I'm a sucker for sushi, both in its traditional forms and its modern fusion creations. When the infamous sushi burritos surfaced, I'm not ashamed to admit that I waited in a ridiculously long line for what is essentially an uncut sushi roll. (As for whether it was worth it or not, well... that's another story.)

I know I'm in the majority when I say that grilled cheese sandwiches are one of life's simplest and best pleasures: gooey, rich, melted cheese, sandwiched between two perfectly-buttered pieces of toast... perfection.

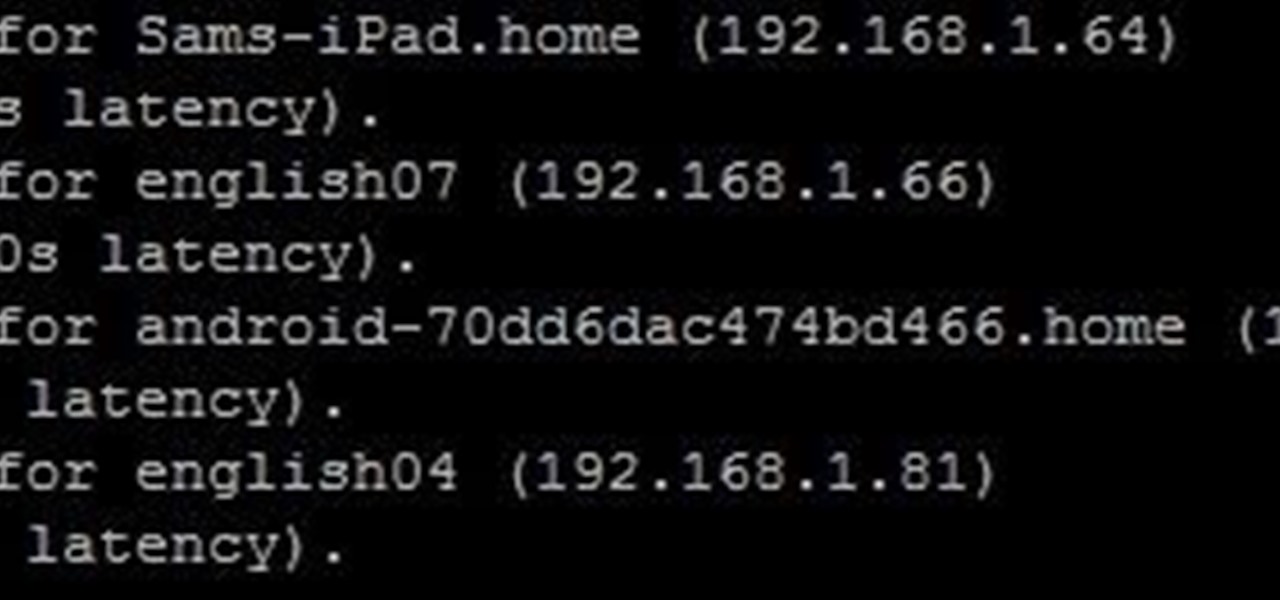
Since Ive started to learn about nmap and metasploit and other tools I was learning well but I had one problem,

Virtual reality is all the rage these days, especially with devices like the Oculus Rift, Gear VR, and HTC Vive hitting shelves lately. But before any of those fancy, expensive headsets ever made it to the market, Google came up with a thrifty and inventive substitute in the form of Google Cardboard.
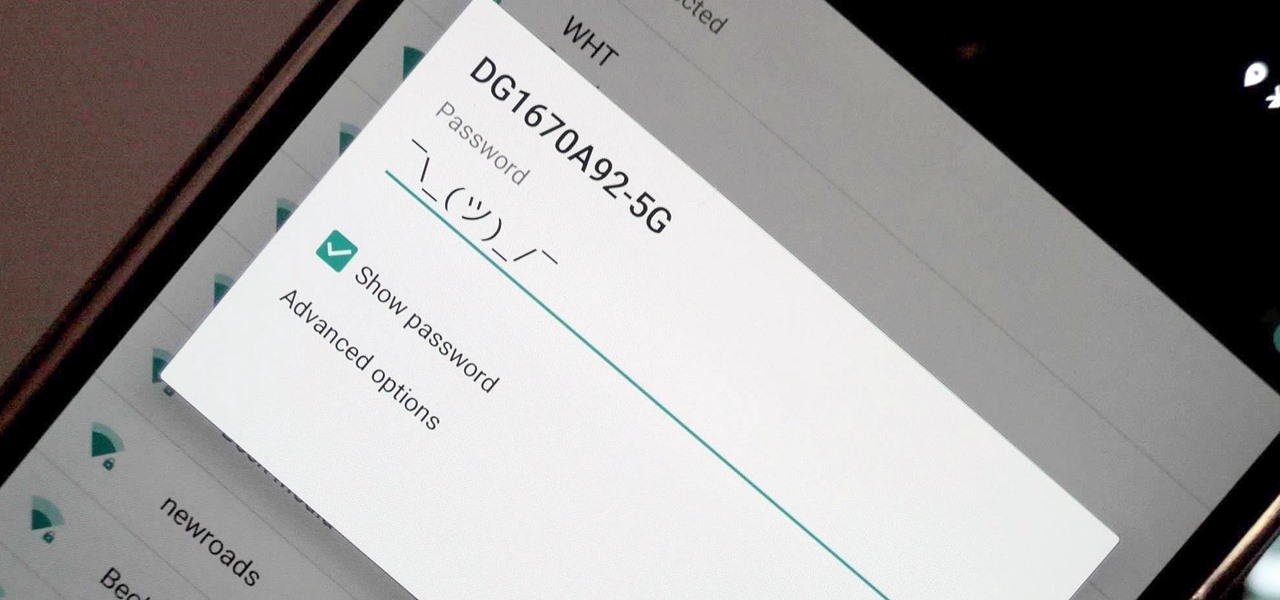
Researchers at MIT's Computer Science and Artificial Intelligence Laboratory have created Wi-Fi technology that identifies where you are, which may eliminate the need for passwords.

Whether you're a seasoned wine drinker or just beginning to explore the wondrous world of fermented grapes, finding fantastic wine on a budget isn't as difficult as one may think. With these 8 tips, you'll see how and why you need not shell out $45 to get a great-tasting, high-quality bottle of wine without settling for vino.

Ever since the Google Play Store removed its "Designed for tablets" section, it's been a lot harder to find good, tablet-optimized Android apps. Not that it was all that great to begin with considering that they used to list apps like Facebook and Twitter, which only have oversized phone UIs on tablets, not actual customized UIs.

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.

Six Flags is teaming up with Samsung to make riding a roller coaster a little more thrilling, and quite possibly a little more nauseating as well.

The Stagefright exploit, which allowed for malicious code to be embedded in files on your device, is now very real in the form of Metaphor. Developed by software research company NorthBit, Metaphor is their implementation of exploits to the Stagefright library, and when executed, can access and control data on your device.

While there are tools online that let you turn photos into interesting emoji art, and mobile apps that let you create emoji mosaics, none do it better than an iPhone app by second verse, which makes it a super easy, highly customizable process.

The Null Byte community is all about learning white hat hacking skills. In part, this is because I believe that hacking skills will become the most valuable and important skill set of the 21st century.

We've all been there—you're away from home, your phone's battery is quickly nearing zero, and you forgot to bring your charger. "Hey, does anybody have an iPhone charger?" you ask. Crickets. If you could understand cricket-speak, you'd know that they too were saying "Sorry, bud. We're all on Android."

Using a technology we like to call "Hive Computing," several Android apps allow you to contribute idle processing power to help further scientific research. This basically means that when you're not using your phone or tablet, it can join forces with other idle devices to form a supercomputer that scientists can use to potentially make a world-changing breakthrough.

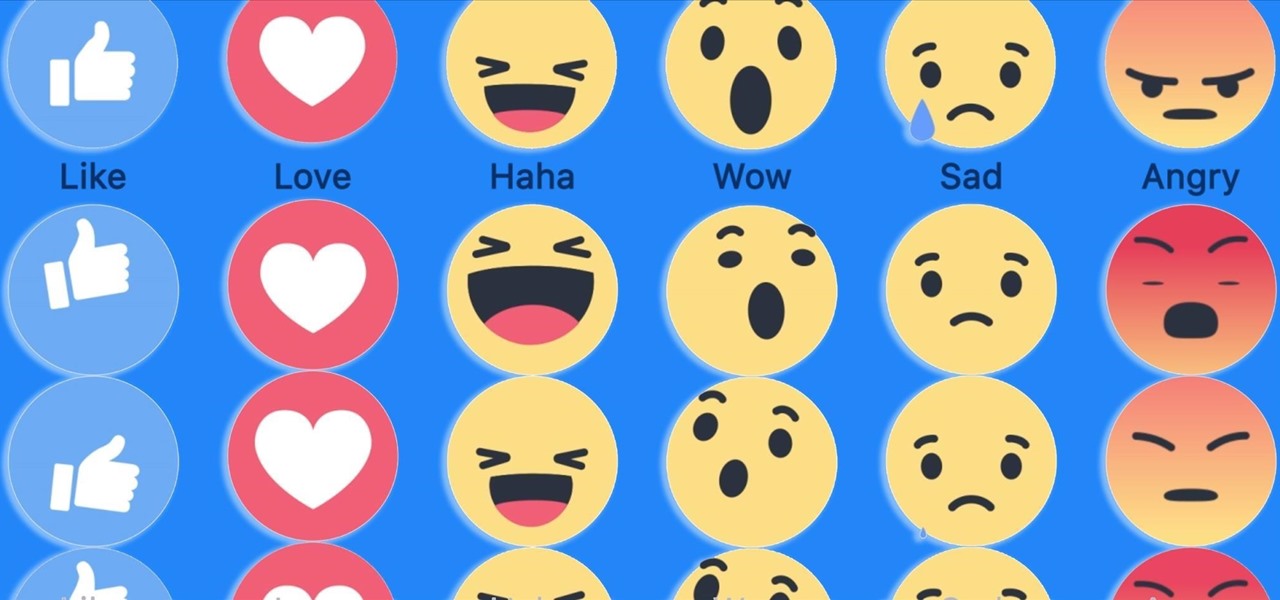
Have you ever run across a Facebook post that you don't necessarily want to "Like," but you're not really passionate enough about to bother stringing together a couple words for a comment? Well, you're in luck, as Facebook added five new "Reactions" that let you do more than just like a post, and they're now live for everyone.

Good day to everyone, today I will present some basic and advanced concepts that targets sophisticated attacks on the social basis, also I will write about some steps that can prevent this attacks from occuring, basically we will examine Social Engineering from the angle of attacker and victim, some people who are interested in security and work for middle-sized companys can learn and use something interesting from this post.

Right, So i've been asking alot of questions here on Null-Byte and everyone has been really helpful to me.

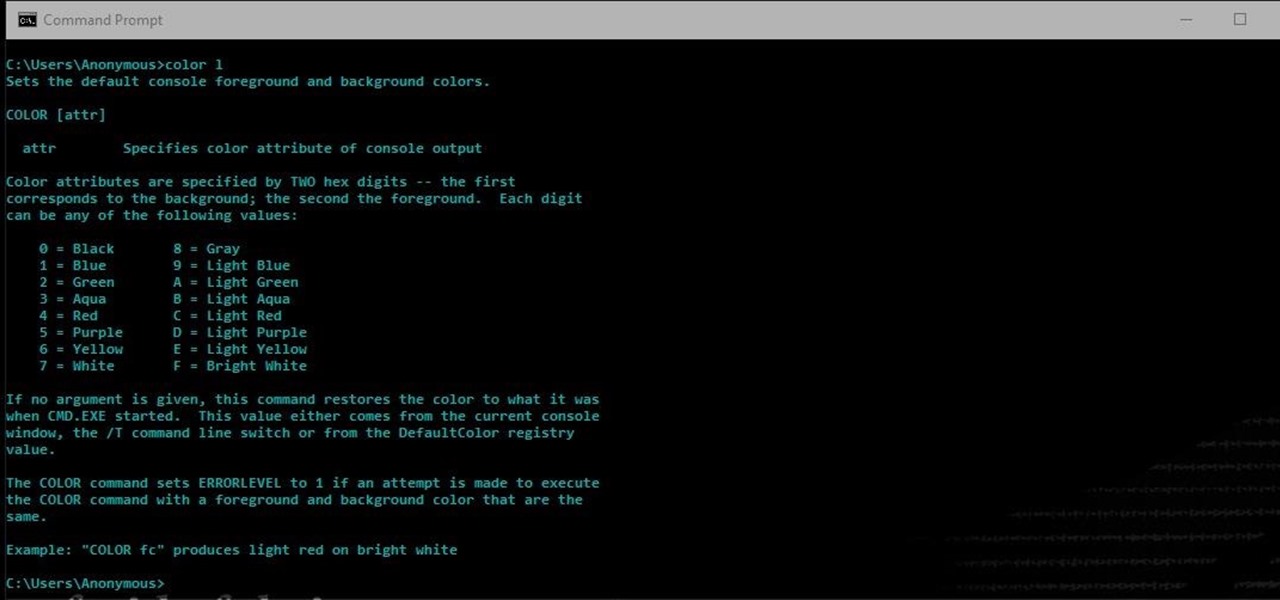
Another series I am now starting, might have to slow down on all of these series, but why tf not. What Is CMD?

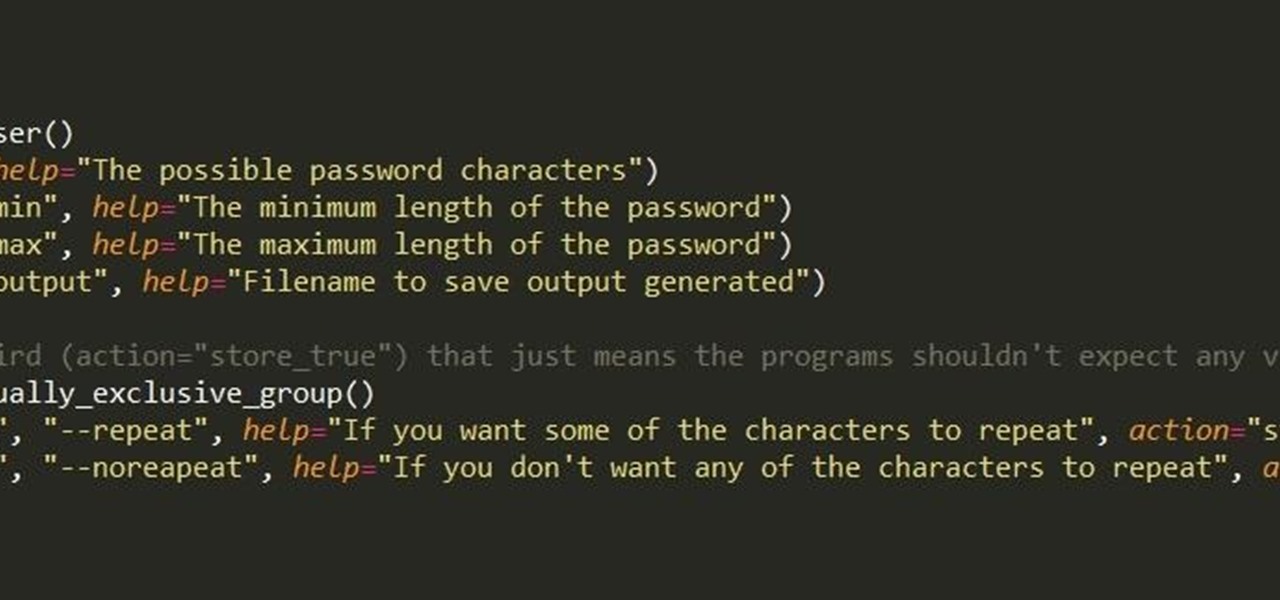
Hello aspiring hackers, It's been a while since I wrote a tutorial, so I figured I might just share one of the tools that I have created to help the community grow.

In my last tutorial, I talked about creating a virus inside of a Word Document in the scenario of a mass-mailer attack. In this post, however, I'm going to be covering creating a fake image or screenshot with a meterpreter backdoor hidden inside to be used in a similar scenario. Step 1: Creating the Virus

Listen up, children, pregnant women, and lightweights: this particular KitKat variety is not for you. Well, with 0.8% alcoholic content per 2 KitKat bars, it's highly unlikely anyone will actually get drunk on these things. Still...

Waking up can be a real struggle for some people. Alarms help, but most of them are so easy to turn off that you can shut them off while you're still half asleep and go back to bed, only to wake up in a panic as your realize you've severely overslept. Microsoft Garage wants to make you at least work for your lethargy with its new Mimicker Alarm.

Five Phases of Hacking:- The five phases of Hacking are as follow:

We all know them, and many of us despize them. And some might support them, regardless many have different opinions.

Android's copy/paste menu and text selection options have traditionally been downright terrible, but things are starting to get better with some recent improvements made in Marshmallow. That being said, there's still a lot left to be desired, and there's always plenty of room for more useful functionality.

You've probably heard the old joke about how Ford is an acronym for "Found on Road Dead." Well, the Detroit automaker on Monday announced a new and much better way to help you find your parked vehicle, as well as a whole host of other features—just use your smartphone.

A video showing what is alleged to be the new Apple iPhone 7 has appeared online. The uploader of the video claims that it was shot on one of Foxconn's assembly lines.

The Nexus 5X and Nexus 6P have identical camera hardware—in fact, both use one of the highest-end camera sensors ever put into a smartphone. The only real difference between the cameras on Google's latest flagship devices is that the 6P natively supports electronic image stabilization (EIS) whereas the 5X does not.

to stay secure, you dont just need Tor, and a VPN. You need good browsing habits. What are Browsing Habits You Ask?

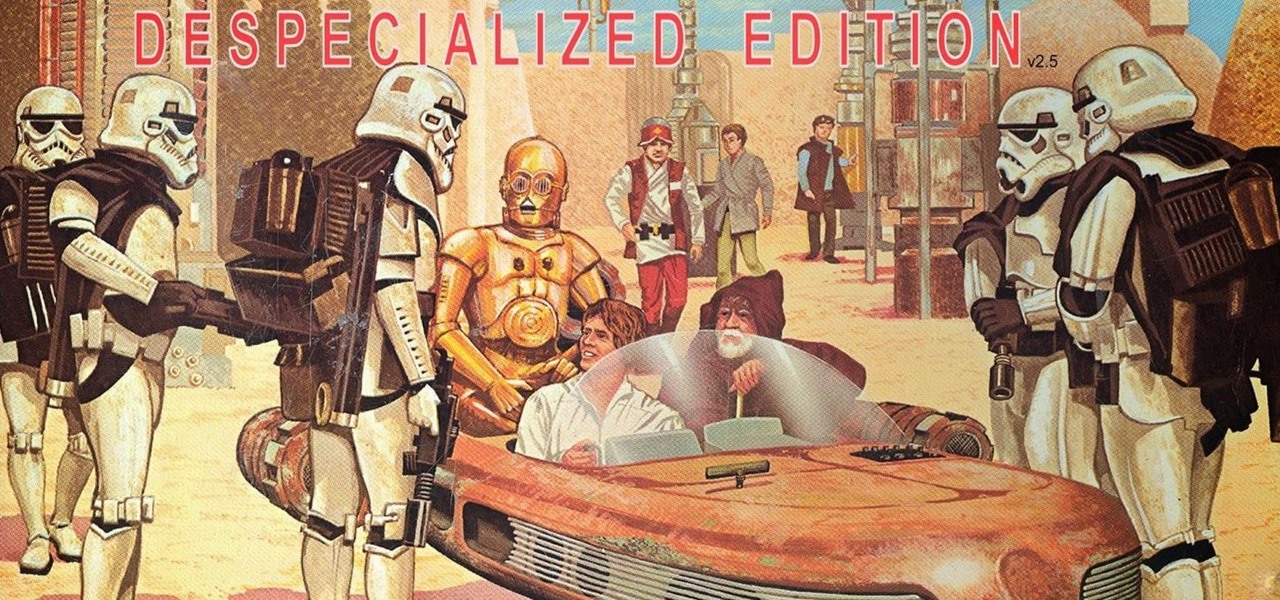
I loved the original Star Wars trilogy when I was a kid, but loathe all of the current DVD, Blu-ray, and streaming versions available today. Ever since 1997, every version of A New Hope, The Empire Strikes Back, and Return of the Jedi has had horrendous CGI effects added in that George Lucas deemed necessary to bring his "ideal" version to life.

UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found at my blog, here - at my blog, here - https://techkernel.org/2015/12/11/embed-metasploit-payload-in-apk-easily/

As you all know, Anonymous have declared cyber war on ISIS and have already proven what they are capable of and whats to come.

CEO's of IT companies doesn't know this because they are not a hacker. Only a true hacker can become a successful Security head officer.

Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.

Your English teacher is a creep. The way he looks at your girlfriend, the way he always spends ages with the girls in the class going over their work but not the boys, just the way he is.

One of the most exciting things about a major iOS update is the discovery of new glitches, or even just finding ways to replicated the old ones that we've come to love so much. One of these is the glitch that lets you nest folders within folders on the home screen, which can save some major screen real estate. While this glitch was available in both iOS 7 and iOS 8, the process is slightly different in iOS 9, but you still have a couple options to choose from.

Cupcakes are special treats by themselves, so surprise-inside piñata cupcakes are extra special for birthdays and special occasions. You can customize these with any flavor of cupcake and any type of candy or chocolate treat you want to stuff them with.

A simply frosted or glazed cupcake is like a blank canvas for creative decorations. Intricate cupcakes are works of art, but piping frosting or rolling fondant can be tricky. Luckily, even the most craft-challenged person can use pre-made decorations to create party-worthy cupcakes. Use chocolates or candies to make designs or other decorations and you can have endless fun (and very little stress) creating eye-catching treats.

The transition from Android KitKat to Lollipop was pretty drastic in the looks department. Google's new Material Design guidelines changed the way many parts of the UI function, like the notification drawer, status bar, and most notably, the lock screen.

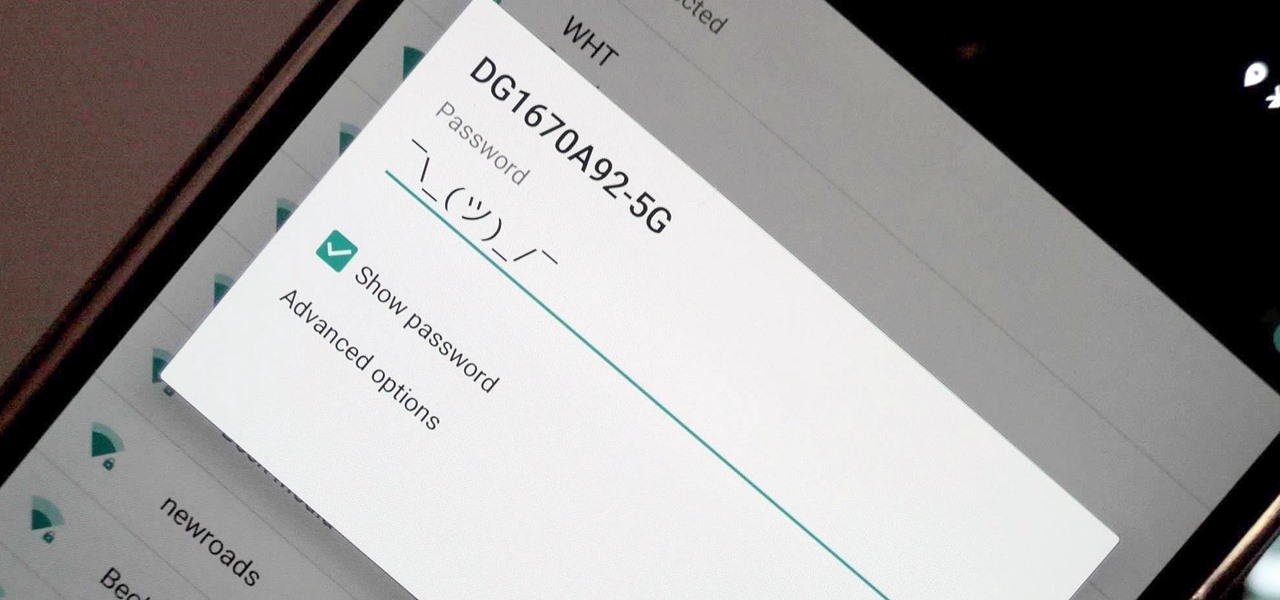
First of all, I hope the title makes sense. :D Well, this is basically creating a program that can help with dictionary attacks. Generate possible passwords. It pretty much lies in you knowing the person you want to hack.