
How To: Clean your body with the antioxidant vitamin E
If ever there was a super-hero vitamin, Vitamin E would be it! Learn why, right here.


If ever there was a super-hero vitamin, Vitamin E would be it! Learn why, right here.

You need to re-stock your supplies of Vitamin B3 each and every day. But why?

Want softer skin, and to see in the dark? Then step right up for your daily dose of Vitamin A!

ADHD can be hard-hitting for children and their parents. Luckily, there are a host of treatment options available.

Over 300,000 Americans who are infected with HIV don't even know it! Learn how to avoid being among them.
Could you boost your brain power by eating a banana? Improve your memory and IQ by pressing certain points on your body? Absolutely! In this video, we'll show you how to amp up intelligence using super simple natural remedies.

You love to drink, but could do without the (literal!) headache. Imagine a world in which hangover prevention is actually possible! In this video, we'll teach you how to prevent a hangover, so you'll never waste another day post-drinking.

You've probably tried every alleged hangover cure--from cold showers to hot coffee--with little success. But a hangover remedy does exist! So watch this video and learn how to be a drunk without suffering hangovers ever again!

Between torturous tests and Friday frat parties, the last thing you want to think about is bed bugs. Unfortunately, these and other parasites, like head lice, may lurk around your dorm room. Here, everything you need to know to prevent these bug bites.

Pink eye, or conjunctivitis as your doctor may call it, is a contagious disease that affects many college students. Blame close quarters and bad hygiene for this itchy ailment that affects the eyes. Here's how to treat and even avoid this condition.

Someone you love is consuming much too much and you want to stage an intervention. While interventions can work, a person who abuses alcohol has to be willing to stop drinking. Here, everything you need to know to help encourage a friend to quit drinking.

You know you're in pain, but are you just feeling the aftershocks of that spaghetti dinner, or is it a heart attack?

Every year, 250,000 Americans are diagnosed with a form of skin cancer called squamous cell carcinoma. What exactly is SCC?
If you know the triggers that bring on a migraine you can more easily sidestep experiencing one.

Heart disease affects more than 20 million Americans. Let's explore the various forms that heart disease can take.

This video explains how to fold an origami goldfish using a single sided solid colored sheet of paper of size 6".

Learn how to fold an origami rabbit with instruction by Ancella Simoes. This video is in two parts, so be sure to click on Chapter 2 for the complete tutorial.

Learn how to fold an origami Reindeer with instruction by Ancella Simoes. Ancella Simoes is the author of the Origamiancy Blog and creator of all the Origamiancy origami tutorial videos on WonderHowTo. From Ancella's site:

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.
Whether you've made a resolution to try and read more books this year or are just looking to set time aside to listen to an audiobook a little bit each day, building good reading habits can be tough with a busy life. However, with iOS 13, Apple Books includes reading goals, which might give you that little extra bit of encouragement and accountability to help you reach your goals.

One of the first steps when pentesting a website should be scanning for hidden directories. It is essential for finding valuable information or potential attack vectors that might otherwise be unseen on the public-facing site. There are many tools out there that will perform the brute-forcing process, but not all are created equally.

Starting Sept. 13, you can preorder the iPhone 11, 11 Pro, or 11 Pro Max from Apple, wireless carriers, and various e-commerce websites. However, unlike with Android smartphones, there is only one set of iOS phones that come out each year, so they're pretty hot items. That means being the first to get your hands on one could be a challenge, but we're here to help you out.

They're finally here. Apple revealed the brand new iPhone 11, 11 Pro, and 11 Pro Max on Sept. 10, and despite the questionable names, these are the best iPhone models money can buy. If you're looking to get your hands on one of these devices as soon as possible, there are few important dates you need to know.

In our comparison of the best gaming phones in 2019, the winner actually surprised us. A phone that most people don't know about from a brand you probably haven't heard of ended up as the clear winner. But how? Well, it ticked so many flagship boxes despite its midrange price tag.

In the technology space, there are certain brands you grow to depend on. Whether it's due to a long, multi-decade track record of success, or new innovations that blow you away, some tech names accrue a rare kind of brand equity with users that's difficult to earn.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

A few months ago, iOS 12.1 came out with a handful of useful new features, and iOS 12.2 goes even further. While some of iOS 12.2's new features for iPhone are much welcomed, there are some that we'd be better without.

If you ask Siri to check the weather on your iPhone right now, you'll get information from the stock Weather app in iOS — even if you have and prefer other weather apps installed. But that doesn't have to be the case. Thanks to Siri Shortcuts in iOS 12 and later, you can set specific phrases that Siri will respond to for any compatible weather app you want.

One of the best ways to improve your skills as a hacker is to learn to combine different avenues of attack to achieve success. What if it were possible to get a victim to connect to our machine and execute a chosen payload on our behalf? This is indeed possible with the almighty Metasploit and the aid of a technique known as command injection.

The new iPhone XS and XS Max have more issues than just their hefty price tags. Customers have only had the phones for a handful of days, but some are already complaining of cellular and Wi-Fi connectivity issues on both models. If your experience is the same on your XS or XS Max, there are steps you can take to get your iPhone reliably back online.

Like an overbearing mother, Apple will constantly nag you through annoying red bubble alerts about iOS updates that are ready to install. Fortunately, you don't have to take this issue lying down, as there are ways to prevent your iPhone from receiving OTA updates and their corresponding prompts, regardless of whether your device is jailbroken or not.

One of the first steps in reconnaissance is determining the open ports on a system. Nmap is widely considered the undisputed king of port scanning, but certain situations call for different tools. Metasploit makes it easy to conduct port scanning from directly inside the framework, and we'll show you three types of port scans: TCP, SYN, and XMAS.

I was in college, and my 15-inch Sony Vaio laptop was my prized possession. It was my first PC and probably the most important thing I brought with me to my dorm — it was both how I completed my assignments and my primary source of entertainment. How could it turn its back on me in my time of need?

I love my iPhone, but it would be a lie to say there aren't some Android features I wish would find their way to iOS. While iOS has plenty of its own advantages, Android has pulled ahead in many other areas. With iOS 12 coming later this year, we're hoping Apple takes a hint from Google and adds some of these awesome features to the iPhone.

Waze is the go-to navigation app for millions of drivers, and it's easy to see why. Benefits such crowd-sourced traffic data, police trap locations, and road work avoidance are just the tip of the iceberg. It can almost be overwhelming, but with these simple tips, you'll master Waze and start navigating like an expert in no time.

If you're in the market for a new smartphone, you'll likely scan spec sheets and read reviews of the top phones, compare display size and technology, RAM amount, and processors. But one factor that is often overlooked is cell reception — and for T-Mobile subscribers, there's only one device that has flagship specs and an exclusive antenna that will actually improve your signal.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.
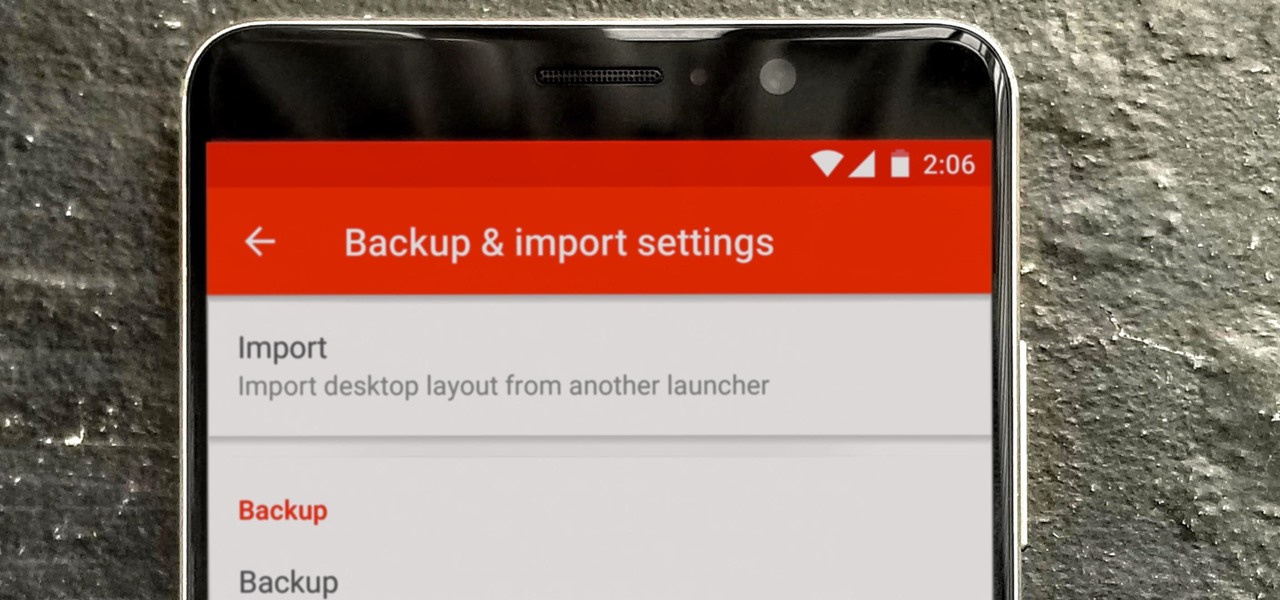
So you spent all day customizing your phone. You tinkered with all the settings, searched the web high and low for the perfect wallpaper, and found an ideal icon pack to complement the color scheme. You go to sleep, proud of the work you accomplished when the unspeakable happens — your phone freezes and tech support is telling you to do a factory reset to fix the problem.

After learning that you'll need to spend at least $74 on a special charger and a USB Type-C Lightning cable to enable fast charging on the new iPhone X and iPhone 8 models, you may be wondering why you can't just use the standard Lightning cable. While we can't answer why Apple didn't include the USB-C cable in the box with their new phones, we can explain why you need USB-C to enable fast charging.

The pictures we upload online are something we tend to think of as self-expression, but these very images can carry code to steal our passwords and data. Profile pictures, avatars, and image galleries are used all over the internet. While all images carry digital picture data — and many also carry metadata regarding camera or photo edits — it's far less expected that an image might actually be hiding malicious code.