Apple just recently launched its 10.10.3 Public Beta for Mac OS X Yosemite, and while it comes with mostly bug fixes for 10.10.2, it also includes a brand new Photos application that's meant to replace iPhoto and Aperture, as well as the inclusion of more diverse emojis.

Trying to remember if it's "beer before liquor or liquor before beer" can be too much of a hassle, especially if you've already have had a few too many. While it would be great if one rhyme could determine the amount of pain you will feel the next morning, we must accept that we all react differently to alcohol and that's that.
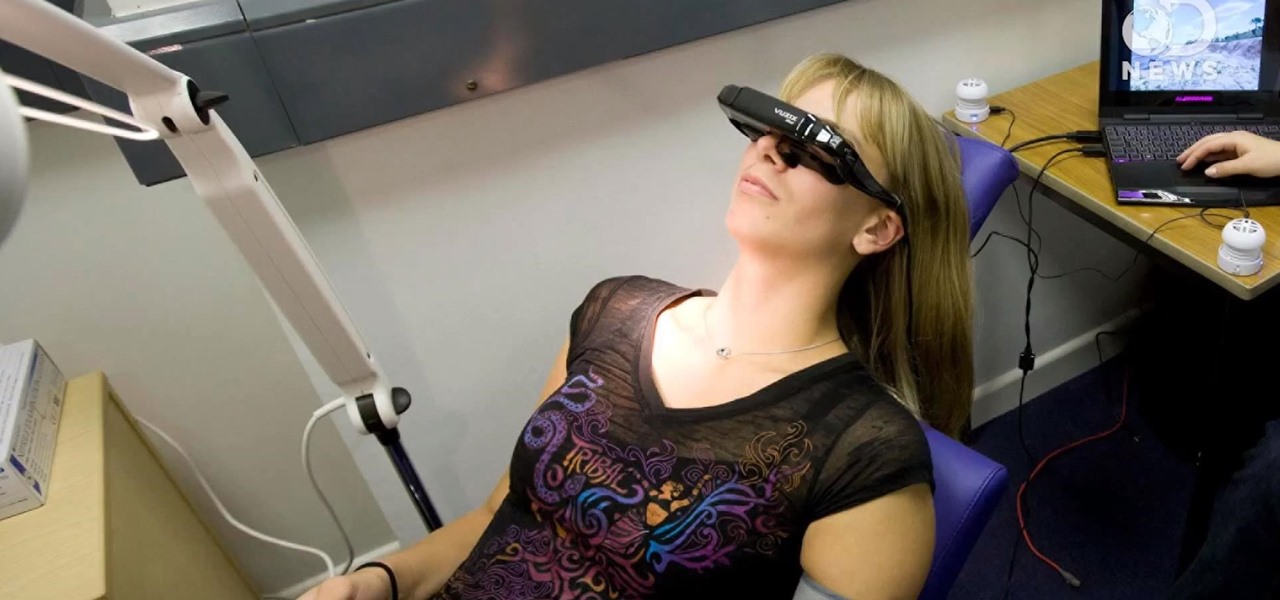
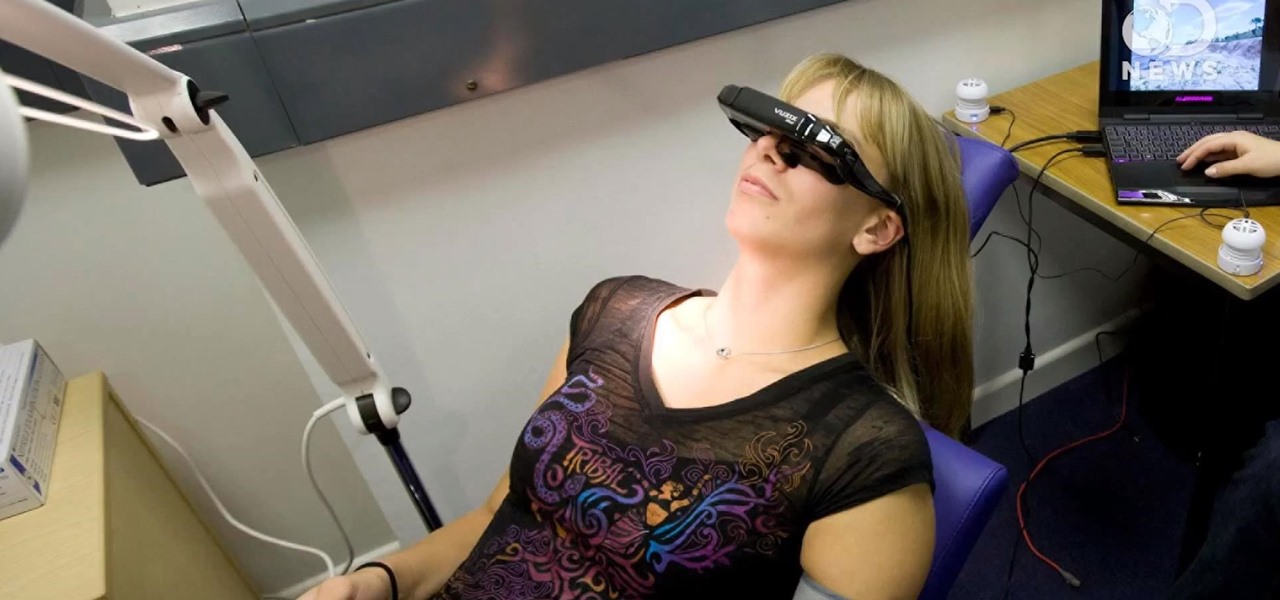
I don't know anyone that likes going to the dentist—few things are more uncomfortable than having someone else's hands in your mouth. But outside of that, not only can the pain of certain procedures be unnerving, the drugs used to numb those pains can be just as uncomfortable. Not being able to feel your mouth for hours on end is a disconcerting feeling. But all that could soon be a thing of the past, thanks to virtual reality.

Playing any multiplayer game without chatting is like watching Avatar on your iPhone—just downright sad. So, in order to get the shit-talking going between your friends and party members, you will need get your headset working properly and use Party Chat, which can get a little confusing.

Have you ever heard the expression "Dress for Success" or "Clothes Make the Man"? When you're wearing a perfectly fitted designer shirt, something inside just shouts, "I look good" and when you genuinely think that, those feeling are radiated outward to all your come in contact with. That said, what kind of designer shirt are you interested in, a bargain basement discount, or one tailored made, outlining your best features?

Electronic devices seem to have an uncanny ability to make noise at the worst possible times. It's always during an important meeting, a quiet study session at the library, or a biology final that your laptop or smartphone decides to play some obnoxious or embarrassing sound.

With more people joining the internet scene each day it's important that it's security is.. well it has to be good. Of course everything can be hacked and that's the way hackers work. They know there IS a vulnerability but they don't don't know the rest. in this article i'll try to explain the big difference between HTTP and HTTPS

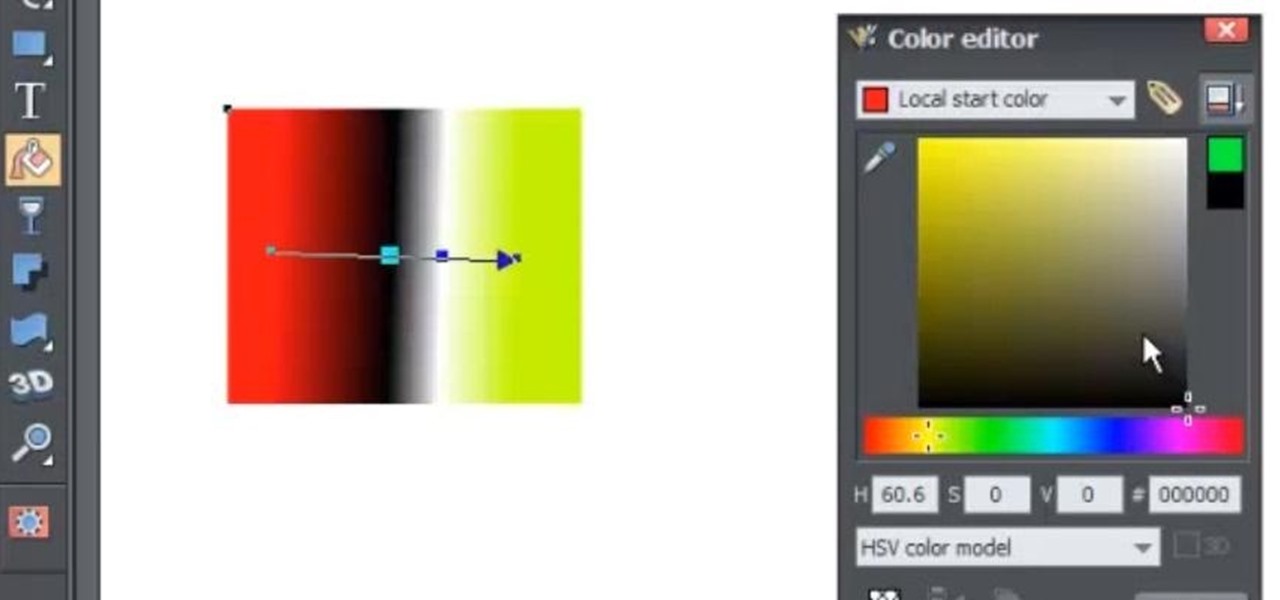
The fill tool will allow you to alter the appearance of objects in your web design document and can be very useful for marketing purposes. The fill tool can be used to give objects one solid color for simple designs.

Even though iOS 6.1 was only released a couple of weeks ago, hackers released evasi0n a couple days after. Evasi0n, the only iPhone 5 jailbreak currently on the market, is the most popular jailbreak in history—with nearly 7 million iOS devices already hacked in the mere four days after its release. Well, now it seems that iOS 6.1 is being taken advantage of again, this time with a simple exploit figured out by YouTube user S1riOS6, which lets you bypass the lock screen on an iPhone running iO...

When subjects are asked to watch a movie and not display emotions (say, a comedy without laughing, or a tearjerker without crying), they evidently use up glucose in particular areas of their brain in a way that subjects who are free to react however they want do not.

What's your Twitter handle worth? If it's considered "desirable" (aka short and simple), it'll get you around 100 bucks, or, if you prefer, the affections of a teenage girl.

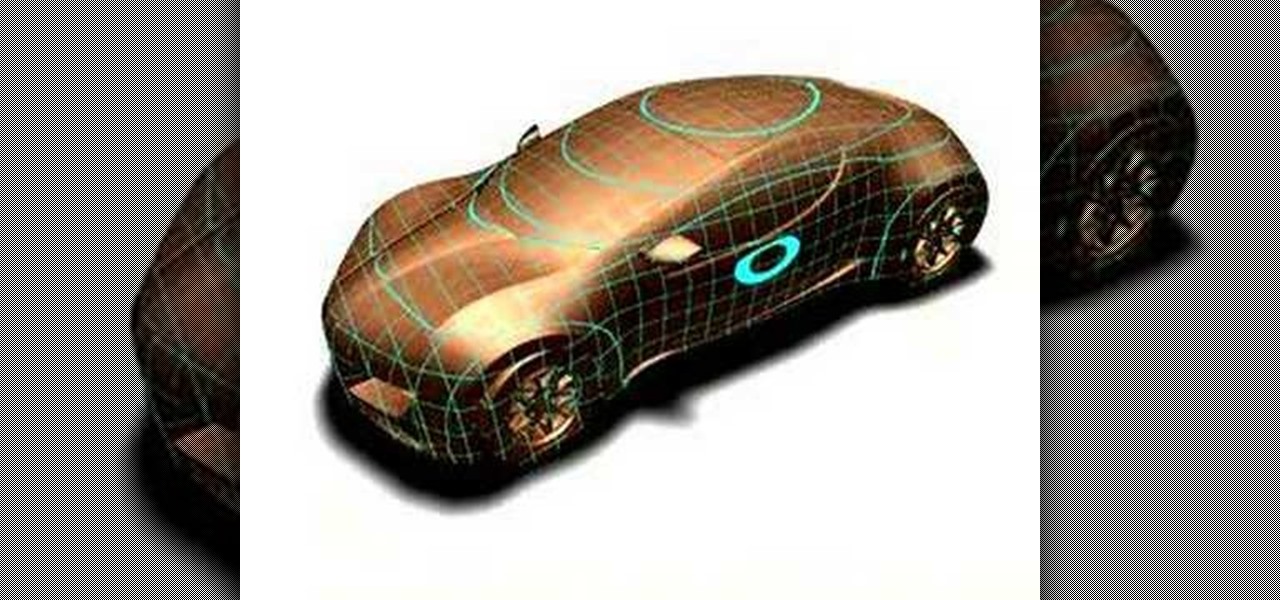
This session is tailor-made for advanced Studio users aiming to achieve ultimate quality surface creation.

World Fusion Drumming combines the energy and feel of rock, Latin, and world music with the technique and improvisational skills of jazz. In this installment from his video tutorial series on the rudiments of world fusion drumming, Berklee College of Music professor Skip Hadden will walk you through several Brazilian-style drum fills that will help you in approximating the sound of Brazilian percussion session.

In this episode we will hear from music transcriptionist Rachelle Randeen (www.MusicTranscription.com) on using the tap mode within hyperscribe. We will also hear from Emmy nominated composer and session guitarist Bobby Hartry on the Seek-Wah pedal by ZVEX.

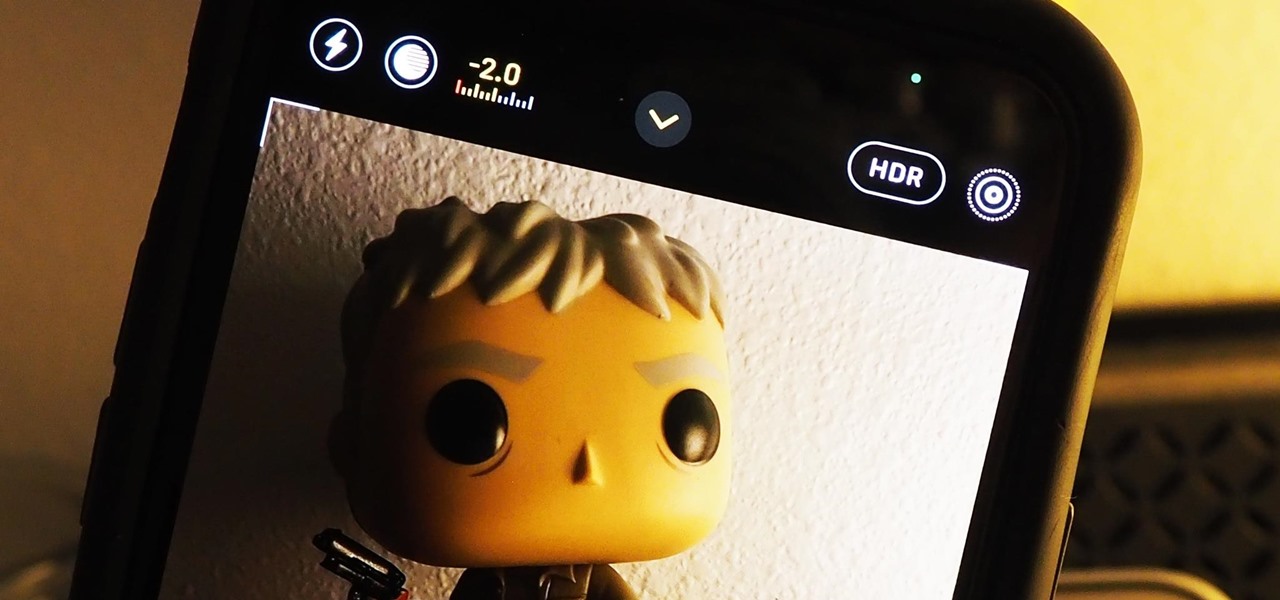
Your ability to control exposure in the Camera app is much better in iOS 14. Instead of setting the exposure for a single shot, you can also lock an exposure compensation value for an entire session while you take photos and videos. A session ends as soon as you exit the app, but you can also remind your iPhone to use your last used ECV the next time you open Camera.

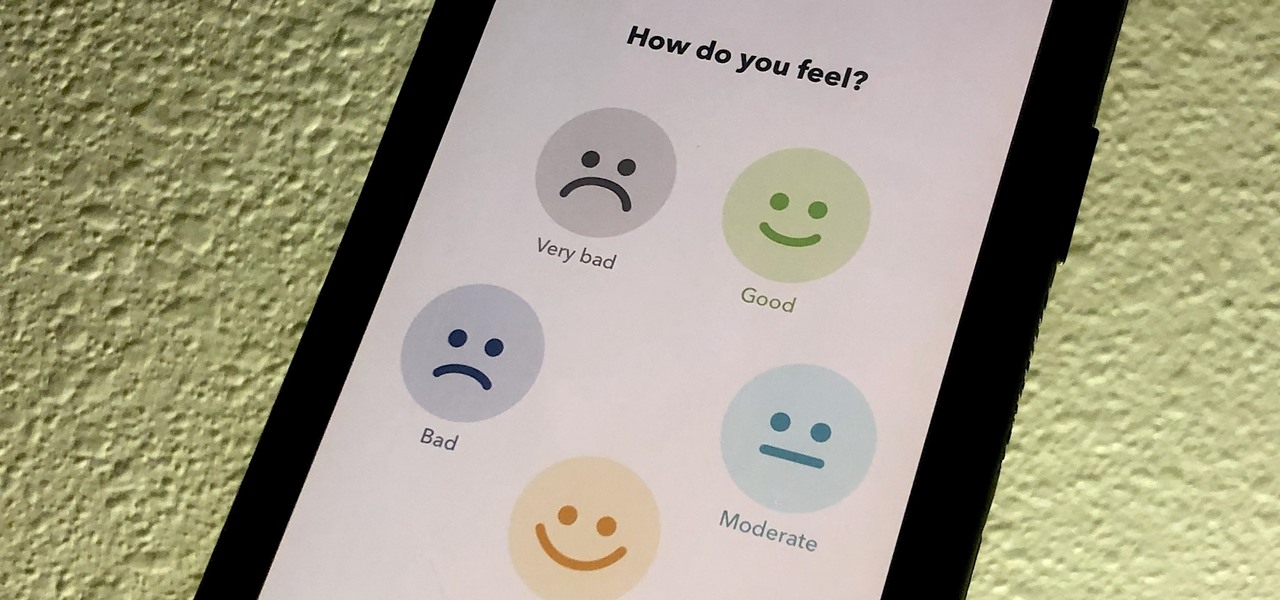
If you made a resolution for 2020 to get healthier, it's essential to concentrate on your mental health just as much as you do on physical fitness. Running and exercising is great, but a sound mind is integral to a healthy and balanced life, and you can improve your emotional and physiological well-being with your smartphone.

When you're gaming on your Android phone, does it sometimes feel "slow" and you can't figure out why? That means a drop in performance, which is when the frame rate dips, causing some noticeable stutters and lag. There's not really a way to know what's wrong unless you made the game yourself. But on the bright side, you can check any game's FPS with a simple tool.

EternalBlue was a devastating exploit that targeted Microsoft's implementation of the SMB protocol. Metasploit contains a useful module that will automatically exploit a target, as long as it's vulnerable. But what if we wanted to exploit this vulnerability without Metasploit holding our hand? It can be done using a Python file to exploit EternalBlue manually.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

Now that the dust has finally settled on Microsoft's big HoloLens 2 announcement, the company is circling back to offer more granular detail on some aspects of the device we still don't know about.

The ability to stay organized and be resourceful with data gathered from recon is one of the things that separates the true hackers from the script kiddies. Metasploit contains a built-in database that allows for efficient storage of information and the ability to utilize that information to better understand the target, which ultimately leads to more successful exploitation.

It's always a good idea to know how an attack works at the very basic level. Manual techniques for exploitation often find holes that even the most sophisticated tool cannot. Sometimes, though, using one of these tools can make things so much easier, especially if one has a solid foundation of how it works. One such tool can help us perform a cross-site request forgery with minimal difficulty.

Yesterday, I talked about what I think is the most immediately mainstream-friendly app on the Magic Leap One is (Screens), and now we'll touch upon the runner-up: Helio.

During its presentation at Unite Berlin, Magic Leap gave attendees a crash course in developing experiences for Magic Leap One (ML1), we found out quite a bit more about how the device works and what we can expect to experience with the device.

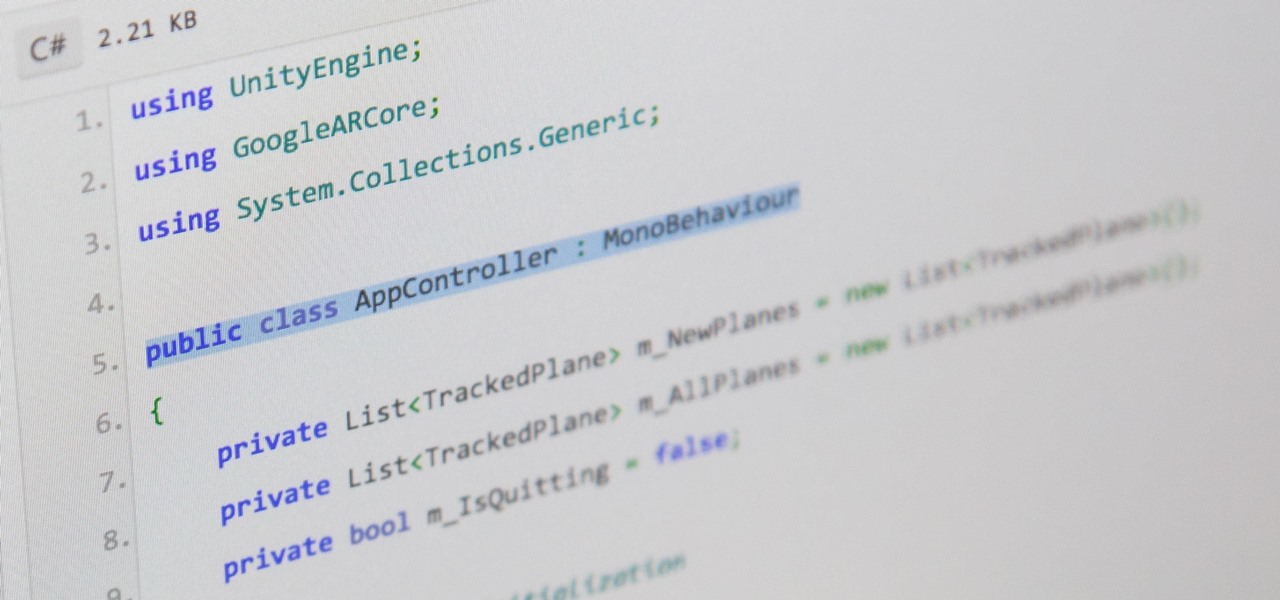
There are hundreds, if not thousands, of programming languages and variations of those languages that exist. Currently, in the augmented reality space, it seems the Microsoft-created C# has won out as the overall top language of choice. While there are other options like JavaScript and C++, to name a few, C# seems to be the most worthwhile place to invest one's time and effort.

After a hacker has configured Metasploit on a remote private server, created a resource script for automation, and created a simple payload, he or she can begin the process of remotely controlling someone's Windows 10 computer with just a few moments of physical access — even if the computer is off.

So, you want to perform an exploit on a victim, but you're not on the same network as their machine. In this tutorial, I'll be showing you how to set up a meterpreter reverse_tcp attack to work over the internet.

Today I am going to teach the various ways that you can use social engineering to hack a system. For those of you that have followed my past tutorials, you know that social engineering can unlock a world of possibilities. This is because no matter how many firewalls, no matter how many patches there are on a server, the password is kept in the minds of people...and people, are not as smart as computers.

A lot of the English you hear in the real world isn't taught in the classroom. Swearing is important to know about if you're going to speak English. In this ESL how to video, you'll learn about the difference between 'bitch' and 'slut' which many ESL speakers confuse. If you look in many dictionaries, 'bitch' is defined as a female dog, so many ESL speakers think when you refer to a female woman as a 'bitch' that she has sex with any male, but this is totally wrong. Watch this how to video an...

We may or may not see Apple's long-awaited take on AR smartglasses this year, but the company is more than getting its practice swings in with its current wearables business, which hit record revenue in 2019 according to financial results released this week.

When trying to get fit, something that can easily be overlooked is your overall sleep quality. Your body needs sleep to recharge and it helps to maintain a healthy lifestyle, there's no denying it. Luckily, Google Fit can help you track your sleeping habits without having to jump through any hoops along the way.

Developers in the augmented reality industry got a lot of love this week.

You can easily deck out your favorite phone with great wallpapers, ringtones, and icons, but what about fonts? Not all Android skins let you change the system font, and even when they do, the options are often limited to a few choices. Certain root apps can open up the system font to customization, but some of these can cause problems now that Google introduced a security measure called SafetyNet.

A simple security flaw can allow an attacker to gain a strong foothold with little effort on their part. When a web application permits remotely hosted files to be loaded without any validation, a whole can of worms is opened up, with consequences ranging from simple website defacement to full-on code execution. For this reason, RFI can be a promising path to obtaining a shell.

Mozilla's Firefox has always been a highly praised internet browser. Since it's open-source, users know what they're getting without any secrecy. It's got plenty of features that are unmatched by any of its competitors on mobile. However, speed and performance have always been a pain point for Firefox, but Mozilla went back to the drawing board to solve this problem with the release of Firefox Quantum.

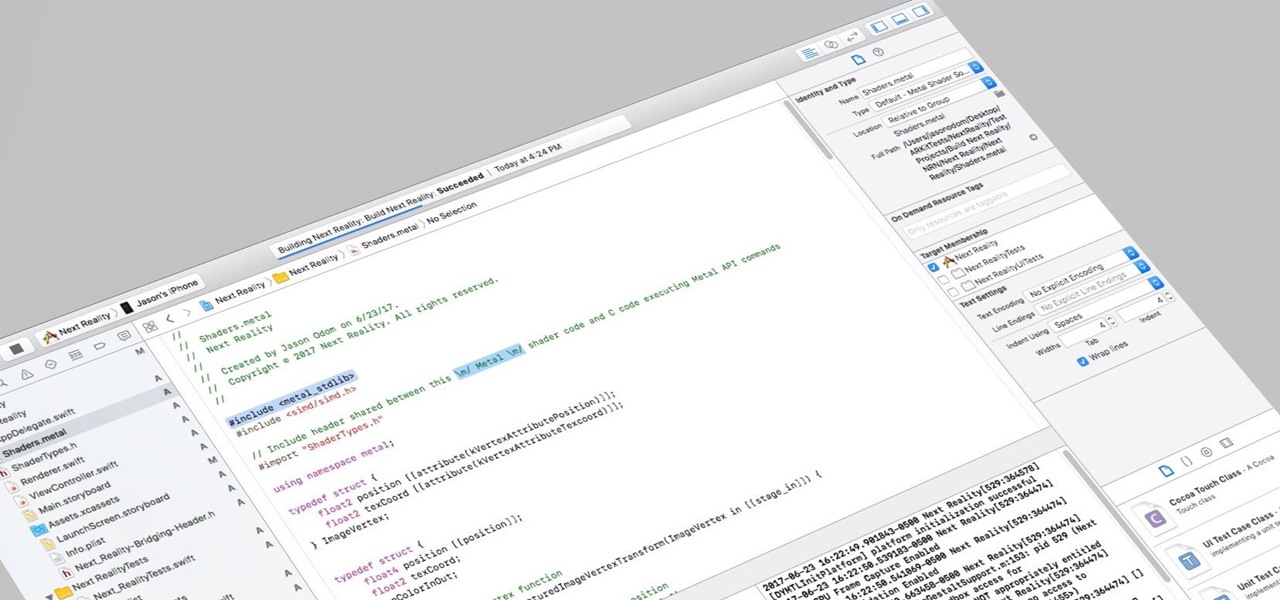
I currently am and have always been what one might call a PC/Android guy. Many that know me well would likely even go so far as to say I am anti-Apple. About an hour after seeing the ARKit demo during the day-one keynote at WWDC, I became the owner of a brand new Mac.

HIV-infected people who are treated long-term with antiviral drugs may have no detectable virus in their body, but scientists know there are pools of the virus hiding there, awaiting the chance to emerge and wreak havoc again. Since scientists discovered these latent pools, they have been trying to figure out if the remaining HIV is the cause of or caused by increased activation of the immune system.

In this tutorial I am going to show you how to create an undetectable Meterpreter Trojan using a Domain name. I have taken a few guides/tutorials and built it into one. The first part is creating the DNS Payload. The second part is creating the Executable file. Part 3 is using both in Shellter to create your undetectable Trojan. Part 4 is setting up your listener using Armitage.

Welcome back my, tenderfoot hackers! Many people come to Null Byte looking to hack Facebook without the requisite skills to do so. Facebook is far from unhackable, but to do so, you will need some skills, and skill development is what Null Byte is all about.

The Oculus Rift is finally shipping to customers in more than 20 countries, and we're getting a good idea of how the device holds up from the initial reviews. You'll see some common threads throughout: along with an impressive virtual reality experience, the device is very comfortable with a solid design.