This video shows how to make a Google Custom Search Engine. A Custom Search Engine safely searches only the sites you want, and gives you relevant results. To set it up go to the Google home page and sign in. If you don’t have a Google account, you can easily set one up by following the directions. Sign in, then enter in your browser “www.google.com.coop/cse”.

This will illustrate us how to use the reverse auction site Dubli. Here are the following steps.Step 1: First of all enter the link and log onto the official website of DubliStep 2: Now you will find various options on the homepage of Dubli.Step 3: go and click the option of auction option.Step 4: The various product that are for auction will be displayed.Step 5: Search for the product that you want to auction for and enter the amount that you pay for the product and press the go button.Step ...
This video is about how to install custom fonts on XP. The first thing to do is to open your browser and type "fonts" in the search bar. Several sites will appear and just simply click on any of the websites. Once you have found the site that suits you best, just start looking for fonts that you may like. And if you already have found a font, just simply press download then save it in your computer. Once you have saved it, other files need to be extracted so just simply extract it. After extr...

In this video you will learn how to download a torrent PC game, mount and the burn it. For this you will need a torrent program (to download torrents), daemon tools (to mount the images) and powerISO (to burn it). To get a torrent go on site mentioned in the video or on other torrent sites. After you downloaded the file, right click on daemon tools icon select virtual drive and mount your image. Enter in image from my computer, take the CD key from crack and write it on a CD case. To burn it ...
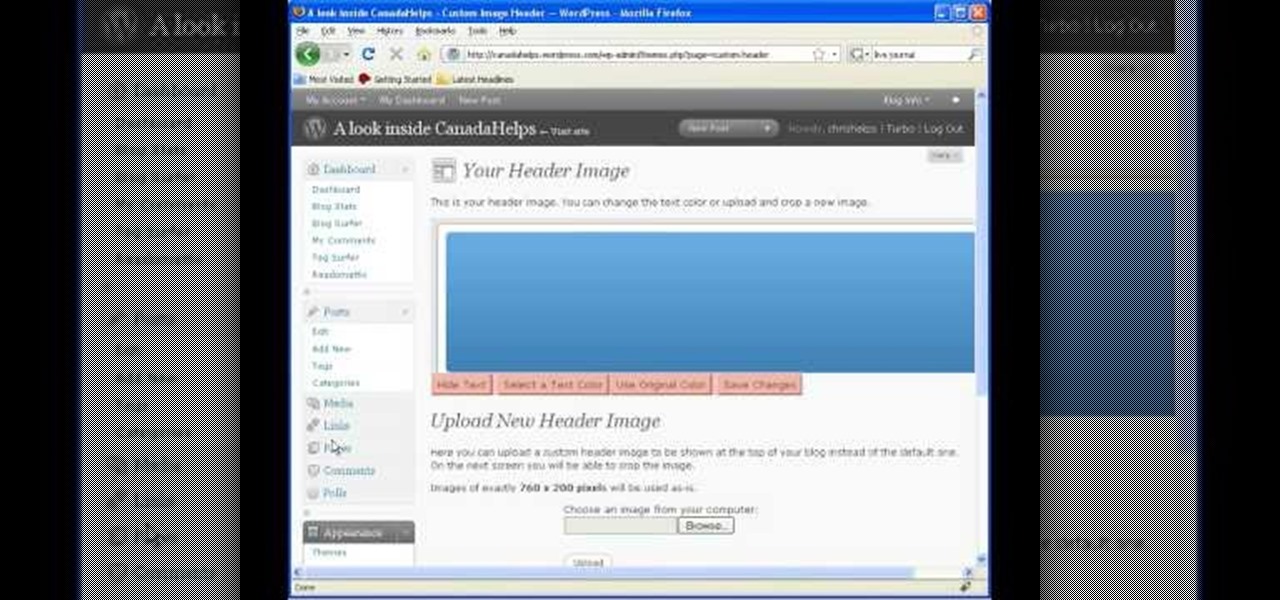
In this video tutorial, viewers learn how to start and set up a free blog. Viewers will learn how to setup a free blog for a charity, make a blog entry, edit and customize a blog and share a blog with their network. A blog is a online journal that provides the reader with regular posts on various topics. Three of the most popular blogging sites are: Blogger, Word Press and Live Journal. When creating a blog, keep the posts short and meaningful. Try to engage the reader. Update your blog regul...
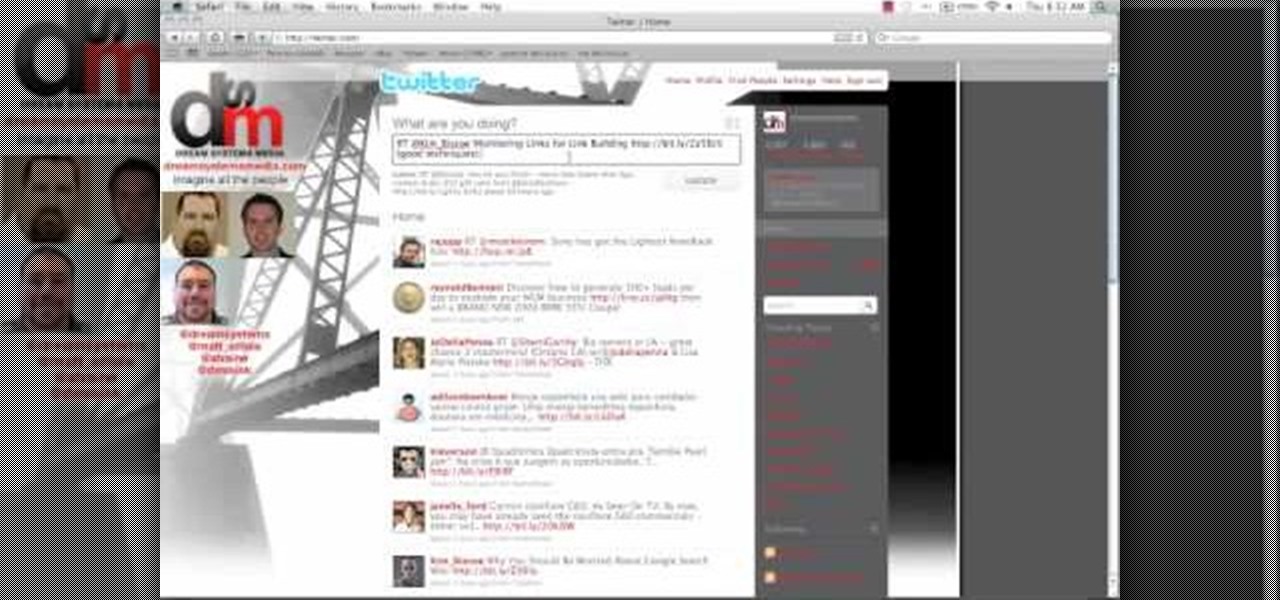
This video shows the method on how to Retweet web sites using Twitter. The website used on this video is Dream Systems Media. First, choose an interesting topic to tweet. Highlight and copy the entire tweet. Second, using either of the following codes: RT, rt, R/T or retweet, and the ‘@’ symbol; paste the tweet previously copied. Check if the tweet contains the name of the site and the URL. Third, place your comment inside the parenthesis following the tweet. Last, click the update button and...

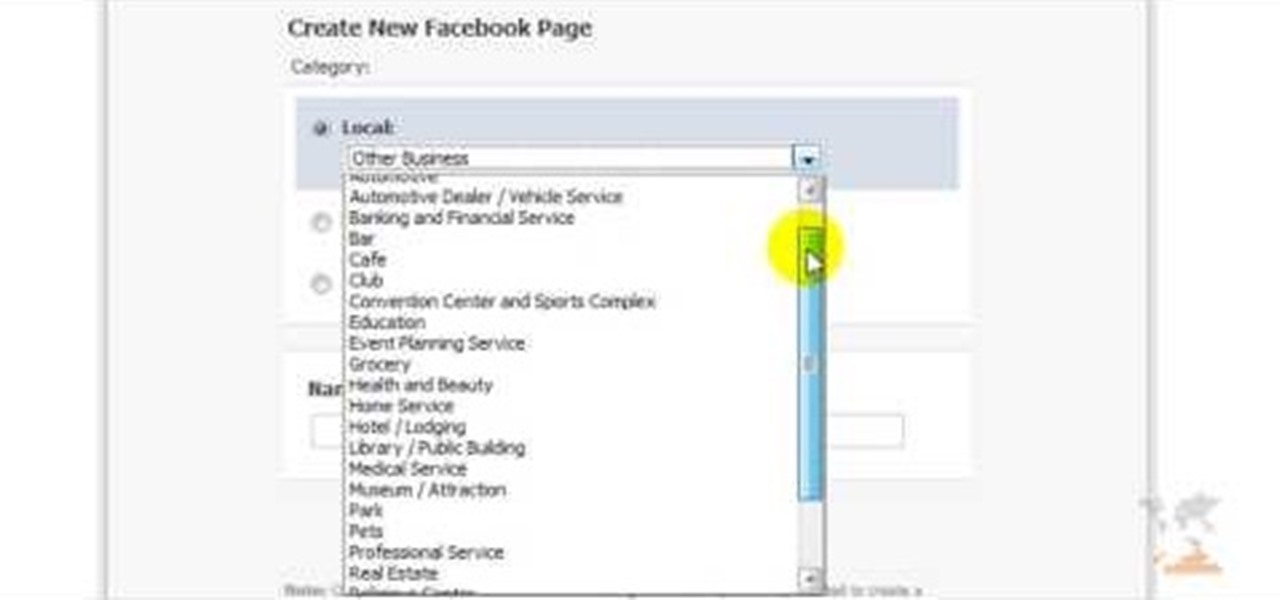
Facebook is one of the most popular Social Networking Sites around. Watch as this video shows you how to make your very own Facebook page so you will be included in one of the biggest things around! First, you want to sign up for an account. "Its free and anyone can join" is their slogan! Go to www.Facebook.com and get to signing up! After that simply login into the site using your user name and password. After that your profile is set up you must simply just personalize it. Fill our your inf...

Shannon Smith shows how to upload files using Filezilla in this episode of No Mac, No Cheese. Filezilla is useful in assisting you with putting files onto a web site. Simply type in your web address, user name, and password. Then create a folder and name it appropriately. Adjust the properties by keeping all permissions enabled. Then, open up the file to find all of the folders on your hard drive. You can easily drag and drop a folder from your hard drive or double click to individually selec...

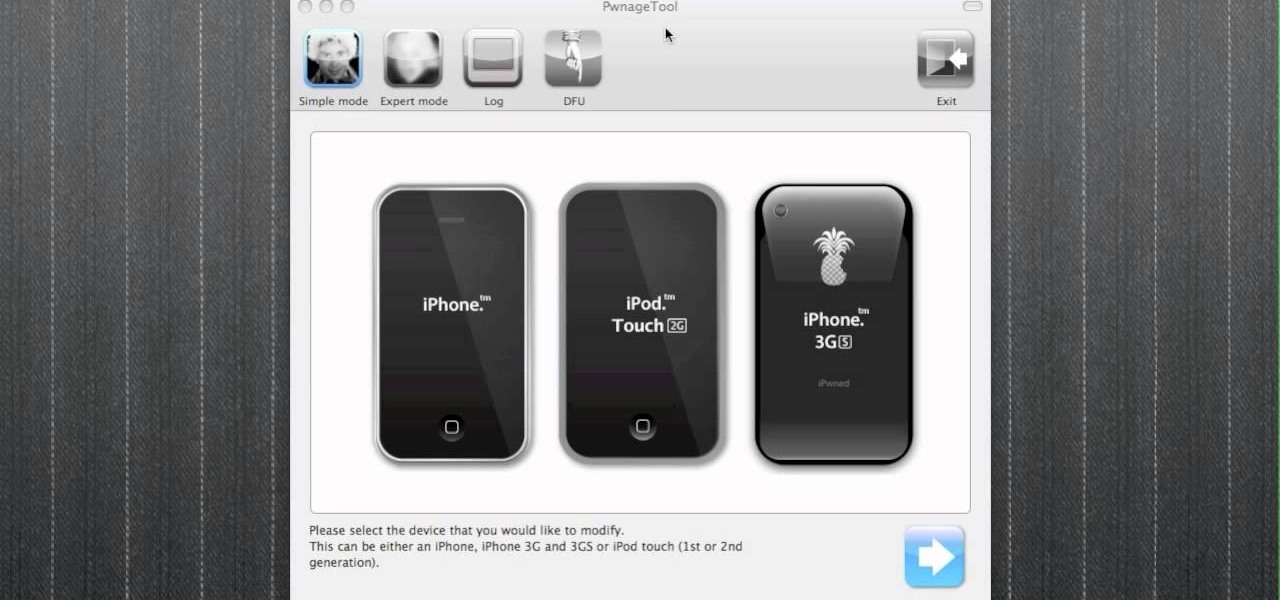
Are you a Windows user who wants to jailbreak your iPod Touch 2G 3.1.1? George from the iPhone Press shows you how in this video. The needed firmware is on the Megaupload site. There is a link provided that will take you to the site so you can download the firmware. Next, it tells how to put your device into DFU mode using Pwnage Tool. Then it explains how you connect your device to your computer, and get iTunes to open up. After iTunes opens, the video shows how to navigate in iTunes to get ...

Want to download a music track that you heard on MySpace? this video shows you how to download music from MySpace using the site File2HD.com. First find the MySpace page that has the music track you want to download, copy the URL and then go to File2HD.com and download the music track as shown in the video make sure to accept the terms and conditions. File2HD.com can be used to download music or videos from other sites that stream content so watch this video and happy downloading.

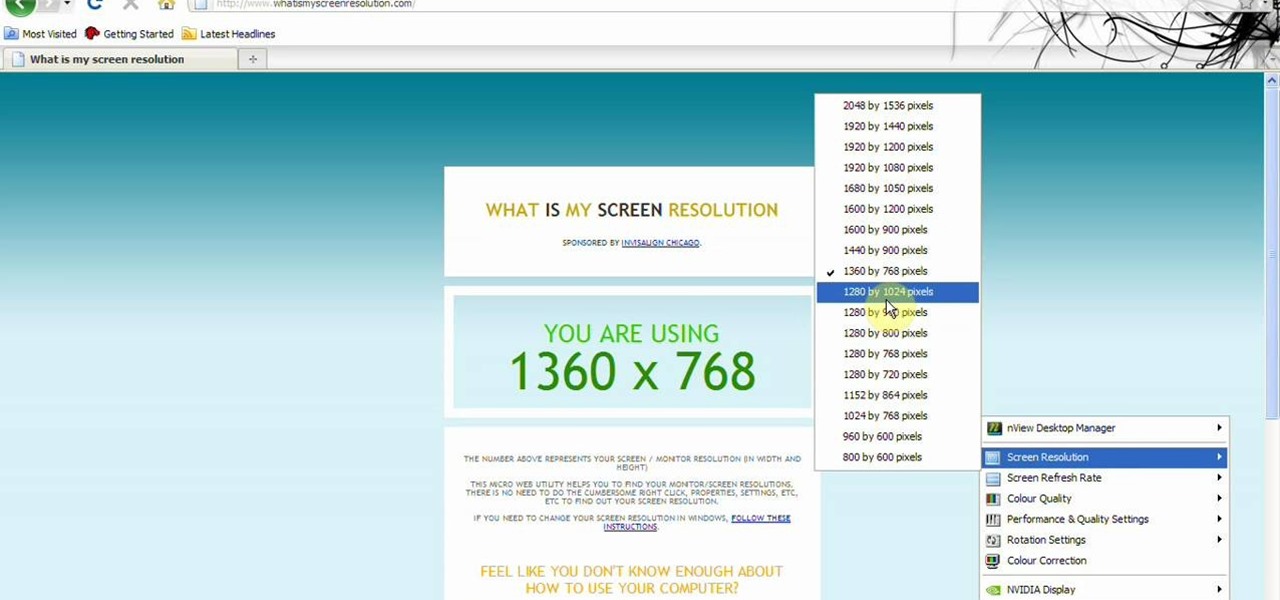
This video tells about the screen resolution of your monitor. In this video it is said that we can check our screen resolution by opening the site www.whatismyscreenresolution.com .While you get into that site our screen resolution will be displayed in the screen. But the screen resolution can be checked easily by clicking the right button of the mouse in the desktop and then selecting the properties button. In the small window that appears click on the settings tab. In that window we can see...

In this video Chris Pels shows how to create an MSBuild project that orchestrates the execution of the aspnet_compiler and aspnet_merge utilities for an ASP.NET web site. First, learn the fundamentals of the compilation process for an ASP.NET web site and the role of the two command line utilities. Next, see how to create an MSBuild project file and the primary elements such as PropertyGroup and Target. Then learn the details of how to execute the aspnet_compiler and aspnet_merge utilities fr...

In this video tutorial, Chris Pels will show how to determine what capabilities a user’s browser has when viewing pages in an ASP.NET web site. First, learn how to access an instance of the HttpBrowserCapabilities object from the ASP.NET Request object associated with the web page request. Next, see the different information available in the HttpBrowserCapabilities object such as the type of browser and whether the user’s browser supports JavaScript and Cookies. Then see an example of how to ...

In this video tutorial, Chris Pels will show how to use the aspnet_merge.exe utility to combine assemblies that have been compiled using the aspnet_compiler.exe utility. First, view the output of the ASP.NET compilation process to learn what assemblies are created. Next, learn the mechanics of using the aspnet_merge.exe utility to merge assemblies from the compilation of a web site, first seeing how to control the compiled assembly names with the –prefix option. Then see how to merge all the ...

Many sites do not use any fancy Content Managment System (CMS) to generate their pages, they are just just good ol' static HTML content. A site for your grandmothers pie baking business probably only has a few pages, perhaps a homepage, about page, and contact page. Each of these pages has different main content, but much of it stays exactly the same, like the header, navigation, and footer. Think of these sections as "modules" that you can easily use PHP to insert into the page. This way, ma...

If you would like to use Google AdSense on your website, in order to make money from your site, you will need to get a Google account. Click "sign in" on the Google home page: www.Google.com. Next, scroll down to the bottom of the page and click on "create an account now. Fill it out. It will send you an email to verify your account. You'll need to open your email to confirm.

In this video tutorial, Chris Pels shows how to use the ASP.NET IIS Registration Tool to configure ASP.NET. First, see how file extensions are mapped to ASP.NET in the IIS Manager on a global and web-site-by-web site basis. These script maps provide the basis for configuring individual ASP.NET applications to run under a specific version of the .NET Framework. Next, see how aspnet_regiis.exe, the IIS Registration Tool command line utility, is specific to each version of the .NET Framework and...

Check out this video tutorial to see how to use the BD Genie Safety Lancet blood sampler device. BD Genie Lancets are high quality, safety-engineered, single-use capillary blood sampling devices. They offer a permanently retractable blade or needle feature that minimizes the possibility of injury or reuse. BD offers a full range of blade depth and needle gauges for sufficient blood volume in multiple sample requirements. All Genie's can be used in conjunction with BD Microtainer Tubes.

Swimming in ocean currents requires preparation and understanding. There are definite do's and don'ts when trying to swim in currents. Get expert tips and advice in this swimming video tutorial.

Some of the oldest art on Earth was created 36,000 years ago on the walls of the Chauvet Cave in France. However, these days, physical access to the cave is restricted in order to preserve the site.

Phishing is the easiest way to get your password stolen, as it only takes one mistake to log in to the wrong website. A convincing phishing site is key to a successful attempt, and tools to create them have become intuitive and more sophisticated. SocialFish allows a hacker to create a persuasive phishing page for nearly any website, offering a web interface with an Android app for remote control.

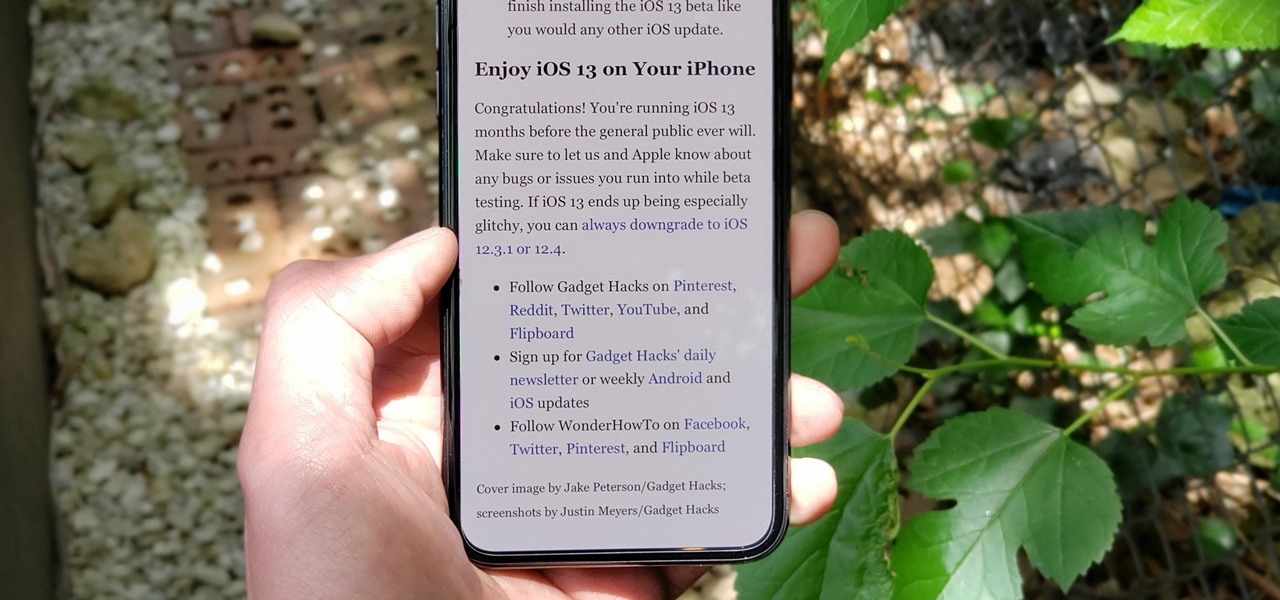
The Reader mode in Safari is a great way to view a webpage on your iPhone in a stripped-down manner, removing unnecessary images, videos, and advertisements for a streamlined experience free of distractions. Apple's iOS 13 improves upon Safari Reader when it comes to choosing which sites you want it to run automatically on, so everything is more accessible with more controls to work with.

The ability to stay organized and be resourceful with data gathered from recon is one of the things that separates the true hackers from the script kiddies. Metasploit contains a built-in database that allows for efficient storage of information and the ability to utilize that information to better understand the target, which ultimately leads to more successful exploitation.

It's fitting that students at the University of Washington can catch a glimpse of the new, 135,000 square-foot computer science building in augmented reality before construction is completed.

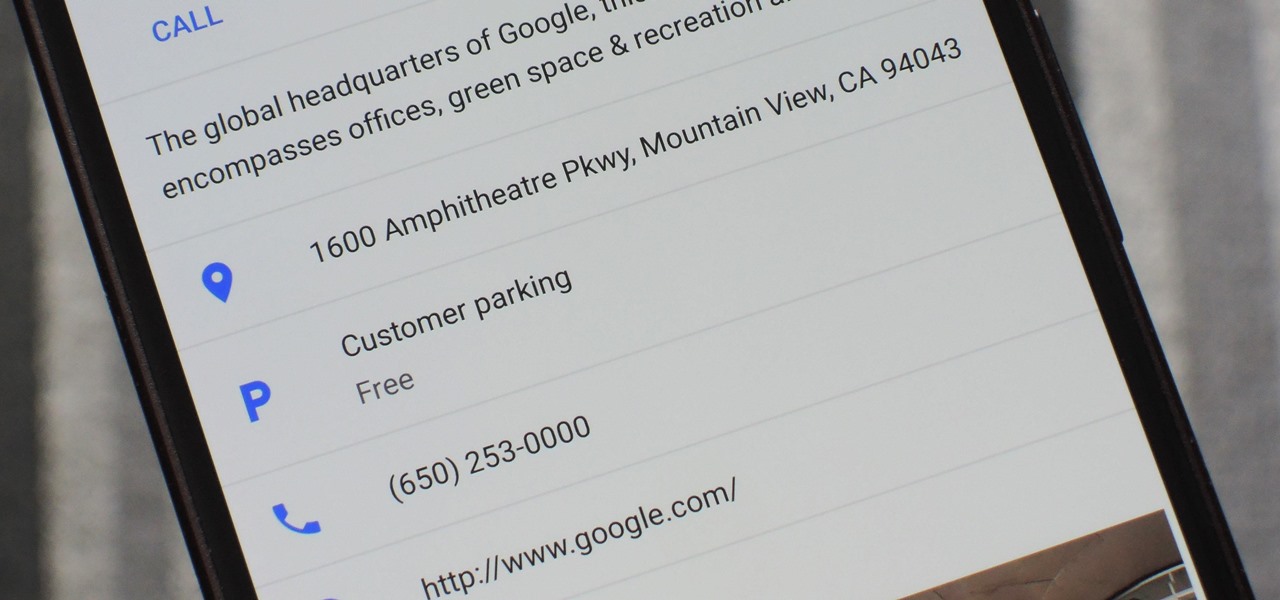
There's nothing worse than driving up to your destination only to discover that there isn't a parking spot in sight — but thankfully, Google Maps will soon have you covered.

Hello Guys, Today I have made a script for ddosing sites with VBScript! And I don't know how you guys do it, but I've made a script that refreshes the page in a chosen amout of milliseconds. And if you want it a number of times or if you want it to go on and on. And this is a script to run it on your botnet. But again I don't know if this works on your botnet too.

Unless you've been living under a rock or ignoring recent news headlines, Ashley Madison, the dating site for married people (or individuals in a committed relationship) has recently been hacked. Millions of their users are shitting their pants, and for good reason, as all of those accounts have just been leaked.

My bathroom is like my own private arcade room. Whenever I'm seated comfortably on the toilet, no one is going to disturb me, so I can play anything I want on my smartphone. You probably do it, too — and your parents, kids, friends, colleagues, and boss — so don't be afraid to admit it.

And we meet again Crackers! Welcome to my 7th post (Part-2), this tutorial will explain about some more basics of Batch Scripting, with C00L Scripts, which in turn will help you learn and understand better

Copy and paste keyboard shortcuts are beautiful gifts from the gods, and any website that blocks such an offering can burn in hell. But really, Cmd+C and Cmd+V (Ctrl+C and Ctrl+V for Windows folks) are second nature to most of us, so it's very frustrating when sites like PayPal don't let us use them.

This time it's serious. Really. The largest web security vulnerability of all time went public on Monday, April 7th, 2014, resulting in widespread panic throughout the Internet as system administrators scrambled to secure their websites from the OpenSSL bug known as Heartbleed.

As you may have already heard, the worst bug in OpenSSL history went public yesterday, dubbed Heartbleed. While we can go deeper into the technical details of it later, the short version is that OpenSSL, the library used to encrypt much of the web running on Linux and Apache has been vulnerable for up to two years.

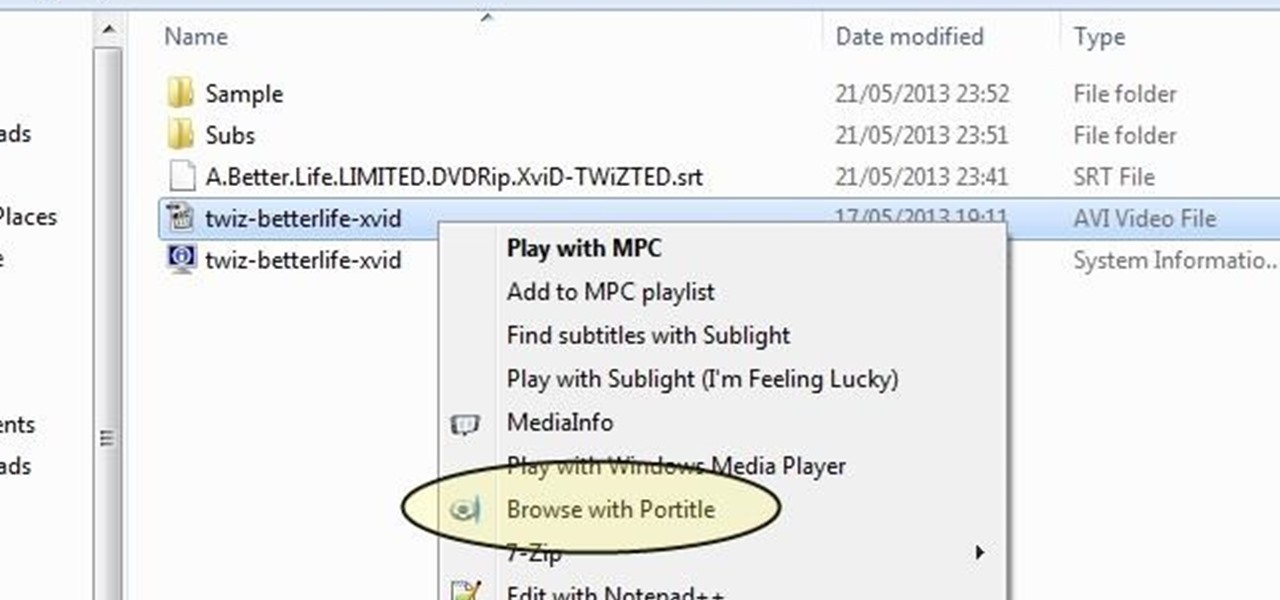
Understand the Problem of Couch Potatoes I have a lot of movies stored on my PC and when I have to finally have the time to watch something, I do not always remember which movie is which. So now I have to google for each movie with the keyboard or search in IMDB.

Welcome back, my tenderfoot hackers! This is the third installment of my series on basic Linux skills that every hacker should know. Although some hacking tools are available for Windows and Mac, every real hacker uses Linux—for good reason.

YouTube is the third most popular website in the world, after Google and Facebook. Millions of subscriptions happen each day on YouTube, with over 800 million unique users visiting each month. In that timespan, roughly 4 billion hours of video are watched, with 72 hours of video uploaded every single minute.

As with most things on the Internet, browser cookies can be either helpful or harmful, depending on how they're used. On one hand, they make your experience more convenient by storing information about sites you use frequently. On the other, they can help companies track you across the web or cause your computer to be more vulnerable to attacks on public networks.

A few weeks ago, Facebook published a blog post called "Proposed Updates to our Governing Documents," which outlines a few changes in their policies and user voting system. These changes would essentially take away users' right to vote on future changes to Facebook's data use policy while also taking away Facebook's responsibility to alert users of those changes. If the new policy is enacted, the vote will be replaced with "a system that leads to more meaningful feedback and engagement," what...

Apple is notoriously cryptic when it comes to the reveals of its new products, and as usual, they've kept us guessing about the release of the iPhone 5 (or "New iPhone?"). It's expected to be officially revealed on September 12, and rumor has it that sales will begin on the 21st. Though the whole world seems to be anxiously awaiting the announcement, there has also been some controversy surrounding the iPhone 5's production. With the high number of suicides and poor working conditions at Foxc...

Online shopping is way more convenient than brick-and-mortar stores in a number of ways, not the least of which are the discounts. But with so many online stores and sites like Amazon which feature thousands of retailers, how can you know you're getting the best deal?