Over the weekend—just days before Apple's big event—an actual iPhone 6 leaked on Chinese site cnBeta. Again, nothing here that we already didn't know about—Sapphire screen, round(er) corners, larger display, and new button stylings. Below are images of the new iPhone 6 next to the current iPhone 5S. We can clearly see the protruding camera module as well as sections on the top and bottom of the back where the antennas will be housed. A second source was able to put together some videos, as yo...

One of the best features of Android is the fact that it's open-source, giving developers the ability to use it on pretty much any device they can think of, like on a Windows PC using Andy. That's what drove the creators behind the Android-x86 project to port over the mobile OS to any computer running an Intel processor.

This past year, Facebook spent $19 billion purchasing the popular messaging app WhatsApp, and for good reason. Mark Zuckerberg isn't going to spend that type of money on just any application. WhatsApp is widely popular and frequently used by more than 500 million users worldwide, which is almost twenty percent of the Earth's population.

Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.

Taking pictures, sharing your location, and making calls are easy enough to do with an Android device, but for the most part, they all require your screen to be on with some sort of swiping and pressing actions. Dedicated shortcut keys are virtually non-existent on any modern day phone, but their utility is something that can be very useful.

I'll give Samsung credit where it's due—the stock keyboard on the Galaxy S5 is actually pretty nice. There's a dedicated number row that resides at the top (something that the Google Keyboard needs a hack to achieve), and various settings exist to make switching between languages a breeze.

Android enthusiasts have their own opinion as to whether you need antivirus software on an Android device. This debate will never end, provided that Android malware is in existence. This guide is not here to say, "Yes, you need antivirus," or "No, you don't." It's to give you all the facts, so that you can make a decision as to whether or not you need antivirus on your Nexus.

Greetings, my friend. Welcome to Null Byte. I am Dr. Crashdump. Linux will be talked about a lot in Null Byte. It's used in most tutorials on this site, actually. You should learn how to use Linux as soon as possible, but where do you start? No worries. Let's figure that out.

If hearing the names of classic PC games like Commander Keen, Fallout, Master of Orion, and Wolfenstein 3D send you into a fit of nostalgia, then DosBox Turbo is the perfect app for your Android device.

E3, or the Electronic Entertainment Expo, is the 20th annual trade show for video games and gaming tech. The event takes place on Tuesday, June 10th at the Los Angeles Convention Center, and you can watch a live stream of the event on Twitch.

Once you unlock your bootloader and root, you're left with one more hurdle to overcome, and that's getting S-Off.

If new leaked images are to be trusted, an iPhone with a display around 5 inches will be released later this year. From Italian site Macitynet, images show a device that's stated to be the new iPhone 6 side-by-side with the new Samsung Galaxy S5. A couple of weeks ago, I showed you leaked internal emails and memos that suggested Apple was concerned with not only Samsung's marketing strategy, but about the industry trend towards larger devices.

YouTube makes money hand over fist every year selling ad space to companies, but unless you're reaping those benefits, they can be pretty annoying. Luckily, there is a simple way to get rid them on your rooted HTC One with Xposed and YouTube AdAway.

First, they came for our Pokémon...now it's an emoji takeover. Adding to the flurry of Google related April Fool's Day jokes, Chrome for Android and iOS has a new hidden functionality: translating the web to emoji!

Part of the reason bacon tastes so good is because of its high fat content, but that also means that it shrinks significantly when you cook it. How much it shrinks depends on how fatty it is and what method you use to cook it. Bacon cooked on the stovetop shrinks quite a bit more than bacon that's baked in the oven. DIY blog Franalan tested a Pinterest tip that claimed rinsing bacon under cold water before cooking it could reduce the shrinkage by up to 50 percent. Yes, we just wrote about how...

With Chromecast-capable applications slowly seeping into the market, it's difficult to find useful ones that we might use on a daily basis.

Welcome back, my budding hackers! As you know, I firmly believe that to be a true professional hacker, you need to be proficient in Linux. This is for a number of good reasons.

Many of us were left scratching our heads when the iOS 7 update removed the Twitter and Facebook options from the Notification Center. Allowing you to quickly tweet and post Facebook updates, these were features used, and missed, by many—including me.

Sometimes I actually search Google Images for things other than GIFs and pictures of athletes' extremely hot wives. Google Images has helped me with school projects, work, and proving my friends wrong on numerous occasions. Unless you're strictly using it for the latter, you're going to have to be aware of copyrights.

Welcome back, my rookie hackers! The more we know about a system or network, the better our chances of owning it and not leaving a trace for investigators to follow. One of the often overlooked sources for information is the Simple Network Management Protocol (SNMP). Many rookie hackers are not even aware of it, but it can prove to be a treasure trove of information, if you understand how it works and how to hack it.

Welcome back, my rookie hackers! A short while back, I began a new series on database hacking, and now it's time to continue and extend your education in that field. As you know, the database contains all of the most valuable info for the hacker, including personally identifiable information, credit card numbers, intellectual property, etc. So, it's the ultimate goal of cybercrime and the APT hacker.

Welcome back, my budding hackers! In my continuing series on Linux basics for aspiring hackers, I now want to address Loadable kernel modules (LKMs), which are key to the Linux administrator because they provide us the capability to add functionality to the kernel without having to recompile the kernel. Things like video and other device drivers can now be added to the kernel without shutting down the system, recompiling, and rebooting.

Ladies and gentleman, it's official—"Selfie" has been named Word of the Year by Oxford Dictionaries.

There's no reason to wait for Halloween to play with dry ice. It definitely creates a creepy fog-like effect when you add a little water to it, but there are some other really cool things you can do wit dry ice. Here are just 5 non-Halloween ways to use dry ice for tricks or pranks.

Welcome back, my budding hackers! Previous to this tutorial, we've focused mostly on hacking the target system. If we're successful in owning the target system, we'll then want to make certain that the system administrator doesn't know we were there, and that he or she cannot track us.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

There are hundreds of sites that host high-res wallpapers for your Android's home screen, but most of us stick with the same old drab stock wallpaper because we're too lazy to go hunt for new ones.

Welcome back, my neophyte hackers! Several of you have written me asking how to crack passwords. The answer, in part, depends upon whether you have physical access to the computer, what operating system you are running, and how strong the passwords are.

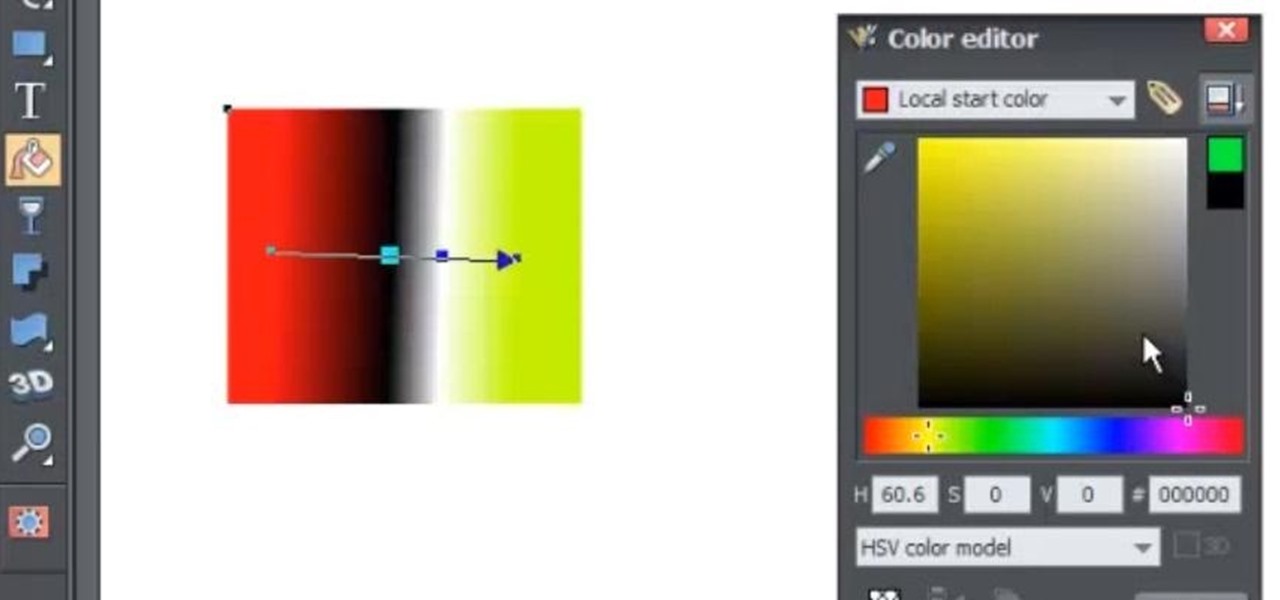
The fill tool will allow you to alter the appearance of objects in your web design document and can be very useful for marketing purposes. The fill tool can be used to give objects one solid color for simple designs.

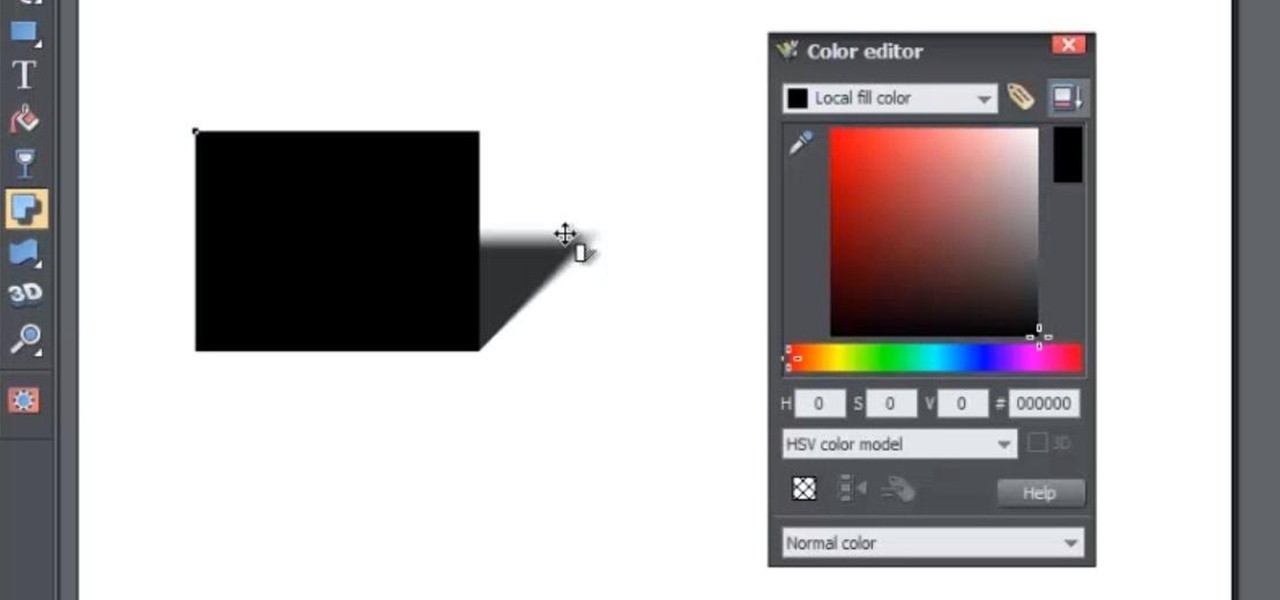
In this web design tutorial, you will learn to use the Xara Shadow Tool. Use the Xara Web Designer shadow tool to add shadow types such as: floor, wall and glow.

Legal Services A group of lawyers refused to provide legal services to needy AARP members for $30 per hour, but when asked to do it for free, they readily agreed.

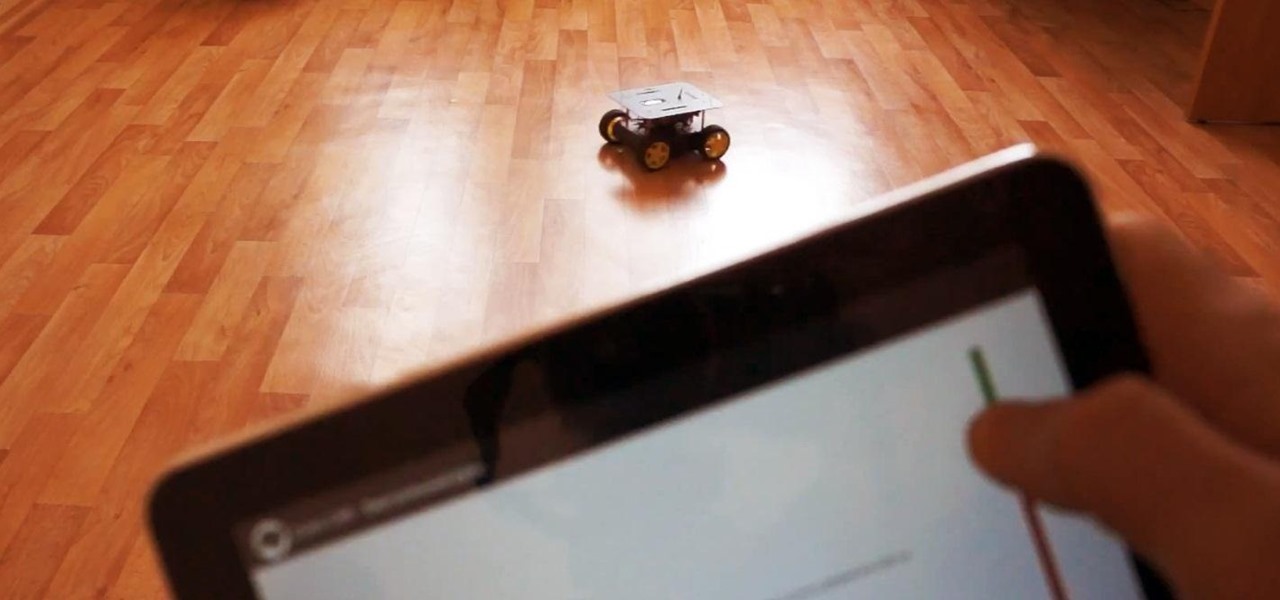
Thanks to its open-source platform and easy-to-use hardware and software, there's literally thousands of Arduino projects detailed online for anyone to make—a magic mirror, DIY polygraph machine, and hotel-hacking dry erase marker just being a few examples. Hell, you can even make the Daft Punk helmet.

The lovely Kato of Steampunk Couture has gone hardcore. For those who prefer to exercise their imaginations a bit more, Voila! Veronique Chevalier in Gearhearts Steampunk Glamour Revue- click here should do... A recent kerfuffle unfolded on facebook's Steampunk Revolution group when a discussion was started by Steampunk R &D''s very own Austin Serkin on the subject of Kato's new foray into steampunk porn, which was, ahem, examined in detail. (Well, figuratively, not literally, since her websi...

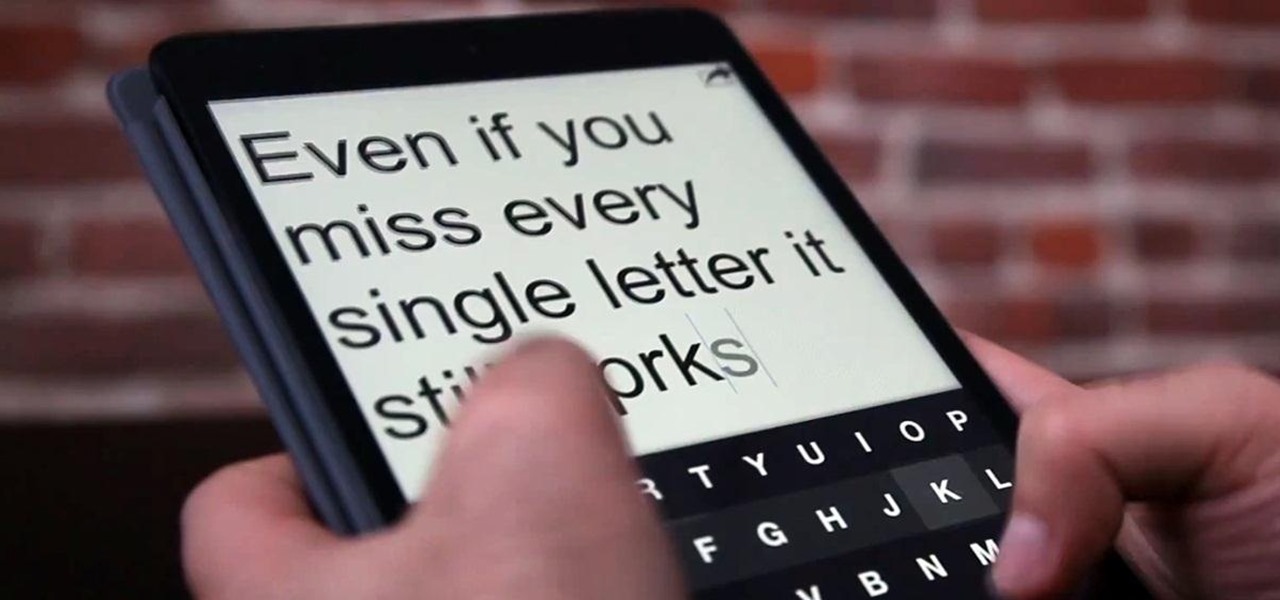
Who doesn't hate Auto Correct? There's nothing worse than hitting 'Send' only to realize that your phone betrayed you by changing a word so that your message doesn't even mean the same thing anymore—especially when it's going to someone like your boss or parents.

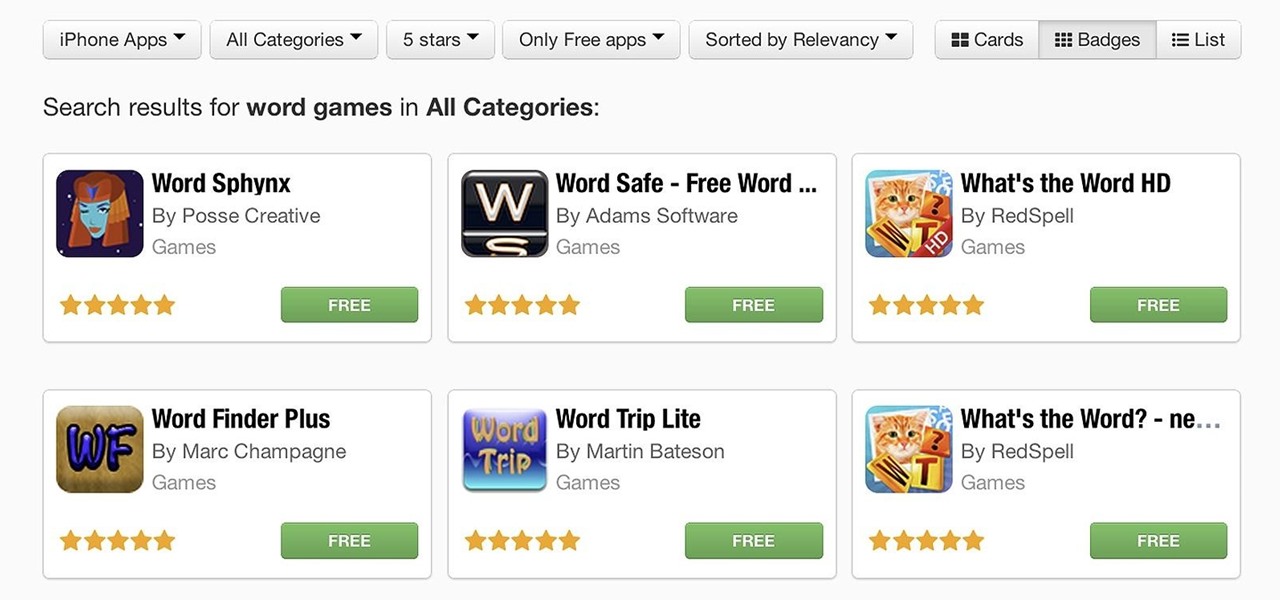
If you have an iOS device, chances are you've spent a decent amount of time in the App Store—without at least a few apps, smartphones are pretty boring. There's an app to do just about anything you could ask for, but the problem is finding them. Searching the App Store sucks.

We've talked before about EXIF data—or metadata—attached to photos and how it can expose information about your location, what type of device you're using, and even the device or camera's unique identification number.

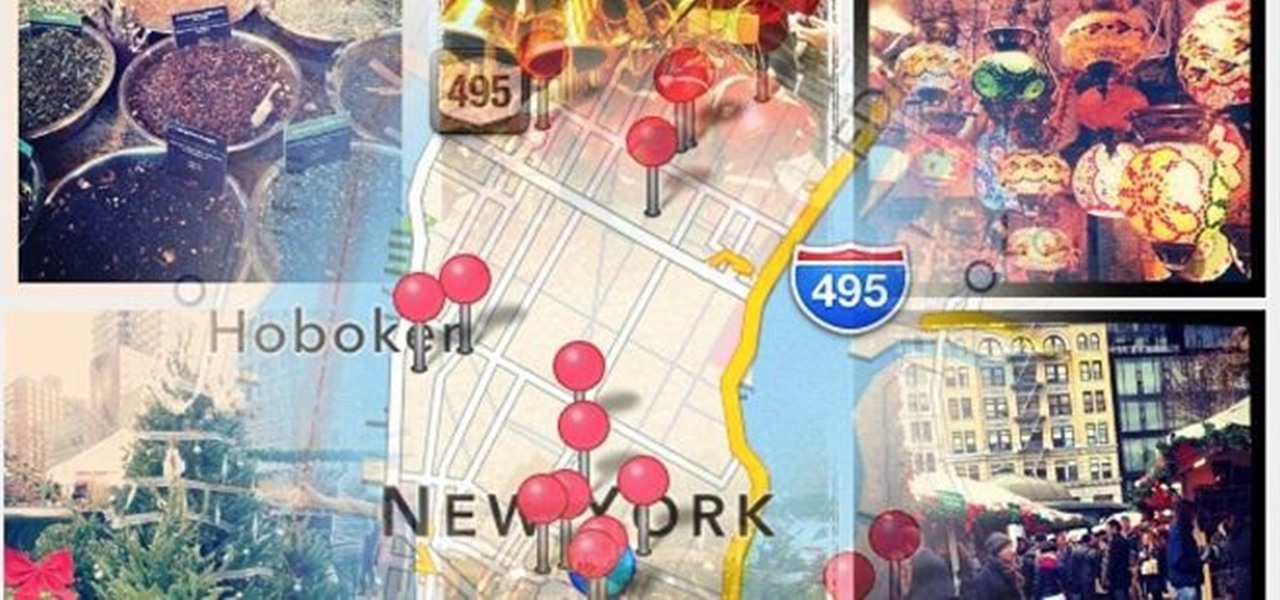
The only thing worse than not having any plans is not even knowing where to begin making them. Sure, you can check Yelp or one of countless other review sites to find a great spot, but there's no way of knowing what the vibe is like before you get there. Is it crowded? Are people having fun, or does it look pretty lame?

Here I have used some very smart and easy to use nail art decals to create this lovely zip nail art design !

Like a computer, your brain can store and process large amounts of information. It can remember names, solve math problems, and save tips that you might need at a later time.

I have never been the most artistic person in the world, but never overlook a great piece of work when I see one. With George Lucas selling the Star Wars franchise to Disney for more money than I could make in ten lifetimes, it's safe to say the franchise has a lot of fans.