The Force was awakened in many a household on Christmas morning this year, as evidenced by numerous recipients of newly unwrapped Star Wars: Jedi Challenges systems sharing their first lightsaber battles in augmented reality on social media.

Avoid an ambush and detect what's available in a given star system! You'll need to learn how to use probes to scan the surrounding area if you want to do a lot of exploring in EVE Online. This video shows you how to set up your probes and execute the scanning function.

As an adult you will come a cross a point in time when you need to make the right impression by writing a formal letter. Follow the format and you will be able to be most effective at conveying the information in your letter.

Play drums using basic beats and time signatures, different equipment and musical styles like jazz, funk and rock; learn how from our professional drummer this free drum tutorial video series.

Play drums using basic beats and time signatures, different equipment and musical styles like jazz, funk and rock; learn how from our professional drummer this free drum tutorial video series.

In this video series, watch as computer expert Gary Zier teaches how to design a graphical business card in Photoshop. Learn how to apply effects and text, how to create masks, and how to resize images in Photoshop. Get tips on how to save a business card as a signature in your email.

In this advanced drumming video series, learn tips and techniques to improve your drum playing ability tenfold. Our expert will demonstrate single and double stroke techniques, how to play quads, how to do flams and paradiddles, how to play eighth note triplets, crossovers, how to increase your speed between drums, how to play odd time signatures—and more important drum tips.

In these music lessons on video with Bill Macpherson, learn what equipment you need to sound like a blues guitar hero. Get tips on what amplifiers to play through, and what electric guitars work best for that smooth, warm signature blues guitar tone. Find out what amp settings work well for drive and reverb, and learn what an effects pedal might offer you for a grittier, more distorted sound. Watch these videos and learn how to continue one of the richest living musical traditions we have today.

In this instructional video series, learn how to read piano sheet music for yourself. Our expert will walk you through a step-by-step tutorial that covers such basics as which notes to play with which hands, what key signatures mean, how to interpret the rhythm of the song, and how to sight read without knowing the song.

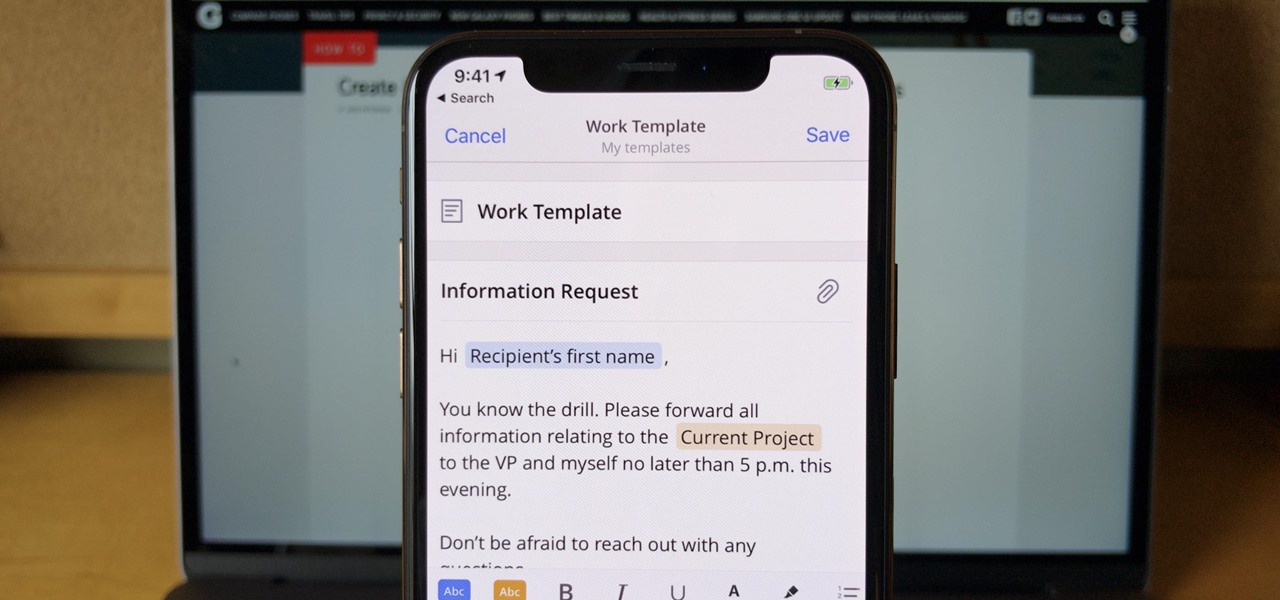
If you find yourself emailing the same email over and over again with just a few changes such as new addressees, or if you're constantly replying to messages with the same response, typing it out every time is, well, a waste of time. Spark, a third-party email client for mobile devices, takes all the work out of this — no matter which email account you need it for.

The rise and fall of Meta, the Silicon Valley-based augmented reality startup that looked to challenge the likes of Microsoft's HoloLens, and others, took just six years.

The LG G6 was officially announced by LG at Mobile World Congress 2017 in Barcelona and released in the US on April 7, 2017. The device is almost exactly what we've been expecting from all of the rumors and leaks building up to its release. The modular design we saw in the G5 is gone, taking the removable battery with it. However, we do gain waterproofing, an improved dual-camera setup, a larger screen with smaller bezels, and Google Assistant.

It seems like every day now that we see a new headline on a cyber security breach. These headlines usually involve millions of records being stolen from some large financial institution or retailer. What doesn't reach the headlines are the many individual breaches that happen millions of times a day, all over the world.

Many of my aspiring hackers have written to me asking the same thing. "What skills do I need to be a good hacker?"

I love cryptography. It is like a great gigantic puzzle for me to solve. However, it is more important than that. It is also how we keep secrets safe. Not just sorta safe either, but really safe.

You're on your computer a lot, so it only makes sense that you download the best apps and software for it. The Official Cyber Monday Mac Bundle Ft. Parallels Pro & Luminar 4 is available for only three weeks at an additional 40% off the sale price of $69.99. Just use the promo code CMSAVE40 at checkout.

Over the last few years, Apple has significantly improved and scaled up your iPhone's ability to edit photos. Using the Markup feature, which was introduced back in iOS 10, you can add doodles, highlights, important text, your signature, and arrows and other objects onto pictures and screenshots. One of the lesser-known tools in Markup lets you zoom into essential details without cropping.

The results of Microsoft's $480 million contract with the US Army are on display and users continue to test the suped-up version of the HoloLens 2.

After closing its office last year, enterprise AR company Daqri has moved on to the final stage of its lifecycle with the liquidation of its assets.

It's new phone season — new handsets are releasing every few weeks, we're seeing endless software updates, and the holidays are right around the corner.

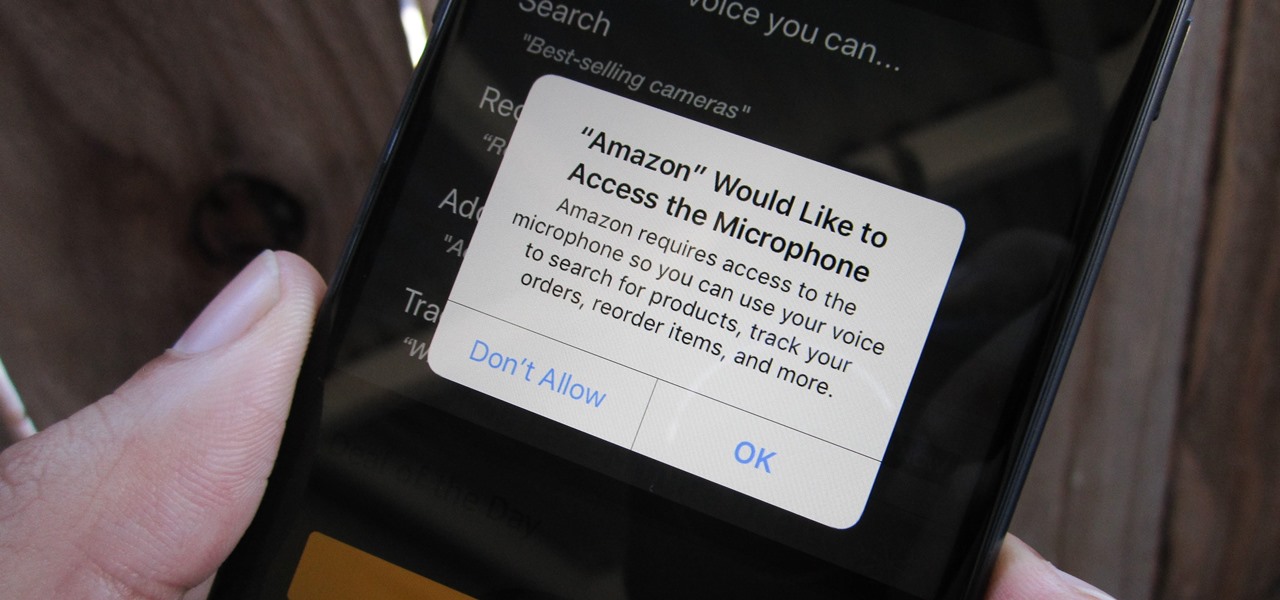
Any app on your iPhone could potentially listen in on your conversations and use that information to target you with tailored ads. Although most companies, including Facebook and Apple, have come out and vehemently denied these claims of spying on consumers, who's to say they're telling the truth? The only way to be sure you're safe is to take matters into your own hands.

Last year, OnePlus released not one but two excellent flagship devices with the OnePlus 5 and 5T. While the 5T released sooner than expected, it brought some worthwhile upgrades, such as a near bezel-less display and a much-needed camera enhancement. Now, that the OnePlus 6 has arrived, it's time to see what OnePlus has in store for 2018.

The Guardians of the Galaxy have to be the most fun superhero team to have at a Halloween party. They dance, they break the rules, and they definitely have the grooviest music. So the Guardians are a great bunch to pick from for your Halloween costume — or even for a themed group costume. Just imagine the badass vibe when you all walk into a venue together with Star-Lord blasting "Cherry Bomb" from a portable speaker. Here's a roundup of some of the best Guardians of the Galaxy costume guides...

This Halloween, Belle costumes will be out in full force as devoted Beauty and the Beast fans represent the tale as old as time. Not only was the live-action version of the animated classic the top-grossing film of 2017 (so far), it's also likely to be a contender during awards season. If you're too swept up in all things Beauty, then a Belle costume may just be the look for you this Oct. 31.

Love is the spice of life — it is also the microbes that couples share through sickness and in health, through the bathroom and in a hallway.

While restaurants and classrooms have enacted policies banning cell phones, one father has had enough of his kids' obsessive phone habits. Dr. Tim Farnum is now seeking to ban the sale of smartphones to children under 13.

No one ever said you had to be a culturally-relevant pun for Halloween, you know—or a scantily-dressed version of the inmates from Orange is the New Black.

From vodka to beer, booze is great for drinking, great for mixing, and, yes, great for cooking with. But there's really no alcohol better for bringing into the kitchen than wine. From savory dishes to sweet ones, wine is so versatile that it can make almost any meal better. And contrary to popular belief, it's easy to cook with.

Chris' Outrageous Cheesecake, a decedent combination of chocolate cake, brownies, cheesecake, and coconut-pecan frosting, is easily one of The Cheesecake Factory's most popular desserts. But, the price of fulfilling your cravings for this addictive treat can get up there (at about $8 a slice), and when you eat it at the restaurant you likely are limited to only one small piece.

The iconic, lovable gummy bear originated in Germany, where it goes by the name Gummibär— but that's not what makes it so much fun. The base of gummy bears is made up of gelatin, which gives them the signature elasticity that makes you feel like a kid again. But the fun doesn't have to stop there.

The octopus is famous for its bulbous head, enormous eyes, and four pairs of long arms. The stuff of legends and nightmares, octopi have been featured in stories, artwork, and meals galore. But how do you eat this distinctive looking, bilaterally symmetrical sea creature?

Garlic is a key ingredient in many delicious meals, and if you've been a fan of our site for even a short while, it's no secret that we love to share tricks and tips to make cooking with garlic even easier than you first assumed.

While a hot dog with all the typical American condiments (ketchup, mustard, relish) is heavenly for kids, as an adult, I realize there is nothing wrong with switching things up a bit and getting creative. In fact, a plain hot dog can be a fantastic blank canvas for chefs to work with—a great, edible example of going from drab to fab.

Welcome back, my rookie hackers! The Golden Fleece of hackers is to develop a zero-day exploit, an exploit that has not been seen by antivirus (AV) software or and intrusion detection system (IDS). A zero-day exploit is capable of skating right past these defenses as they do not contain a signature or another way of detecting them.

Hello again, readers! In our previous crypter tutorial, we looked at how we could obfuscate our malware (or any program) by using a simple one-byte XOR key. In this quick tutorial, we will be looking at how a simple little tweak can create a better means of obfuscation. Let's get right into it!

I hate wasting money. To be fair: I doubt there are many people out there who relish the idea, but I especially hate it. And I also dislike spending in excess of what I need. This happens all too often, I feel, when it comes to recipes that involve using sausage.

Welcome back, my greenhorn hackers! The Holy Grail of any hacker is to develop a zero-day exploit—an exploit that has never been seen by antivirus (AV) and other software developers, as well as intrusion detection system (IDS) developers. In that way, you can exploit systems with your newly discovered vulnerability with impunity!

It goes without saying that a pizza stone is one of the keys to making a perfect pizza. The science behind pizza stones is relatively simple: the stone conducts and holds heat, which keeps the oven temperature steady even when a cold ingredient (such as an uncooked pizza) is introduced. This not only helps the pizza cook more evenly, but also allows the bottom to get crisp.

When I get struck by a craving for something SCJ (savory, crunchy, juicy), nothing fits the bill better than a BLT. But why settle for the sandwich form when there are so many other possibilities? Some of my favorite alternative ways to serve up a BLT are 1) as a salad, 2) in tomato cups, 3) in mini bread bowls, 4) as lettuce wraps, 5) as a dip, and 6) in bacon cups.

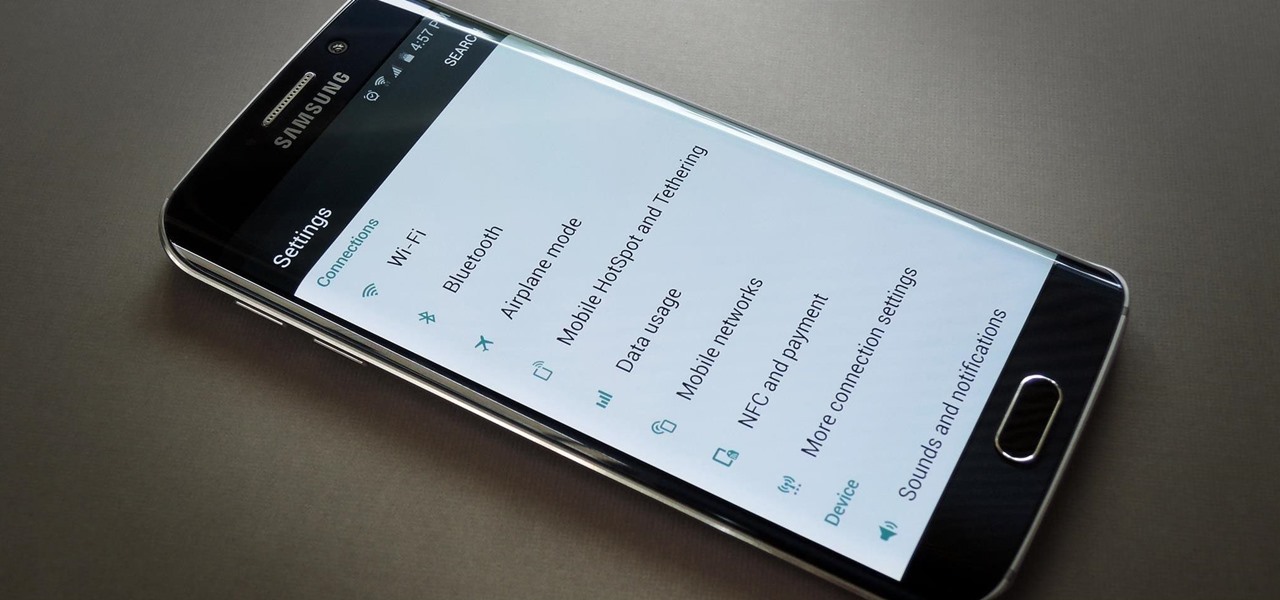
When the Galaxy S6 hype-train was building momentum ahead of the phone's release, many reports had Samsung cutting back on its much-maligned TouchWiz skin. In the end, these reports were either highly exaggerated or entirely fabricated, because while not as egregious as previous devices, Samsung's signature bloated UI and duplicate apps are definitely present on the Galaxy S6.