Love them or hate them, Live Photos have their place. The problem is, they're always on, requiring you to disable the feature every single time you open the Camera app. At least, that's how Apple has things set by default — but you can change that with just a few taps.
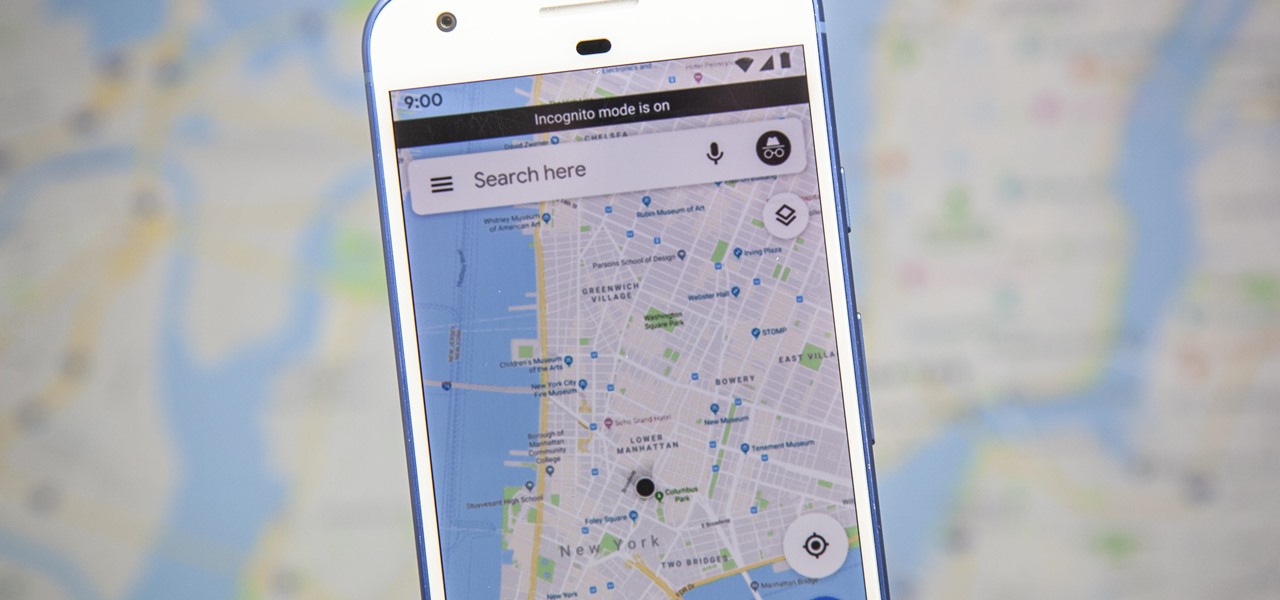
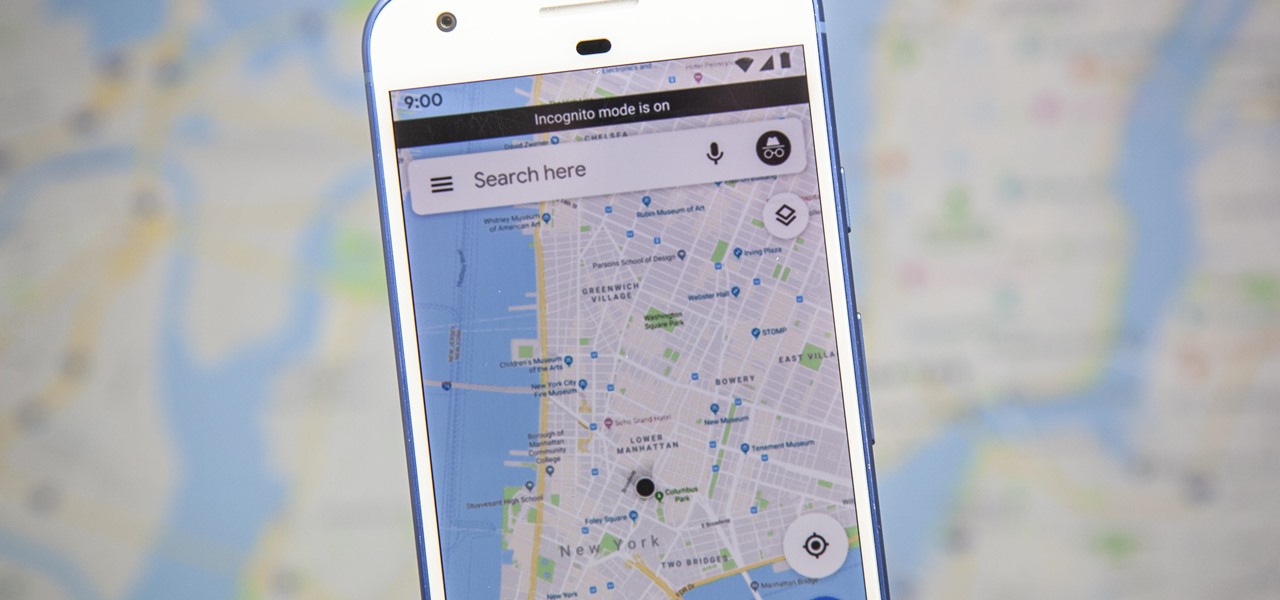
Google just recently added an incognito mode feature to Google Maps for iPhone and Android. With that, you can now use Maps in private at any time, which means you can browse and search with peace of mind.

Samsung Internet makes it easy to close your browser tabs thanks to intuitive controls, but this also means it's easy to accidentally close a tab. Fortunately, you can recover recently closed tabs on your Galaxy in just a few taps.

As part of the Samsung Development Conference today, Samsung unveiled that they will expand support for Google's ARCore platform to include the Galaxy S8+ and Galaxy Note 8.
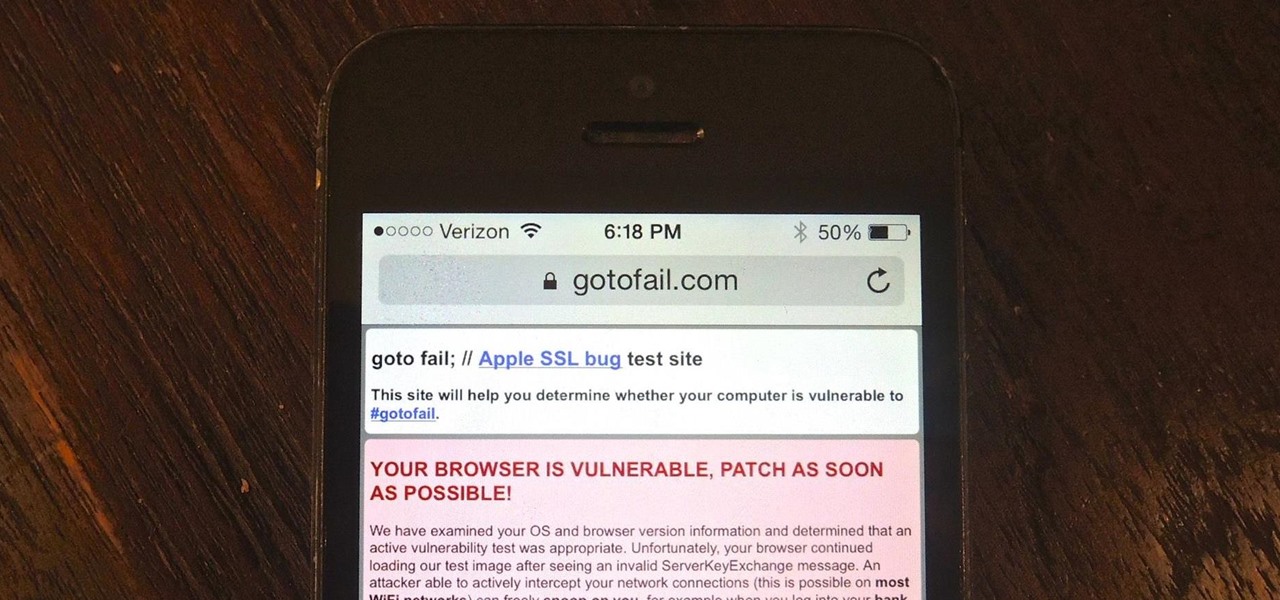
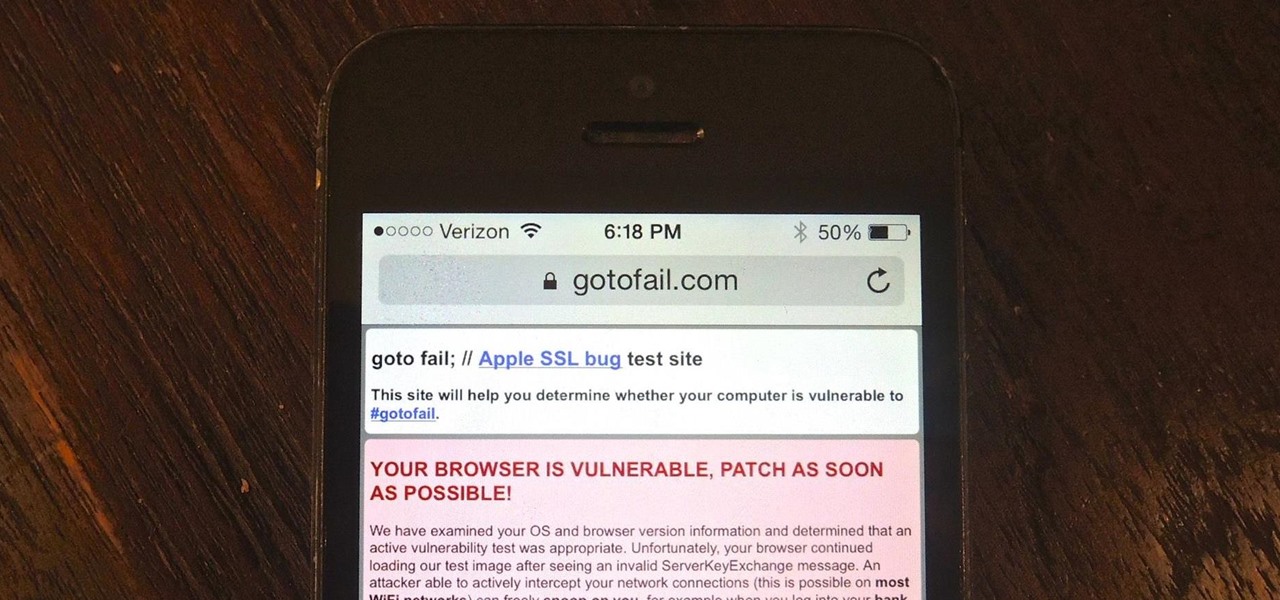
Apple released iOS 7.0.6 last week, an update to fix a serious security flaw that allowed hackers to not only capture sensitive user information such as bank statements and passwords, but also modify that same data on secure HTTPS sessions.

Want to sear the perfect restaurant-quality steak in the comforts of your own kitchen? Use a cast iron skillet.

What to do when your motivation is running low and you absolutely don't want to do something that needs to get done? If nothing is working for you, hack your brain with the following techniques to motivate yourself.

When you share a computer with other people, privacy can be a complicated matter. Even if you trust the other users, there are some things that you don't want anyone else having access to. Sure, you can encrypt everything, but what happens when someone needs to use the computer while you're in the middle of something?

We all know the dangers of logging on to our personal accounts on public networks, but we pretty much all do it anyway—especially when it comes to Facebook. But the next time you're in a public place and can't wait to check out your Facebook news feed, use this simple trick to make sure that no one gets a hold of your password. In order for this to work, your mobile phone needs to be linked to your Facebook account. All you have to do is text "otp" (for one time password) to the number 32665.

When that midday fatigue starts hitting you, sometimes the best solution is to just give in to sleep and nap it off. But how long should you sleep? Nap for too long and you often wake up feeling even worse than before, and it could be hours before you finally feel fully awake. Australian researchers conducted a study that back up this idea. They found that not only is a very short nap perfectly fine for recharging your brain, but that longer sleep sessions can cause a period of impaired alert...

To say Steven Purugganan is fast is an understatement. The twelve-year-old from Longmeadow, Massachusetts has won two Cup Stacking world championships, and appeared in commercials for McDonald's and Firefox.

For those who were creeped out by the Knoxville mannequin, well now i've outdone myself! Just like Jackass has taken their game to a whole new level with 3D, i've taken mine to a new level...the Jeff Tremaine sex doll! Though I can't take full credit for this doozy, because Mr. Julien Nitzberg(genius behind The Wild Whites of West Virginia) came up with the idea. He suggested I make one, and he would hand deliver it to Mr. Knoxville himself(for reasons only to be kept secret).

Artists have represented humans in their work for thousands of years, and Michelangelo's "David" is one of the most important artistic studies of the human form. Explore the proportions, style, and detail used in this classic marble sculpture. Analyze Michelangelo's David.

Hangouts are one of the most fun features in Google+. As long as you have a webcam and a microphone, you can "hangout" with up to 10 of your buddies on Google+ and do just about anything. Of course, sometimes it can get kind of awkward when you are hanging out and you don't really have anything to say. This problem can be mitigated if you host hangouts with a plan.

Chris Pontius is blindfolded & handcuffed and is led to either a glory hole or to sit astraddle a chair where he is further restrained.A small young female chimpanzee or small young female orangutan is brought into the room. A second small young female chimpanzee or small young female orangutan can be optional. (No boy monkeys please, we don't want make this skit even more disturbed AND ALSO GAY!)The monkey/monkies is then trained to then perform an act of fellatio on Pontius and possibly als...

In America, football has become religion. And that religion has blossomed into an unstoppable juggernaut, which has rocked the very foundations of both television and business. In an era where fragmentation has savaged traditional network television, the NFL's Nielsen ratings (both the season games and the Superbowl) have defied gravity and actually increased.

By Ethical Traveler As the world becomes ever more interconnected, being an ethical traveler becomes both easier and more urgent. Travelers today have access to far more information than we did even 10 years ago. We can observe–almost in real time–the impact that smart or selfish choices, by governments and individuals, have on rainforests and reefs, cultures and communities.

Politics(the Government) is built to accomplish a few things: maintaining order, providing necessities, operating businesses (stimulating the economy, trade), maintaining public relations and the most important of all, protecting the rights of the individuals it governs. It has a broad role, and as such, an array of bills, laws and rules to regulate itself and the country.

It's no secret that water and electronics don't mix well, but somehow, people always manage to combine the two. I've had my fair share of water-damaged electronics, everything from cheap headphones to a desktop computer. My devices are getting dunked in water so much, it's like doughnuts in coffee. And I know I'm not the only one. That jam session with your favorite song will end really quick when your iTouch is chilling in the toilet bowl.

Here's another delicious Byte. Ucha Gobejishvili, a Georgian Security Researcher under the handle of longrifle0x, discovered two cross site scripting (XSS) vulnerabilities on the official website of Forbes. He discovered the hole in two different locations on the site, and has already informed the website of the vulnerability.

What's your highest scoring game of Scrabble? Since starting this Scrabble World, I've been able to break 500 points on a regular basis. This year I've even managed to break the 600-point barrier a couple times. If you ask me, that's a pretty hefty sum to score in one game, but I'm not on par with the professionals yet.

Welcome to another Community Byte announcement from Null Byte! The goal of the Community Bytes is to teach people in a co-operative, hands-on manner. Learning from experience and immersing yourself in a subject is the best way to learn something foreign to you, so that is exactly what we do! In our sessions, we have started to both code and complete HTS missions. This means that there is something for everyone here, so make sure you join us.

With the plethora of programming that we promote at Null Byte, I figured a lot of you newbies that stop by IRC will need a big boost in the right direction to make your dive into programming a lot easier. A hot question that has been thrown around in IRC a lot when making the initial dive is, "How do I write code?". People who do not know much about computers can't understand how code is written. Code that we write here is usually scripted and written in Python, so we will use it as our examp...

Our mission for this week's Community Byte was to create a Python program to crack web-based passwords, like the ones you would see on an email or router login. I wanted it to be universal in the sense that it could be easily modified and adapted to another website just by changing a few variables. That was a success! Even though people weren't on time to the coding session, everything went well.

File recovery on Linux is a bit different than Windows. It requires different software than the Windows counterparts because every OS has their own file system. Windows uses NTFS, or FAT file systems, while on the other hand, Linux uses ext-based file systems. I personally use ext4 file system because it's the latest and greatest ext-journaling system and supports a large level of directory recursion and file sizes, but most installations still use ext2 or ext3. When files are deleted from a ...

Welcome to the second Goonight Byte! Our second coding session was kindly hosted by th3m, so props to him for letting this happen.

Our first Community Byte went well! We had around 8 people in the room coding collaboratively and watching to learn. LukeStav did the kind task of hosting it on Gobby for all of us, so big thanks to him!

Bingo! No, this isn't the game where balls fly around in machines and players dab their cards with daubers. In a game of Scrabble, bingo refers to the bonus a player receives when emptying their rack in one turn, which gets them an extra 50 points on top of whatever their play was. Even if you had two blanks on your rack and didn't utilize any premium squares on the board, you'd still have an impressive 56-point turn (at least) by using all 7 of your letters.

While using Google+, it's been apparent that there are two types of posters. There are the people who post thoughtful, serious posts about everything from tech to dealing with cancer. And then there are the meme propagators, the people who decide to rick roll others (ahem, +Bryan Crow), and constantly put up animated gifs. Sometimes they are the same people, and this is where it gets a little controversial.

As Google+ became available to more people, it started running into issues of accounts being suspended due to names that did not sound "real". According to Google+'s community standards, names that users "commonly go by" were encouraged, but not pseudonyms. Those who were using pseudonyms in their Google+ profiles quickly found themselves suspended from using Google+.

It's called a Quick Response code, but most know it simply as QR code, a matrix barcode dedicated to the world of smartphones. The information contained within the square black modules could be text, a URL, vCard, or some other kind of data. And even though mobile tagging has been around for eight years, it's just now spreading like wildfire across the globe, being incorporated into artistic portraits and wall art. And most recently... "social clothing".

Always falling asleep behind the wheel? The National Highway Traffic Safety Administration (NHTSA) estimates that there are over 56,000 sleep-related accidents each year, resulting in 40,000 injuries and 1,550 deaths annually in the United States. Don't want to be a statistic? Then you may want to try out ASP Technology's mobile application which aims to keep you awake when you're fatigued on the road.

You've had a hard day at work and need to get out of the house, have a few drinks, but you don't want to go just anywhere—you want the right crowd and the right bar. For those nights, barhopping just isn't the answer, it's SceneTap.

The point of any workout is to stress your body and initiate an adaptive training response. Period. What are appropriate levels of stress necessary to achieve the adaptive response? In terms of the cardiovascular system, studies have shown that it usually takes about two minutes to get the heart rate into the training zone. Once there, the heart shows an adaptive response after five more minutes of training in the zone. Total minutes needed to get an adaptive response from your heart? Seven.

Make this Valentine's Day one to remember! Well... because you forgot. But don't worry, you can still make that heart pitter-patter for your love by saving face and getting some last minute Valentine gift ideas on the cheap. There's no reason to shop at Hallmark or buy expensive jewelery—just use your heartwarming ingenuity to make those cheeks blush.

Throw Knoxville in a makeup chair and age him to make him look older, put him in a Catholic priest outfit and send him out on the streets. Have hidden cameras follow him as he goes into porn shops, porn theaters, strip clubs, buys tickets to kids movies, goes to gay bars, reads a Playgirl in public places (bus stops, parks, book stores, coffee shops, etc.) walks around mens rooms and locker rooms, goes to playgrounds, takes pictures and video tapes men at Muscle Beach, etc, etc.

While walking around where ever (conservative areas are great for this) wear a shock collar around your neck (you can attach a leash which another person leads you with, kind of like a little kid on a leash but more like with a mental patient... or even a sex slave, I dont judge!) anytime you "misbehave" the person next to you presses the button for you to get shocked. And of course freak out when you get shocked... or act like you like it, like I said, I don't judge.

Wouldn't it be nice to just sit at your buddy's house, plug into his network, and see exactly what he's doing? What if it was as easy as that? What makes packet sniffers like Wireshark such potent tools is that a majority of local area networks (LANs) are based on the shared Ethernet notion.

Do you need to email your wife your Social Security number? Send confidential business plans to your partner in Thailand? Send your hacker buddies the recovered hashes from last night's breach? Try using GPG, a valuable and easy to use open-source encryption program.

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.