Short Url Search Results

How To: Snorkel
If you love the ocean and love swimming, it's time you step up to the next level… snorkeling. Snorkeling is one of the best ways to explore the underwater life, without fancy equipment or expensive training. And all you need is a snorkel. If you want a better look at what’s underwater, all you have to do is snorkel.

How To: Get a Bollywood bride inspired makeup look
Feeling a little Bollywood? Misschievous shows you how to do a look inspired by Bollywood artists and brides. You can achieve the look by following these simple steps! 1. Apply a copper tone eyeshadow on your lid. Sharpen the edge and go light as you bring it inwards. 2. Define the edge by applying a Cranberry tone eyeshadow following the shape of the edge and buffing it out as you go up to the crease. 3. Using a darker shade like Mac's Beauty Mark, draw a semi-V shape following your crease. ...

How To: Make a mini uzi out of paper
Learn to make this easy mini paper Uzi gun for gaming with your friends! Supplies: Scissors, Scotch tape (Note: DO NOT USE MASKING TAPE OR DUCT TAPE; IT WILL NOT TURN OUT WELL), lots of paper. 1. Take one piece of paper and roll it up from top to bottom to make a short tube. Tape it. 2. Take another sheet of paper and do the exact same thing that you did to the first one and tape it as well. 3. Take a sheet of paper and roll it up from side to side (long ways). Make the hole in the middle abo...

How To: Design for pants and bottoms
Tips for fashion design and illustration, including flare legs, jumpsuits, skirts, skinny legs, and city shorts. Design fashion for pants and bottoms in this fashion illustration video series with a fashion designer.

How To: Practice squash serving drills and return to the T
Don't let your teammate suck the fun out playing squash. Watch this how to video tutorial and learn twelve different serving drills. These fancy serving drills are sure to impress your squash buddy.

How To: The Simplest Way to Remove the Background from Photos on iOS, iPadOS, and Android
It's super easy to add filters, adjust levels, and crop images using the default photo editor on your smartphone, but there's rarely any built-in tool for removing the background in a photo. A third-party app can help isolate people and objects in your pictures, and we've found a free one that's easy to use, works with high-resolution images, and is available for Android, iOS, iPadOS, and the web.
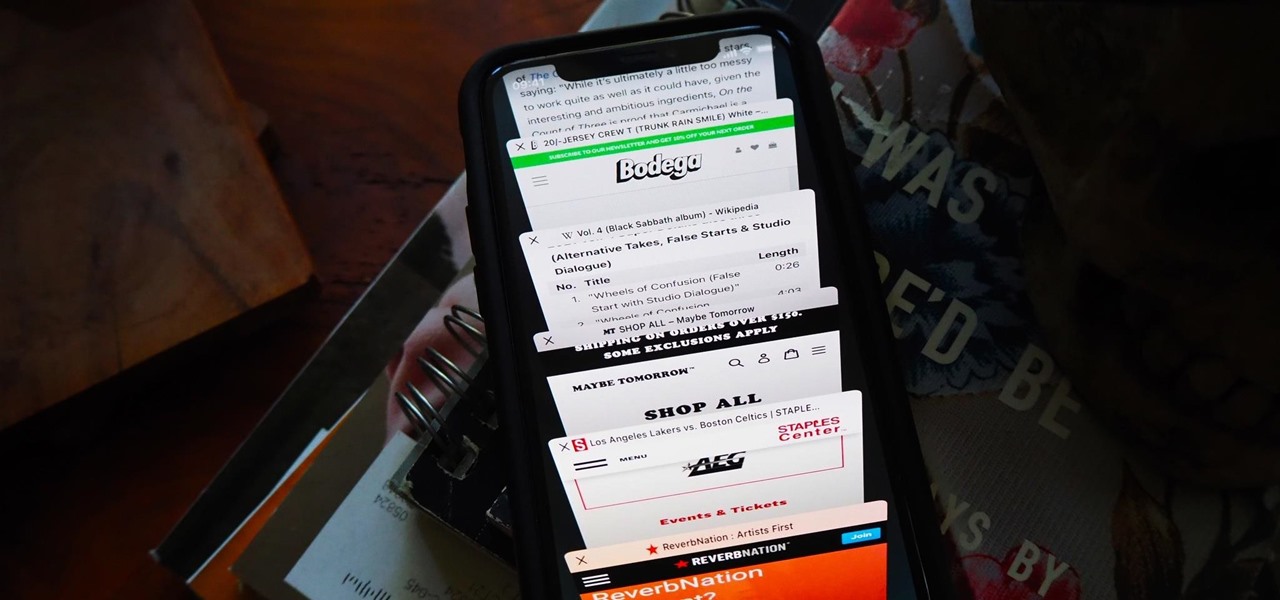
How To: You're Searching Your Safari Tabs Wrong — Use This Hidden iPhone Trick to Find Them Faster
I am constantly hitting Apple's limit of 500 open tabs in Safari on my iPhone, so it's safe to say that I have way too many tabs to sort through. With that many tabs open in the browser, it can be impossible to track down the one needed at any given moment. If that sounds like you, stop browsing tab after tab to locate the right one because there are hidden tricks to searching those tabs that make it easy.

How To: The Easy Way to Upload Files Anonymously from Your iPhone So They Can't Be Traced Back to You
If you need to share something online but don't want your personal information attached to the file, use an anonymous file hosting site. By uploading files anonymously, you keep your IP address safe and won't need to create any kind of account that could provide further logging. You can do this in a web browser, but it's much easier to do using a shortcut on your iPhone.

How To: Can't Find Episode Notes in Apple Podcasts? Here's How to Unlock Them on Your iPhone
Many podcasts you come across will tell you to check out the episode notes for information and links about whatever that show's topic is. Easy enough, unless you're using Apple Podcasts, where these episode notes don't appear to be anywhere at all. Luckily, they're just hiding in plain sight.
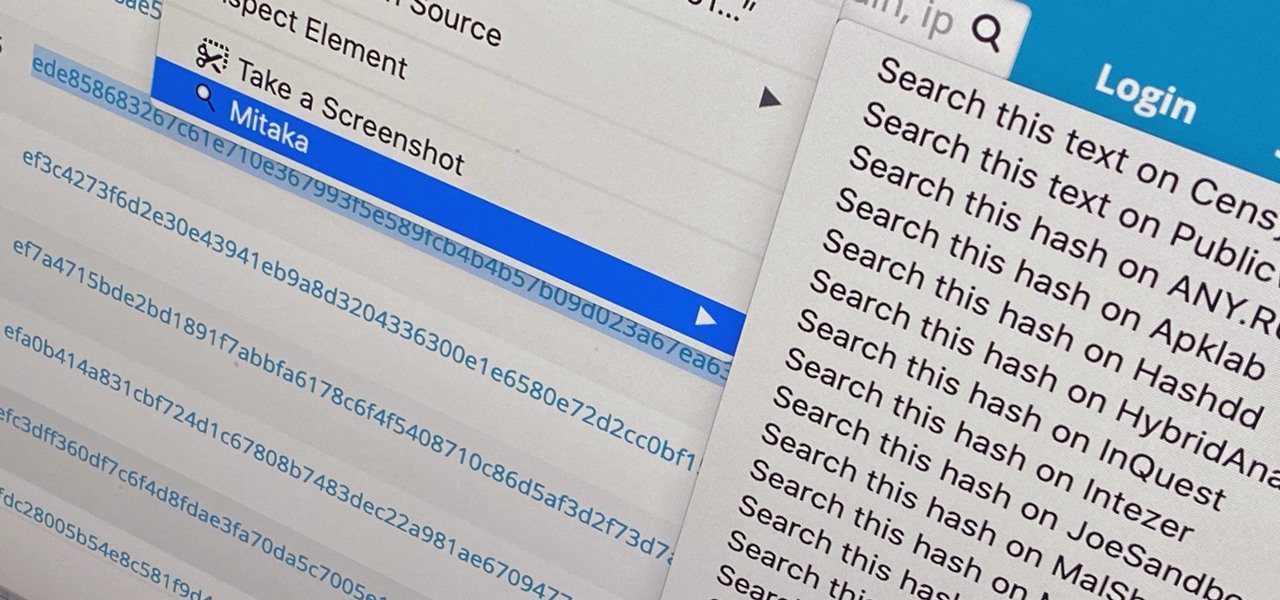
How To: Use Mitaka to Perform In-Browser OSINT to Identify Malware, Sketchy Sites, Shady Emails & More
Web browser extensions are one of the simplest ways to get starting using open-source intelligence tools because they're cross-platform. So anyone using Chrome on Linux, macOS, and Windows can use them all the same. The same goes for Firefox. One desktop browser add-on, in particular, makes OSINT as easy as right-clicking to search for hashes, email addresses, and URLs.
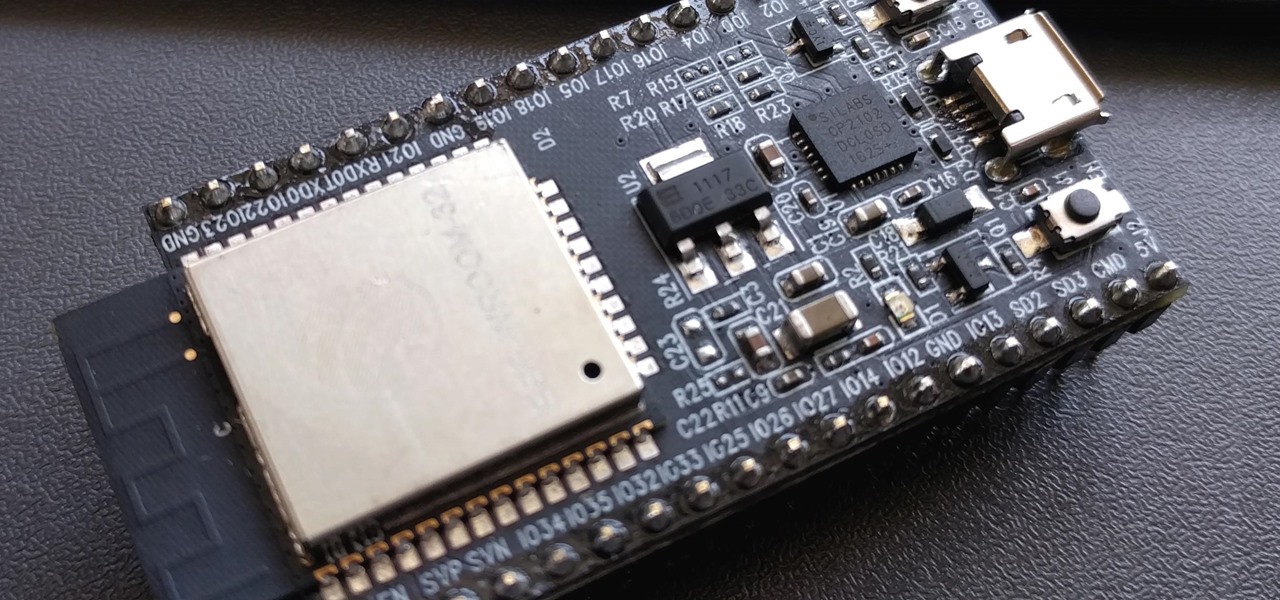
How To: Enable Offline Chat Communications Over Wi-Fi with an ESP32
PirateBox is a great way to communicate with others nearby when cellular and Wi-Fi networks aren't available. With it, you can anonymously share any kind of media or document and even talk to one another by voice — without being online. However, it needs a Raspberry Pi, which is more expensive than ESP32 boards, and if you only need a text-based chat, there's a much simpler option.
How To: Here's What That 5G+ Icon in Your Status Bar Really Means
When you look at the top corner of your phone, what do you see? Upon upgrading to Android 11 or iOS 14, you'll see either "5G," "5G+," or "5G E" if you're connected to the right network. But what exactly do these symbols mean? They indicate not only if you're using 5G, but also what type you're connected to.

How To: Change a Phone's Coordinates by Spoofing Wi-Fi Geolocation Hotspots
In many urban areas, GPS doesn't work well. Buildings reflect GPS signals on themselves to create a confusing mess for phones to sort out. As a result, most modern devices determine their location using a blend of techniques, including nearby Wi-Fi networks. By using SkyLift to create fake networks known to be in other areas, we can manipulate where a device thinks it is with an ESP8266 microcontroller.

News: Now's the Perfect Time to Brush Up on Your Excel Skills
We've become accustomed to new models of learning over the past generation. What once required classrooms and chalkboards now only needs a laptop and an internet connection. At this moment, with much of the population staying inside, eLearning has never been more necessary than now.

How To: Use This Zoom Hack to Make Everyone Think You're Still in the Video Meeting When You're Not
It's OK to want an extended break when you're working or learning from home. Maybe you want to play a video game, spend more time with your family, hang out with your dog, or FaceTime with friends. But how can you do that when you're supposed to be in a Zoom video conference or class? Thanks to one Zoom feature on your iPhone, it may be easier than you think.
How To: Access the US Government's Coronavirus Testing Website Without a Computer
On March 13, President Trump announced during a briefing in the Rose Garden that Google was building a COVID-19 screening website to help Americans understand if they might have the new coronavirus. If likely infected, the site would also include the location of a local drive-through testing site to visit. So how can you access the screening website?

News: BBC Earth Releases 'Micro Kingdoms: Senses' Insect Experience on Magic Leap 1
As first reported by Next Reality last year, game developer Preloaded, in partnership with BBC Studios, has finally launched BBC Earth - Micro Kingdoms: Senses.

News: Disney's Alternate History Series 'Motherland: Fort Salem' Uses Snapchat AR to Give You Magical Powers
Alternate US history is the go-to move for hot new cable and streaming shows, from HBO's Watchmen to Hulu's The Handmaid's Tale, reimagining how things might have turned out is an endless well of narrative inspiration.

How To: The 4 Best Password Managers for iPhone
Using a strong password is critical to the security of your online accounts. However, according to Dashlane, US users hold an average of 130 different accounts. Memorizing strong passwords for that many accounts is impractical. Fortunately, password managers solve the problem.

News: UK Wireless Giant Three Promos 5G for AR, VR, & Smartphones with Wild Sci-Fi Video That's Better Than Some Movies
The entire wireless industry is working overtime to convince the world that 5G, and the higher prices associated with the faster speeds it affords, will not only be worth it but will deliver never-before-seen wonders. But few companies have produced such a stunningly well-done sales job as Three, one of the leading wireless giants in the UK.

News: The Galaxy S20, S20+ & S20 Ultra Are IP68 Water-Resistant — Here's What That Really Means
Samsung's new line of Galaxy S20 flagships have a water resistance rating of IP68. This means you don't have to worry as much about getting the phones wet, but there's a limit to that.

News: Nreal Pauses Smartglasses Production as Coronavirus Issues Impact China, Amazon, Facebook, Intel, & Nvidia Exit MWC
The deadly Wuhan coronavirus outbreak has not only has claimed lives in China but also has caused disruption around the globe, particularly in the tech industry. To date, the virus has claimed more than 1,000 lives in China, according to the country's officials.

News: Apple Just Released iOS 13.4 Public Beta 1 for iPhone, Includes New Memoji Stickers & More Convenient Mail Tools
After the lackluster update that was iOS 13.3.1, we beta testers were in need of some excitement. Thankfully, Apple delivered the goods with iOS 13.4 developer beta 1, introducing fun new features like fresh Memoji stickers and a new Mail toolbar. Of course, that update was for developers only, so we public testers are thrilled that Apple just released the first public beta today.

How To: Everything You Need to Know About Pinning a Tweet
Pinning a tweet is a great way to get the point across because it's the first post people see when they visit your Twitter profile. When you pin a tweet, reply, or retweet, it sticks to the top of your profile, whether you create new tweets or not. It's the perfect spot to place one of your more popular tweets, a fantastic blog you wrote, or even just a joke that shows your personality.

How to Hack with Arduino: Building MacOS Payloads for Inserting a Wi-Fi Backdoor
Arduino is a language that's easy to learn and supported on many incredibly low-cost devices, two of which are the $2 Digispark and a $3 ESP8266-based board. We can program these devices in Arduino to hijack the Wi-Fi data connection of any unlocked macOS computer in seconds, and we can even have it send data from the target device to our low-cost evil access point.
How To: Customize Spark for Android Notifications with Lights, Sounds & Vibrations
Android is all about customization. That's why it's entirely appropriate that Spark for Android's newest update adds a ton of customization options for your out-of-control email alerts. Now, you can add lights, sounds, and vibrations to notifications, and you can even set specific settings for all of your email accounts.
How To: Block Ads in Games on Your iPhone for Distraction-Free Gameplay
No one likes in-app advertisements, especially in mobile gaming, but they're necessary because they offer developers a way to make revenue without having to charge you to play. In some games, in-app purchases give you the chance to remove ads, but what can you do about apps that don't offer the option to kill ads?
News: 8th Wall, Amazon Sumerian & Trigger Team Up to Deliver Web AR Promotion for 'Jumanji' Movie Sequel
Augmented reality already seemed like the ideal technology to advertise for a movie based on the premise of being sucked into a video game world the first time around. For the sequel, how about two times the immersion?

How To: Identify Missing Windows Patches for Easier Exploitation
No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.

News: Hello Kitty Challenges Pokémon GO's Reign as Top AR Game with Kawaii World
After three years and change, no one seems to be able to knock Pokémon GO off its augmented reality throne. Zombies, dinosaurs, and ghosts have all met defeat at the hands of the pocket monsters. Heck, not even the world's most popular wizard and Pokémon GO's developer can replicate the original's success.

How To: Find Passwords in Exposed Log Files with Google Dorks
You may not have thought of dorks as powerful, but with the right dorks, you can hack devices just by Googling the password to log in. Because Google is fantastic at indexing everything connected to the internet, it's possible to find files that are exposed accidentally and contain critical information for anyone to see.

News: The Second iOS 13.2 Public Beta Is Out, Includes New Emoji, In-App Camera Settings & More
We public testers are in luck. Today, Apple released the second developer beta for iOS 13.2. As is the case with most beta releases, developers get theirs first, while public testers are left waiting. Will we get our update the same day, or will we need to wait? As it turns out, Apple decided to throw us a bone. The second public beta for iOS 13.2 is officially here.

News: Harry Potter Fans Can Now Summon a Wizarding World Sorting Hat in Augmented Reality
If you need to know whether you are really a Hufflepuff or a Gryffindor, then it's time to get yourself an augmented reality sorting hat.

News: ThirdEye Gen X2 Smartglasses Take Aim at Military Applications with AR-Enhanced Weapons Sight
Following on the heels of the announcement that ThirdEye's Gen X2 MR glasses began shipping in September, ThirdEye has revealed it has developed an app that helps soldiers aim their weapons during battle situations.

How To: Disable Bloatware for Free on Your Galaxy Note 10 or 10+
You may have noticed your Note 10 came with quite a bit of bloatware. Even the unlocked version of the phone comes with Facebook preinstalled, and if you bought it from a carrier, it's much worse. Luckily, there's a way to remove any apps you don't want, and you don't need root or a paid app to do it.

How To: Scan Websites for Interesting Directories & Files with Gobuster
One of the first steps in attacking a web application is enumerating hidden directories and files. Doing so can often yield valuable information that makes it easier to execute a precise attack, leaving less room for errors and wasted time. There are many tools available to do this, but not all of them are created equally. Gobuster, a directory scanner written in Go, is definitely worth exploring.
News: Google Challenges Apple's iPhone X Series with Face Unlock & Air Gestures on Pixel 4
It's been almost two years since Apple added the TrueDepth depth-sensing camera of the iPhone X for Face ID and Animojis, but now Google is ready to upgrade the front-facing camera on its Pixel series.
News: Vuzix Blade Augmented Reality Smartglasses Add Real-Time Language Translation via Zoi Meet App
Next to map data overlays, one of the most often discussed concepts for apps that could propel augmented reality smartglasses into the mainstream is a real-time language translation app.

News: Intel Makes Augmented Reality Production More Accessible with Affordable New RealSense Standalone Depth Camera
For developers and makers getting started with augmented reality, Intel is lowering the barrier to entry for its RealSense line of sensors.

