There's a lot of fighting to endure in the Xbox 360 game Bayonetta. In Chapter 1 - The Angel's Metropolis, it's your first real battle. Central Station Platform - Go to the far side of the platform and go through the security gates. The door on the far side of this hall is locked, but on one wall in the hallway you'll see a strange sphere. Walk up to it and start doing combos to open a door.
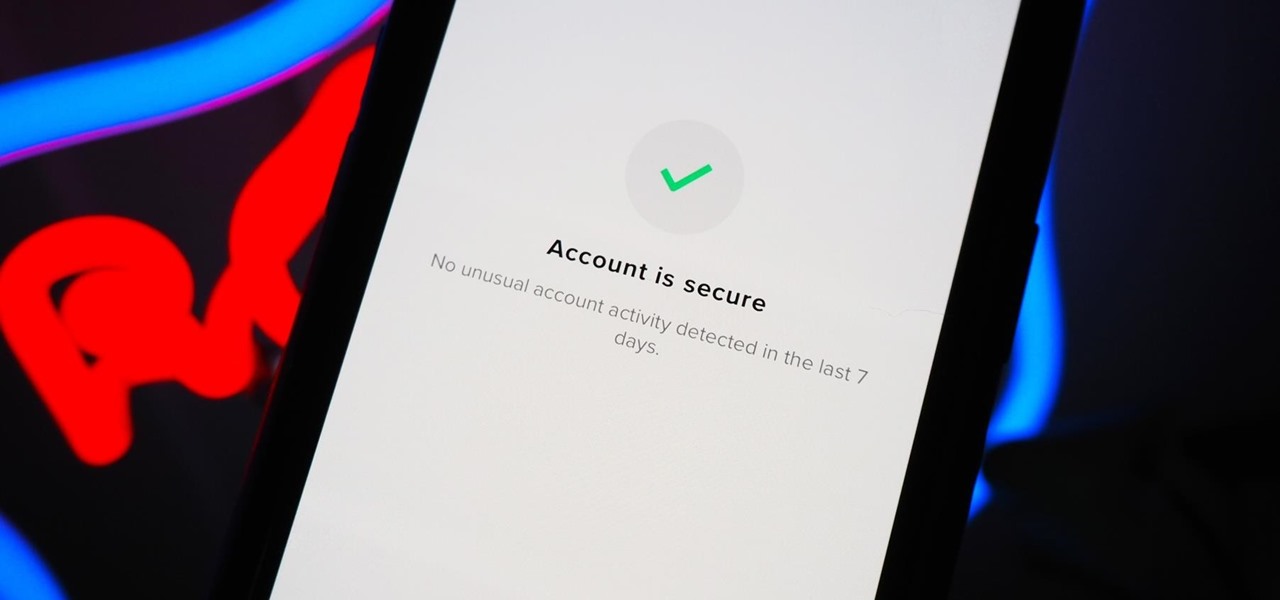
You should feel relatively safe to watch and post videos on TikTok, but like with any online service, you're always at the mercy of hackers.

Smartphones are more like computers than actual telephones. Unfortunately, thieves, hackers, and other bad actors know this and are always looking to make money off your personal data. Thankfully, your Galaxy S20, S20+, or S20 Ultra has tools to combat these threats — as long as you know where to look.

One of the more low-key functions to arrive with the Note 10 was the ability to easily record your screen system-wide. Thankfully, this long-awaited feature will finally make its way to popular Galaxy devices like the S10 and Note 9 thanks to One UI 2.

After building a tech empire on revenues from search advertising, Google is not about to sit back and let Snapchat, Facebook, 8th Wall, and others draw all the AR marketing attention to their platforms.

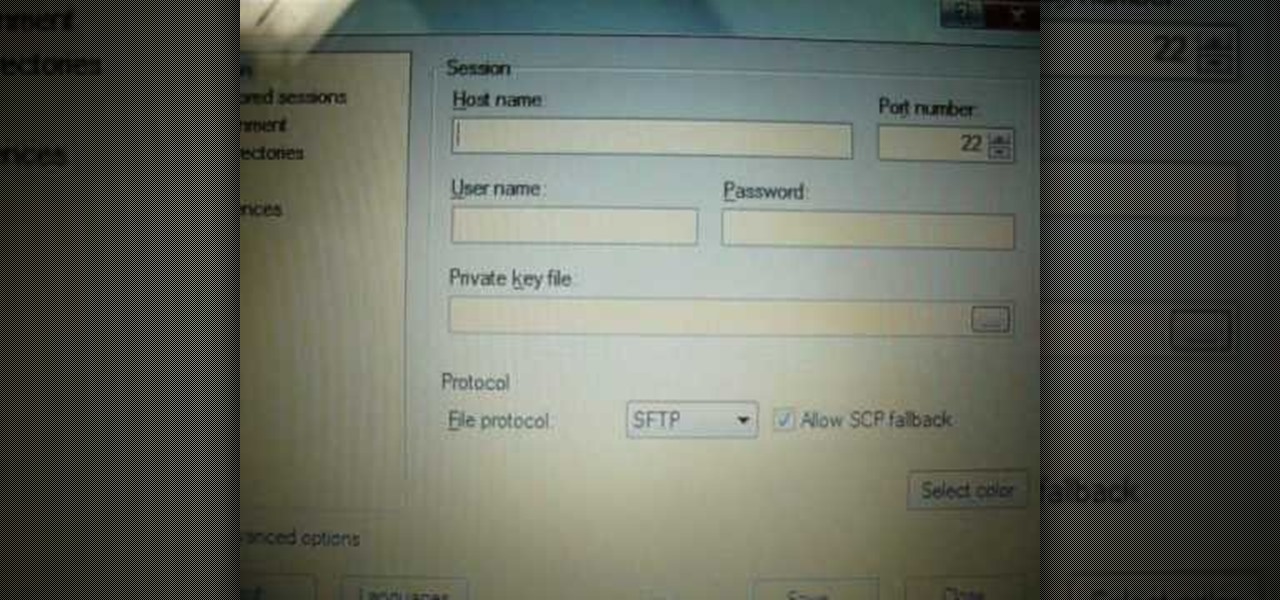
Computers all over the world rely on a program called "libssh" to use the SSH communications protocol, which allows trusted users to log in and administer computers remotely. Due to a flaw in libssh, fooling a computer into granting SSH access is as easy as telling it you already have permission. The vulnerability can lead to an attacker gaining complete control over a device.

If you've grown bored of day-to-day hacking and need a new toy to experiment with, we've compiled a list of gadgets to help you take password cracking and wireless hacking to the next level. If you're not a white hat or pentester yourself but have one to shop for, whether for a birthday, Christmas present, or other gift-giving reason, these also make great gift ideas.

One of Apple's most touted (but seldom seen on social media) apps, Clips, got an update on Wednesday.

Over the years, we've seen security breach after security breach, as well as high-profile data scandals where collected personal information was misused by companies. Apple makes customer privacy a priority, so there have been few issues to worry about when it comes to its services on your iPhone. However, there are still plenty of privacy settings to explore and change, especially within Safari.

Google Calendar is a cornerstone of the Google Suite, perhaps second only to Gmail itself. Whereas email is constantly plagued by phishing attacks, as of yet, the calendar is a relatively untapped social engineering attack vector. But it's relatively easy for an attacker to inject a meeting or event into a target's Google Calendar and use it to exploit them.

Augmented reality developers are rapidly bringing science fiction tropes into the real world, with the latest example leveraging the TrueDepth camera on the iPhone X to emulate the cloaking technology made famous by movies like Predator and Marvel's The Avengers.

So you want to do Kendrick Lamar's "HUMBLE." in Animoji Karaoke, but you need the lyrics. Well, now you can see those rhymes spit out in augmented reality.

The Easter Bunny is about to get his first experience with mixed reality. Virtual Reality Los Angeles (VRLA) will host its third annual expo in April, and this year's attendees will get to experience a fun Easter egg hunt sponsored by AfterNow and VRLA, in partnership with mixed reality king, the Microsoft HoloLens.

Disney Chairman and CEO Bob Iger has out and out rejected Virtual Reality (VR) as a component of any Disney Theme park. While Knott's Berry Farm, why-hasn't-this-chain-shut-down-yet Sea World (seriously, RIP Tillikum), and Six Flags have all invested in VR to help spice up their parks in this theme park depression period, Iger has "ordered his team not to even think about it." Iger instead is very much onboard the Augmented Reality (AR) train.

If maintaining privacy is an ongoing battle, the front line is your smartphone. Apple included several new security features in iOS 10, but at the same time, some of the best new functionality comes with potential privacy trade-offs that everyone needs to understand.

With most augmented and mixed reality devices, you wear a purchased headset and use it alone, in a place of your choice—but not this one. Ben Sax decided to reinvent the binoculars to create a mixed reality experience that anyone can walk up to and try for free. He calls it the Perceptoscope.

As Android's official app provider, the Google Play Store is packed with thousands of useful programs. But Google's terms of service is extremely restrictive, which means that countless apps simply don't qualify to be hosted on the Google Play Store.

It has become a popular and must-have beauty essential—the bath bomb. Not only does it bring an aromatic and calming feel to bath time, but it also leaves your skin soft and will make you smell wonderful for a whole week!

With an Android device, you can replace almost any default app with a third-party offering. Don't like your home screen app? Replace it. Tired of the text messaging interface? Upgrade it. The same can be said for Android's lock screen. But while many third-party lock screen apps are available, so far, only one has been designed with the Samsung Galaxy S6 and its fingerprint scanner in mind.

Aside from identifying songs with Shazam and using the "Hey Siri" feature while driving, Apple's personal assistant isn't something I regularly use on my iPhone.

The possibility of the Sriracha factory in Irwindale, CA being shut down was one of the biggest food stories of 2013. Huy Fong Foods was almost forced to close the plant due to complaints about the factory's smell, but luckily the brand emerged triumphant.

When subjects are asked to watch a movie and not display emotions (say, a comedy without laughing, or a tearjerker without crying), they evidently use up glucose in particular areas of their brain in a way that subjects who are free to react however they want do not.

Michael Faraday was awesome. He discovered electromagnetic induction, diamagnetism and electrolysis, and he invented the Bunsen burner (before it was the Bunsen burner). Because of his work, we can make suits that can withstand 1,000,000 volts of electricity and cases to protect our gadgets from nuclear attacks.

Knit blankets are comfortable and scream home and security, but they are expensive and making them is an arduous task. If you want to get started on a major knitting project, watch this video, and learn in general terms how to knit a blanket.

Take a look at this video and learn how to hack into a wireless Linksys router. This hack isn't applicable for all security enabled networks, only ones that use generic passwords.

SQL injection is a type of code injection that takes advantage of security vulnerability at the database level. It's certainly not the easiest form of hacking, but if you're serious about turning a website upside down then this is the way to do it.

The Thule Snug Tite hitch lock is for carrier to receiver security. This video shows you how it assembles first, then how the lock is applied to a bicycle rack.

This video demonstrates how to install or replace a dead bolt in your door. Having a dead bolt lock gives you a added sense of security, because it is more secure than just the lock on the door handle.

For a moment, picture a situation where you want to host some files or images, but you do not want it traced back to you. Perhaps you're working on a project with others and need secure data storage. Anonymity is the new shield of the 21st century—and you best protect yourself. As always here at Null Byte, we are trying to make that happen. Before someone can learn how to root a box, they need to learn how not to be found. I can not stress that point enough.

iPodTouchedMaster shows how one can easily SSH into their iPod Touch with all firmware! To SSH is the ability to hack into your iPod Touch's file system. First, your iPod Touch must be jailbroken. Next, you'll have to open Cydia. Click "Featured Packages" or search for the terms "Open SSH" (it will be listed under Console Utilities & Daemons). When you have OpenSSH click on it and click 'Install' and 'Confirm'. After this is finished, click return to 'Cydia'. This may take a lot of battery po...

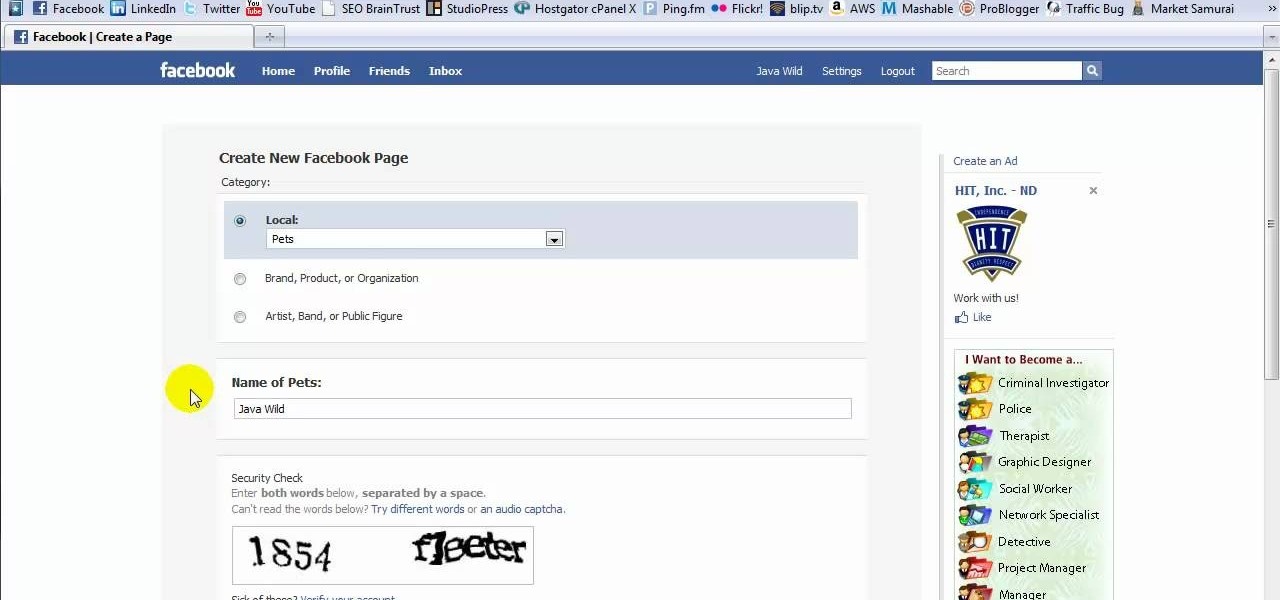
This tutorial is in response to mail to Facebook. Scott Wilde leads you through the process. You can start by creating a brand new profile page. In this case, Mr. Wilde created a profile page for his dog Java Wilde so he could have a fresh new page without having to alter his initial profile page. Fan pages are different than your base profile. Your base profile is not indexed, it is not public, it is private and limited to 5000 friends. A fan page is unlimited up to millions of fans and it c...

This video is a step by step guide for creating exposed teeth makeup . This is loosely based on the Harvey Dent character from Batman: the Dark Knight.

Reduce your chances of becoming the seatmate everyone hates by learning how to head off a screaming jag.

Research shows that color can have a powerful effect on our emotions. Start harnessing that power today. Watch this video to learn how to improve your life with chromotherapy.

This video includes instructions on how to get your PlayStation Portable (PSP) onto the BGSU wireless network.

Wade Bourne, host of Wade's World Hunting at MyOutDoorTV, shows you how to create a "path of least resistance" for deer this season. Let's face it: deer can be pretty stupid. With a little leg work, you can trick your deer into going exactly where you want them. Hunting your prey will be a snap!

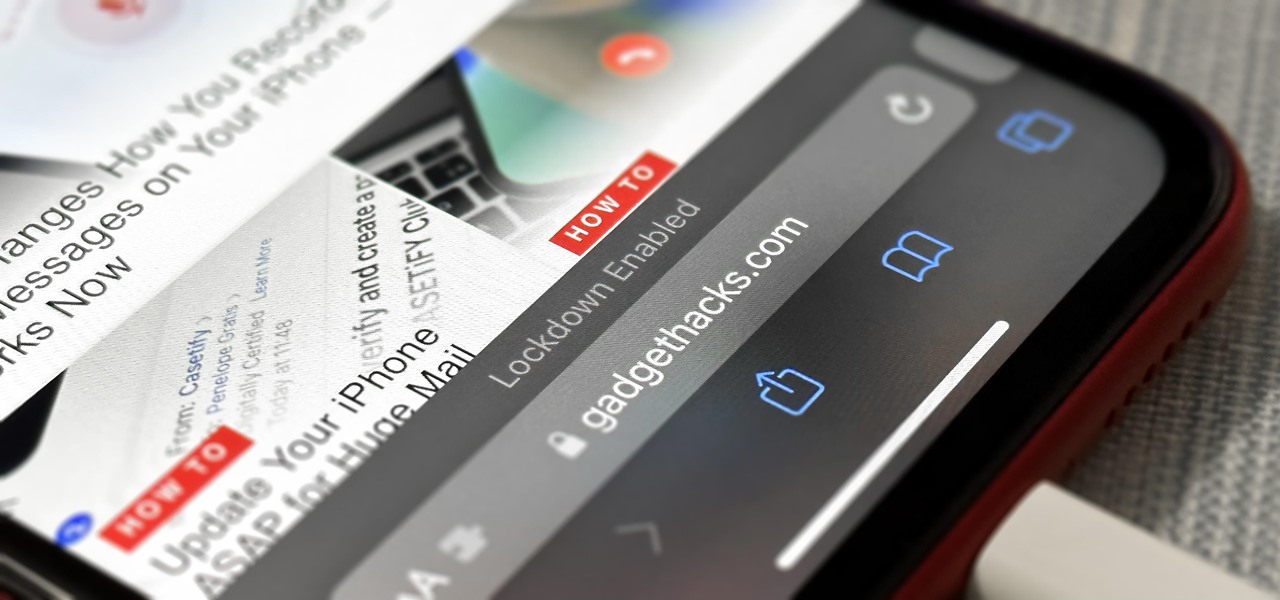
If you think you might be a likely target of a black-hat hacker, there's a new iOS security feature that offers extreme protection for your iPhone against spyware, phishing attempts, and other highly sophisticated cyberattacks.

The Internet of Things (IoT) is changing everything in our homes and at work, from security systems and lighting fixtures to smartphones and speakers. An estimated 50 billion devices are now hooked up to IoT.

It is well documented that what you say and do online is tracked. Yes, private organizations do their best to protect your data from hackers, but those protections don't extend to themselves, advertisers, and law enforcement.

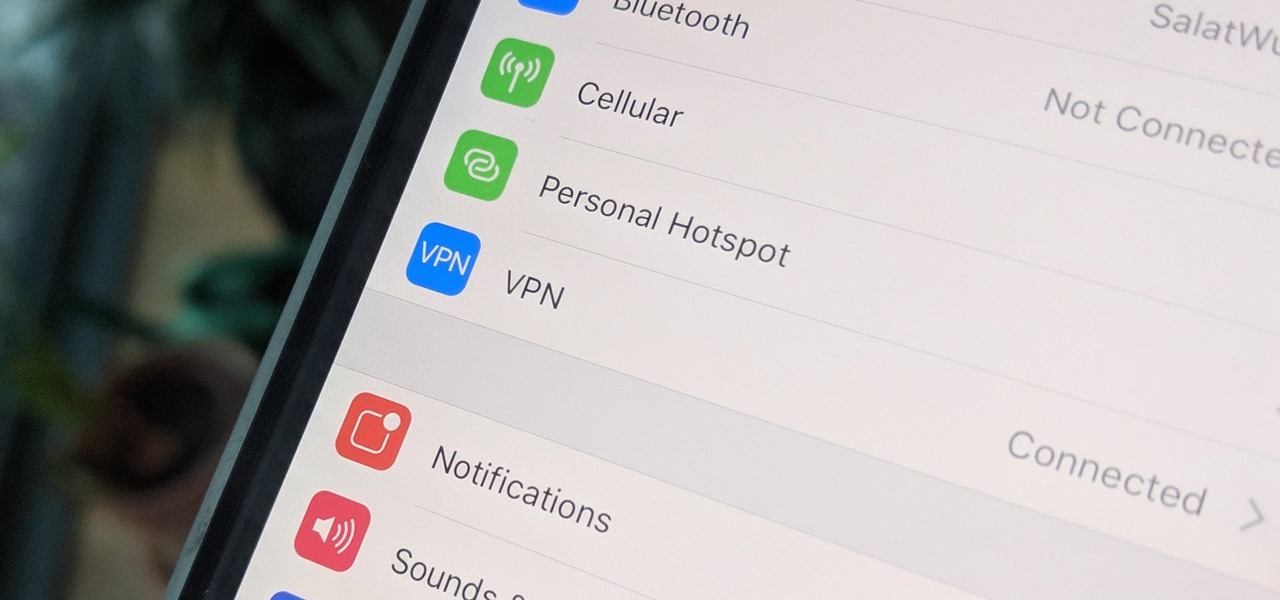
A virtual private network is a necessary part of your arsenal if you're insistent on surfing the web privately and securely on your iPhone. The App Store is littered with hundreds of different VPN services that encrypt traffic and mask your IP address, but what they all have in common are connectivity issues.