From LAist: "A silly ad is how you get attention, right? Well, the Republican candidate for California's 36th Congressional District, which covers Venice, the South Bay, San Pedro and parts of South L.A., has certainly done that.

Season 5 of Dexter is set to premiere on September 26th, and it's looking bloody as ever. The trailer for the highly anticipated season debuted at this year's Comic-Con. Things aren't looking so good for Dex... Not a fan (yet)? Instructables user Forkable offers a brief synopsis, and more importantly, an edible party favor for your upcoming premiere party.

Anybody who says they don't love golden, crispy fried chicken is lying. Fried chicken is DEE-licious.

Check out CocoRosie at the historic Orpheum Theatre in Downtown LA as these sisters promote their latest release Grey Oceans.

Matador, the label behind our favorite indie bands is turning 21 this year. To celebrate they're having this awesome festival in Vegas! Guided By Voices will be reuniting to play the Matador at 21 Festival along with Belle & Sebastian, Cat Power, Cold Cave, The New Pornographers, Sonic Youth, Spoon, Yo La Tengo and many more. Matador at 21 will be taking place at The Palms in Las Vegas from Friday, October 1 - Sunday, October 3 in collaboration with Los Angeles promoters FYF Fest. No on-sale ...

Janelle Monáe is simply in a class of her own. Genre-bending beats, distinctive fashion sense (à la the fabulous Grace Jones), and sweet dance moves to boot. Whether or not Monáe falls within your musical realm, you've gotta admit: the tiny five-foot-tall singer is chock full of infectious energy and exceptional talent.

Check out this article from the LA Times that picks through how awesome Red Dead Redemption is for its creators Take Two.
Microsoft office 2010 is the successor version of office 2007 and is code named as office 14. It is the first 64 bit version of office which is only compatible with Microsoft service pack 3, Windows vista and windows 7. It was released on April 15, 2010. It is the first Microsoft application which offers free online version of word, excel, PowerPoint and one note. These can be easily used with all the popular browsing software. The various functionality which are added in office2010 are descr...

Los Angeles is filled with a myriad of options restaurant wise for all of your foodie needs. I am indeed a foodie, but there is nothing better to me then simple produce inspired plates. Here are three of my favorite spots in Los Angeles to find great organic treats all around the city. Happy Eating!

COOLHAUS! Just in time for summer, if you are in the LA Area this great wagon o goodness is here for you! These architecturally inspired ice cream sandwiches only employ the best (organic whenever they can) products for their handmade artisanal ice cream flavors like mexican chocolate, marscapone balsamic fig and brown butter with candied bacon. These bovine derived beauties are folded between two homemade cookies that are bound to make your mouth smile. They are a moving operation so make su...

If it has an internet connection, it's got a huge attack surface for hackers. But what makes your phone even more dangerous is its portability and the collection of sensors it houses that can be just as good at tracking you as the camera and mic.

WhatsApp is the go-to messaging app for millions worldwide and its easy to see why. The app can be considered the Swiss Army Knife of texting thanks to numerous features like Group Chats and Status Stories, in addition to striking a great balance between ease of access and overall security.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Many popular IoT devices have terrible security. For instance, a hacker who's on the same Wi-Fi network as a Sonos speaker can assume direct control over the device's behavior. If an IoT device doesn't secure the messages used to control it over a network, it's easy for somebody to write a few Python scripts to make it do whatever they want.

With all the controversy around the Pixel 3 XL, the regular-sized Pixel 3 might be the phone of choice for most users. Thanks to the huge boost in screen size, the little brother is now an easier pickup for those who like a bigger screen. And once more, the internals are the same, giving you the same experience as the 3 XL without the display notch.

The "controversial" Pixel. No phone in the history of Google's Pixel lineup deserves this title more than the Pixel 3 XL. For some (including myself), the design is a welcome change that embodies the modern design of 2018 flagship phones. For others, it has an ugly huge display notch that destroys symmetry.

Most companies have services like employee login portals, internal-only subdomains, and test servers they would prefer to keep private. Red teams and white hat hackers can find these obscure and often vulnerable services using a tool designed to help protect users from fraudulent certificates.

If you're using a mobile device, it's a pretty safe bet that your apps are sending lots of information back and forth from their servers. To make sure there is no inappropriate data collection going on, it's worth setting up a web proxy to spy on this traffic, so you know exactly which apps are "phoning home" and when.

Kali Linux is established as the go-to operating system for penetration testing, but in its default configuration, it's less than ideal for regular desktop use. While in many scenarios, a live boot or virtual environment can resolve these issues, in some situations, a full installation is better. A few simple changes can be made to a Kali Linux desktop to make it safer to use in this environment.

While the security behind WEP networks was broken in 2005, modern tools have made cracking them incredibly simple. In densely populated areas, WEP networks can be found in surprising and important places to this day, and they can be cracked in a matter of minutes. We'll show you how a hacker would do so and explain why they should be careful to avoid hacking into a honeypot.

Between the Cambridge Analytica scandal and the revelation that Facebook logs your calls and text history on Android, many are considering joining the #DeleteFacebook movement. But it can be difficult to leave the site, because so much of its content is only available to active users. If you want to keep in the loop without sacrificing your privacy, you'll want to follow the steps below.

Before you go ahead and delete your Facebook — don't lie, you've been thinking about it — consider this. Facebook offers users a wide variety of privacy options to mess with, which can help you find a little control over your information. We're not saying this solves Facebook's privacy crisis, but it might be a more reasonable option than throwing in the towel entirely.

After finding and monitoring nearby wireless access points and devices connected to them, hackers can use this information to bypass some types of security, like the kind used for Wi-Fi hotspots in coffee shops, hotels, and in flights high above the ground. By swapping their MAC address for that of someone already connected, a hacker can bypass the MAC filter and connect freely.

In just a few months, Binance has experienced explosive growth, overtaking its rivals to rank among the top three cryptocurrency exchanges in the world by trading volume. Without a doubt, Binance is now among the best sites for trading alt-coins like Ripple (XRP), Stellar (XLM), and NEM (XEM) to name a few.

Threats to your privacy and security are everywhere, so protecting your data should be the highest priority for anyone with a smartphone. However, one threat many people overlook is the company who supplies the operating system your Android phone runs — Google.

Welcome back, my fledgling hackers! Hacking has a long and storied history in the U.S. and around the world. It did not begin yesterday, or even at the advent of the 21st century, but rather dates back at least 40 years. Of course, once the internet migrated to commercial use in the 1990s, hacking went into hyperdrive.

You (or your partner, or both) are a Steampunk. Let's get away from all the mindless, unfeeling commercialism for a few minutes and think about dates instead of gifts—where do you take your significant other for Valentine's Day? What would be the ultimate Steampunk Valentine's Day date?

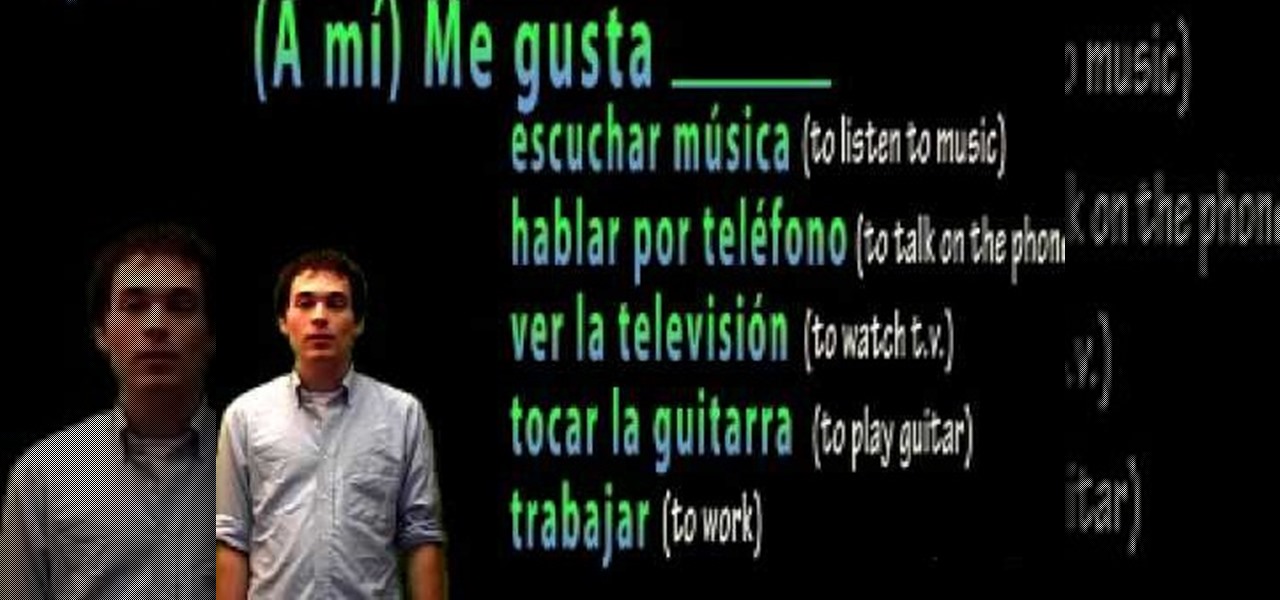
In this video, we learn how to speak Spanish: "me gusta" (I like). First, you will need to learn how to form sentences. After saying "me gusta", you will need to say a verb that you like to do. These include: "nadar" (to swim), "practicar deportes" (to practice sports), and "estudiar" (to study). These are just a few of the many words you can use for verbs. An example of a sentence would be "me gusta tocar la guitarra" (I like to play guitar). If you would like to say you don't like to do som...

Apple pie is the classic dessert enjoyed anytime, breakfast, lunch or dinner! And granny smith apples make the best filling. This golden, crisp apple pie is delicious with cinnamon, whipped cream or à la mode. Watch the full video recipe for baking apple pie with Chef Hubert Keller.

In this video, Nate Bosch from PianoLessons.com shows viewers how to play "Row, Row, Row Your Boat" by ear. This simple song is built around the G-major scale and the chords D and G.

What would be cooler than showing up at your prom with a famous celebrity? It's a long shot, but here's your best chance to make it a reality.

Hack mybrute with this mybrute cheat. MyBrute hacks, cheats, tricks. Watch this video tutorial to learn how to hack a wolf or bear in MyBrute (07/26/09). Without Cheat Engine!

PlayStation Store is having great discounts on some PS3, PS4, and PSV games. You can get GTA V for only $25 and some other Rockstar games with the discount of 60-80%. You can check the whole list here: Big savings on Rockstar titles start today - PlayStation Store.

Love the look of Metro's live tiles, but can't see yourself ever owning a Windows Phone device? Then fear not—you don't have to subject yourself to Windows Phone in order to experience those sweet live tiles. You can simply use Tile Launcher, a new launcher app for Android devices that simulates the Metro interface pretty well. Tile Launcher, which is in beta for Android 4.0 and above, allows users to style their homescreen with customizable tiles à la the Metro user interface! Some of the fe...

Johnny Knoxville should dress up like a hard-core redneck and go to the hardest gangster rap club in LA and try to blend. It would be hilarious if he tried to pick-up on pretty ladies and deliberately got out on the dance floor for a dance. A disguise of corse will be needed and should consist of usual redneck clothes complete with mullet in tow. At some point he should act so drunk that he somehow takes over the DJ table and and puts on any George Jones song. This prank could possibly includ...

The Redneck Roller Coaster is the invention of Dave Rock, a Canadian garbage picker and nudist. He has also fathered many children, two of whom he 'made for lezbians'.

Way before $5 gallons of gas and billion dollar bailouts, Kipkay made this gas saving video. Congratulations Kip on winning the 2008 WonderHowTo Recession Survival Award!

The WonderHowTo Awards winners are in. The votes have been tallied. Despite all of these devastating wild fires, pyromania thrives!!

On June 23, 2003, Linden labs created a free client program known as Second Life. This program allows users, or residents, to interact with each other in a virtual world by using avatars. Thanks to this program, residents are able to explore, socialize, and create and trade virtual property, and services with each other. Second Life has become one of the most popular programs used by various age ranges from 16 to 60, but how do you enter this world and get your own avatar?

Does your network begin to crawl right around the time your sinister-looking next-door neighbors get home from work? Do you harbor suspicions that one or more of them may be stealing your Wi-Fi? It's easy to find out. And equally easy to give freeloaders the boot. In the guide below, we'll show you how to secure your wireless connection in three easy steps.