In this cardmaking project I show you a card that I create using items that are featured in popular cardmaking kits. This particular card has no flowers no it, because hard as this maybe to believe some people do not like them... I know I know!! but we have to cater for all !! so this card is fancy without flowers, however still just as pretty. Step 1: Now Watch the Tutorial

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.

If you have a local Trader Joe's, you know first-hand how enchanting the frozen aisles are—almost every item offers the promise of a delicious meal or dessert. (We're always tempted to open the package and eat the cookie butter cheesecake, stat.)

The produce section is full of fruits, both familiar and quite strange. Depending on the season, you may see giant, bright-green bananas on display next to the normal bananas that you know and love. No, those aren't super-unripened bananas—they're plantains, and they are definitely a different fruit altogether. However, once you get to know them a little better, you'll find that they're much more fun to cook with.

Hello, everyone. Stealth is a large part of any successful hack; if we don't get noticed, we're much less likely to be caught. In these next few articles, we'll be building a shell based on keeping us hidden from a firewall. There are many ways to stay hidden from a firewall, but we'll only be incorporating a couple into our shell. This article will outline and explain these evasion concepts and techniques.

In my last tutorial, I talked about creating a virus inside of a Word Document in the scenario of a mass-mailer attack. In this post, however, I'm going to be covering creating a fake image or screenshot with a meterpreter backdoor hidden inside to be used in a similar scenario. Step 1: Creating the Virus

Greetings aspiring hackers. I have observed an increasing number of questions, both here on Null-Byte and on other forums, regarding the decision of which USB wireless network adapter to pick from when performing Wi-Fi hacks. So in today's guide I will be tackling this dilemma. First I will explain the ideal requirements, then I will cover chipsets, and lastly I will talk about examples of wireless cards and my personal recommendations. Without further ado, let's cut to the chase.

Smartphones have been a hot button issue around school campuses for several years now—some schools allow them, others confiscate them on sight. But the fact of the matter is, when used correctly, a smartphone can be just as much of a learning tool as a textbook or school-issued laptop.

Before I continue with a topic on strings, we first require some fundamental understanding of how memory works, i.e. what it is, how data looks in memory, etc. as this is crucial when we are analyzing vulnerabilities and exploitation. I highly suggest that your mind is clear and focused when reading the following article because it may prove to be confusing. Also, if you do not understand something, please verify all of your doubts, otherwise you may not completely understand when we touch on...

Recently the newly famous ProtonMail service was under attack by DDoS attack. This attack was believed to be the hacking group Armada Collective.

Hello, my web huggers! In today's tutorial we will learn how to use the Google Hacking Database (GHDB) developed by Exploit Database, to find vulnerable web servers and "juicy" information.

G'day, Knuckleheads, and welcome to Episode 22 of my Owner Builder Series. In this video we look at cutting and setting up Verandah / Decking Posts. It's really important that you get thuds right as nothing looks worse than badly set up posts. Check it out and let me know what you think!

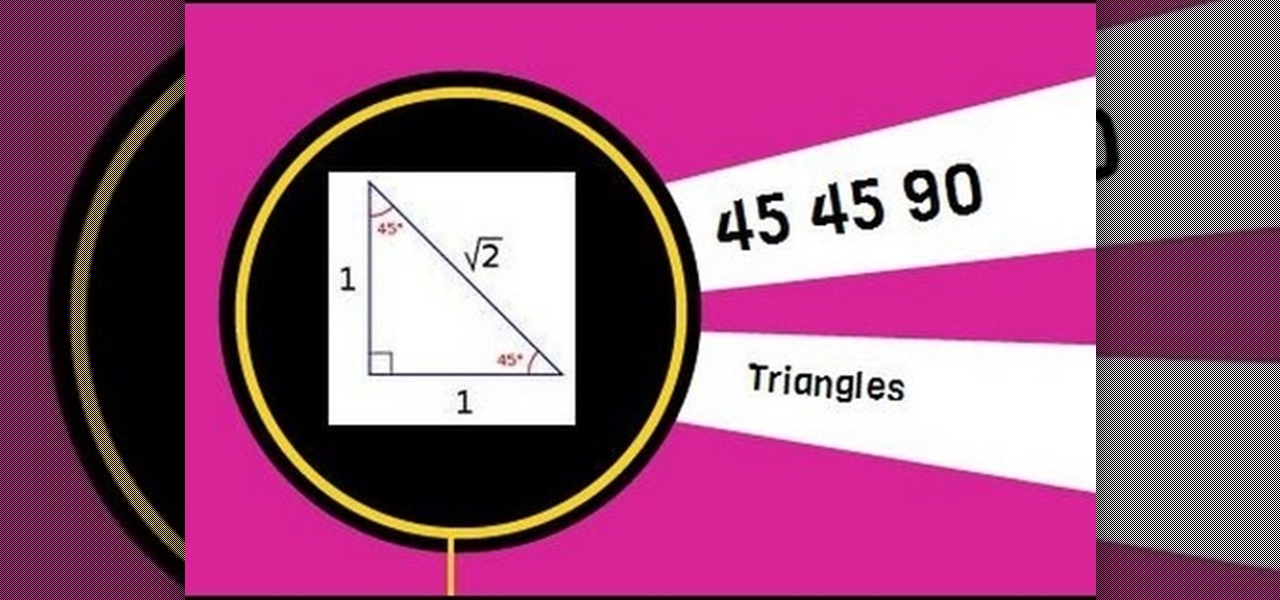
A 45 45 90 triangle is a special right triangle because you can use short cuts to find leg length and hypotenuse length. This video solves two problems involving leg length and hypotenuse length.

Other than salt, there's no ingredient that's as big a kitchen staple as olive oil. And just like salt, there are a million little known uses for it.

Based on OTW's encouragement in his post on "How to Find the Exact Location of Any IP Address", I decided to make a gui(graphical user interface) which would hopefully make the process easier. However, because turning a python script into a standalone executable is a right pain in the nether-regions, particularly for linux, I haven't yet completed this step(I will soon and update this). I did however, make an apk for android(you use a .apk file to install an app on your android device), which...

Spotlight, Apple's selection-based search system, received a major facelift on Mac OS X Yosemite. Packed with dozens of new features, such as a central search window and increased app suggestions, the reworked Spotlight was a breath of fresh air.

As many of you know, I firmly believe that hacking is THE skill of the future. Although the term "hacking" often conjures up the image of a pimple-faced script kiddie in their mother's basement transfixed by a computer screen, the modern image of the hacker in 2015 is that of a professional in a modern, well-lit office, hacking and attempting to development exploits for national security purposes. As the world becomes more and more digitally-dependent and controlled, those that can find their...

There's nothing in this life that we love more than making one ingredient or one food tool do multiple things. It saves money! It saves time! It makes us look smart at cocktail parties!

You can find chili peppers in practically every cuisine. From the sweet Italian variety to the spicy Thai bird's chili and the smoky Mexican chipotle, peppers are ubiquitous and universally loved. But if you find the range and scope of these little fireballs overwhelming, you're not alone.

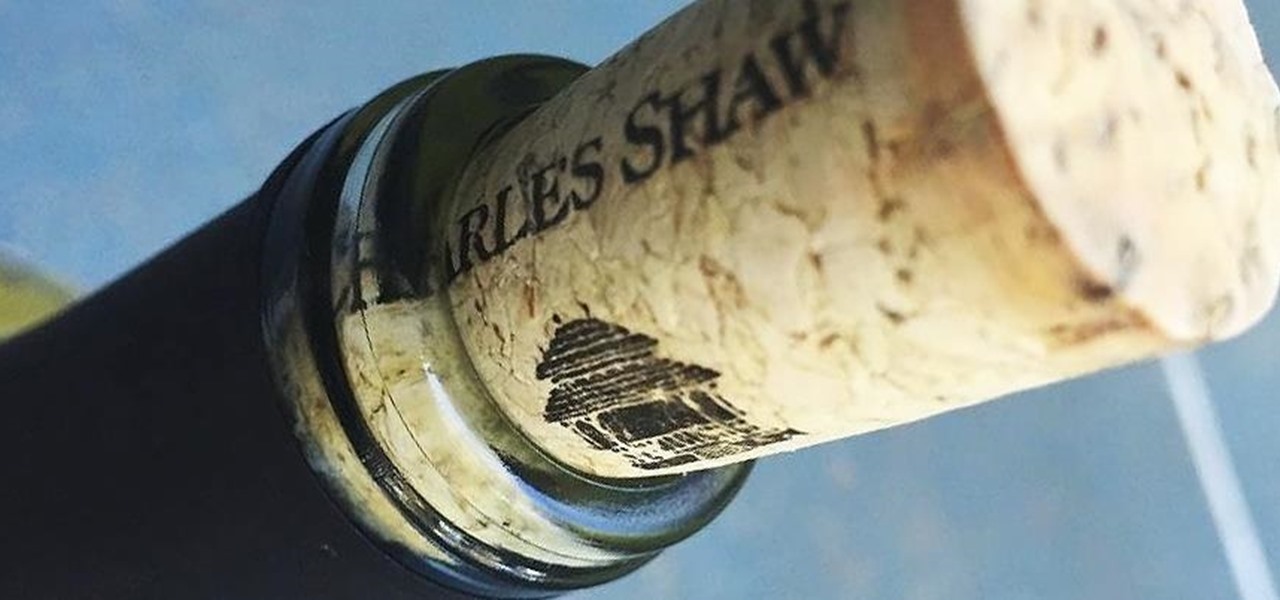
Bad news, guys. The shelf life for liquor leftovers does not apply to your two-buck chuck. While an opened bottle of your favorite whiskey will stay respectable for ages thanks to its high ABV (which makes it inhospitable to outside elements), an opened bottle of merlot will sour quickly. However, it turns out that red and white wines have different life spans once they're opened—for reasons which we'll cover below.

In-N-Out Burgers on the West Coast is famous for their not-so-secret and secret menus, along with their cheap, no-fuss burgers. Pre-internet, you felt like you were actually part of a small, select club when you knew what secret menu items to order.

By now, Samsung's Multi-Window Mode is a pretty well-known feature. With other manufacturers now recreating this functionality in their own flagships, like LG, it's safe to say the feature has been a hit with consumers.

Aluminum foil is one of those things that every cook, experienced or just starting out, has in their kitchen. And while we may think we know how useful this handy material can be, there are hundreds of ways we could be utilizing tinfoil to make our lives a whole lot easier.

Each day, we read about another security breach somewhere in our digital world. It has become so commonplace that we hardly react anymore. Target, J.P. Morgan, iCloud, Home Depot, and the list goes on and on.

Everything you thought you knew about cooking pasta is wrong. When I took cooking classes in Italy, they taught me to bring a large volume of salted water to a rolling boil, add a drop of olive oil so that the noodles wouldn't stick together, and wait several minutes until it was al dente (which literally means "to the tooth," i.e., firm and not mushy when bitten).

Battery drain. App crashes. Random reboots. All of these issues can be attributed to an uncooperative third-party app on your Nexus device. To be sure that's the problem, rebooting into "Safe Mode" is the way to go.

Microsoft's latest Xbox commercial features Aaron Paul, the actor best known as Jesse Pinkman on Breaking Bad. Check it out below, but keep an eye on your own Xbox One, if you've got one.

It has been a long while since I last came here to write an article. Graduate school keeps you busy. After I looked over what I had written previously, I decided that I should introduce another fun topic from cryptography. In this case, steganography.

Last year, Todd Blatt ran a Kickstarter campaign to make 3D-printed accessories for Google Glass, and has turned it into a company: GlassKap.

Chances are that you've been using your microwave just to nuke leftovers, but they can do so much more than heat up last night's dinner—microwaves can help you peel garlic more quickly, get more juice out of lemons, disinfect your kitchen, dry out herbs, give beauty products new life, cause exciting explosions, and even arc weld.

Shopping online can be as easy as buying cigars in Mexico. You find what you like, ask for the price, and walk away. "My friend! Come back! I give you 10% off. Just for you."

This video tutorial shows How to make a Macrame Bracelet with fish symbol in another way. Historical explanation: The origin of this acronym is something else again. It is not in the Bible. No one really knows who first came up with the acronym ICHTHYS, ( in Greek, it is an acronym for Jesus Christ, the Son of God, our Savior ) used by early Christians as a secret Christian symbol and now known colloquially as the "sign of the fish" or the "Jesus fish".

Recently, there have been some questions regarding networking popping up and we have decided to put together this series to try and cover this gap.

This year in Android has seen a myriad of visual improvements among various apps' user interfaces. From the card swipes of Google Now to the article fade-ins of Circa News, developers have shown that they can strike a beautiful balance between form and function. Check out the following video, complied by redditor hinesh, for some examples.

I am writing this to first pregnant moms. I am 25 weeks along and I have some advice as to getting through an uncomfortable pregnancy.

You saw our post on the 18 coolest new features of iOS 7, but now that you've had a chance to play around with your updated iPhone, it's time to lock it down.

Unless you're a pretty avid home cook, you probably don't know a lot about sous vide. Sous vide is a low-temperature cooking method where food is cooked in vacuum-sealed plastic bags in a water bath for a prolonged period of time.

There are many impressive features on a Samsung Galaxy Note 2, but just like any other smartphone on the market, the most used one is the camera. How many times did you take a picture today? Or admire all the selfies in your gallery? Or upload a video to Instagram, Vine, or Snapchat?

The airline is not your friend. It will do anything it can to gouge your dignity, time, and most of all, money. One of the biggest scams to get a few extra bucks out of you are those dreaded baggage fees. If the lines, security, "random" screenings, and unwanted fondling aren't bad enough, you have to pay them to check your bags (which, most of the time, is done poorly). Flying truly is the most inconvenient way to travel.