In this how-to video, you will learn how to create a Facebook group. First, you must have access to a computer with the internet and a Facebook account. To create the group, you need to press the application button and press groups. Press the create new group button. Once this is done, fill out the information required and click create group to finish the process. Now you can invite other people into the group. You can bring a group of people together with a common interest using these groups...

MsMobileMaster shows you how to transfer multi media files between your PC and Motorola Rival or between two Motorola Rivals. This is done by using the mini-SD memory card in the Motorola Rival and by using Bluetooth. First you need to connect your Motorola Rival to your PC via Blootooth as shown in the video, and access the phone's mini-SD memory card. Thereafter, files can be transferred between your PC and Motorola Rival. This same method can be used to transfer files between two Motorola ...

Learn how you would bypass a school’s web filters so that you can go to content sites that are always blocked in examples of YouTube. Click the ‘Start’ button and then click on ‘Run’ and type in cmd and hit enter on your keyboard. This will bring up a command prompt where you type in ‘ping’ and then when that populates the next prompt you enter in the website to bring up the IP address. By entering the populated number you can get into a website from the search field of a web browser. It incl...

This is kind of scary! This video demonstrates just how easy it is to hack into an iPhone to access the data on it - including recovering deleted photos. You only think you've deleted those naughty photos you sent to your girlfriend.... Fortunately, there is a way... However, this particular process requires software available only to law enforcement. But that's never stopped a hacker - or a jilted ex - before!

This all-in-one printer's versatility will help you in any aspect of home office printing, whether it's business documents or family photos. Learn how to print photos without even turning on your computer. Printing and organizing photos will now be a breeze!

Windows users probably remember the system resource tab in the task manager which showed you your resource usage. Well, in Windows 7, this feature has been revamped. This tool will give you real-time reports for CPU, disk, network, and memory usage.

Give someone his or her own personal ticker tape parade with this easy prank. You Will Need

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to install a Wii homebrew hack using the Twilight Hack.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to turn a Fon+ wireless router into a network tap.

Personalize your drinking glasses by etching names and messages on them. Your guests will be so impressed!

Notorious hacker Chris Tarnovsky opens his underground laboratory to WIRED, providing a peek into the world of satellite television smart-card hacking. This complicated process involves nail polish, a pin head and various acids -- so don't try this at home (unless you're Chris Tarnovsky)! Chances are you won't even know what's going on here, but that's not going to stop you from watching this video tutorial on how to reverse-engineer a satellite TV smart card, is it?

Learn how to create a green screen effect using Boris Continuum Complete's Chroma Key filter in Apple Final Cut Studio. BCC Chroma Key is used for compositing camera footage shot using a blue, green, or orange screen as a backdrop over a new background video or a still image from a separate file. BCC Chroma Key is also included as part of Boris FX 9.2 and Boris RED 4.3. If you have access to this powerful plug-in for Final Cut Pro, watch and learn how to use it for precise chroma keying.

Lance Lund, a professor at Anoka-Ramsey Community College, was asked to prepare a promotional science video for the college back in 1995 that was to air on a local cable access channel. All went well until he inhaled some sulfur hexafluoride (SF6). The video never aired, but many more of you from around the world will be able to enjoy this right here.

This is a short video tutorial of how to correctly remove the SIM card from the Palm Centro Smartphone. First thing you will have to do is remove the battery cover on your cell phone. Then, take the battery out. Right there is your SIM card access. You will need to remove the Stylus before attempting to remove the SIM card on the Palm Centro Smartphone. Just watch and learn to see how easy it is.

In this video tutorial, Chris Pels will show how to share data in between JavaScript and server-side code by using a hidden field in an ASP.NET page. Next, learn how to use the RegisterHiddenField method in server-side code to programmatically create a hidden field on the client. In addition, see how to programmatically create a HiddenField server control for sharing data on an ASP.NET page. Finally, use the RegisterArrayDeclaration method to create a container in server code for storing mult...

In this video tutorial, Chris Pels will show how to extend the standard set of ASP.NET configuration settings with your own XML configuration elements. First, see how to create a configuration section handler which is required to interpret and process the information in custom XML configuration elements. During this learn how to use declarative model for defining the behavior of a configuration section handler. Next, see how to add a custom section handler and custom elements to an ASP.NET co...

In this video tutorial, Chris Pels will show how information can be passed from one page to another using a query string. First, see how to construct a query string including variable names and values from information on a data entry form. Next, see how to access the query string information when the page is posted including how multiple query string variables are handled. As part of the server side processing of query string information, see how to implement validation for existence of query...

In this video tutorial, Chris Pels shows how to create a Cross Page PostBack in ASP.NET, where a control on a source page raises a PostBack event to a different target page. First, learn how to configure a Button control to PostBack to a different target page. Then, learn how to get information from controls on the source page with the PreviousPage property and the FindControl method. Then, learn how to use public properties on the source page to expose data to the target page, and learn how ...

Notice: This is probably not new to many people. This *IS* new for some people however, and meant for them! Post interesting cameras you find.

When an iPhone is lost or stolen, it's imperative to start tracking it via Find My as soon as possible, whether that's from a computer, tablet, or someone else's phone. However, if it's stolen, there's a good chance the thief or robber turns on Airplane Mode, blocking all communication with the iPhone. If this is a scary thought, you can prevent thieves from accessing Airplane Mode altogether.

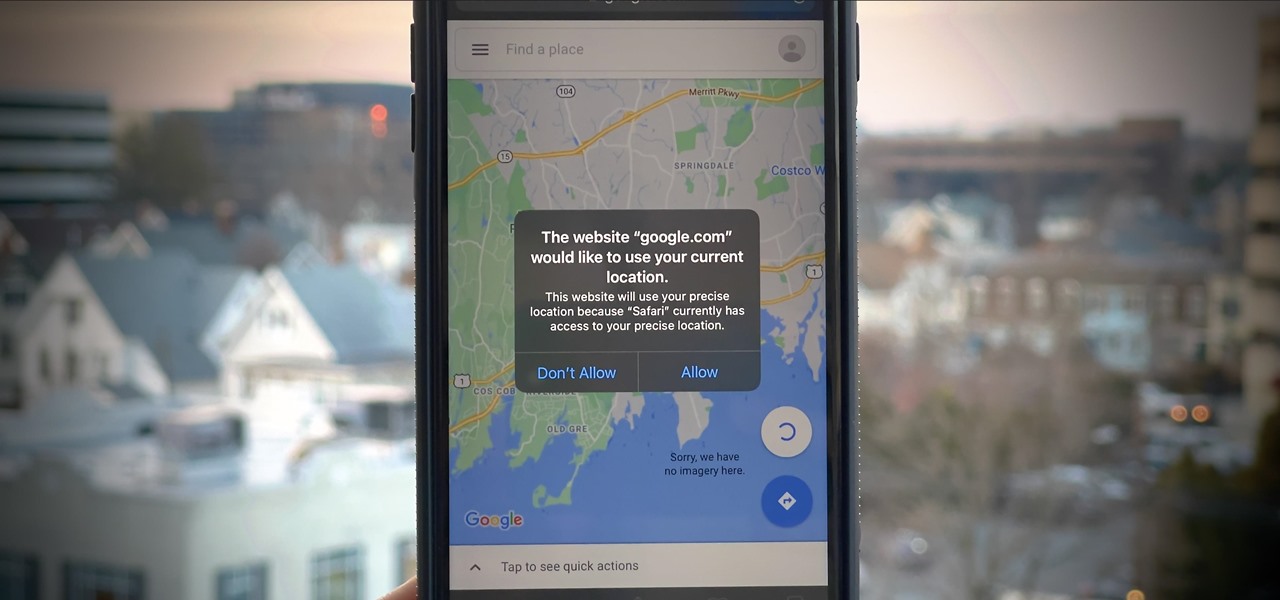
If you surf the web on your iPhone, you no doubt run into this problem all the time: a website wants your location. It can happen when performing a location-based task, such as using a store locator, or whenever a web app just wants to deliver better ads or local recommendations. If you're tired of allowing or denying permission each time, there's an easy way to stop the annoying security pop-ups.

In the tech world, our data is always under attack. When you download and install a new app, it can be difficult to know what information the app is actually accessing. Thankfully, a new emphasis on privacy in iOS 14 changes the game, exposing more of what your apps want access to — and even changing some behavior along the way.

Many apps on your iPhone want to use your location, most of which are for valid reasons. But some apps can function perfectly fine without location permissions, while others have no business even requesting it. If you want to be more selective about which apps and services you give away your coordinates to, the best thing you could do is start from scratch.

SSH, or the secure shell, is a way of controlling a computer remotely from a command-line interface. While the information exchanged in the SSH session is encrypted, it's easy to spy on an SSH session if you have access to the computer that's being logged in to. Using a tool called SSHPry, we can spy on and inject commands into the SSH sessions of any other user logged in to on the same machine.

As fun as Twitter is, it can also quickly turn scary. Anonymous, aggressive, and troll accounts can attack you for your tweets and stalk your every move. While you could make your profile private and block users, there are lesser-known privacy and security features that you can switch to improve your safety online.

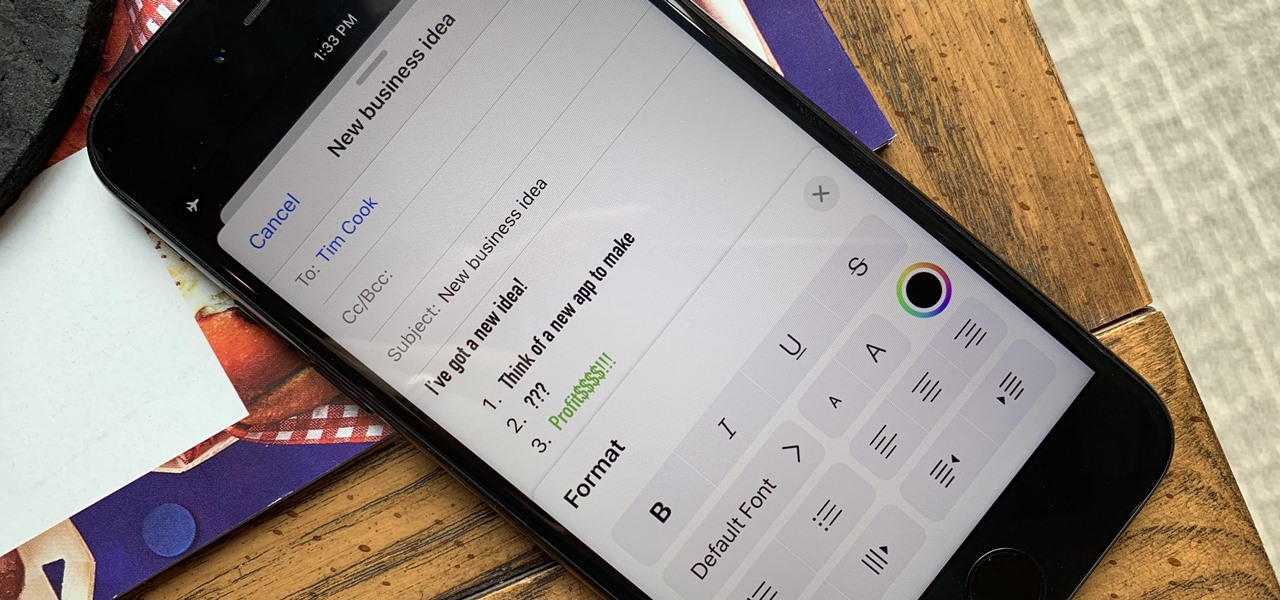
Although Mail didn't get a massive update in iOS 13, the new formatting and attachments toolbar makes it easier to stylize your messages and get quick access to files you'd like to send. It even includes the excellent document scanner built into iOS, so you can use your iPhone to turn a physical document into a PDF and attach it to your message — all from within the Mail app directly.

The idea of squeezing your phone might have sounded a bit out there when it was new, but it's now a hallmark feature on Pixel devices. As useful as it is for summoning the Google Assistant, however, it certainly would be nice to be able pick and choose what action is triggered by squeezing the phone. Well, now you can.

UAC is something we've all dealt with on Windows, either as a user, administrator, or attacker. It's a core feature of the Windows security model, and for the most part, it does what it's supposed to. But it can be frustrating as a hacker when attempting privilege escalation, but it's easy enough to bypass UAC and obtain System access with Metasploit.

By far the most significant development for AR in the coming months and years — the development that will drive AR adoption — will be our reliance upon the AR cloud.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, but a hacker can surgically disable a webcam or other Wi-Fi connected device without disturbing the rest of the network.

It's easy to run Kali Linux from a live USB on nearly any available computer, but many publicly accessible laptops and desktops will be locked down to prevent such use. School, work, or library PCs can be secured with a BIOS password, which is often an easily recovered default password. Once you have access, though, you can use a USB flash drive to run Kali live on any PC you find.

Don't think because your MacBook is using FileVault disk encryption your device is secure or immune to hackers. Here's how to find out if that FileVault password is strong enough to withstand an attack from a motivated attacker.

Over the years, we've seen security breach after security breach, as well as high-profile data scandals where collected personal information was misused by companies. Apple makes customer privacy a priority, so there have been few issues to worry about when it comes to its services on your iPhone. However, there are still plenty of privacy settings to explore and change, especially within Safari.

While there are a variety of privacy-focused search engines available like StartPage and DuckDuckGo, nothing can offer the complete trust offered by creating one's own search engine. For complete trust and security, Searx can be used as free metasearch engine which can be hosted locally and index results from over 70 different search engines.

Between the Cambridge Analytica scandal and the revelation that Facebook logs your calls and text history on Android, many are considering joining the #DeleteFacebook movement. But it can be difficult to leave the site, because so much of its content is only available to active users. If you want to keep in the loop without sacrificing your privacy, you'll want to follow the steps below.

After finding and monitoring nearby wireless access points and devices connected to them, hackers can use this information to bypass some types of security, like the kind used for Wi-Fi hotspots in coffee shops, hotels, and in flights high above the ground. By swapping their MAC address for that of someone already connected, a hacker can bypass the MAC filter and connect freely.

Waze is the go-to navigation app for millions of drivers, and it's easy to see why. Benefits such crowd-sourced traffic data, police trap locations, and road work avoidance are just the tip of the iceberg. It can almost be overwhelming, but with these simple tips, you'll master Waze and start navigating like an expert in no time.

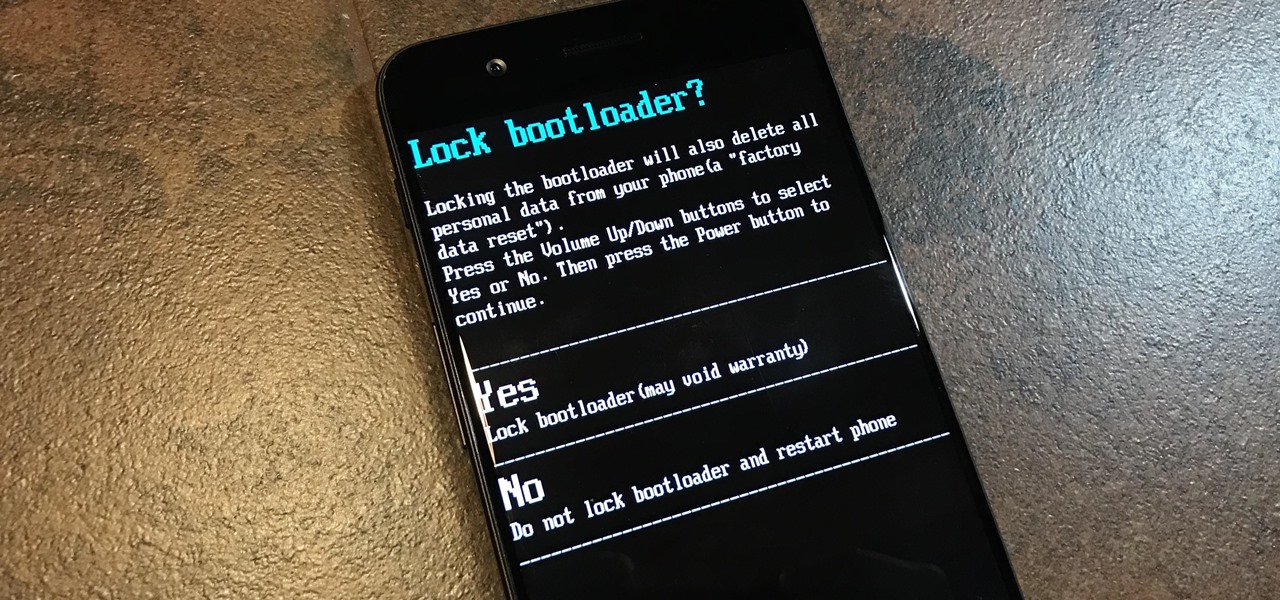
To please those of us who love to mod and root our Androids, OnePlus has made both the OnePlus 5 and 5T relatively easy to customize — so much so that the 5T topped our list for the best phones for rooting. Unfortunately, unlocking the bootloader and using root to modify the firmware on your OnePlus 5 or 5T makes it hard to update to a new firmware such as Oreo when compared to stock.