iPad, iPhone, and iPod touch owners: it's that time again. iOS 8 has been released to the public, and those who have been eager to update since Apple's WWDC announcement won't have to wait any longer. Since iOS 8 promises to pack a bunch of new, really great features, it's time to present your options for getting on the latest and greatest for your Apple device.

Pushbullet is one of those apps that helps separate Android from its competition. By pushing the boundaries of cross-platform data syncing and file sharing, the service truly demonstrates how flexible and robust the world's leading mobile operating system can be.

Before your carrier got its grubby little hands on your Galaxy S5, there was less bloatware installed and more functionality offered by the Samsung flagship device. Case in point: the GS5 that Samsung designed was capable of recording phone calls, yet the one that you own probably isn't.

How many times do you misplace your phone? Once a day? Twice? As much as you may hate losing your phone, it always seems to happen, and finding it isn't very easy if you left it on silent mode.

Welcome back, my rookie hackers! I recently began a series on using Metasploit, and my goal with it is to teach you the very basics the incredibly powerful hacking tool has to offer while progressively moving on to the more advanced features.
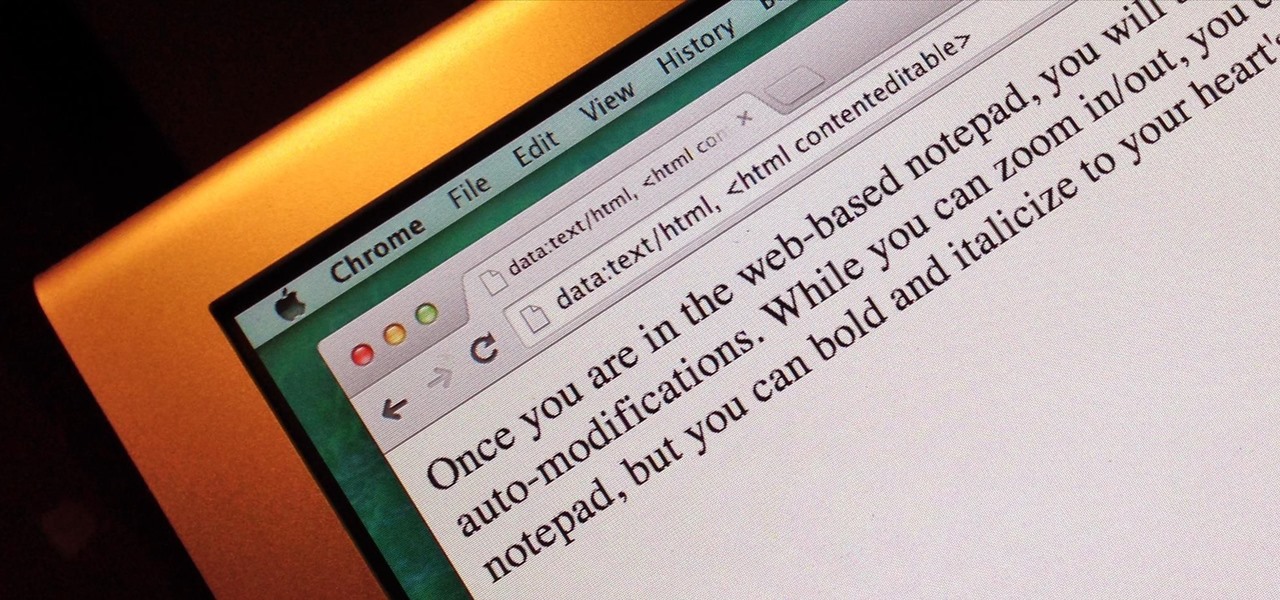
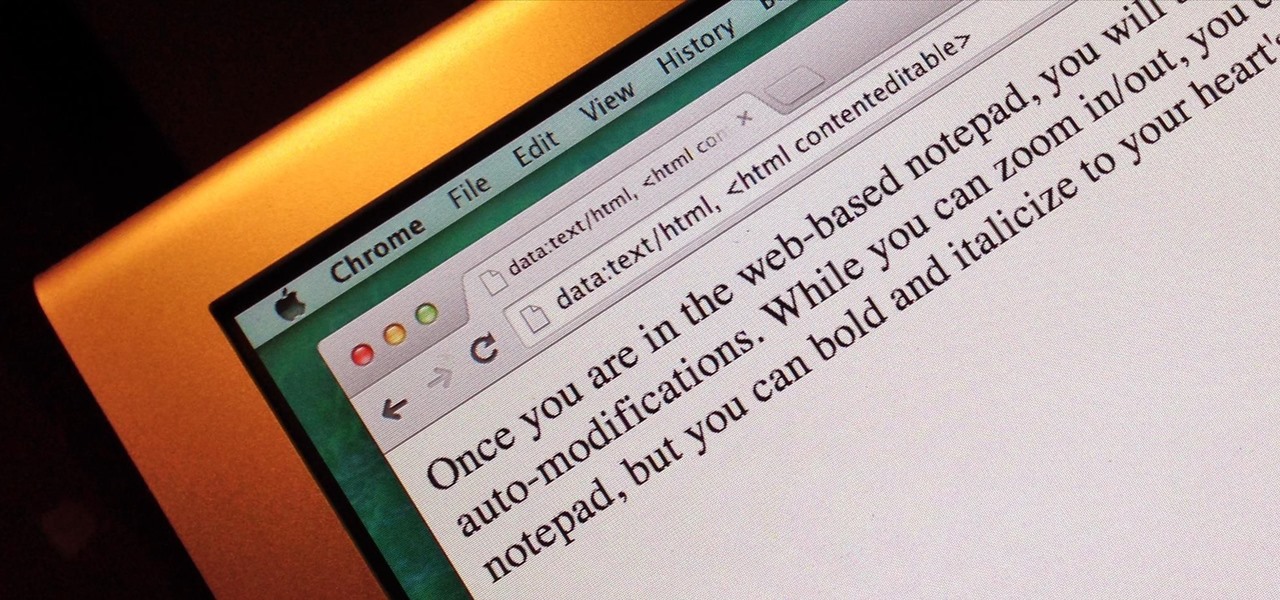
Do you take your notes on a word processor while browsing the web? Well, stop. There's an easier, less RAM hungry way to take notes by turning the tab of your web browser into a notepad. Whether it's an email address, a line of code, a new how-to, or an idea you don't want to lose, you can easily jot it down without slowing down.

Finally! A media box that gives you everything you want, in one tiny package. The EzeeCube will allow you to view your pictures and videos while staying organized at the same time.

Welcome back, my novice hackers! It has become clear from some of your questions that quite a few of you are unfamiliar with the hexadecimal system, or simply, hex. The hexadecimal system is used throughout computing and if you have never studied this Base16 numering system, it may appear relatively opaque.

Sony is ready to get into the micro-console gaming fight, with its PlayStation TV set to debut this fall.

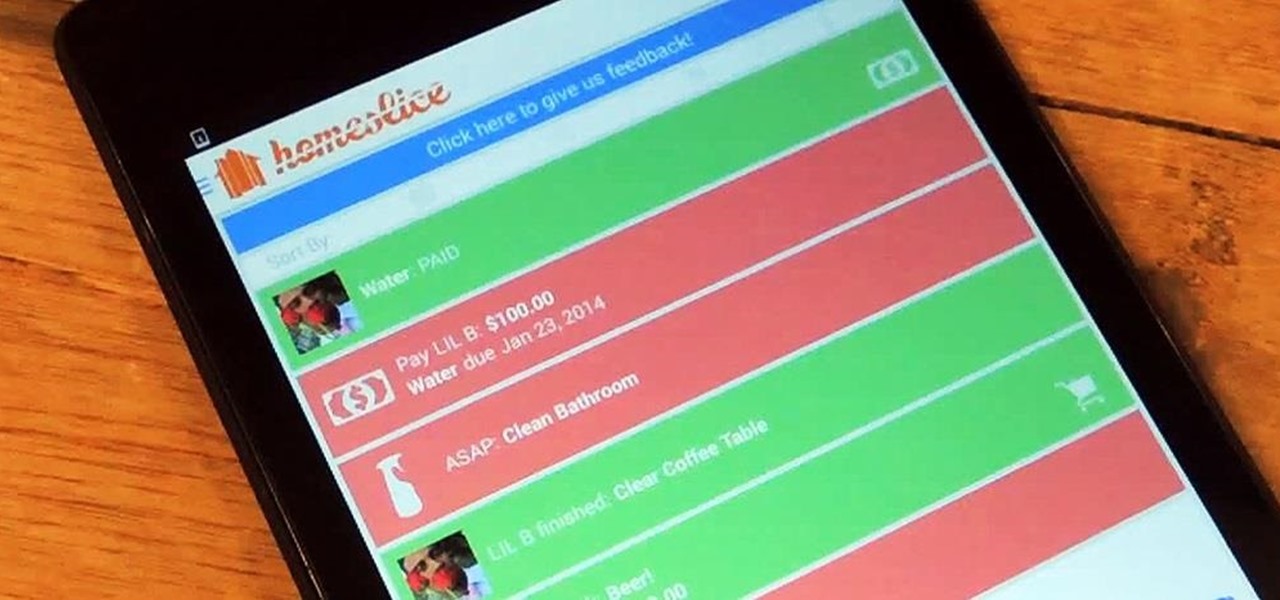
To-do list and reminder apps are a dime a dozen on Google Play, so trying to find the right one for you could take hours as you sift through hundreds of similar apps and widgets. Well, search no more, as we've found one of the most well-designed and easy-to-use reminder apps out there.

A month ago, we showed you what I, and many around the web, dubbed the "Nexus Killer". That device is the OnePlus One, a low-priced, high-powered, CyanogenMod-run Android device.

Your beloved Samsung Galaxy S3 is nearing the end of its life cycle. Sure, it can do most of what newer devices can, especially if you were lucky enough to receive the KitKat update, but your diminishing battery and scratched up screen have seen better days.

Removing the thin aluminum foil wrapping from a Hershey Kiss isn't necessarily a difficult thing, but even the easiest of things can be annoying sometimes. For instance, getting chocolate under your fingernail when you're trying to peel the wrapper off, or making a wrapper mess. To make this first-world problem go away, simply grab a Hershey Kiss in-between your index finger and thumb, then pull on the paper plume to yank the chocolate straight out of the wrapper. The plume was originally des...

This Square knot design feature picots, which are small loops at the sides of the knot. Picots are simply loops along the edges. Picot Designs are vintage Macrame techniques. They are often used to make the edges of craft items to look like as flower petals. This is a good project for children and beginners to learn one of the basic knots frequently used in Macrame. To this pattern you can add pearls and have an interesting look.

Welcome back, my novice hackers! I have tried to emphasize throughout this "Hack Like a Pro" series that good reconnaissance is critical to effective hacking. As you have seen in many of these hacks, the techniques that we use are VERY specific to the:

Midway through 2013, a popular custom ROM called Paranoid Android introduced their multitasking feature "Halo." Bubble-style notifications inspired by Facebook chat heads pop up near the top of the screen, and you simply tap on them to bring up the app in a floating window.

We've all heard our fair share of roommate horror stories, or have some of our own, because we never truly know who someone is until we've lived with them. Cohabitation issues generally revolve around things like bills, chores, cleaning, and groceries. Approaching a roommate, especially an adult one, to remind them to do their chores can be an anxiety-ridden and daunting task. After all, we're roommates, not parents!

Video: . It can some time be a pain to separate egg whites from the yolk. I did some searching online and came to find some great ways to separate them.

Welcome back, my budding hackers! I've written several listener guides on creating a malicious PDF or malicious Word document that would carry in it a payload with the Meterpreter, or reverse shell enabling you to own the system. One of the hurdles to using these techniques is the antivirus (AV) software on the target system. For instance, if you try to email a malicious PDF or Word doc, it's likely that the victim system will alert the victim that it contains a virus or other malware.

Welcome back, my fledgling hackers! It's been awhile since we did a Metasploit tutorial, and several of you have pleaded with me for more. I couldn't be happier to oblige, as it's my favorite tool. For the next several weeks, I'll intersperse some new guides that'll help expand your Metasploit skills and keep you abreast of new developments in Metasploit, so look for them in the near future.

The new Apple iOS 7 is here for your iPad Mini. Closing running apps prevents them from taking up precious memory, resources and battery. Simply quitting an app by pressing the home button doesn't work; the application is still running. Watch the video below to see how to close them completely.

Video: . In Adobe Photoshop CS5.1 there are several ways to perform same action. I make a video tutorial in which you can learn that how to combine two images to perform your different operations. I used a very simple and quick method. To follow my method you can get a quick adjustment of two or more then two images just in single frame and get the result you desire.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

Welcome back, my nascent hackers! Earlier, I wrote a guide on finding operating system and application vulnerabilities in Microsoft's own security bulletins/vulnerability database. In this tutorial, I will demonstrate another invaluable resource for finding vulnerabilities and exploits by using the SecurityFocus database.

It's very popular thesedays to use a old looking Vintage effect on photos. I do it myself with Photoshop a lot and for me it's simply the explanation, that the retro optic of an old camera justs awesome.

We have another BioShock: Infinite achievement tip for you. This achievement (aka trophy for the PS3ers out there) is called Heartbreaker, and requires you to kill and Handyman by only shooting at its heart. If you haven't encountered a Handyman yet, take a look at just how much work went into creating these badass baddies.

Welcome back, my tenderfoot hackers! In some of my past articles, I've shown numerous ways of embedding a listener/rootkit on a remote system, including buffer overflows of the operating system, getting the victim to click on a link to our malicious website, and sending a malicious Microsoft Office and Adobe Acrobat file.

I can definitely say that my MacBook is one of my best friends, but I was still very disappointed when I realized that the only game my laptop came with was chess. For starters, I'm not very good at chess. I haven't even beat the computer once, which really grinds my gears. But, it has come to my attention that chess isn't the only pre-installed game on my Mac—there seems to be some hidden gems that I simply wasn't cool enough to know about. For some of you, this may be old news, but for me, ...

Live Beyond Feng Shui consultation by Master Aur with guest Janine from Brisbane Australia. In this call Aur shows how that just by seeing a floor plan we are able to know many intimate details about a persons life.

Did you know that your bathroom is directly connected to your money and can show us just by taking a peek inside how you spend it?

Free trials are a great way to test out products before a purchase, or simply for the exploitation of free stuff for that limited amount of time. Some trials last a few days and some last even a month or two, but no matter what—these trials will always expire. But like most things in life, there is a way to get around such limitations.

Watchmen may be old(ish) news, but cheap and legit costumes never go out of style. Easily the most sought after character for Halloween (it might be a little cold outside if your hoping to pull off Dr. Manhattan), Rorschach with his trench coast and splotch-filled mask make for a cheap, easy, and instantly recognizable costume for this coming Halloween.

Windows 8 and its new Windows Store have simplified the process for uninstalling and cleanly deleting applications from your computer. Removing applications in older versions of Windows required a few more steps: My Computer -> Control Panel -> Add or Remove Programs -> Find the Program -> Click Uninstall.

With just sticks, some magnets, and a bit of Sugru, you too can be the proud owner of an awesome set of magnetic construction toys! The idea is very straightforward. Simply bond magnets onto the tips of thin sticks using Sugru, but the results look like a whole lot of fun.

The guys at PoorManMods show you how to smoke or tint your taillights using a spray tint by VHT. Simply clean off the taillight to prep it. Spray one to three even coats of tint on the taillight for your desired result. Let them dry, put them on the car, and the stand back and admire your work!

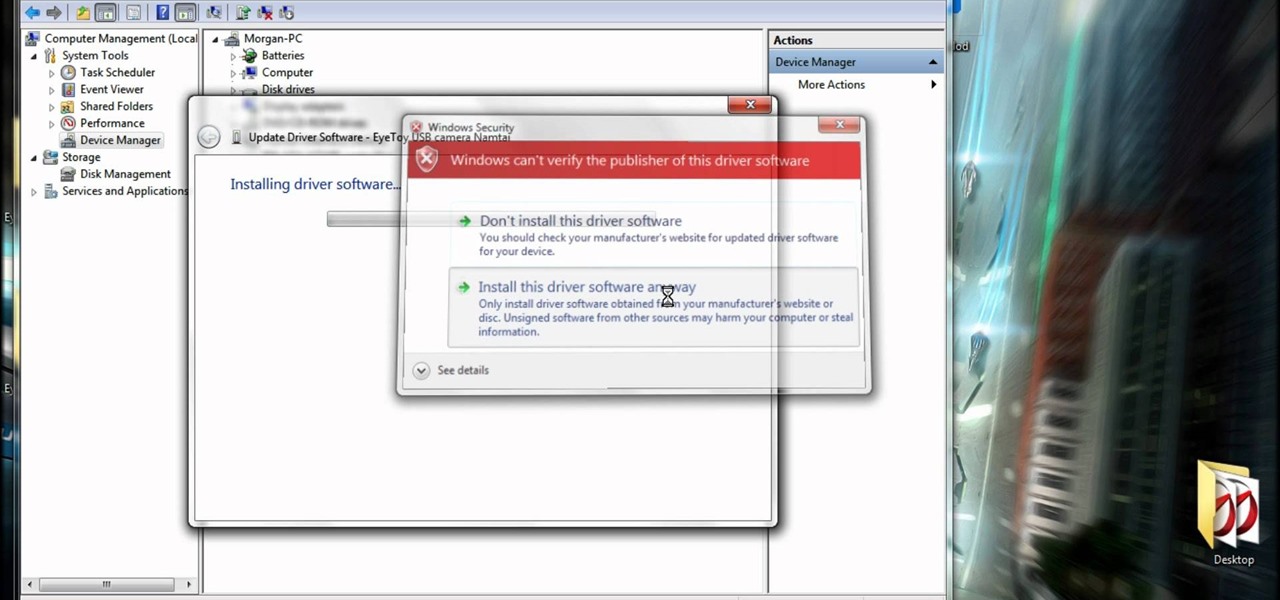
If you have a PS2/PS3 Eyetoy, but don't want to go and spend $30+ dollars on a new webcam, then this is for you.

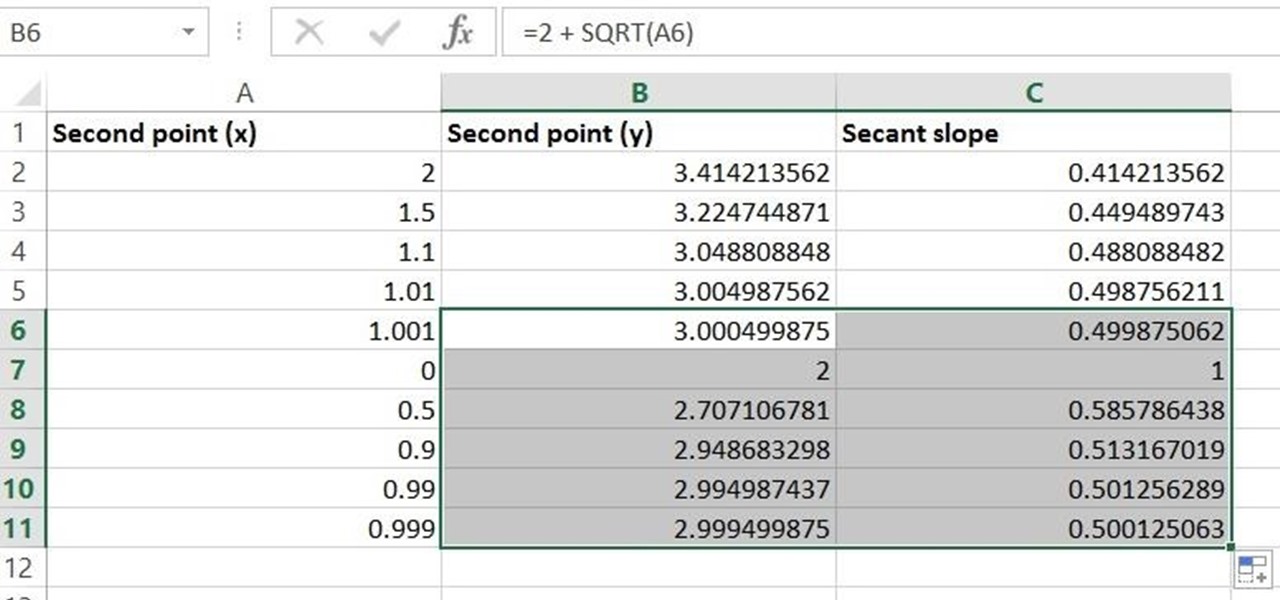
Given a function, you can easily find the slope of a tangent line using Microsoft Excel to do the dirty work. That is to say, you can input your x-value, create a couple of formulas, and have Excel calculate the secant value of the tangent slope. This is a fantastic tool for Stewart Calculus sections 2.1 and 2.2.

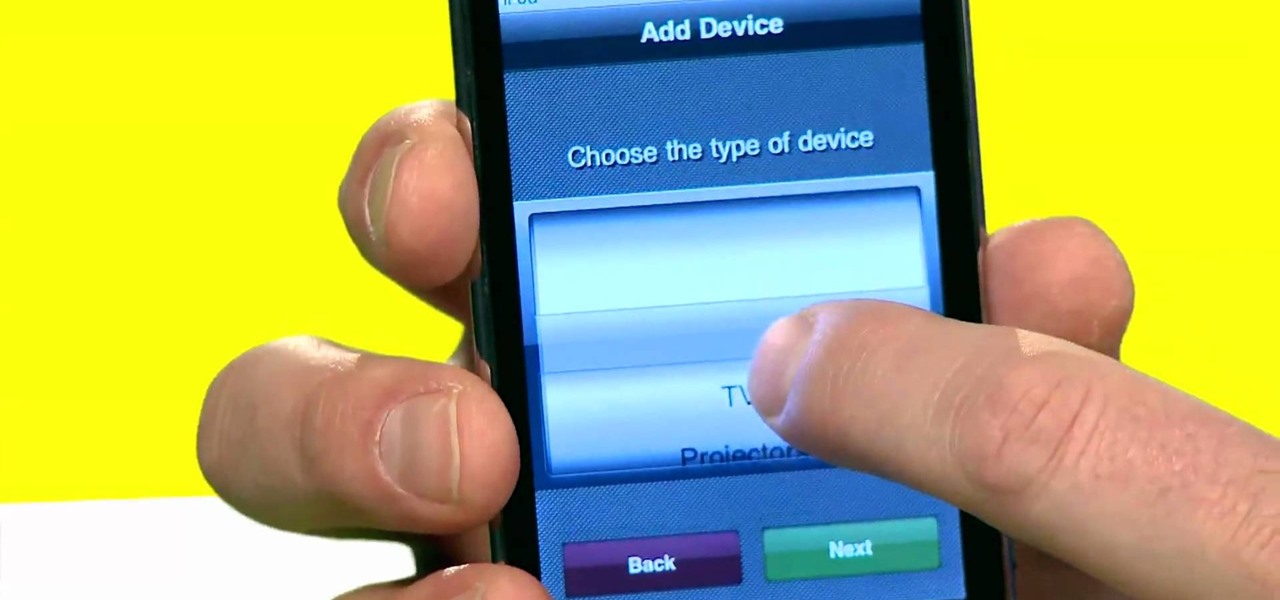
Your iPhone can do just about anything. It can even be a television remote. And a DVD player remote. Also, a CD player remote. You name it, it can be a remote for it. But it can't do it by itself, you need to use FLPR. It's a nice little piece of software that turns your iPhone into a universal remote. But it can be pricey. So what's the deal with FLPR? Best Buy has answers. The Best Buy Mobile team explains how simple it is to transform your Apple iPhone into a universal remote with FLPR.

To add flavor and moisture to your chicken, beer can chicken can allow you to cook a whole chicken on the grill. This tutorial outlines how you can do it to get moist, flavorful chicken. It also ensures that your meat cooks evenly. To begin, combine 1 teaspoon of sugar and salt, 1 1/2 teaspoons of paprika, 1 teaspoon of ground black pepper, 1/2 teaspoon of onion powder, 1/2 teaspoon of garlic powder, and 1/2 a teaspoon of cayenne powder. Stir these ingredients together. Next, rinse your chick...