Today in Santa Clara, California, at the Augmented World Expo, Scope AR revealed a major new update that will add markerless tracking for their remote assistance application, Remote AR, on standard devices.

In March, we wrote about the growing threat of yellow fever in Brazil. At the time, the disease had killed just over a 100 people. Unfortunately, the disease has only spread since then with many more people infected and more killed.

ProtonMail has long been the favorite of journalists and security-conscious professionals, with Edward Snowden the most famous example. But these days, everyone cares about anonymity, so it's no surprise that ProtonMail currently has over 2 million users. And now the service is even better.

With the Game Developers Conference (GDC) in San Fransisco just a few weeks away, Microsoft Senior Program Manager Vlad Kolesnikov has announced via Channel9 (Microsoft's developer news outlet) that not only will new low-cost virtual reality headsets be coming in March to developers, but that they will be at GDC, too.

We've been hearing some interesting rumors in the last few days that are stirring up all kinds of speculation about the potential upcoming consumer release of the HoloLens. However, MSPoweruser has speculated a bit further past the consumer HoloLens release to a possible HoloLens 2 as soon as Q3 2017.
If you've ever built a piece of IKEA furniture, you're familiar with the confusion that some 2D instruction booklets can create. But neuroscience suggests that they're cognitively overloading, as our brains have to translate their basic flatness into physical reality and that's pretty hard to do. Fortunately, augmented reality has come to the rescue.

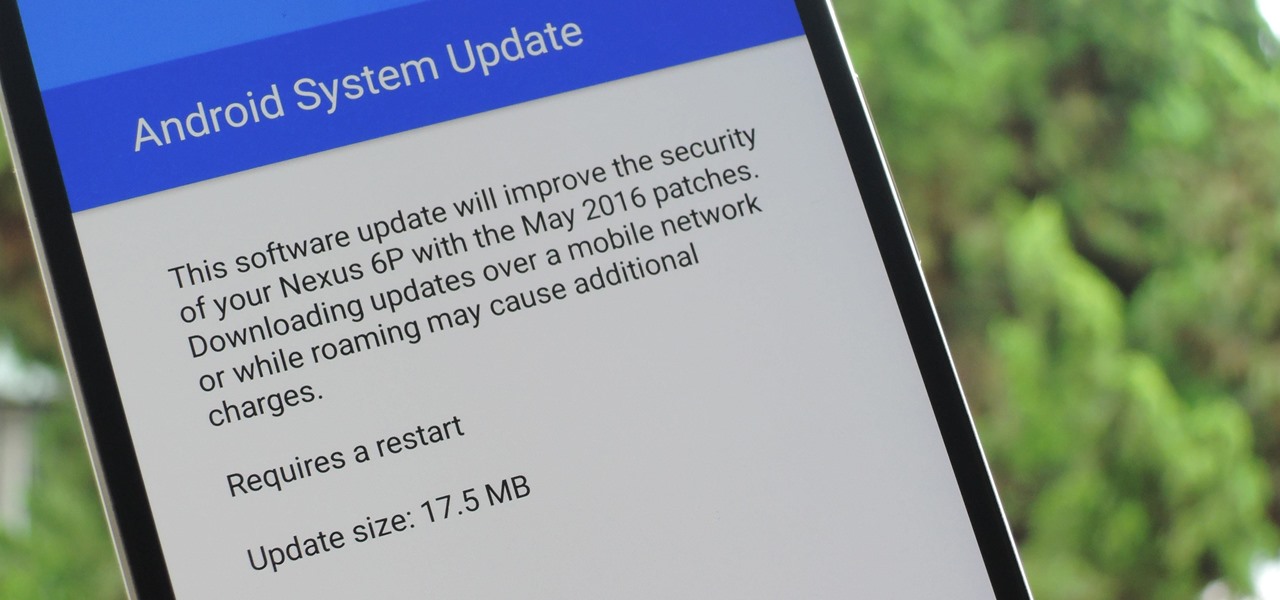
The beauty of Nexus devices is they receive firmware updates faster than any other Android phone, and keep getting updates for years longer than most of the competition. This means that you can always use the great new features that come along with an Android update, and even more importantly, your phone gets monthly security patches to keep hackers and malware at bay.

Sup? Today, we'll be learning about for loops in Java: What they are, how they work, and how to create them.

Hello everybody Joe here. Today I will be demonstrating how you can find XSS vulnerabilities in a website and what you can do with them

There are many reasons to keep adult websites off your iOS device. They can pop up accidentally at the least opportune moments, can give your device malware, and are not welcome in a kid-friendly home.

hello my dear colleagues, I made a visit to nullbyte and found that there is not a complete tutorial about the google dorks, so I felt the need for this tutorial, and seeing that there are many newbies around, so here's a tutorial that will teach you how to use google to hack.

SoundHound's new virtual assistant application, Hound, is gaining a lot of buzz in the tech world—especially after a demo video showed just how awesome it works (it has amassed over 1.6 million views in under a week).

It's been over a year now since Google introduced a visual way to track down which tabs are playing audio in Chrome, something that was previously only available using third-party extensions. However, they still didn't give an easy option for shutting those tabs up without having to stop what you're doing.

Today, I want to share a tutorial on one of the most useful but old methods which you could use to hack websites, that is using the Dot net nuke (DNN) vulnerability . I know some of you already know about this method.

Oops... did you forget to connect to a Wi-Fi network before streaming HBO GO on your iPhone? While those episodes of The Wire may have been absolutely life-changing, your three-digit cellular bill is definitely going to hit you a little harder.

When you're on a limited data plan, bumping up against your monthly cap is a major concern. Overage fees are incredibly high these days, and being throttled down to 2G coverage almost renders a smartphone completely useless.

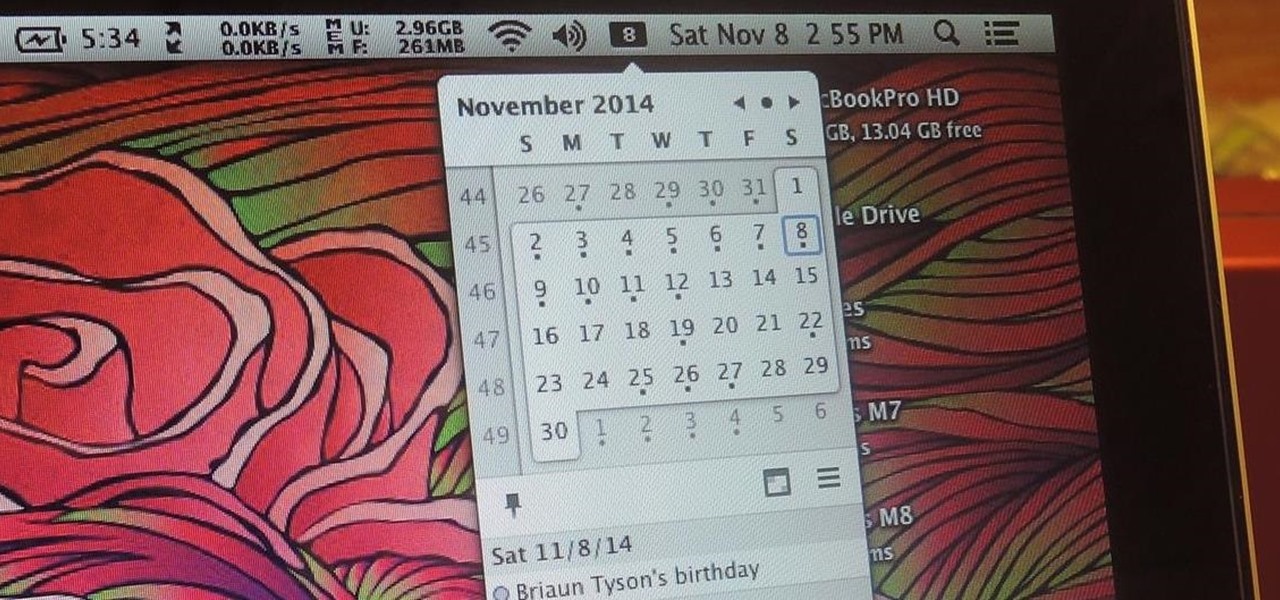
While it's much quicker in Yosemite, the Calendar app for Mac has never been as fast as I'd like. If my schedule is really full, it can sometimes hang when first opening the Calendar.

These days, phone calls aren't always the best way to communicate with others. Maybe you need to reach people out of the country, or you simply want to have a more visual conversation. Either way, there's a reason why video calling has become so popular.

With all of the different websites we use in our day-to-day lives, keeping track of our numerous login credentials can start to become a hassle. This has created a market for password managers that aim to centralize these account credentials and generally streamline the process of logging into our favorite sites.

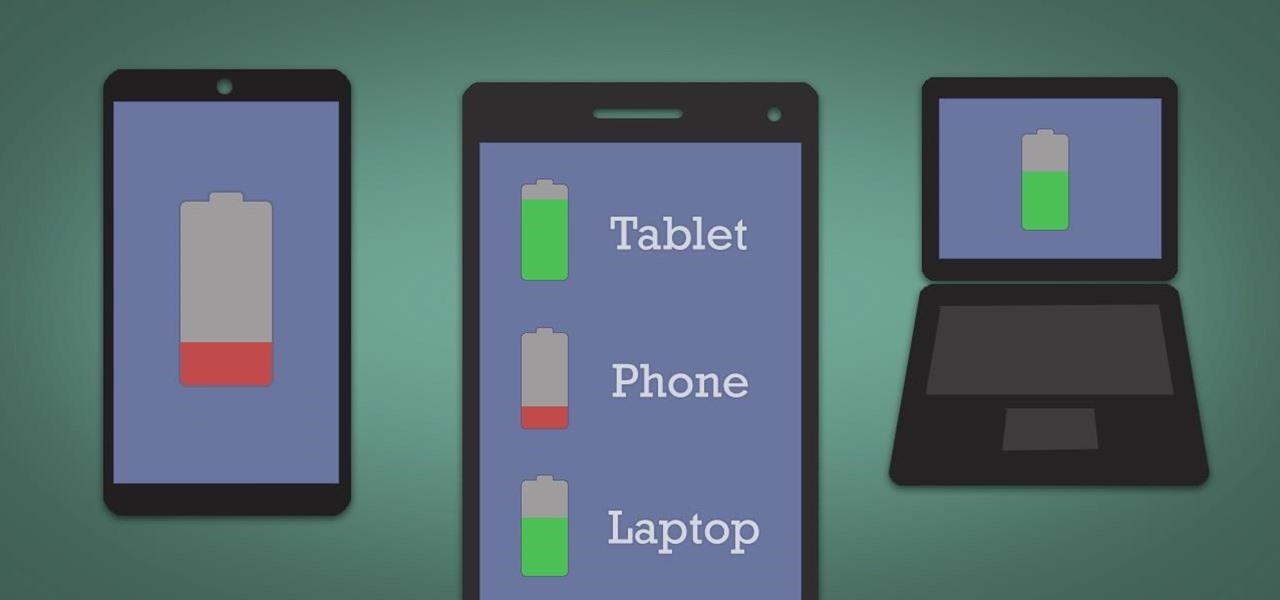
It's hard enough to keep tabs on the battery life of one device, let alone all of the different gadgets that a typical consumer owns in this day and age. Say your smartphone is running low on juice, so you switch to your tablet only to find out that it's almost dead as well. Better hope your laptop is fully charged, right?

Say goodbye to your boring stock Apple keyboard, because when iOS 8 is finally released, you'll be able to use Fleksy, SwiftKey, Swype, TouchPal, and other third-party keyboards on your iPad, iPhone, and/or iPod touch.

Normally, it's good to automatically update your apps to the latest version, but sometimes those updates take away features that you've grown to love.

Only scumbags hide their call and message history, right? Wrong. While it may seem like a tactic for the unfaithful, it's still a good thing to do for certain contacts on your phone that you don't want to block outright.

I passed a cool looking bar the other day that I wanted to check out. When the weekend came around, I was ready to go, but for the life of me couldn't remember where it was. Not wanting to retrace my steps or drive around aimlessly, I gave up.

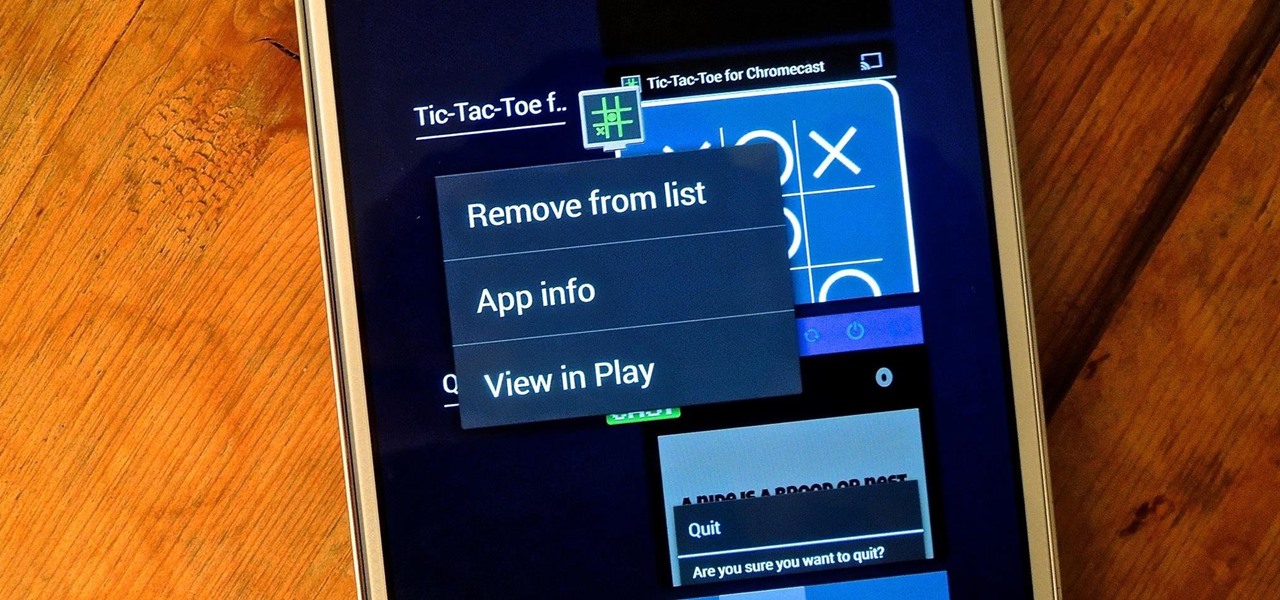
On more than one occasion, I've wanted to check out the Google Play page for an app I was currently using, whether it was to get contact information or read recent reviews to see if others were experiencing issues that I was.

When you're scrolling through your iPhone's home screens, you'll inevitably reach the end and have to either swipe backwards or hit the Home button to return to the first page. Why Apple didn't instill an endless scrolling feature, or at the very least an option for it, is anyone's guess, but just because you can't do it out of the box doesn't mean you can't do it.

Like insurance, it's always better to have a computer mouse and not need it than to need it and not have it. Honestly, I don't want to carry around a clunky mouse with my laptop, so I don't. I do something else, something more convenient. I use my Nexus 7. If you want to give it a try, I'll show you how it's done right now. All you need to is a Wi-Fi network and a specific Android app to control your computer with your Android tablet.

I could write about a new launcher everyday, because there are so many options out there for Android users, but one of my favorites it Everything Home. You probably have your own favorite, but what if you could actually use two launchers together, taking advantage of each one's awesome features?

"Ain't No Sunshine" might just be a classic song to you, but for me and my Samsung Galaxy S3, it means so much more. For the most part, my GS3 does a decent job at automatically adjusting the brightness of the screen when I'm in normal lighting, but when I'm in little or no lighting, or there's just way to much, I usually have to switch over to manual to get the right balance. Luckily, we're not stuck with Samsung's built-in auto brightness feature. There are some really good third-party solu...

How much privacy are you getting as an AT&T customer? With the recent leaks confirming the National Security Agency's surveillance on AT&T users, and the ongoing trial of Jewel v. NSA, it seems not much at all.

Welcome back, my eager hackers! In recent blogs, I've demonstrated how to grab password hashes remotely using Metasploit's meterpreter and pwdump. Once we have the Windows passwords from the SAM file, we can then crack these hashes using tools such as Cain and Abel.

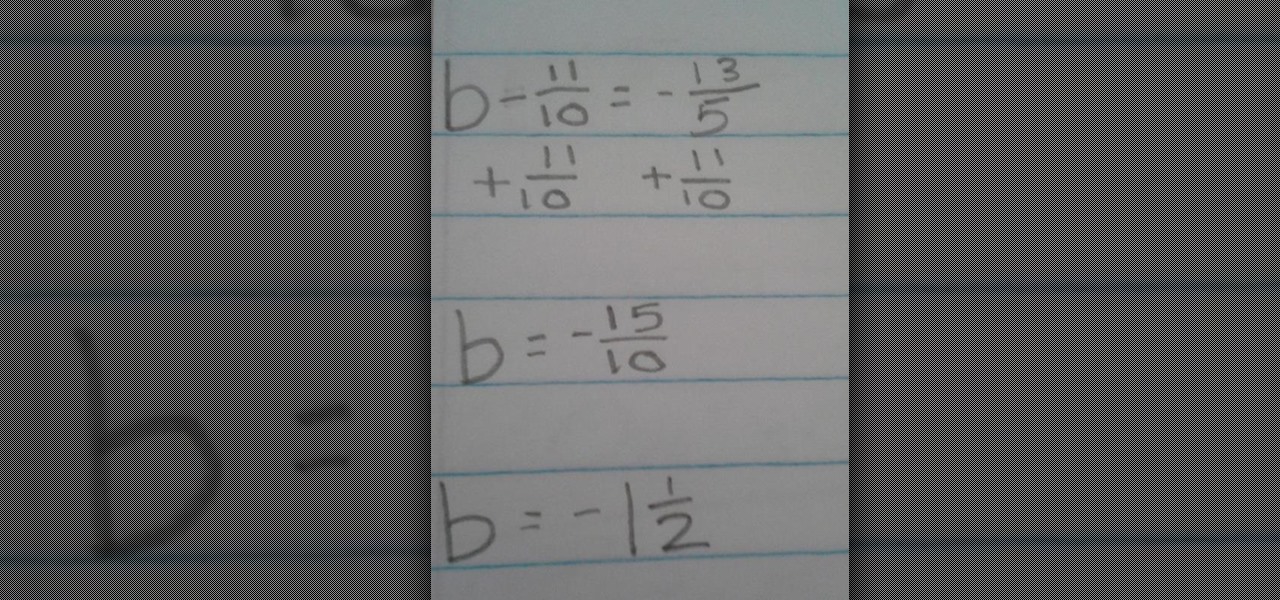
Solving Equations with Fractions Using Addition In our first example, our equation is b - 11/10 = -13/5

Welcome back, my novice hackers! Most of my tutorials up until this point have addressed how to exploit a target assuming that we already know some basic information about their system. These include their IP address, operating system, open ports, services running, and so on.

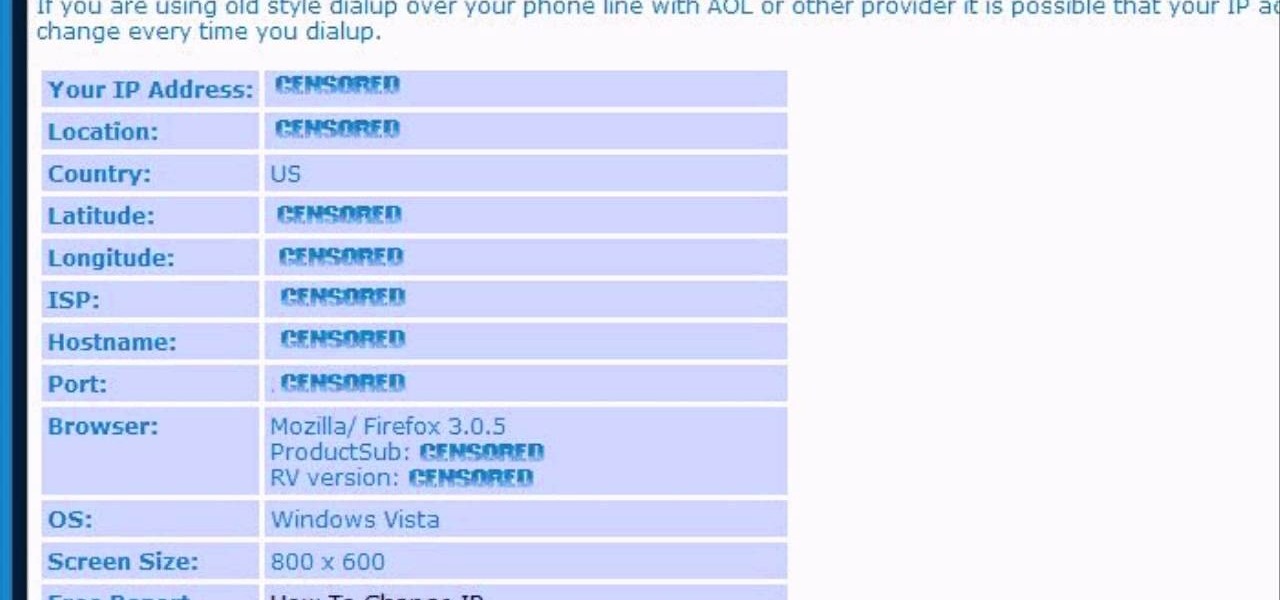
In this video, we learn how to find your IP address. First, start up your computer and open up your web browser. Next, you will type in the site: WhatIsMyIPAddress. Once you do this, you will be led to a new site which will load up your IP information at the top of the page. Once you have this information, make sure you don't share it with anyone else. If someone gets this information, they will be able to hack into your computer and ruin it. They could also access sensitive information and s...

In this video, we learn how to unblock a Facebook firewall at school. First, you will need to try to go to the website you want to go. If you try this and you can't reach the site, go to the top of the bar where you typed the website in at. Once here, you will find where it says "http". Type in an "s" after the "http" so you end with "https" then type in the website that you want to visit. After this, you should be able to go to the website you want to go to without any trouble, just make sur...

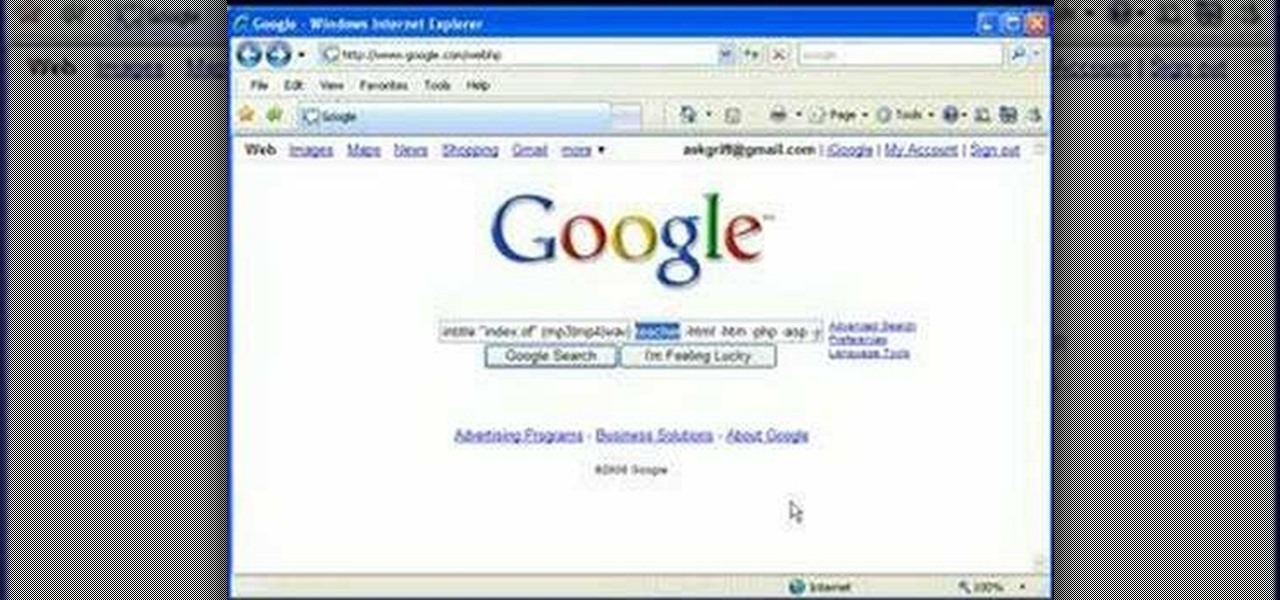
In this video, we learn how to find music and movies easier using "insite" in Google. If you are looking for media and can't find it through iTunes or an official site, you can find it on Google. First, go to Google, then type in "intitle:"index.of"(mpg(avi)wmv) (word you're searching for) -html -htm -php -jsp -asp". After you search this, you will see "index of" pages where you can do searched of what you are looking for. Once you click on the links that are available, you will be able to do...

In this tutorial, we learn how to get started out on Twitter. First, you will need to go to the main website and sign up by entering in your personal information. After you do this, you will be asked to enter in your other e-mail addresses to see if your other friends are on Twitter as well. After this, you can change your settings to change the icon that shows up on the site. Next, you will be able to start to follow people and enter in what you want your tweet to say. Go through the differe...

In order to find out if an email is a scam, you should avoid clicking on any links in that are in any emails. The links that are attached to emails, in this manner, usually have cloned the website of the institution where you do your banking. The link will look similar to your banking institutions site. Do not enter any of your personal information in emails in this fashion. Your bank will not contact you in this way.

Peter Answers is a fun website online that you can use to play pranks on your friends. This site is easy to access, free and requires no downloads.

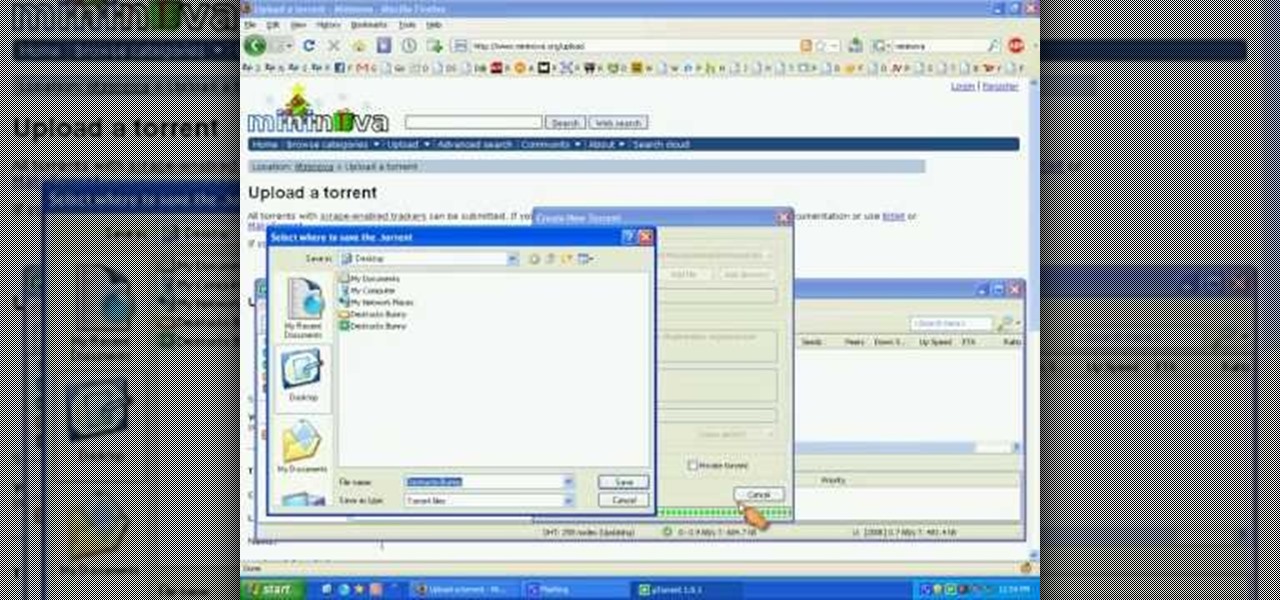
In this how to video, you will learn how create a torrent using uTorrent. First, download the program uTorrent. Next, find a tracker on a website such as Mininova. Open up uTorrent and go to file and create new torrent. Next, select the folder in which the files you want to upload are located. Paste the tracker in the form shown. From here, press create and save us. Choose a name and then close. Now your tracker will be created. Next, upload to the site by going to the website and uploading t...