The personal computer is a strange and powerful entity, capable of bringing great joy. Just as often, you probably want to chuck the damn thing at the wall because it doesn't work right. If you want to pull a prank on a friend that will really upset them, messing with their computer is one of the best ways to do it. This hilarious video will show you how to do three great PC pranks quickly and easily, including changing the contrast on the monitor and pretending to edit websites using Javascr...
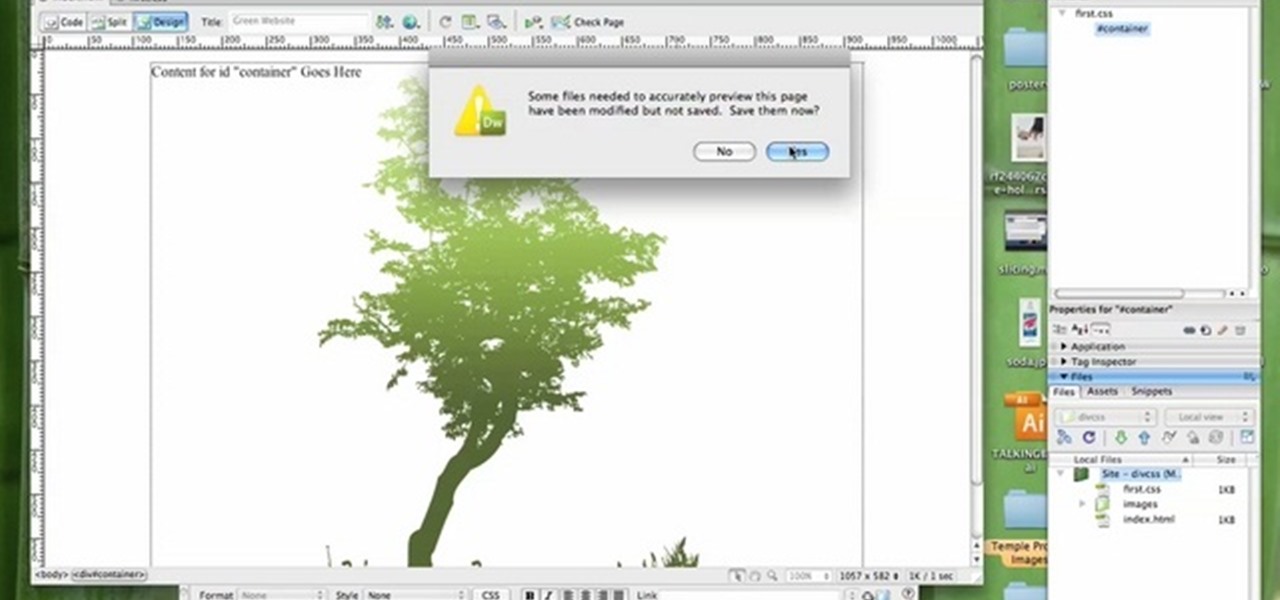
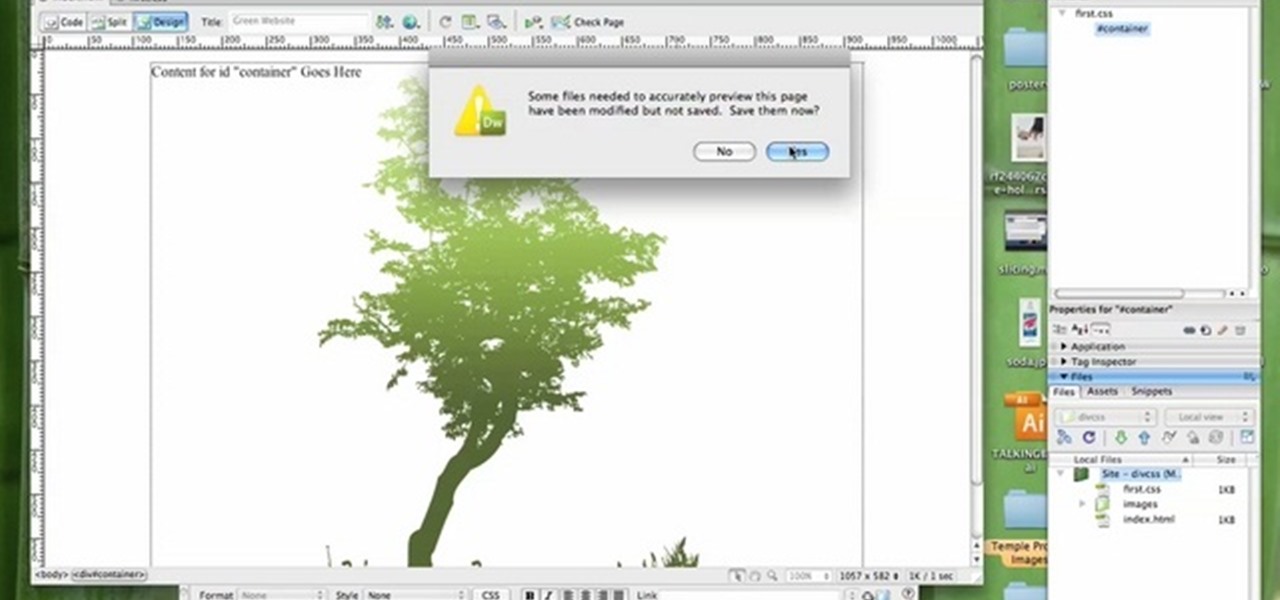
In this tutorial, we learn how to create a website with external CSS and HTML. Start off by managing your site like usual, then create a new HTML document and new CSS document. Now, name both of these to what you would like, then link them both together by linking the CSS in your HTML document. Now, make a container div, which is what will center your main document. Change your different settings so your div will be exactly how you want it to be. Next, make a banner for your page and set the ...

Lady Gaga is definitely in shape. No one can deny that. But how does she do it? How does pop music's most popular artist stay in perfect shape? How does she get those great looking abs?!?
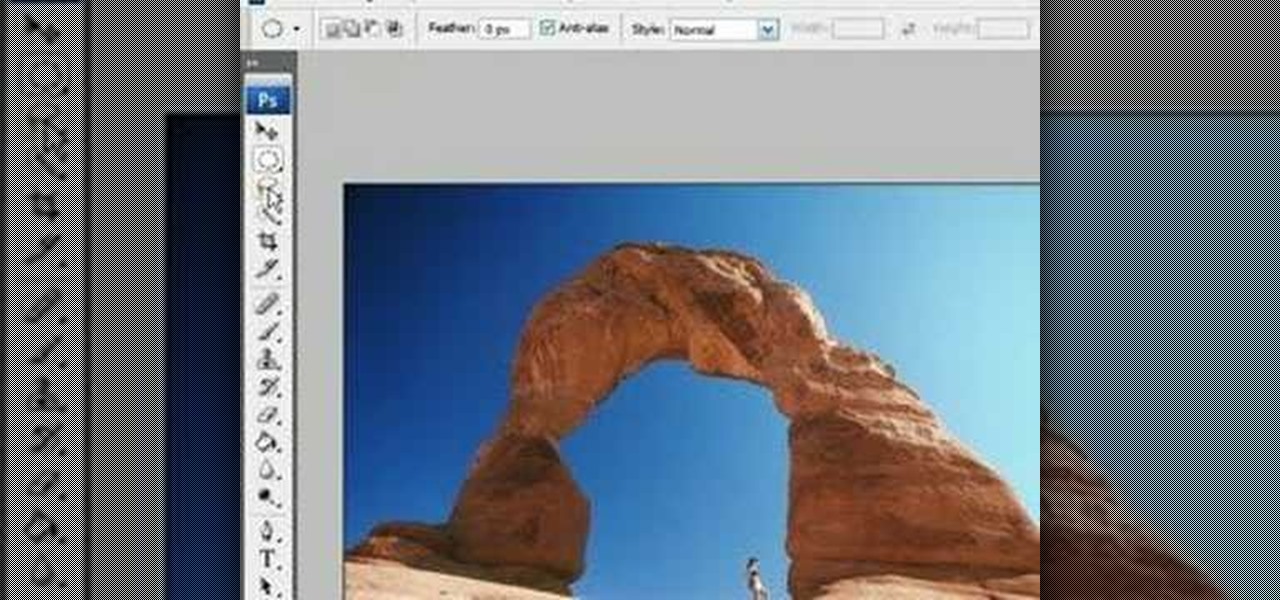
Adobe Photoshop is the industry and personal standard for editing photos on a computer. If you have a digital camera, or ever want to have a digital camera, you need to know how to use it. This video series will show you everything you need to know about using Photoshop's many tools and options to do just about anything you want to a photo.

If done wrong, a backflip could be devastating. But if done right, a backflip just might make you the coolest person ever. This is a unique backflip tutorial that uses both video examples and instructional text. See how to do a backflip. Follow these steps, one by one, to see what you're doing wrong.

It can be hard finding fellow singles in the suburbs but it can be done! Keep your eyes peeled and make sure you are out and about meeting new people in public settings. Don’t forget about your online or in print options.

The check just arrived; now what? Whether you sipped tap water all night or ordered a rare bottle of wine, we have an answer. Learn how to avoid over paying. Follow proper bill splitting etiquette with this how to video.

Most augmented reality experiences are purely visual, with spatial audio gaining in popularity to make visual experiences more realistic. However, leveraging the sense of touch may be the next frontier for AR experiences.

Live Photos capture the seconds before and after you take a photo, creating a fuller and also unique moment to share with friends and family. Unfortunately, it has been nearly impossible to share Live Photos with non-iPhone users — until now. Thanks to iOS 13, you can easily convert a Live Photo into a video, and even stitch multiple Live Photos together to create one long video.

After joining Google and Huawei in underwriting the UW Reality Lab at the University of Washington in January, it appears Facebook is already seeing a return on its donation.

Gmail conversations, Facebook private messages, and personal photos can all be viewed by a hacker who has backdoor access to a target's Mac. By livestreaming the desktop or exfiltrating screenshots, this information can be used for blackmail and targeted social engineering attacks to further compromise the mark.

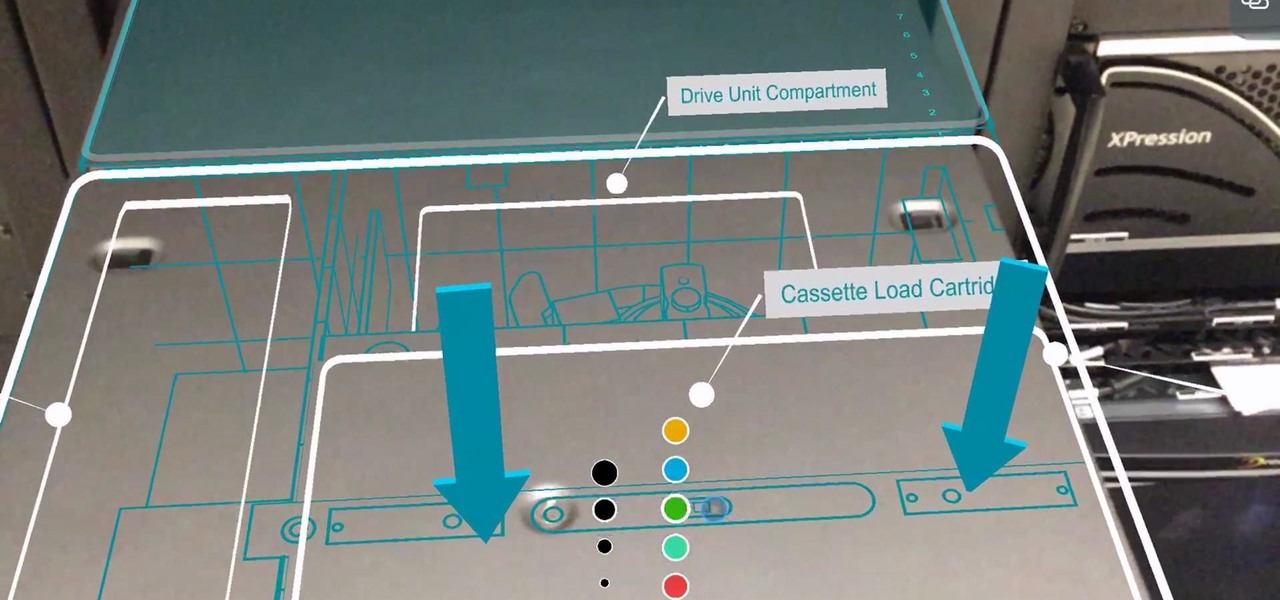
Enterprise augmented reality software maker Scope AR is bringing the powers of its two productivity apps together like the Wonder Twins into the form of a single app.

Single sign-on (SSO) lets users login across different sites without having to manage multiple accounts. I'm sure most of us appreciate the convenience of seeing "Sign in with …" buttons that let us login with a single username. Hackers, however, see a possible avenue for exploitation, and you'll soon learn how an attacker can exploit a SAML vulnerability to assume another user's identity.

If you love to hear yourself talk, you can now enjoy seeing your words materialize in augmented reality with an ARKit-compatible iPhone or iPad.

Digital imaging company OmniVision Technologies and the Hong Kong Applied Science and Technology Research Institute Company Limited (ASTRI) entered the CES fray this week with a new reference design for an augmented reality headset capable of 60 degrees field of view (FoV).

Intel's driverless division will be managed by Israel-based Mobileye, as the chip giant emerges from relative obscurity in the driverless space to become a major supplier after completing its $15.3-billion purchase of Mobileye this week.

The new Leaf with Nissan's ProPilot driverless feature could launch as soon as this year, following a teaser image and video the Japanese carmaker released of its flagship EV yesterday.

Update 6/15: Netflix responded to our request for comment: This [download limit] may vary depending on the title and licensing agreement. There may be limits to the number of titles from the same licensing agreement that you can download at the same time. We will only enforce these limits in cases where our licensing agreements require us to do so.

The LG V20 was released in the fourth quarter of 2016 as a flagship phone with audio capabilities far superior to that of anything else on the market—but only if you have your headphones connected. The single bottom-firing speaker, on the other hand, is just unpleasant to listen to. At first, it was believed there was a software issue with the speaker. However, it turned out to be an issue with the speaker grille impeding sound.

Android's notification system is quite robust, especially now that Google added bundled notifications and quick reply features to Android 7.0 Nougat. However, things can still get quite cluttered when you have several unread messages, which fills your status bar with icons and makes your notification tray take up half of the screen by itself.

Rooted users have been able to remap their hardware buttons since the earliest days of Android, allowing them to change the functionality behind one of the most centralized methods of interacting with a phone or tablet. Up until now, however, non-rooted users have been left out in the cold, meaning these buttons could only perform the functions assigned to them by the device manufacturer.

We tend to think of Google Play as Android's app store—but there's far more to it than that. Not only does it allow you to purchase apps and games, but you can also buy movies, music, books, and even devices, plus there's always those pesky in-app purchases that it also handles.

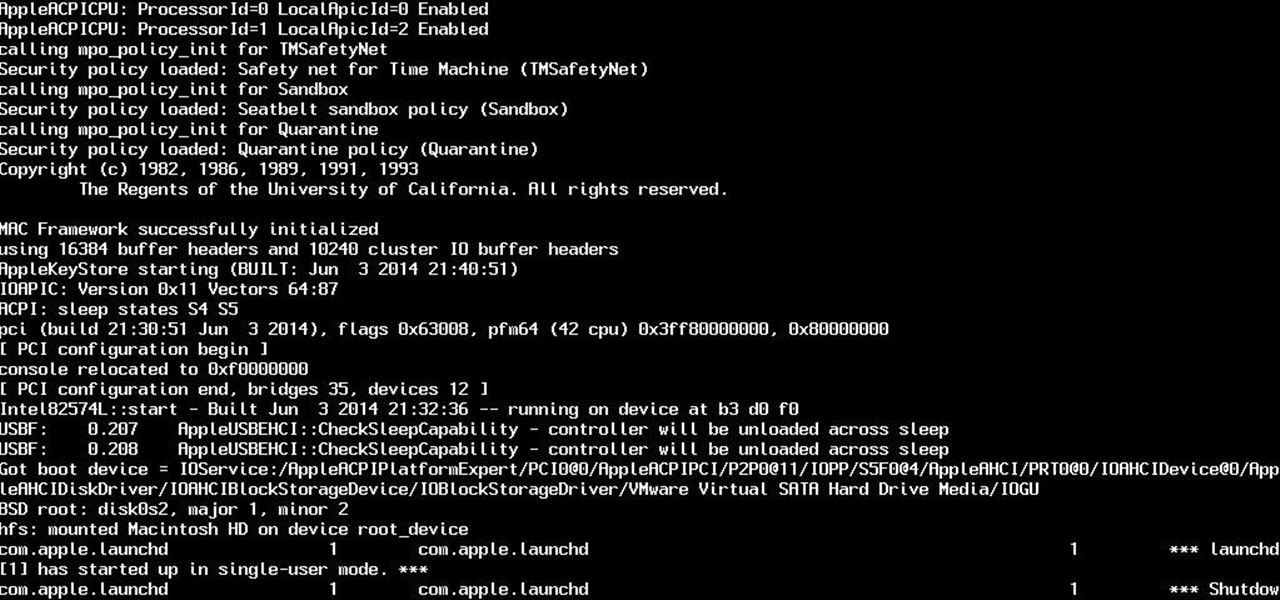
So yeah. Its AugustFackYou and I felt like posting today and being an active member of the community. After reading this please tell me if you have any comments on what I can do better or if this method is bad. Anyway today I will be showing you how to get root on a mac. I managed to become an administrator at my school with this and one other method.

Starting in Android 4.3, Google added some code to AOSP that tagged your internet traffic when you were running a mobile hotspot, which made it incredibly easy for carriers to block tethering if you didn't have it included in your plan. But as of Android 6.0, this "tether_dun_required" tag has been removed, which means you no longer have to edit a database file to get tethering up and running.

Over the past decade the Internet community has been witness to the rise of many new forms of online interaction. These new technologies have given rise to anonymous networks (like TOR), black markets within the deep web network (like the Silk Road), and even forms of digital currency, or more accurately crypto-currencies, such as Bitcoin. All of these technological advancements have contributed to securing users around the world and protecting their privacy. Therefore it is no surprise that ...

The buttons on most Android devices are laid out (from left to right) in a Back, Home, Recent Apps format. Samsung is the lone exception to this rule, which flip-flops them, so this can make for an inconsistent experience if you own multiple Android devices.

Collaborating with other people can be a pain, especially if you have to share one device between the entire group. Usually when you're creating a new design or trying to edit a mockup, you end up hunched around a single screen or end up emailing revisions back and forth, which can be difficult when you're short on time.

One of the Note 3's best features is Multi Window mode, which allows users to display more than one app on the screen at the same time, taking advantage of the large and high-resolution display.

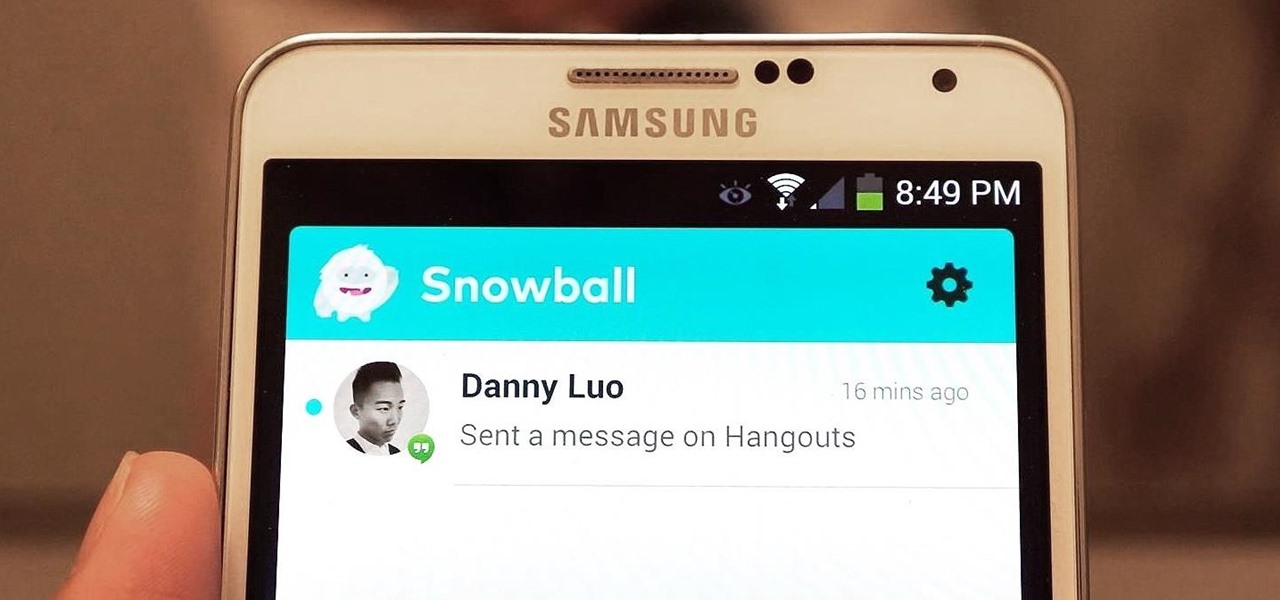
Your favorite instant messaging service might not be your friend's preferred choice of communicating, and your sibling might prefer yet another. So when they send you messages via different apps, it's like having one address but multiple mailboxes on a single porch.

A dead British science nerd figured out the best way to cut a cake to preserve maximum freshness, and it's pure genius (well, sorta). His name? Sir Francis Galton, a polymath infamously known as the founder of eugenics, and apparently owner of a very big sweet tooth.

There are a lot of great music apps available on Google Play for your Android device, each usually specializing in one feature or another, and we’ve shown a bunch of them. There's everything from floating controls to equalizers to deeply integrated streaming, but what if you want all of those features jam-packed into a single app?

In early 2000, at the age of 19, Noah Kalina began taking a photo of himself with the same facial expression—every single day. Six years and over 2,000 photographs later, Kalina turned his project into a time-lapsed montage on YouTube. In just one day, his video received over a million views.

Search Engine Optimization is important for every successful SEO or blogging campaign. Therefore it is required to be implemented in the correct manner. Google consider many factors while ranking a webpage and it keeps on changing. Some of the common SEO mistakes which you must avoid are as follows:

Facebook has been looking to launch a new product for a while now, and it seems they've finally realized what they're best at—being as creepy as possible. If you thought your boss checking out your girlfriend's beach photos was weird, Facebook's new Graph Search has only upped the ante. Now, I don't want to be an alarmist, because I'm sure there are a bunch of great things a Facebook search would find. If you're single, perhaps you could search "Girls that are single that like Goodfellas." Th...

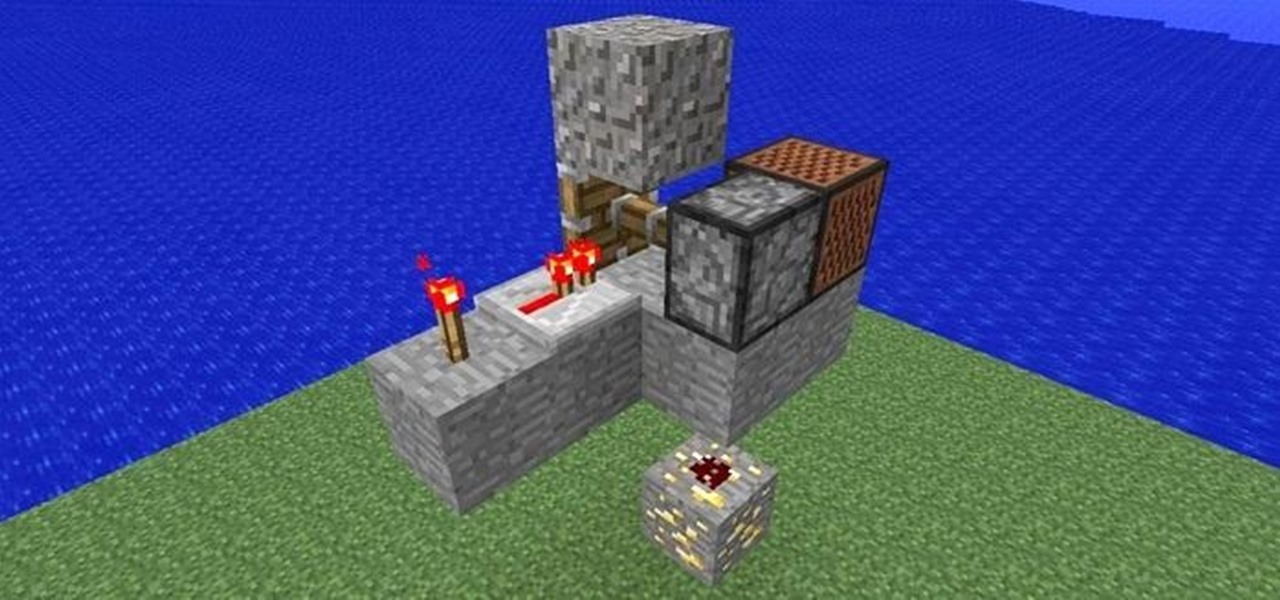
I saw Maro post about a trap on YouTube today, so I thought I'd post one here that I just invented. Since we are friendly at WonderHowTo, the TNT has been replaced with a note block. Step 1: Bait

During my early elementary school years, origami was my go-to pastime. When it came to learning about it in art class, I ventured out well past the basics that were being taught.

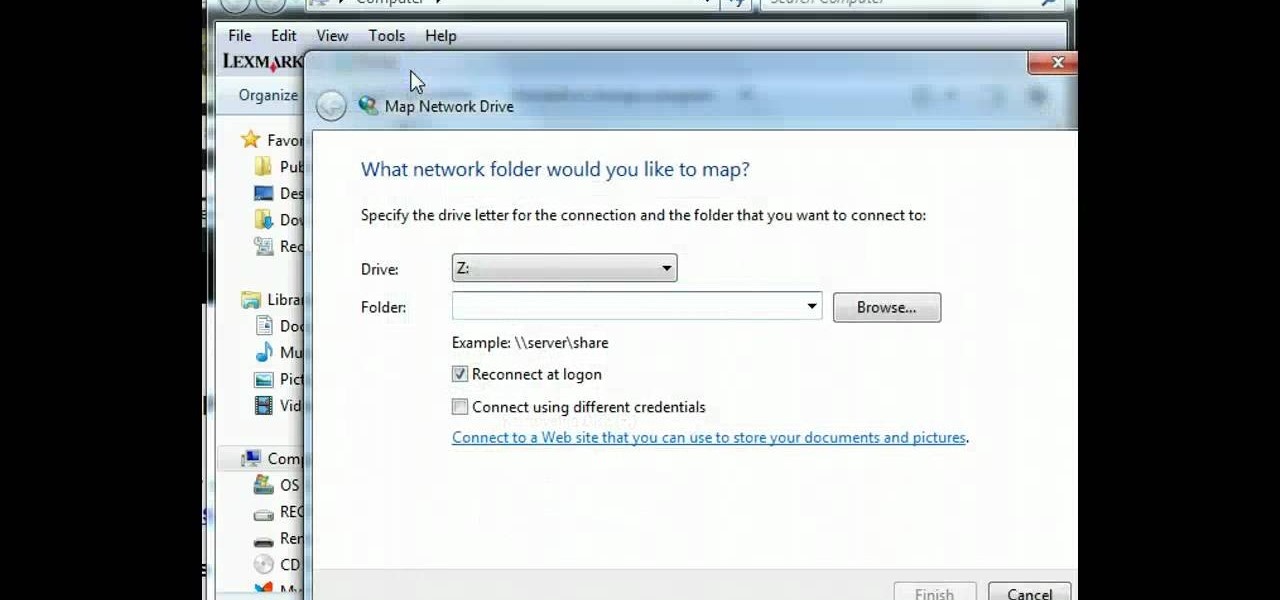
In this tutorial, learn how to map a network drive on your personal computer and make your life easier and more organized. If you need to map your system for any reason, check out this video. This video will give you a complete overview and step by step in just a few short minutes so you will be ready to map your network in no time.

If you like to shop online then it is extremely helpful to have a PayPal account to safely make your online purchases. Help reduce your risk of identity theft by using protected methods like PayPal when your credit card information is involved.

Learn how to do single leg squats with this fitness tutorial. Single leg squats are great for toning and building muscle in your legs and glutes. Watch this how to video and you can get in shape with single leg squats.

In this language tutorial you will learn how to use personal pronouns in biblical Greek (Koine). This is a perfect lesson for the scholar looking to study the ancient language of Greece. Watch this how to video and you will be speaking the biblical Greek language in no time.