
The Nexus Killer: OnePlus One Phone Review
A month ago, we showed you what I, and many around the web, dubbed the "Nexus Killer". That device is the OnePlus One, a low-priced, high-powered, CyanogenMod-run Android device.


A month ago, we showed you what I, and many around the web, dubbed the "Nexus Killer". That device is the OnePlus One, a low-priced, high-powered, CyanogenMod-run Android device.
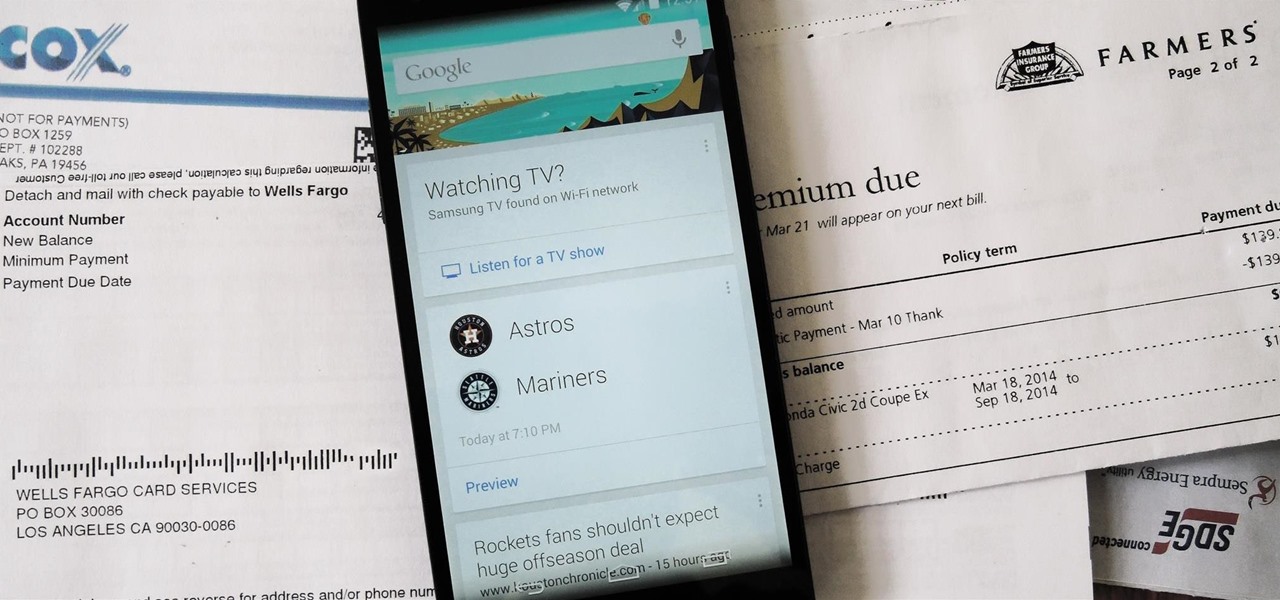
Google is widely renowned for its mastery in using data to tailor specific search results and ads. Their Android and iOS search apps put this ability to use in finding the most relevant pages for your query, and their desktop site is the most-used search engine on the web as a result of it.

If you've ever seen one of those Samsung commercials from about a year back, you know that the Galaxy S series of phones come with a feature that allows you to do certain things by making gestures in front of your screen. They call this feature Air Gesture, and it enables you to perform certain functions without even touching your phone.

Your beloved Samsung Galaxy S3 is nearing the end of its life cycle. Sure, it can do most of what newer devices can, especially if you were lucky enough to receive the KitKat update, but your diminishing battery and scratched up screen have seen better days.

Removing the thin aluminum foil wrapping from a Hershey Kiss isn't necessarily a difficult thing, but even the easiest of things can be annoying sometimes. For instance, getting chocolate under your fingernail when you're trying to peel the wrapper off, or making a wrapper mess. To make this first-world problem go away, simply grab a Hershey Kiss in-between your index finger and thumb, then pull on the paper plume to yank the chocolate straight out of the wrapper. The plume was originally des...

This Square knot design feature picots, which are small loops at the sides of the knot. Picots are simply loops along the edges. Picot Designs are vintage Macrame techniques. They are often used to make the edges of craft items to look like as flower petals. This is a good project for children and beginners to learn one of the basic knots frequently used in Macrame. To this pattern you can add pearls and have an interesting look.

Welcome back, my novice hackers! I have tried to emphasize throughout this "Hack Like a Pro" series that good reconnaissance is critical to effective hacking. As you have seen in many of these hacks, the techniques that we use are VERY specific to the:

The flexibility within Android is pretty amazing. Unlike iOS, you can make a lot of modifications with nothing more than a download from Google Play, but to really step up your softModder game, you'll need to go a little further.

Midway through 2013, a popular custom ROM called Paranoid Android introduced their multitasking feature "Halo." Bubble-style notifications inspired by Facebook chat heads pop up near the top of the screen, and you simply tap on them to bring up the app in a floating window.
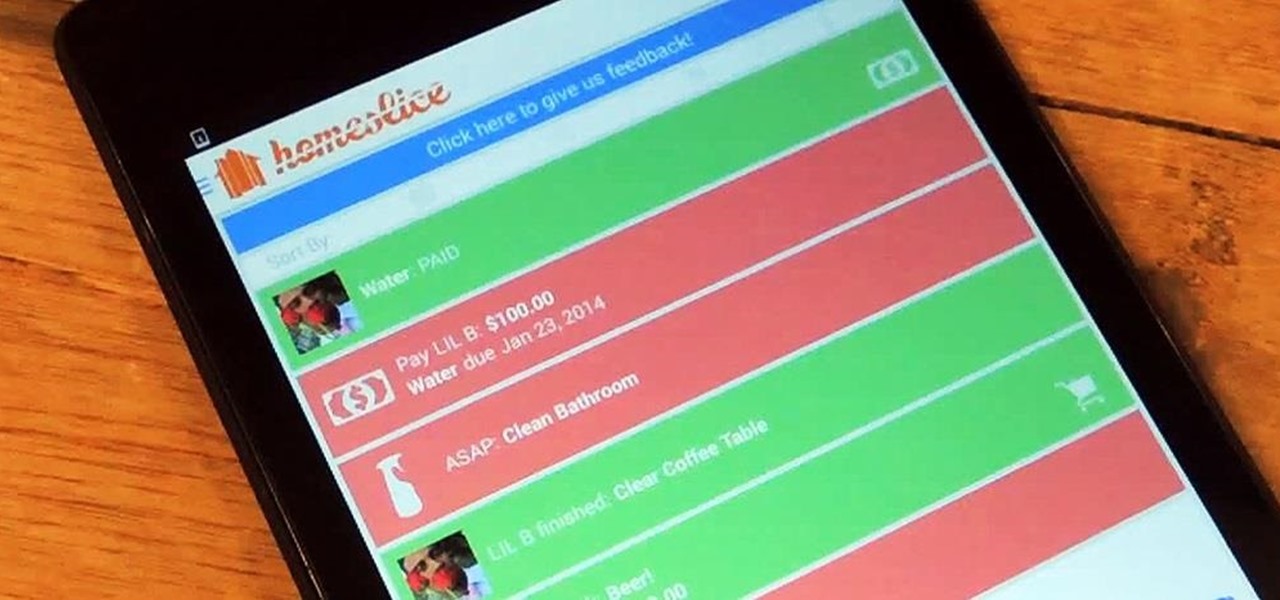
We've all heard our fair share of roommate horror stories, or have some of our own, because we never truly know who someone is until we've lived with them. Cohabitation issues generally revolve around things like bills, chores, cleaning, and groceries. Approaching a roommate, especially an adult one, to remind them to do their chores can be an anxiety-ridden and daunting task. After all, we're roommates, not parents!

Video: . It can some time be a pain to separate egg whites from the yolk. I did some searching online and came to find some great ways to separate them.

It may finally be dying down a bit, but there are still plenty of cat lovers addicted to Grumpy Cat, who has surpassed her internet meme stardom to move onto books, calendars, and even a soon-to-be film. For those of you who just can't get enough of the crotchety-faced Tardar Sauce, make this Christmas a Grumpy Christmas with this free printable paper ornament of Grumpy Cat.

Welcome back, my budding hackers! I've written several listener guides on creating a malicious PDF or malicious Word document that would carry in it a payload with the Meterpreter, or reverse shell enabling you to own the system. One of the hurdles to using these techniques is the antivirus (AV) software on the target system. For instance, if you try to email a malicious PDF or Word doc, it's likely that the victim system will alert the victim that it contains a virus or other malware.

Automation applications bring the future a little closer. If you've seen Minority Report or other futuristic sci-fi movies, the intrigue of having your electronics work independently is something we can all appreciate.

See how to open a bottle of champagne with a kitchen knife, a wine bottle with a ribbon, and a bottle of beer with a paper note! Watch the video below for the full instructions, or hit up the brief guide below.

Despite its deliciousness, the pomegranate is one of the hardest fruits to eat. Once you cut it open, the seeds are stuck behind a bitter-tasting white membrane, and trying to pull them out with your fingers just results in a huge mess.

Welcome back, my fledgling hackers! It's been awhile since we did a Metasploit tutorial, and several of you have pleaded with me for more. I couldn't be happier to oblige, as it's my favorite tool. For the next several weeks, I'll intersperse some new guides that'll help expand your Metasploit skills and keep you abreast of new developments in Metasploit, so look for them in the near future.

Unless you like paying exorbitant prices for out-of-contract phones, most of us are stuck with the one we already have for two or more years. The tech industry moves fast, and as new phones are released seemingly every month, your Samsung Galaxy S4 might start looking older by the week.

If I were a math major, I'd probably be rolling in dough somewhere in Silicon Valley right now, but since multiplying numbers and figuring out tangents gives me panic attacks, I went the English route... pays much better.

The new Apple iOS 7 is here for your iPad Mini. Closing running apps prevents them from taking up precious memory, resources and battery. Simply quitting an app by pressing the home button doesn't work; the application is still running. Watch the video below to see how to close them completely.

If you're a dedicated Instagrammer, you're probably well aware of the humblebrag hashtag #NoFilter, which expresses to other users that your photo is just so damn awesome that it looks like you added filters to it, even though you really didn't.

The shortest distance between two points is a straight line, but the shortest way to launch an app on an iPhone can be a much more complicated process.

Video: . In Adobe Photoshop CS5.1 there are several ways to perform same action. I make a video tutorial in which you can learn that how to combine two images to perform your different operations. I used a very simple and quick method. To follow my method you can get a quick adjustment of two or more then two images just in single frame and get the result you desire.

Apple may have unabashedly lifted their upcoming "Control Center" from Android devices, but visually speaking, it's an awesome take on Quick Settings that would look pretty good on a Samsung Galaxy S3.

Being in your twenties is tough. You're not a child anymore, but also not quite a full-fledged "adult" yet. Sure, you do adult things like cook asparagus sometimes, but you're also sweating about securing enough likes on your social media posts.

Welcome back, my nascent hackers! Earlier, I wrote a guide on finding operating system and application vulnerabilities in Microsoft's own security bulletins/vulnerability database. In this tutorial, I will demonstrate another invaluable resource for finding vulnerabilities and exploits by using the SecurityFocus database.
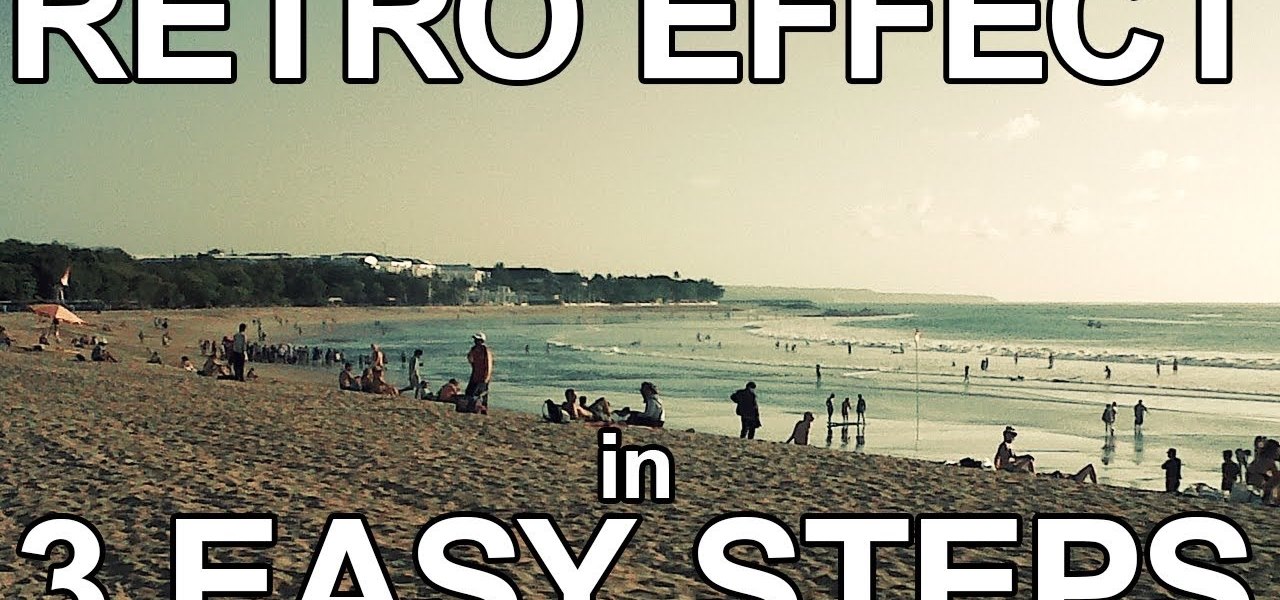
It's very popular thesedays to use a old looking Vintage effect on photos. I do it myself with Photoshop a lot and for me it's simply the explanation, that the retro optic of an old camera justs awesome.

Welcome back, my novice hackers! Most of my tutorials up until this point have addressed how to exploit a target assuming that we already know some basic information about their system. These include their IP address, operating system, open ports, services running, and so on.

Welcome back, my neophyte hackers! Several of you have written me asking how to crack passwords. The answer, in part, depends upon whether you have physical access to the computer, what operating system you are running, and how strong the passwords are.

I took trap and skeet my senior year of college and couldn't have felt any more badass. Hitting a little orange disc as it flies across the sky may not sound that legit, but trust me, it is very much so. In honor of the age-old shooting game, BioShock: Infinite has the "Skeet Shoot" achievement.

Now that there's a working jailbreak for every iOS 6.1 device, there are more and more people jailbreaking their iPhones (including me) for better customization. But for those of you who have no desire to jailbreak, you can still do some pretty cool tweaks.

Earlier today, a meteorite flew over the Chelyabinsk region of Russia, triggering a shock wave that injured hundreds of people and caused damage to buildings and vehicles in the area. Witnesses describe seeing a bright ball of light streak through the sky followed by a loud boom as the 10-ton meteorite entered the Earth's atmosphere and exploded.

Forum member Luciano posted a terrific guide on adding hacks to our phone by editing build.prop. The article was great, but one of best things I saw in it was the "What You'll Need" section:

Welcome back, my tenderfoot hackers! In some of my past articles, I've shown numerous ways of embedding a listener/rootkit on a remote system, including buffer overflows of the operating system, getting the victim to click on a link to our malicious website, and sending a malicious Microsoft Office and Adobe Acrobat file.

Live Beyond Feng Shui consultation by Master Aur with guest Janine from Brisbane Australia. In this call Aur shows how that just by seeing a floor plan we are able to know many intimate details about a persons life.

Did you know that your bathroom is directly connected to your money and can show us just by taking a peek inside how you spend it?

As we've already mentioned, Skyfall is an awesome James Bond movie - one of the best, really (if not THE best?). Today's very special Watch This Instead looks at one of the reasons it turned out so great: cinematographer Roger Deakins. He's worked with Skyfall director Sam Mendes many times before and has a special relationship with the Coen bros. also. If you're not a James Bond freak or you can't make it out to see Skyfall, then check out some of his other work instead!

After a two-month delay, Apple has finally released iTunes 11, which was initially slated to be released alongside iOS 6.

As people continue to upgrade their PCs to Microsoft Windows 8, more and more developers are adding content to the Windows Store. While the offerings are not as vast as Google Play or the iTunes App Store, it does have some solid apps for both productive users and those looking to just while away the time.

Automator is a built-in Mac utility found in Mac 10.4+ and can be used to convert a PDF file to text format.