
How To: Apply iron-on transfers to T-shirts
Want to design your own custom t-shirt? Get tips for sewing and applying designs to your T-shirts in this free video clip from a professional fashion designer.


Want to design your own custom t-shirt? Get tips for sewing and applying designs to your T-shirts in this free video clip from a professional fashion designer.

Looking for a unique t-shirt? Well, make one yourself! Learn how to sew patches, paint, and design a custom t-shirt in this free video series.

Learn how to pick the right fabric, how to build, how to sew and how to hang the perfect wall hanging in this free video series.

If you're drawstring fell out, it may seem like the end of the world, but take a deep breath -- it's possible to put back in!

In this tutorial, we learn how to make cotton candy with a cotton candy machine. First, you will want to take your choice of flavored sugar and pour it into the top of the cotton candy machine. Next, you will take your paper cone for cotton candy and place it in your hand. Turn on the machine on and when it's heated up and sprays out sugar strings, move your hand quickly around the machine and gather the cotton candy up with the cone! You can enjoy as soon as it's done and layer different fla...

Today's post is a small go-to guide for beginner programmers in Null Byte. With many of our community members picking up programming from our Community Bytes, it only makes sense to lay out a one-stop guide for your reference. Hopefully this guide will help you make an educated and thoughtful choice on what programming languages you want to learn, and how you want to learn said languages.

In this video series, our expert Terri Turco will show you how to make and sew a table runner, and how to make a table runner without sewing. Terri will teach you how to iron the fabric, how to stitch the fabric, and how to use stitch witchery to fuse two pieces of fabric together.

Do you believe you just don't have an intuitive sense of math? Sadly, this is the case for many people. The reality is that math is learned with practice. No one is born with a math gene making them more intuitive than others.

For anyone using open source information to conduct an investigation, a balance between powerful tools and privacy controls are a must. Buscador is a virtual machine packed full of useful OSINT tools and streamlined for online research. This program can easily be set up in VirtualBox, and once that's done, we'll walk you through some of the most useful tools included in it.

Smartglasses maker Epson remains the top gun in the drone market with its Moverio line of wearables, and the company is further elevating its offerings with its new Drone SoAR app for DJI drones.

While mobile gaming, in the 10 years since the App Store launched, has matured to console-level quality, premium augmented reality games built with ARKit (or ARCore) have been scarce.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

Microsoft's Monday keynote introduced the fourth generation of the company's Kinect sensor during Build 2018 in Seattle.

With the heavily anticipated installment of the God of War game series arriving on April 20, PlayStation has taken the opportunity to make its first foray into mobile augmented reality with a companion app.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

At the Augmented World Expo Europe press conference in Munich today, RE'FLEKT will unveil the addition of remote video calling to their RE'FLEKT One enterprise augmented reality platform, in addition to ARKit and ARCore apps that demonstrate the platform's capabilities.
A Norwegian carrier's launch of a pilotless container ship next year could lead the way to a new era in sea transportation and shipping if successful.

Research group OpenAI, a research institute co-founded by Tesla CEO Elon Musk, says it is possible to trick driverless cars' neural networks into mistaking images for something else.

The National Transportation Safety Board (NTSB) said it is still investigating the circumstances of a fatal Tesla crash last year to determine if the car or Tesla's Autopilot driverless system was at fault, but revealed more details about the circumstances of the crash.

Former Google employee Tristan Harris claims there's an easy way to combat phone addiction without installing any new software. By enabling grayscale on your phone, checking your apps and notifications will be less appealing and thus stop you from obsessively checking your phone.
Google, the company that rules the internet, is now testing a method to leverage its machine learning with its ubiquitous presence on mobile devices. The new model they're employing is called Federated Learning, and it hopes to apply artificial intelligence to Google's services on Android without compromising user privacy.

Mirror, mirror on the wall, who's the smartest of them all? Since Max Braun's Medium post went viral back in January of 2016, smart mirrors have been appearing on tech blogs in all shapes and sizes. Some are technically sound, some incredibly easy, but all are visually compelling. However, we've never seen one with a fully functional operating system and gesture support—until now.

Black Mirror, Netflix's technology-horror anthology, never fails to provide thought-provoking entertainment centered around emerging and futuristic technologies, and the third season's second episode, "Playtest," delves deep into the worlds of mixed, augmented, and virtual reality. While designed to leave you haunted by the end, offering a more "evil" narrative than we'll likely see in our actual future, the episode explores possibilities that aren't as far off as one might think.

On Wednesday, Microsoft launched a chatbot on social media that learns from conversation, and trolls quickly taught it how to be a shameless, Nazi-loving bigot. Oh Internet, an opportunity for a Hitler joke never slips past you, does it? This Is Why We Can't Have Nice Things

In this article I will show you how to obtain victim's credentials without cracking any hashes. There are a couple of ways to perform this task (for example dumping the SAM file and cracking the NTLM hashes), but here I will explain how to do it using PowerShell and a bit of social engineering. We are going to create a fake login popup.
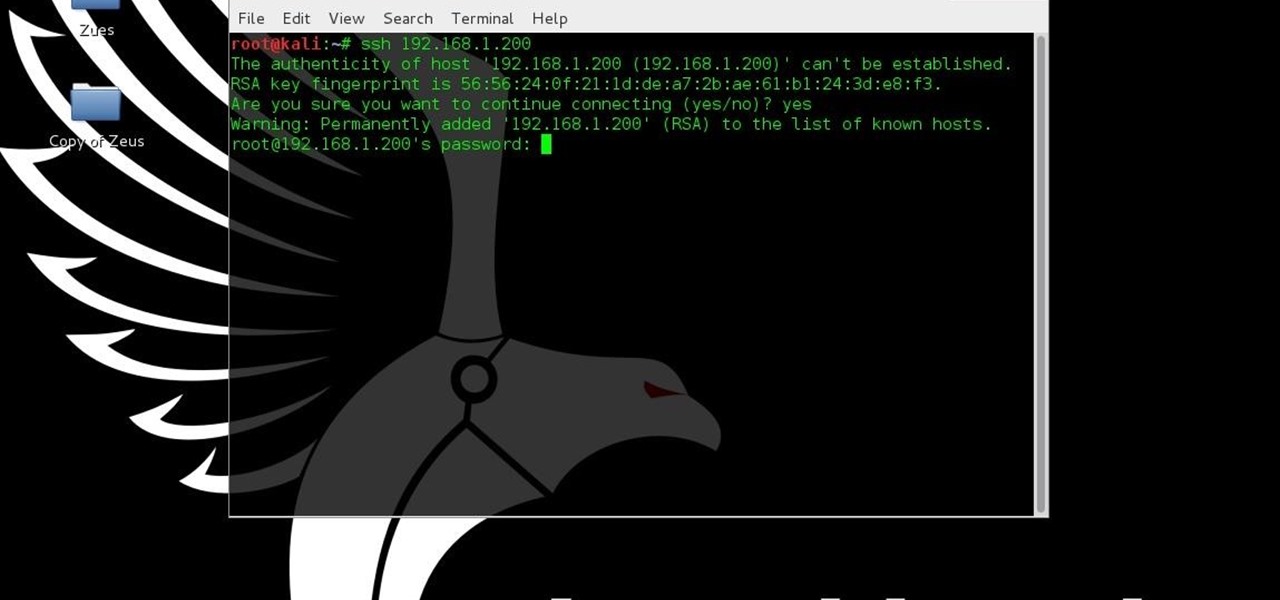
This tutorial is for people who want to try different types of hacks in an environment that is the same for everyone so it will help people to ask questions and learn. This series assumes you know how to run a VM and network them together. This series also assumes that the services running on the Metasploitable machine are needed to be running.

As you're probably well aware by now, the Apple Watch isn't just for sending text messages and checking Instagram—you can also use it as your wallet. With Apple Pay compatibility, you can use your Watch to make purchases at any retailer that accepts the payment service.

Welcome to the sequel to the latest post on writing 64 bit shellcode! This tutorial will assume that you are aware of everything mentioned in the last one, as I will try to make this tutorial void of formalities and straight to the point! If you have not read the last one, I suggest doing so unless you are familiar with basic assembly programming and system calls. This is by no means rocket science, so therefore I will simply repeat my TL;DR from last time before we get started, so that the a...

If you're like most people, you've stretched before a workout or playing sports. Doing so should help you get your muscles ready to work. While stretching is good for your muscles, you're wasting your time if it's the first thing you do. I talked to Dr. Brian Parr, professor at the Dept. of Exercise and Sports Science at the University of South Carolina Aiken, who explained this misconception and what you can do about it:

Need to add some spooky ambient fog to your super-scary Halloween party? Rather than shelling out money for a fog machine you'll probably only use once a year, make a trip to the nearest drug store and pick up a bottle of glycerin, a gallon of distilled water, a 2-liter bottle of cola, a disposable mini-pie tin, and a big candle in a jar.

Sometimes you just want to grill. It doesn't matter where you are, what you have, or whom you're with—you just want a delicious burger and you don't care what it takes.

Need a little help with your magic card skills? Check out this video tutorial to learn how to perform the "time machine" card trick.

Watch this instructional knitting video to complete and open cast on with a knitting machine. Push your needles back into forward position and knit across one row. You will want to use clips and claw weights to keep your knit work straight. If you knit with a knitting machine, this is an essential trick for getting started with larger projects.

Watch this instructional knitting video to hang a rag hem on your knitting machine. Add weights to the inside of the knitted hem to keep your knit work straight. You will need a single pronged tool or a three pronged tool. If you knit with a knitting machine, this is an essential trick for getting started with larger projects.

This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to use a knitting machine to crochet cast on. This is one way to cleverly weave your yarn onto the knitting machine and begin the piece of knit work. You may want to reference written instructions in addition to watching this knitting video.

This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to use a knitting machine to crochet a cast off. This is one way to cleverly remove your work from the knitting machine and complete the piece of knit work. You may want to reference written instructions in addition to watching this knitting video.
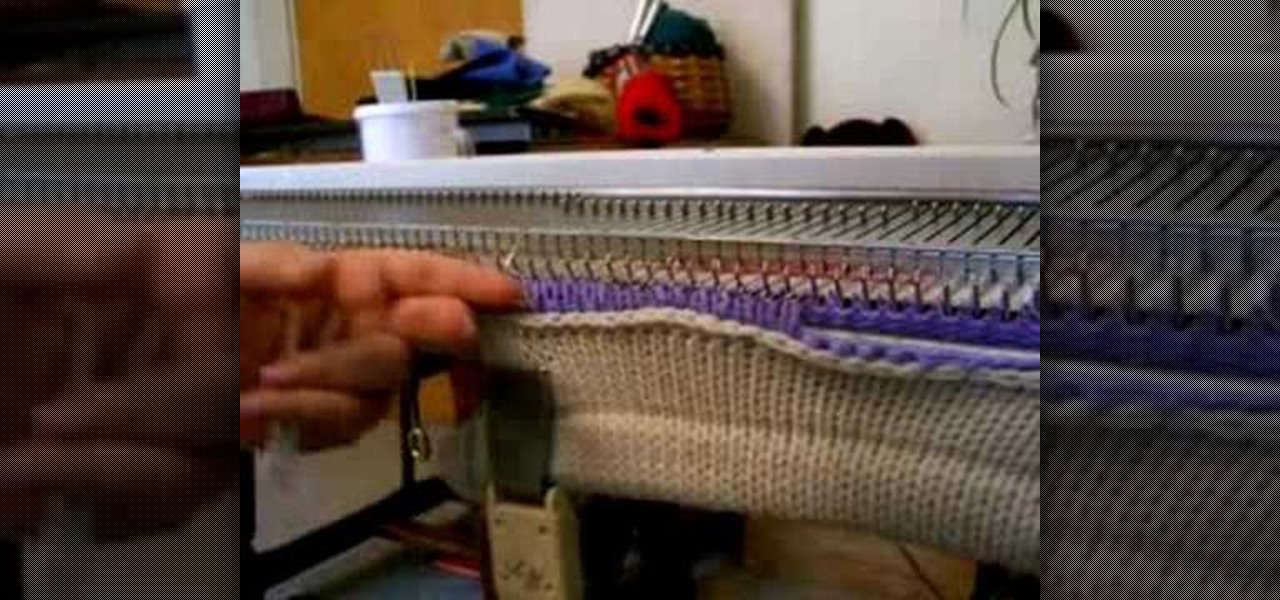
This instructional knitting video provides tips for making interesting patterns using a knitting machine. This is a demonstration of how to pick up and hang stitches. Use a three prong tool to attach one piece of knitting work to the knitting machine. Once you set the set the machine up, you can knit a wearable piece with an altering pattern.

If you knit with a knitting machine, a cone of yarn proves much more useful than a standard ball of yarn. This instructional knitting video demonstrates how an electric cone winder works. This little machine allows one to quickly wind a ball of yarn onto a cardboard cone.

Take a look at this instructional video and learn how to build your own miniature computer numerical control (CNC) machine. A CNC machine acts as a controller that reads G Code instructions for machine tools such as drills and printers. To perform this task, you'll need some geared motors you can find in old analog camcorders with optical zoom.

In this video series, let our expert show you how to use the confusing hip abduction and hip adduction machines for thigh exercises. With Sheila Lindsey's help, you can start learning how to work your inner and outer thighs. She illustrates the various parts of the machines, and she gives you some tips for achieving the results that you are looking for. With her simple gym instruction, you can begin your thigh workout with just the right amount of expertise. So, watch and learn today!