A long time ago, we recommended the Hover Zoom extension for Chrome as an easy way to blow up small image thumbnails without actually have to "click" on the images themselves. Over the past year, there have been reports that Hover Zoom now collects and sells your browsing data to third-party advertisers without your consent.

Welcome back, my greenhorn hackers! In a previous tutorial on hacking databases, I showed you how to find online databases and then how to enumerate the databases, tables, and columns. In this guide, we'll now exfiltrate, extract, remove—whatever term you prefer—the data from an online database.

Welcome back, my budding hackers! In my continuing series on Linux basics for aspiring hackers, I now want to address Loadable kernel modules (LKMs), which are key to the Linux administrator because they provide us the capability to add functionality to the kernel without having to recompile the kernel. Things like video and other device drivers can now be added to the kernel without shutting down the system, recompiling, and rebooting.

Welcome back, my rookie hackers! When Wi-Fi was first developed and popularized in the late '90s, security was not a major concern. Unlike wired connections, anyone could simply connect to a Wi-Fi access point (AP) and steal bandwidth, or worse—sniff the traffic.

Welcome back, my hacker trainees! A score of my readers have been begging for tutorials on how to hack Wi-Fi, so with this article, I'm initiating a new series dedicated to Wi-Fi hacks. This will probably be around 6-9 articles, starting with the basics of the technologies. I can hear you all groan, but you need to know the basics before you get into more advanced hacking. Then hopefully, developing your own hacks.

Those of us who lived our childhood through the '90s remember the rapid advancement of console gaming. From the Nintendo to Game Boy to Dreamcast to PlayStation, we were consistently greeted with newer and better technology on a year to year basis.

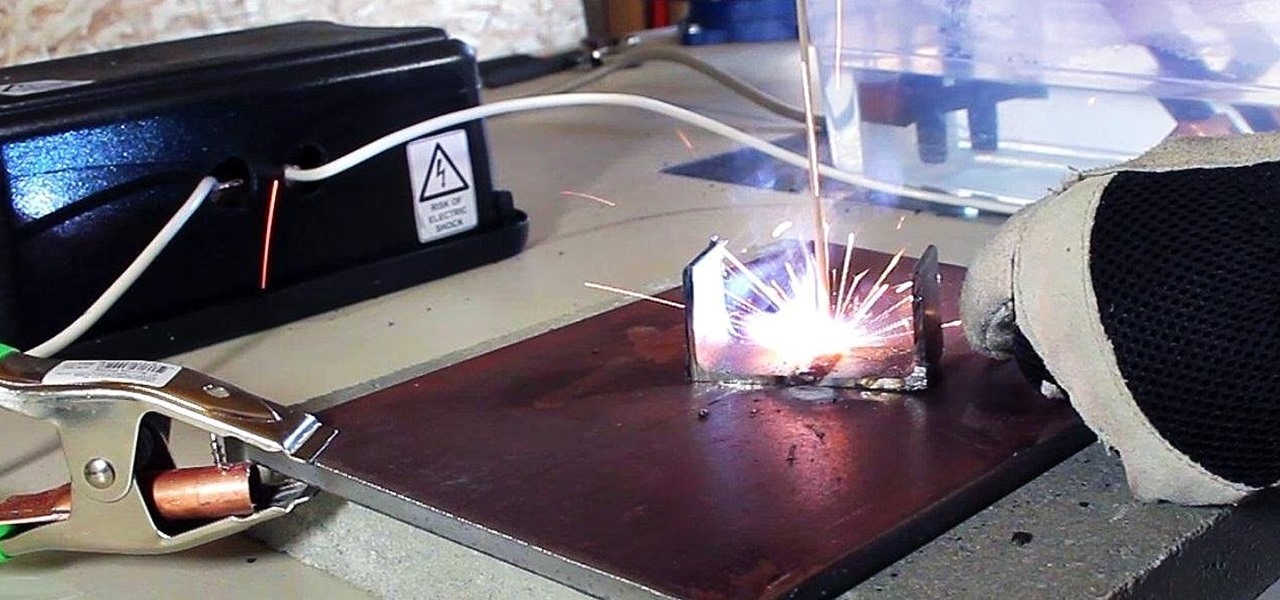
In a previous article, I demonstrated an Arc Welder made using parts from old microwave ovens. Video: .

If you're an avid PC gamer, then you're probably well familiar with the term overclocking, which is basically just tweaking your computer hardware to run faster than it was originally intended.

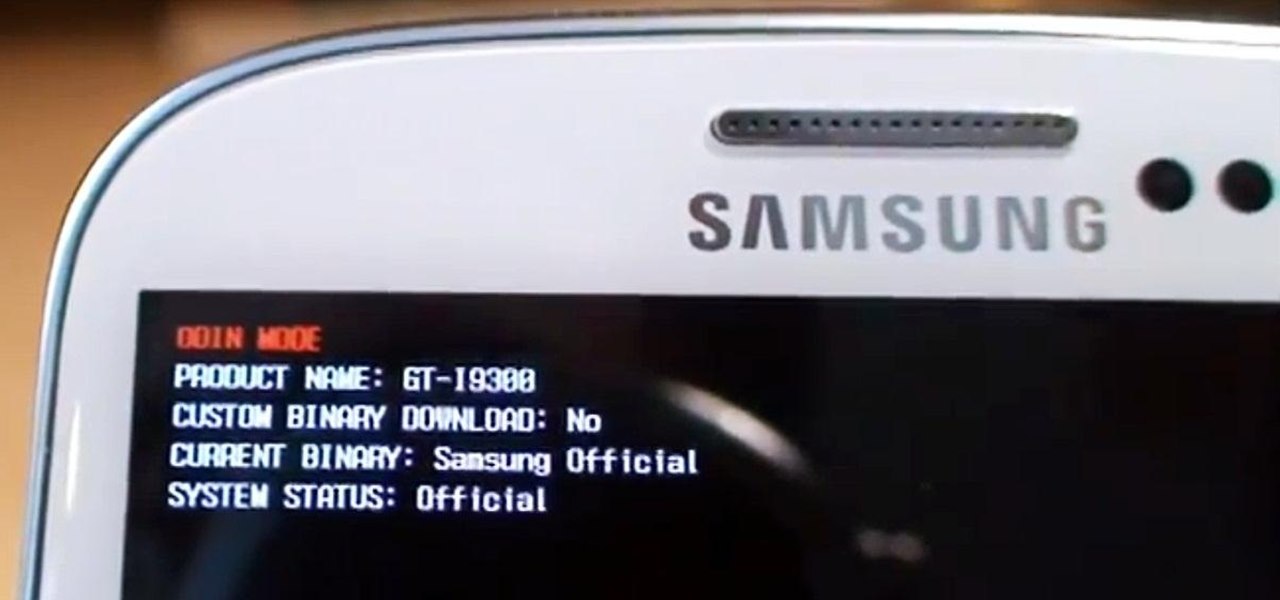
Need root on your Samsung Galaxy S3? Phone not getting the Jelly Bean update? Stuck on the Samsung screen? Phone bricked? Need to restore back to stock? Odin can help!

As practically the entire Steampunk world knows by now, IBM has predicted that Steampunk will be the big new trend from 2013 to 2015. They based this prediction on their computers, which sift through broad swathes of the internet in order to see patterns that may help commercial industries. According to them, Steampunk has been on the rise for the last few years, and they predict that it will explode into peak popularity within the next two years. But what does that mean and how will it impac...

It might be time to move those Instagram photos to another service. It seems that Instagram has never heard of the phrase, "If it ain't broke, don't fix it." In a very big WTF moment, the extremely popular photo sharing and editing app decided that it has the right to sell its users photos to third parties without pay or notice. Yep, you heard that right. That photo you took of your girlfriend laying out on the beach could be in the next stupid Corona commercial without your consent and witho...

MAC addresses (not to be confused with Macs) are unique identifiers assigned to network devices in order to access the internet. Hotels use these Mac addresses in order to check if a registered patron has agreed to their terms and conditions, how much bandwidth is being consumed, and of course, whether they've paid or not.

If you want to make clothes for your cat, you're on your own. As I recently said in this article, cats will just totally flip out if you make them wear things. Your dog may also flip out, but I've found them to be more tolerant, personally.

When I left off on our last hack, we had hacked into the ubiquitous Windows Server 2003 server by adding ourselves as a user to that system so that we can return undetected at any time. The problem with this approach is that a sysadmin who is on their toes will note that a new user has been added and will begin to take preventative action.

Welcome back, hacker novitiates! In the next few hacks, we will be breaking into Windows servers. In this installment, we will learn to add ourselves as a user to a Windows 2003 server. Of course, when we have added ourselves as a user, we can come back any time and simply log into our account without having to hack into the system and risk detection.

I'm not admitting to anything, but let's be honest, most of us download content on the Web from time to time. With copyright holders laying down the law more and more often, it can't hurt to do so with caution. And even if you aren't downloading copyrighted material, you still don't want companies snooping in on your online activities. So just how do you protect yourself when torrenting? Avoid "Open Communities"

From A Hamburger Today: your guide to regional hamburger and cheeseburger styles. What red-blooded American doesn't love hamburgers? Think you're an enthusiast? Think again. There's more to the burger than the Big Mac (though the Big Mac is included in this guide, of course).

According to Amazon.com, Kindle was their best-selling item this year, which means many, if not all of you are playing with a brand new Kindle on Christmas Day. Of all of Amazon's Kindle models, the Kindle 3 (6") will be the most common eReader in everyone's hands, either the Wi-Fi version or the 3G model.

There are some basic tips that you will need to know in order cook over various types of campfires. Hazel wood is a good wood to use, because it is a quick growing wood. Make a tripod with 3 wood posts and copper wiring. You will also need 2 hook sticks. Reserve them, when you are scavenging for wood for your fire and your tripod. These will be useful tools.

Read palms for success in the hand. To focus mainly on business or workplace look to the mound of Jupiter, which should be prominent. Additionally, the first finger should be longer. A longer first finger is as long as the third finger. This shows someone who is ambitious, connected with work, and authority over others.

There’s so much you can do with a shoe. Be it the house in a fairy tale or just on the foot of a man, you will want to know how to sketch a good shoe. Keep on practicing and try giving your shoes a little wear-and-tear character.

Is there a black or yellow mustache stripe? This is just one of the physical characteristics you will need to know to determine what kind of meadowlark you are looking at. Take a minute to enjoy the outdoors while identifying the distinct sound, look and location of meadowlarks.

It might seem like an inconvenience but it is important to take the time to find out what has caused your oil light to come one in your car. You may just be low on oil or you may have a more serious problem but ignoring the warning will only lead to further damage.

A bouquet of roses is a lovely thought but will quickly wilt and die. Give your loved one a bouquet of roses that will last for years to come and it will only cost you the price of a pencil and paper. They’re quick and easy to sketch.

Bird watching is a great activity to do on your own or to spend time with the whole family. Look for the habitat, coloring, behavior and call of this beautiful bird and enjoy its beauty and soft cooing.

Are you wanting to improve your tennis game? Is your footwork a problem when trying to get to those short balls? Get tips on improving your footwork from a professional tennis instructor in this free sports video series.

Watch this how to video to learn how to make Malfouf, or what is also known as stuffed cabbage is. For this recipe you will need:

In this video series, our expert Jay Golden will teach you how to putt and improve your short game. Having a great drive like Happy Gilmore doesn't mean you know how to get that ball in the hole. Jay will show you what to do when stuck in the sand, when your ball rolls down the green to the rough, or when your ball is just inches from the green and you can't decide what's next.

In this short series, Nathan shows you everything you need to know about changing wiper blades. He shows you how to know when they need to be replaced, how to choose an new blade, how to install them and how to fix them.

Well, why aren't you? They're all the rage in pop culture right now, what with The Avengers blowing away audiences and the finale to the Batman trilogy coming out soon. Not to mention that Marvel is remaking Spider-Man! The original is only like, what, less than ten years old? Jeez. Now, I know what you're saying, "But, Henry! Comics are for nerds! We're waaaay cooler than that!"
The Power of One is one of those books that I really should have read years ago. I’ve certainly meant to read it for a long time so this was a satisfying title to cross off my list. It’s stunning that this was Bryce Courtenay’s first novel. I look forward to reading his others because if this is where he started, he’s a talented writer.
I read Timothy Keller’s The Reason for God on the recommendation of a philosophical friend and before I had finished it I was adding Keller’s The Prodigal God to my list of books to read. Keller has a gift for succinct and wise writing. I believe he truly has his finger on where society currently is spiritually, and where it might be going. In The Reason for God, Keller says that our society is both more spiritual and more secular than it has ever been. The book is a great look at the Christi...

Around the world, X-People (yes... there are X-Women, too) are under attack from an intolerant sapiencentric ruling class. Integration without equality is a farce. Autonomy is denied outright. Human prejudice cannot abide a mutant state. Human fear, born to hate, imposes itself on the life of every mutant.

Cryptography is a quintessential part of computer security in the modern world. Whenever you buy something on eBay or log into Facebook, that data is encrypted before it's sent to the server in order to prevent third parties from eavesdropping and stealing your sensitive information.
Author's Note: Hi there, some of you may know but most of you probably won't. My name is Semeria and I am an author on the rising. I plan to be posting one of my novels on this website for people to read. Comment and let me know what you think and I hope you enjoy the story.

In each day of our life, we see inflammation. We see it during sore throats and abscess formations in our bodies, and even slight tooth pain is a form of inflammation. Sometimes it's good when it fights to protect us from invading organisms, but sometimes it becomes bad when it occurs in inappropriate ways, like acne.

In this article, I'll show you how to make a portable prank stun-baton. Powered by static electricity, simply charge up the baton, and discharge it for a static surprise. The concept behind this device ties in with Leyden jars, and their tendencies to retain static electricity.

As per Alex's request, I am posting about generating word-lists in Python. However, this is my FIRST attempt with Python, so please provide me with critiques and any and all comments. I really want to know what you think as there was a little bump here and there seeing as I am transitioning from C#.

We're officially seeking Null Byters on a weekly basis who would enjoy taking their time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (if up to par, of course). This is a job meant for anyone with the will to share knowledge. There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials...