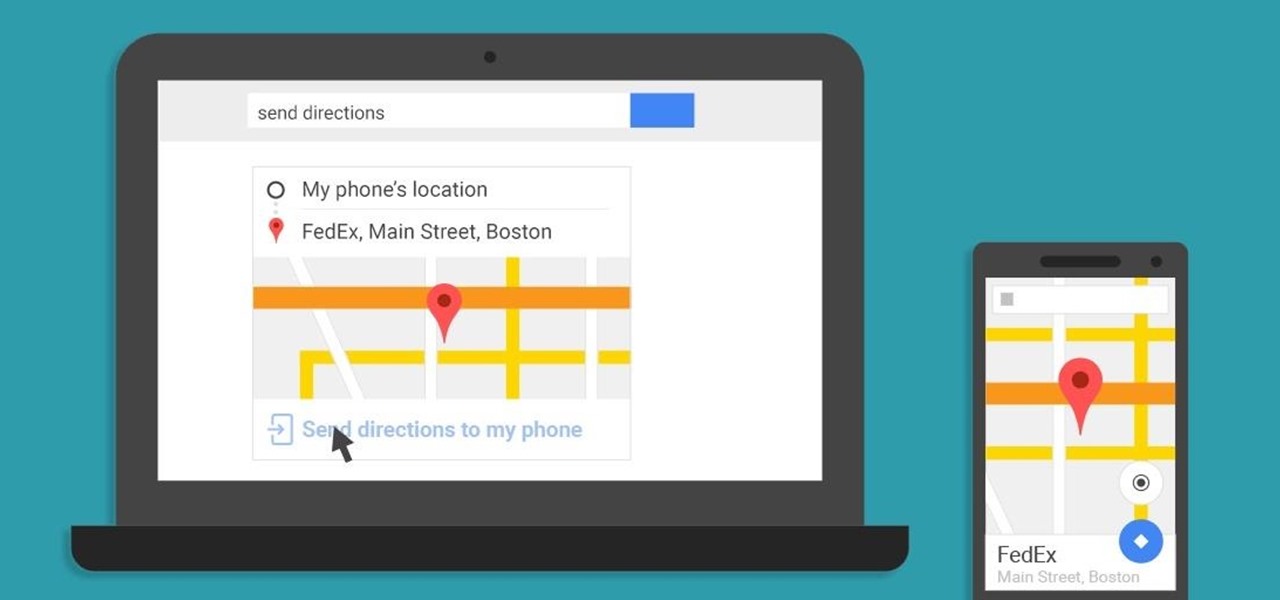
A set of cool new Android-related Google Search functions made their debut this week, which will allow you to locate your phone, send directions to your mobile device, set alarms and reminders, and send notes from any web browser.

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

Android's auto brightness feature was recently updated, and as of version 5.0, a new "Adaptive brightness" feature was added. This allows users to set a preferred overall brightness level, but still have the ambient light sensor adjust the backlight accordingly.

Using a timer to take a photo is great if you're looking for a quick workout. You have to prop up your phone, frame your shot, set the timer, and sprint to get into the frame. Then when you realize your position was a little bit off, you have to reset the timer and jump back in—over and over again until you get the photograph right.

These days, we truly have a world of knowledge at our fingertips. Trouble is, a large portion of that information is not something you'd want your five-year-old learning about quite yet.

We all fall sleep in different ways. Some may require absolute silence, others need white noise, and some enjoy listening to a song or two to help bring on the sleep. If you're in the latter group, like I am, there's a problem. Fall asleep before the music stops, and a loud song may jolt you awake in the middle of the night. With an iPhone, however, that issue can be avoided with a little setup.

Hello Hackers! Welcome to my 2nd Post: This is a tutorial explaining how to hack android phones with Kali.

I've been lucky enough to never be a victim of street crime, but I have read and seen too many articles and videos to completely rule it out as a possibility. You can do some things to prevent it, but if your life suddenly turns into a scene from Friday the 13th, you'll want to be prepared with some sort of way to let others know you need help. This is where Shake2Safety comes in, a free Android app from Phontonapps.

Could possibly be the most evil prank you can pull off. Use the noise maker found in a party popper to set up this evil prank that will just about scare the living $#?# out of anyone that puts it on.

The worst thing to clean up is a broken egg on the floor, it's not only smelly but gooey too. Here's a really fun booby trap you can pull off at home using an egg, it will require the use of 2 magnets and a paper cup like the ones you get a your local fast food joint.

This video will show you how to set up a connection with wifi network in your Samsung Galaxy S5. So please watch the video and follow all the steps carefully. Employ the technique in your Samsung Galaxy S5 phone and enjoy a wifi environment.

Welcome back, my nascent hackers! We have spent a lot of time in previous tutorials focused on hacking the ubiquitous Windows systems, but the vast majority of "heavy iron" around the world are Linux or Unix systems. Linux and Unix dominate the world of Internet web servers with over 60% of the market. In addition, Linux and Unix servers are the operating system of choice for major international corporations (including almost all the major banks) throughout the world.

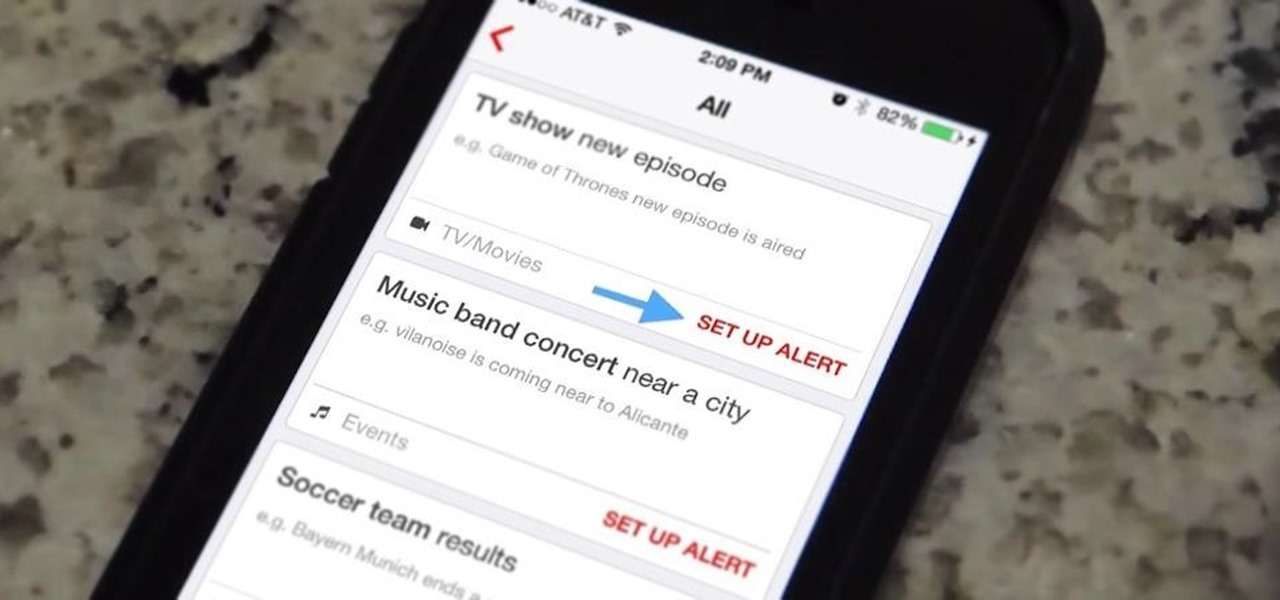
While it's not too hard to remember to watch your favorite TV show every week, it's almost impossible to remember to watch all of your favorite shows. Add on to that sports games, live music events, and new film releases and you'll find yourself in a disorganized mess with a lot of missing out.

Welcome back, my greenhorn hackers! In previous Wi-Fi hacking tutorials, I have shown you ways to create an Evil Twin, to DoS a wireless AP, and to crack WEP and WPA2 passwords, but in this tutorial, I will show you something a little bit different.

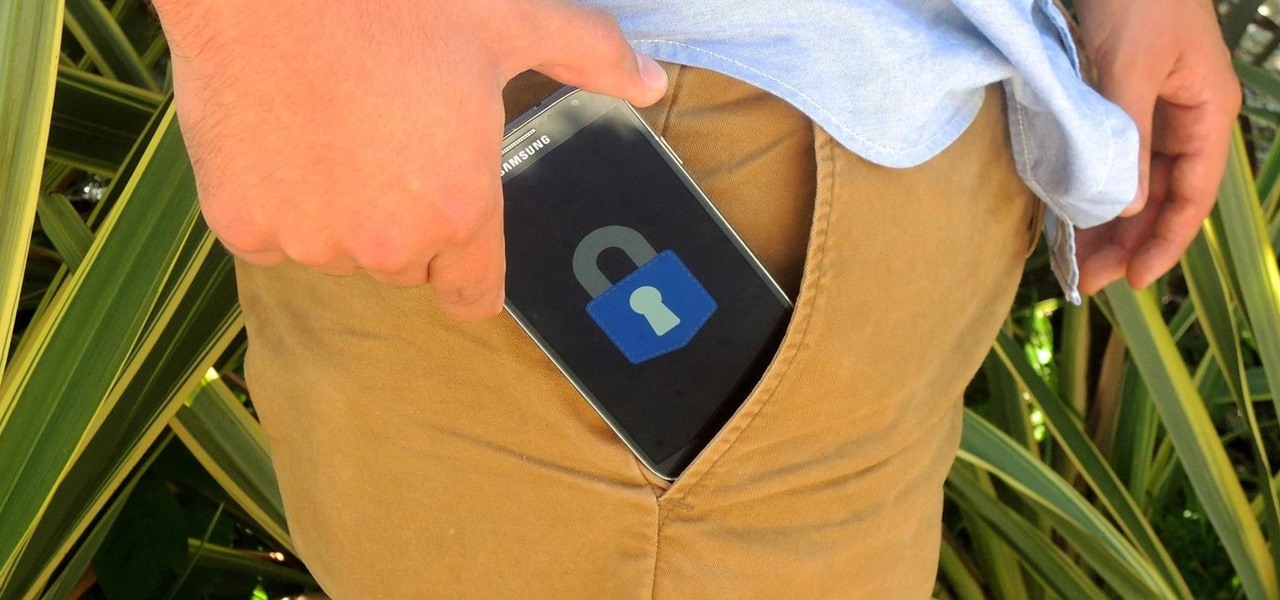
There are those who hold their phone or set it down when they're not using it, and others, like myself, who pocket it. If you're like me and are rocking the pants pocket fade, then you'll love the new Android app I found.

Among the additions that Apple's included in iOS 8 for iPhones are a couple of new features to the Camera app, including a timer and manual control of the exposure setting. Hit up the video to see how these new features work, of scroll down for the written walkthrough.

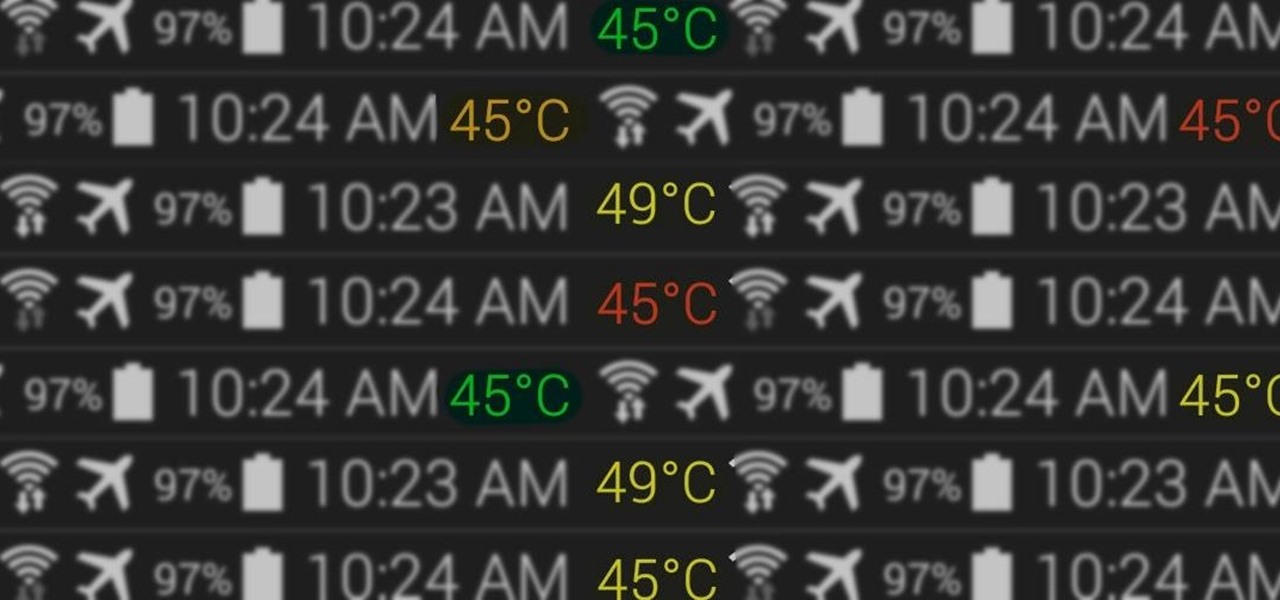
At the core of your Galaxy S5's hardware lies the central processing unit, or CPU for short. Practically every piece of data, every binary bit, has to pass through your CPU before it can be used to display a video or execute a game command.

Samsung's Galaxy devices, for all the grief they get about supposed "bloatware", offer quite a few functional features that are not included in stock Android. From "Air Gestures" to a handy "Smart Alert" notification reminder, many of these features are more than just the latest gimmick to pitch in their ads.

You hand your iPhone to a friend to show them a picture. What happens? They swipe. Left, right, it doesn't matter. You don't remember what lies in either direction of the photo in question, and you don't want anything compromising exposed to the unassuming viewer. Luckily, Apple includes a safety net in iOS to prevent this scenario from ever happening, so long as you set it up ahead of time.

This video will show you how to set finger print scanner for phone unlocking in Samsung galaxy S5. The finger scanner option allows you to register your finger print for unlocking your phone. This method of unlocking your phone saves your time over typing password. This way no one can open your phone except you. Watch the video and employ the tricks in your Smartphone.

Whether it's your dad or your older brother you want to prank, There's no going wrong with prank. It's full proof and will never fail.

As long as your friend's cup is made of styrofoam or paper then you should have an easy time pulling off this practical joke.

Everyone uses the bathroom at least once or twice a day, which is why its the perfect place to set up some booby traps as practical jokes for april fools day or any other day for that matter.

As the title says, you'll learn how to set up a prank that will end up with your victims having eggs on their faces.