Sick of your school dictating what websites you can visit and which you can't? Learn how to bypass school web filters and get on any website of your liking with help from this free video. Surf the web with total freedom in just a few simple steps! Bypass school filters and get on any site you want.

Now that you've set up your email accounts for your new domain, how do you get your website files to your server? One way is to simply use Cpanel's File Manager.

In this video tutorial, Creative Cow leader Tony Ross revisits the tutorial how to build a basic site about Colors in Flash. This version is created using Actionscript 3. The basic principles learned from this tutorial will enable the user to create a variety of simple websites. Elements covered are basic Actionscript 3, navigation, labels, button and graphic symbols. Build a basic site using ActionScript 3 in Flash.

Watch the video to learn how to let the user choose the background of the site. This is a cool feature that makes your site more user friendly. Let the user choose the background in HTML.

You've had a massive hard disk failure.. ...in your PC or laptop and like a large number of people who think it will never happen to them...you did not have a backup of those 2000+ family pictures, those hundred of important Word documents, those family videos that you downloaded from the camera then erased from the cameras disk...the inevitable "I'm Screwed!'

The Internet is full of information, accessible with a web connection and a few strokes of the fingertips. The web is perfect for doing research for your college essays, or term papers, or thesis statement.

This morning, I received a message from a friend who was reading a hack log, and she had some questions about the commands used. This got me thinking, as Linux has a ton of commands and some can be archaic, yet useful. We are going to go over everything you need to know to read a hack log and hopefully implant the steps in your head for future use.

For a moment, picture a situation where you want to host some files or images, but you do not want it traced back to you. Perhaps you're working on a project with others and need secure data storage. Anonymity is the new shield of the 21st century—and you best protect yourself. As always here at Null Byte, we are trying to make that happen. Before someone can learn how to root a box, they need to learn how not to be found. I can not stress that point enough.

Cross-Site Request Forgery (CSRF, pronounce "sea-surf") is a common web exploit. However, for unknown reasons it's not used very often. It plays on a given website's trust in a web browser by executing another website's form action, for example, sending money to another person. It's usually placed in abnormal places like HTML image tags.

Six months ago, 1.3 million registered users of Gawker Media had their passwords compromised when the site was hacked by Gnosis. The passwords were encrypted, but 188,279 of them were decoded and made publicly available for all to see. Just three weeks ago, Sony Pictures was hacked by LulzSec, with 1 million passwords taken and 40,000 made publicly available. Comparing the two data sets, Troy Hunt found 88 accounts on both sites that used the same email address, and of those accounts, 67% use...
So precisely what is an affiliate marketer? Essentially, an affiliate marketer has an online site and also refers guests to some other sites, called 'merchants'. When these site visitors buy things, the other websites pay the particular online affiliate marketer a payment, which depends upon online monitoring softwares which monitors web customers purchases.

Want to make money by streaming videos online? Here's three steps to success. Find Good Quality Websites to Submit Videos

My girlfriend was going away for a few weeks, but where she was going, there was no easily accessible Internet. She works mostly on the web, so it was imperative that she have a decent Internet connection during her travels. So, tethering her phone was the only real possibility.

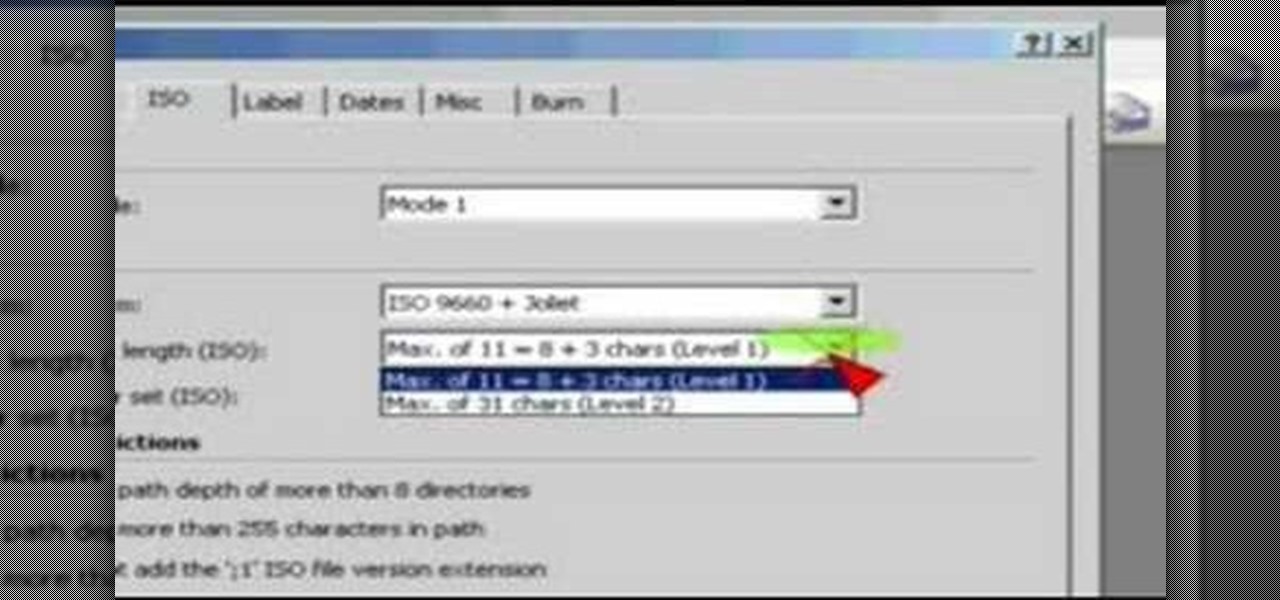
This video uses Nero Burning ROM. First you must open Nero. Then choose Burning ROM. Scroll down to the CD-ROM(BOOT) icon. Click it. From there you choose you ISO image. To do this just browse and navigate to the correct directory where your ISO image is stored. From there be sure to set the emulations to No Emulations and change your available sectors to 4. Next change to the ISO tab. Be sure that it is set to run ISO+Juliet and that the max characters are set for Level 1. Next choose the La...

To make customizing a template as easy as possible, it is important that you pick a template that is closest to what you’re after, this includes the layout, the images and the color schemes. Keep this in mind.

In each day of our life, we see inflammation. We see it during sore throats and abscess formations in our bodies, and even slight tooth pain is a form of inflammation. Sometimes it's good when it fights to protect us from invading organisms, but sometimes it becomes bad when it occurs in inappropriate ways, like acne.

Introduction In the competitive world of today's video game scene, PC gamers are known to squeeze out the best possible visuals in their games. Every few months a new video card rolls out, and RAM is ever increasing; constant upgrading is the norm of staying ahead the curve. One of the most important things a PC gamer looks at is how many FPS (frames per second) he gets. It defines his gaming experience.

Omegaville archeological research site / mgabrys' underground (weekly) challenge submission Rest of flickr set peek at : http://www.flickr.com/photos/87457200@N00/sets/72157629196076400/

How do you like the new site banner? :)

http://www.seonorthamerica.com See how to use social bookmarking sites in your SEO campaigns.

This article is all about creating content. This is a very important concept to grasp because the content that you create for a website is going to be the basis for how you will advertise and promote that website. Content, meaning articles, videos, and even podcasts is now really the new advertising. Instead of traditional types of advertising and instead of the traditional separation between editorial content and advertising, that has gone the way of the dinosaur.

What is Google Dorking? Well, simply put, "Google Dorking" is just an efficient way to utilise keywords in order to perform very specific searches on a given subject. In this case, one would look for websites/servers that are vulnerable to attacks or are configured improperly by using specific search criteria that should yeild results, should it find matches to known mistakes/errors in a website or webserver.

Welcome to the 10th Community Byte session for coding in Python and completing the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

I write for a movie site called Flixist, a sister-site of Destructoid. Basically, I write movie news, reviews, features, and interviews. I wrote this for our feature series Flixist Film School. It's a primer into film editing technique.

Google+ is taking over more and more of Google's core properties. This week, we've seen several announcements from Google blogs about new products, new features, new looks, new integrations. If you're like me, you actually want to know where to go for all the latest information on Google products.

Learning the basics of SEO In this tutorial I will go over the basics of Search Engine Optimisation. The "white-hat-way" ("black-hat" SEO is tricking Google and other search engine providers, this will get you into trouble quick!).

I recently came across this amazing MIT media lab site, Kit-of-No-Parts. Though not directly related to the content Cory has been posting, it is an interesting "craft" approach to technology/science. The site was created as documentation of a student's thesis work in the High-Low Tech research group at the MIT Media Lab:

SSL stands for Secure Socket Layer. It's an encryption standard used on most sites' login pages to avoid their users' passwords being packet sniffed in simple plain-text format. This keeps the users safe by having all of that traffic encrypted over an "https" connection. So, whenever you see "https://" in front of the URL in your browser, you know you're safe... or are you?

In this Null Byte, we are going to be installing Packet Injection capable drivers in Linux. These are the open-source drivers required to sniff wireless traffic, inject packets to crack a wireless access point, and go into "monitor-mode". These drivers are superior because they are the fastest available drivers.

You'll see a lot of Linux action going down here at Null Byte. We use Linux for hacking-related stuff because it provides a more relaxed programming environment, making it easy to write exploits and tools. Linux has many features Windows is lacking, such as full control over the OS right down to the Kernel and massive availability of mature, open source (read: free & tweakable) tools & projects.

The group social networking application Fridge has been purchased by Google, and two of its team members will be moving to Mountain View to work on the Google+ team. Fridge, in addition to being a group social sharing site, has photo and event sharing features. The event and calendar-sharing are popular requested features for Google+ users.

UK-based artist Matthew Nicholson is a man of many talents: designer, photographer, professional free runner and papercraft engineer—and in the latter of which, he generously posts free downloadable DIY kits for your folding pleasure.

When Apple‘s iTunes was introduced back in 2001, it rekindled my interest and purchasing of music. I was so excited by the program that I immediately started converting all my rather large collection of CDs into MP3 tracks. I then sold off my CDs and remaining vinyl albums, and used the money for additional iTunes purchases. iTunes made managing and listening music a wholly different experience. But in the last few years, iTunes has taken a back seat to streaming music services, which I find ...

Luxirare is a site of mystery; the genius behind the intricate and painstakingly photographed projects remains somewhat anonymous, despite her culinary mastery, fashion pieces and e-shop being featured in the likes of Vogue, Lucky Mag, ABC, NBC, and the New York Times. Insanely stylish and original, Luxirare has been blogged about all over the web.
Balloon Library is a great place to learn how to make balloon animals. There are free tutorials and also paid tutorials as well. There is a section for basic, intermediate, and advanced balloon tutorials. Additionally, there is a section for eBooks on balloon twisting and a balloon forum also. It is a site I highly recommend to anyone asking me about learning balloon animals.
This is a page of links to paid to write sites please check back often as new links will be added.

If you want to blow your mind, check out this amazing new tumblr blog devoted to abstract moving stills from classic films. Here is the main site.
The website is brilliant. Downloadable tricks, links to knife artisan sites, it's incredible. It even has tricks for maintenance and care of your knife.

MyShoppingGenie is an online shopping application that can help you find the best deals on products you search for.
This weather site has hundreds of locations. Giving you the benefit of viewing wind-direction, wind-speed, waves, temperature, almost anything to do with wether on the water. Although geared to Wind-surfers, this site is usually accurate and is great for sailing.