The figure eight follow through boating knot is one of the strongest knots. (also can be used for paddling). It is generally rated at 70% - 75% of rope strength. Due to it's strength and the fact that it is easy to visually inspect, it is commonly used by climbers as their "tie-in knot" - the knot that connects the climber to the rope. It forms a secure non-slip loop at the end of a rope. For even greater security, finish the tag end with a backup knot such as one side of the double fisherman...

While this is pretty out of the way for people who don't live in Poland, this restaurant, Wodna Wieza, is really gorgeous!
From Chow's "perfect series", Chef John Sedlar demonstrates how the perfect tortilla is made.

Very cool 1920's papercraft toys from the LA Times "Junior Times" section. Just print, cut out and assemble (if you don't mind turning a blind eye to the dated racial association, e.g. Lee Ling...the Chinese Laundry Man).

SQL injection is a common web application attack that focuses on the database backend. WebGoat is a deliberately insecure J2EE web application maintained by OWASP designed to teach web application security lessons. I plan to use WebGoat for a few future videos. This first WebGoat video will show the basics of installing WebGoat and doing two of its SQL injection lessons. Hack websites with SQL injection and WebGoat.

It turns out that the government of Saudi Arabia has managed to do something last month's Game Developers Conference couldn't — give us a few new glimpses of the Magic Leap One being worn by someone other than Shaq.

Mac OS X has finally added a way to use two apps side by side in full screen mode, à la Microsoft's Windows Snap. But since it's only available in 10.11 El Capitan right now, those of us with older systems will have to wait until the El Capitan Public Preview or final build is released later this year.

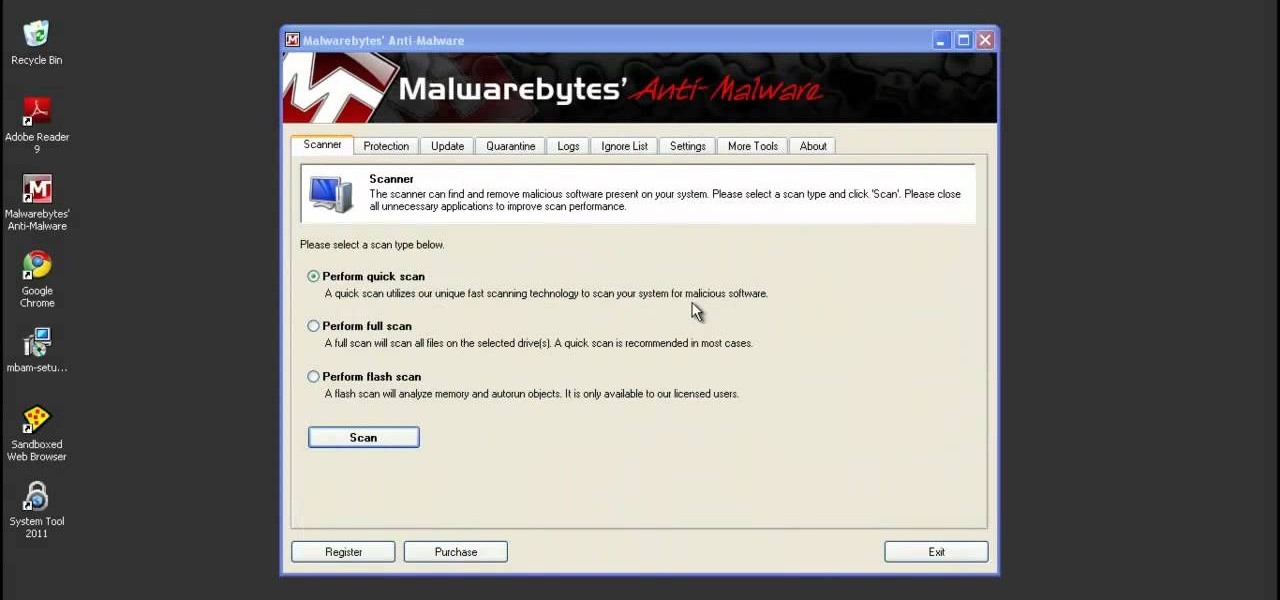
System Tool and System Tool 2011 are the most widespread fake-antivirus rogues on the internet today, infecting countless machines. This video will teach you how to uninstall both warez completely, returning your computer to blessed normalcy.

The iPad's got some stiff competition these days, especially from Android, who plans to invade the tablet market with their high-end mobile operating system. And they're off to a good start with the Samsung Galaxy Tab, available from AT&T, T-Mobile, Vodafone and Verizon Wireless, along with other carriers.

What's better than one prank? Five pranks! This video from the notorious Kipkay provides five fantastic, funny, and facile pranks to pull off on your friends and family… maybe even your enemies.

Do you remember "The Heist" from episode 21? Well, the sequel is even more unfair than the original! Check out this video if you want to stump people with a trick called "The Heist II." For this trick, you need only a few simple supplies: a match, a cup, and a nickel.

Systm is the Do-It-Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. They will help you avoid pitfalls and get your project up and running fast. In this DIY episode, see how to build a firewall from a junk PC to protect networks.

Learn the French hand gesture for "oh la la!"

In this video tutorial, viewers learn how to change the default password on a NET-GEAR router. Begin by opening your web browser and go to this site: Router Login. When the Prompt window opens, type in your router's user name and password, and click OK. In the sidebar, under Maintenance, click on Set Password. Now type in the old password, new password and re-type the new password once again to confirm. Finish by clicking Apply. This video will benefit those viewers who use a NET-Gear router,...

In this video tutorial, viewers learn how to change the default password on Apple Airport Base stations. Begin by selecting the Apple Airport Express item. Then double-click the Apple Airport Express item or press the Configure button on the bottom right of the screen. Now enter your password and click OK. Then click on the Airport tab and click on Change Password beside your Airport name. Now type in the new password, confirm it by re-typing it and click on Change. Finish by clicking on Upda...

In this tutorial, we learn how to set and encrypt a Wi-Fi password using WPA in Netgear. First, type "www.routerlogin.net" into your internet browser. Next, a pop-up window will appear, type your user name and password into this dialog box. A new window will pop up, click on the tab on the left hand side of the screen that says "wireless settings". Type in your user name and password once more, then find where it says "security settings", and click on the "WPA-PSK" radio button. Now, make a p...

Safari v1.0 is a web browser for Mac OS X. This simple video explains how to disable accepting cookies in the Safari web browser. There are only 4 very easy steps to follow. Open your Safari web browser window. On the your Safari browser left menu tab click on Safari, a drop down will appear once you click it.

Watch this video to learn how to encrypt Wi-Fi using WEP password on Linksys in 4 simple steps. Connect to your wireless network. Open your Web browser and type in the web address http://192.168.1.1. Press enter key. Type in the User Name for your network. Type in the Password, press OK button. Select the Wireless text tab, select the Wireless Security text item. Pull down and select the WEP menu item. Type in a good password. Click the Generate button. Click the Save Settings button. Encrypt...

Check out this hacking video tutorial to learn how to hack a cell phone with a magnet. You can easily hack Verizon's Motorola RAZR mobile phone to bypass the user password.

In this tutorial, you'll learn how to exploit weak security questions to take control of a given Yahoo! Mail account in much the same way Sarah Palin's Yahoo! account was recently "hacked." (To access Sarah Palin's account you will need, in addition to the tutorial, some manner of time travel device.) For a detailed, step-by-step reenactment of the "hack" (scare quotes very much intended), take a look. "Hack" Sarah Palin's Yahoo! Mail account.

Looking for a front-yard upgrade that'll have visitors beating a well-lit path to your door? The answer is an easy to install pathway lighting set. Too often, we're forced to choose between form and function. But when it comes to the route that leads to your front door, you can have it both ways: a pathway lighting system that combines the safety and security of good exterior illumination along with decorative elements that enhance your landscaping. Even though you might not have any experien...
In a riveting interview on TruNews Radio, Wednesday, private investigator Doug Hagmann said high-level, reliable sources told him the U.S. Department of Homeland Security (DHS) is preparing for “massive civil war” in America.

As hard as you try to protect your valuable information with strong passwords and anti-doxing measures, there's nothing you can really do when someone else gives up your goods. And that is the case with the recent Global Payments breach.

US Secretary of State Hillary Clinton lashed out against Russia and China after a meeting in Tunis. The meeting aimed to increase pressure on Syria to stop its bloodshed. Hillary represents the US as an ally for the rebels.

Merry Christmas all! I hope you are all having a very wonderful day!

This article relates to changing the settings in Adobe Flash so that you can improve your overall computer security and privacy. Changing these settings might have a negative performance impact on your computer - but it is worth while.

Security awareness seems to be a hot topic these days on the web, with developers making apps and devices that can hack networks and machines with just a few clicks. But these applications aren't only exploiting security flaws in systems and networks, they're being used by amateur and wannabe hackers who want to have a little fun, but don't want to learn how to actually "hack" anything.

As a USC student with limited funds, I'm always trying to figure out how to make the most out of my night when I go out. LA is great because there is so much going on for little to no cash if you know where to look. Echo Park/Silver Lake definitely has the most options, see below for my breakdown.

There are nearly 100,000 unique onion service addresses online with over two million people using Tor every single day. Join me as I explore a small fraction of what the Tor network has to offer.

Its official: On May 8, T-Mobile finally released the Android Oreo update for the LG V30 and V30+. Now, every major US wireless carrier has pushed the update. For me, this update is a big deal. Not only does Android Oreo bring some new tools and features, but LG has also included a few additions as well.

The 2015 LA Auto Show showcases the best of the auto industry—well, at least according to car companies. Increases in horsepower, better fuel economy, and most importantly—the latest tech—is all on display during the 10-day event in Southern California. Once of my first missions at the show was to figure out who is putting the most care and thought into in-cabin electronics, mainly the ones that guide us around and play our music, affectionately known as "infotainment."

There was one company at the 2015 LA Auto Show that had everyone intrigued. They didn't have a big booth, and they only had one car on display, but they definitely had everyone's attention.

Unbeknownst to you, hundreds of retailers, shopping malls, coffee shops, and airports track and log your movements. Using sensors installed by retail analytics companies, businesses sniff out your smartphone's MAC address, a unique fixed identifier to your device, whenever your device interacts with their Wi-Fi hotspots.

Security is always a top priority for our smartphones. Leaving your phone at the bar or even at a friend's house can leave you open to hacks and lead to the loss of sensitive information.

The new Jelly Bean 4.2 is a great improvement over previous Android versions for the most part, except one thing—the lockscreen. Users have voiced their complaints in regards to Android 4.2's new lockscreen features, and it's not pretty.

The Library of Congress video archives brings this Baroque dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a bourée from "La Savoye" dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a Baroque bourée from "La Savoye" dance.

The Library of Congress video archives brings this Renaissance dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a cinq pas de la gaillarde dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a Renaissance Cinq pas de la gaillarde, or basic galliard step dance.

The Library of Congress video archives brings this Renaissance dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a cinq pas de la gaillarde dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a Renaissance Cinq pas de la gaillarde, or basic galliard step dance.

Michelle Phan demonstrates how to create an egg mask facial. Egg white and yolk mask. Perfect for oily skin. It helps brighten and tighten the skin. The reason why the egg yolks are so good and rich for your skin is because they are loaded with Vitamin A! Protein and nutrients!

Wireless networks. Nowadays, everyone uses 'em, but most don't secure 'em. On average, I can drive up and down any block in my city and find at least one or two open or semi-open networks on any given day. With some changed MAC addresses for good measure, an attacker can use your network as a spring board for who knows what. When the police come a few days after, they are coming to your door—and not to talk about how nice your lawn is. Don't be that guy.