In this tutorial, we learn how to do the easy step interview in QuickBooks. Although you can skip this interview, go through it so you don't skip important elements for a solid accounting program. To start, enter all of your company information and then click "next". Select your industry, how it's organized, the first month of your fiscal year, and a password. Continue this information until you are at the end, then save the file for your information somewhere you can easily find it. Make sur...

In this tutorial, we learn how to customize your toolbars in QuickBooks. You will notice that there are a variety of different icons with text to describe them underneath. If you are on a page in QuickBooks and want to add that page to your icon bar, you can go to the view menu and then add this to the icon bar. Now, the icon will appear with text underneath it. You can also change the name of the label if you need to name it something else to remember to the name. You can remove or add these...

Editing with the Canon 7d and Final Cut Pro couldn't be easier, here are some tips to help you get started.

The battery-operated, Bluetooth-controlled pieces use downward-facing sensors to read grids built into the individual squares on the board. They then communicate with the controlling computer to keep track of their location in relation to other pieces. The computer tells each piece which direction to go, and how far, on its turn.

Tats that Fly! Augmented Reality Skin Art

Microsoft Research and Carnegie Mellon University have teamed up to to create an armband that projects a touchscreen interface directly on to your skin. The best part? Skinput knows which part of the body you've tapped, based on the sound that's matched against skin, muscle or skeleton.

As a slightly belated birthday tribute to Photoshop (Photoshop turned 20 this past Friday), here is a clever stop animation short honoring the software.

Adobe Photoshop Creative Suite 3, or CS3, is the industry-standard application for digital photo manipulation. It is ideal for professional photographers, serious amateur photographers, and graphic designers. Having the software, however, isn't enough; you'll need to know how to use it. In this CS3 tutorial, you'll learn how to distress text edges in Adobe Photoshop CS3. Distress text edges in Photoshop CS3.

Get an overview of the award-winning Genuine Fractals 5 plug-in for Photoshop in this software tutorial. The Genuine Fractal 5 plugin allows you to enlarge digital images over 1000% without loosing quality. A must for anyone printing photos or other digital footage. If you are new to the Genuine Fractals 5 Photoshop plug-in, this tutorial is a great place to start. Get started with Genuine Fractals 5 Photoshop plugin.

In part one of this 3 part series on using the blur tools in Autodesk's Toxik software, you will be introduced to the blur tool UI and it's related tabs and learn how to create directional blurs and reproduce motion blur with the Radial blur. Part two goes over simulating convincing depth of field with the Modulated Blur, and part three covers using forward vectors to create realistic motion blur. Use the blur tools in Toxik - Part 1 of 3.

In part one of this Final Cut Pro tutorial, Ben Scott shows you how to use the text generator and how to make broadcast safe titles that don't flicker. Part two goes over taking your titles out of Final Cut Pro, using Apple's Motion software to create nicer text for your titles, then bring them back to Final Cut Pro. Create titles in Final Cut Pro - Part 1 of 2.

Apple just released iOS 12.5.1 (build number 16H22) for iPhone 5S, 6, and 6 Plus, as well as iPod touch 6th generation, in addition to iPadOS 12.5.1 for iPad Air, mini 2, and mini 3. The update fixes an issue in iOS 12.5 where Exposure Notifications could incorrectly display logging profile language.

Well this law was passed... Our privacy is slowly being pulled away from us. But I'm certainly not going to let it stop me. We'll just have to take more secure measures. If You Use Tor Browser, The FBI Just Labeled You a Criminal.

FBI has taken down a notorious hacking forum called "darkode" where cyber criminals bought, sold and traded hacked databases, stolen bank accounts, and malicious software that steal information from other computer systems and helped each other to infiltrate other computers. The FBI called the site one of the most serious threats to data security in the world. criminal charges has been filed against 12 individuals who were associated with the forum and the investigation is still ongoing, more ...

When turning your 3D model into a 3D print, Maya requires some extra editing before you end up with a printable piece: the wall thickness needs to be checked, the model needs to be watertight, and your final printing size needs to be defined. To make your life easier, Autodesk Maya expert Russ Ogi has put together a step-by-step tutorial about how to make your Maya 3D model printable. See more at: 3D Printing with Maya: Step-by-Step Tutorial on How to Turn Your 3D Model into a 3D Print.

With 2015's generation of flagship smartphones fast approaching, LG is turning to virtual reality to clear its G3 inventory. VR for G3 is a Google Cardboard-inspired virtual reality headset that was custom fit to encase the phone and uses a pair of lenses to create stereoscopic imagery.

Christmas is only a few days away with New Year's right around the corner. If you're like me, you count down the days until Christmas for family and presents like a little kid, and then count down the days until New Year's like an adult that can't wait to have their first cocktail.

Apple's fix to its previous fix—which was a complete and utter disaster—is rolling out now, thankfully ahead of the "few days" they stated earlier. The update to iOS 8.0.2 fixes the issues with cell signal and Touch ID, as well as the the previous bugs 8.0.1 aimed to squash. No matter if you took the update and have had a de facto iPod the past 24+ hours, or whether you reverted back to iOS 8.0, you'll want to install this update pronto.

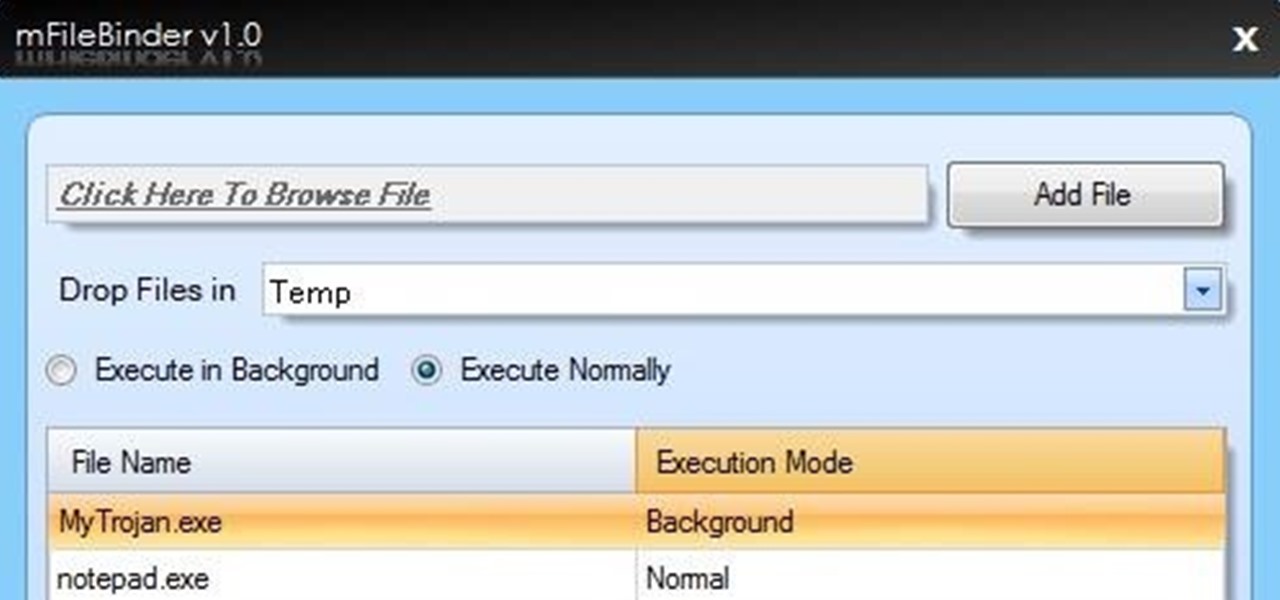
`Today I am going to tell you how to bind i.e. join two or more files and make single executable file.

Google has updated the MyGlass application for Android, fixing several bugs, redesigning the user interface, and including a feature to allow Explorers to share Google Maps locations from their device to their Glass. If you haven't updated yet, do so now, then follow along as we go through it. Redesigned User Interface

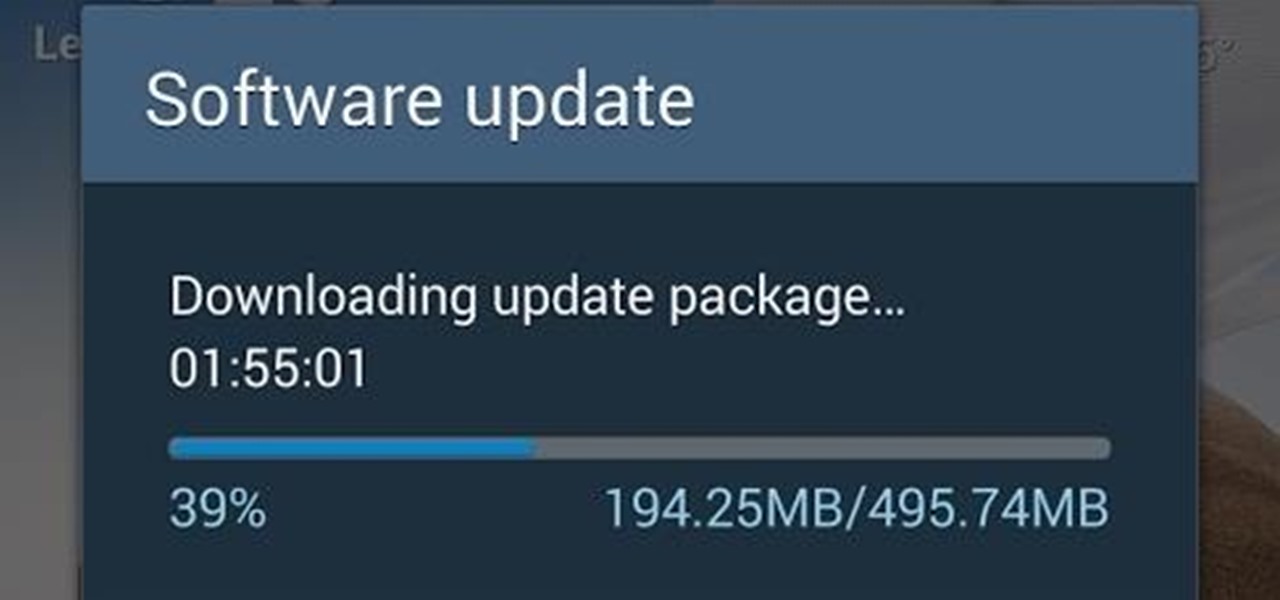
A few days ago, we got word that Verizon's KitKat update to the Samsung Galaxy S4 was scheduled for release on May 2nd, 2014. However, this morning the OTA update was popping up on devices all over the states, ready for download and installation. Galaxy S4 owners on various other carriers have reported a myriad of problems with the new update, such as increased battery drain, missing apps, and the inability to write to their SD cards—most of which we've been able to find workarounds for. Pres...

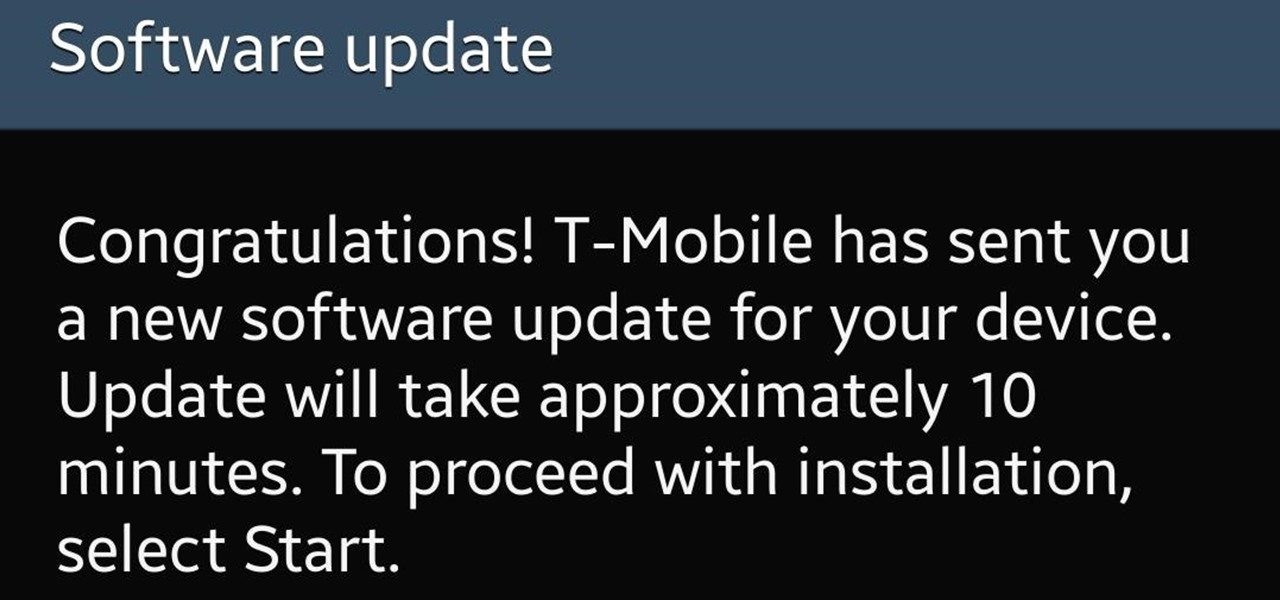
Starting today, T-Mobile has begun rolling out the Android 4.4.2 KitKat update to their Galaxy S4s. The roughly 390MB update brings the standard KitKat fare to your GS4, including:

As reported by member Rick, the Android 4.4.2 KitKat update is rolling out right now for the T-Mobile variant of the Samsung Galaxy Note 3, matching the Sprint and US Cellular updates from last week. While we don't have any specifics from T-Mobile regarding the update, it can be assumed that it brings the standard KitKat features such as immersive mode, transparent status bar, lock screen upgrades, and cloud printing support.

Per an anonymous leak yesterday and an official announcement today, the latest version of Android, KitKat (4.4), is rolling out right now for Sprint's variant of the Galaxy S4.

UPDATE: Verizon has posted their support document, with everything you need to know about this update. Last week it was Sprint's turn to push out Android 4.4 KitKat for the HTC One, and today it's Verizon Wireless who's up to bat.

Falling in line with tradition, Samsung is ever-so-subtly teasing their big Galaxy S5 reveal at an event dubbed Unpacked 5. Just like with previous releases, we've seen a steady stream of information leak about Samsung's next flagship, from possible UI elements to more detailed hardward and software information. Now, we've got a date to look forward to, on the first day of Mobile World Congress no less.

As announced today, Sprint customers can manually update their HTC One devices to the latest version of Android, called KitKat.

HTC has started rolling out it's KitKat update (Android 4.4.2) for the HTC One to French carrier SFR, expanding on the original update to it's Google Play Edition devices from November. Update roll outs tend to begin in Europe, Asia, and Africa before hitting stateside, but the release means we can't be too far away from a public build. As always, US carriers take much longer than their international counterparts, but the French OTA (over-the-air) update means that, for all intents and purpos...

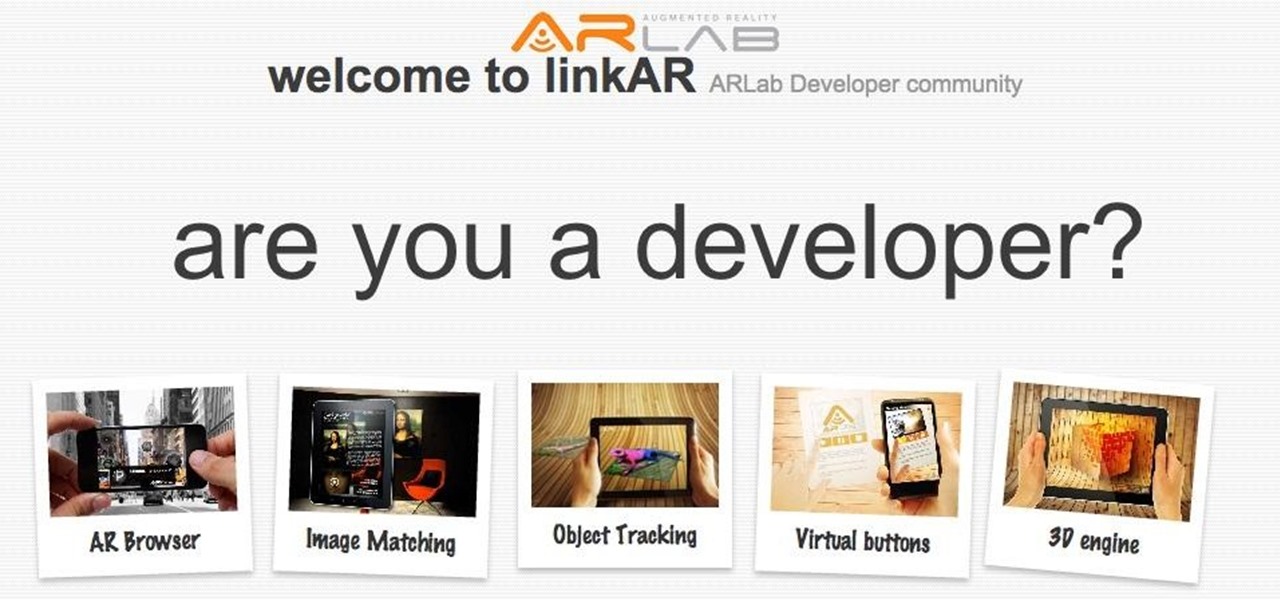
Hello, I'm Daniel Yelamos and I'm the CM of ARLab, a Spanish-Israel company that develops AR solutions. We've released a couple of SDKs and a few apps based on AR to help people develop this kind of software. Last week we released LinkAR, a social community for developers interested in AR community, I could type and type about all its features, but why don't you watch it for yourselves here?

With Facebook and Twitter dominating the world, playing chess opposite a real, touchable person is no longer necessary. With the ChessBot, you can now play on a real chessboard remotely - the next best thing to in-person play.

Even if you do not understand Photoshop, you should watch this, because the storytelling is great. As our 90,000+ video library attests, how-to's are a genre, per se. And screencasts are a particular sub-genre, especially useful for software instruction.

If you're an owner of a BlackBerry smartphone, chances are you're going to want to use BBM, which for all of you newbie BlackBerry owners, stands for BlackBerry Messenger. BBM is an instant messaging application developed solely for BlackBerry device owners.

Remember that scene in The Matrix when Trinity uses a realistic Nmap port scan, followed by an actual SSH exploit (long since patched) to break into a power company? Well, believe it or not, but that scene is not far fetched at all. If you want to exploit vulnerabilities and root boxes, you'll need to learn how to perform the necessary reconnaissance first. In fact, you will spend far more time researching your target then you will exploiting it. In this article, I am going to show you the fi...

Have you ever forgotten your password and didn't know how to get back on your computer? Or ever had an annoying roommate you wanted to play a trick on to teach them a lesson? Or perhaps overly religious parents who think the internet is of the devil and won't let you read online articles about elliptic curve cryptography applications to C++? Well, then this article is for you!

The already robust and ingenious Nmap tool has received a whole slew of new scanning scripts that can be used to do all sorts of naughty endeavors. Notably, the SQLi module, since it is a necessary evil that we must cover here at Null Byte. This major update is going to fuel today's lesson.

When Windows stores a password, it is done so by hashing the password in an LM hash and putting it in the Windows SAM file. In the scary moment that you lose your password, but don't want to pay some geek to have full root access to your computer, you need to recover it using Ophcrack. Ophcrack doesn't remove the password, or bypass it, it cracks the password hash using rainbow tables.

File recovery on Linux is a bit different than Windows. It requires different software than the Windows counterparts because every OS has their own file system. Windows uses NTFS, or FAT file systems, while on the other hand, Linux uses ext-based file systems. I personally use ext4 file system because it's the latest and greatest ext-journaling system and supports a large level of directory recursion and file sizes, but most installations still use ext2 or ext3. When files are deleted from a ...

Permanently deleting files is something that a lot of people aren't aware of. Actually, most people think that once a file is deleted, it is gone forever. This is not the case. Hard drives write to the disk via magnetic charges, positive and negative correlate to 1s and 0s for binary. This is then interpreted into information for the computer to use and access.

Welcome to part two in a series about steganography, the art of hiding things in plain sight. We are practicing steganography because it can be a useful skill if you don't have access to encryption software, or need a quick solution to make sure the sender and recipient are the only ones who are able to read your message.

If you're interested in bypassing Windows and Linux passwords, there is a great tool from the good people at Kryptoslogic. Have you ever forgotten your administrator password? Have you ever bought a used computer with a password on it? Well, Kryptoslogic have created a boot-disc call 'Kon-Boot', which allows you to bypass any Windows 32 or 64 bit OS, as well as Linux passwords. There is both a paid and freeware version available.