These instructional animated slides teach you how to easily fold a paper Halloween Frankenstein face Japanese style. Learn how to use the Japanese art of origami to make your own Frankenstein face. Use the start, stop, forward and back buttons to easily follow along. You can also speed up the instructional origami video if it is going too slow. Very cool Japanese origami how-to video! Origami a paper Halloween Frankenstein face.

These instructional animated slides teach you how to easily fold a paper werewolf face Japanese style. Learn how to use the Japanese art of origami to make your own paper werewolf face. Use the start, stop, forward and back buttons to easily follow along. You can also speed up the instructional origami video if it is going too slow. Very cool Japanese origami how-to video! Origami a paper Japanese werewolf face.

This video shows you how to do a face toning massage. It is a very simple technique to energize and rejuvenate the face. The natural lift. Do a face toning massage.

If you want to learn how to make a 3D game using C++, then this is where you should start. This video lesson will show you how to download and set up OpenGL and GLUT for Microsoft Visual C++ Express on a computer running a Windows operating system.

Artist Jo dePear and VideoJug team up to show you how to draw a face in this informative video. You will need paper, pencils and a ruler. First draw an outline. Draw dividing lines to map out the proportions of the face. Then what? You will have to watch! Draw a face.

Whether you are protecting your children or hiding personal information, there are ways to block unwanted websites from your computer. Follow this tutorial and learn how to accomplish this on a Windows PC easily.

With 2 simple props and a bit of sleight of hand, you can be well on your way to performing an interesting card trick.

Getting Started Steps for Beginners If you are brand new to Expression Web 4, then read the following guide to quickly set up your web site and web pages.

An iPad can serve as a second screen for a Mac via Sidecar, available since iPadOS 13, but Apple isn't the only manufacturer to support such a feature. Samsung has had a similar tool since One UI 3.1 that lets you turn certain Samsung Galaxy tablets into second displays for your PC — and there's a hidden feature that expands it to more tablets and even Samsung Galaxy smartphones.

It's 2022, and the coronavirus pandemic is still going strong, meaning many people still wear masks. If that's you, unlocking your iPhone with Face ID is still very inconvenient when donning a face covering — until now.

For those not used to it, working from home can be a difficult transition. Everything around you can be a distraction, and distance from your boss and coworkers means less pressure and incentive to get things done. So it's not surprising to see a major drop in productivity during a period of self-quarantine, but your phone can help you stay on track instead of sidetracking you.

The response to the COVID-19 pandemic means that social distancing has become the new normal. It also means that more Americans are using video conferencing to connect with colleagues working from home or friends and family in quarantine because of the new coronavirus.

Facebook recently hit a snag in its quest to take augmented reality face effects to its millions of users.

When it comes to filters, Snapchat is no slouch. The chat app's array of effects rivals even the fiercest competition from filter masters like Instagram. Now, the company has a new trick up its sleeve that adds depth to your selfies (and even more new filters), and that feature is called 3D Camera Mode, available for iPhone models with the TrueDepth camera used for Face ID.

Microsoft.com is one of the most extensive domains on the internet with thousands of registered subdomains. Windows 10 will ping these subdomains hundreds of times an hour, making it challenging to firewall and monitor all of the requests made by the operating system. An attacker can use these subdomains to serve payloads to evade network firewalls.

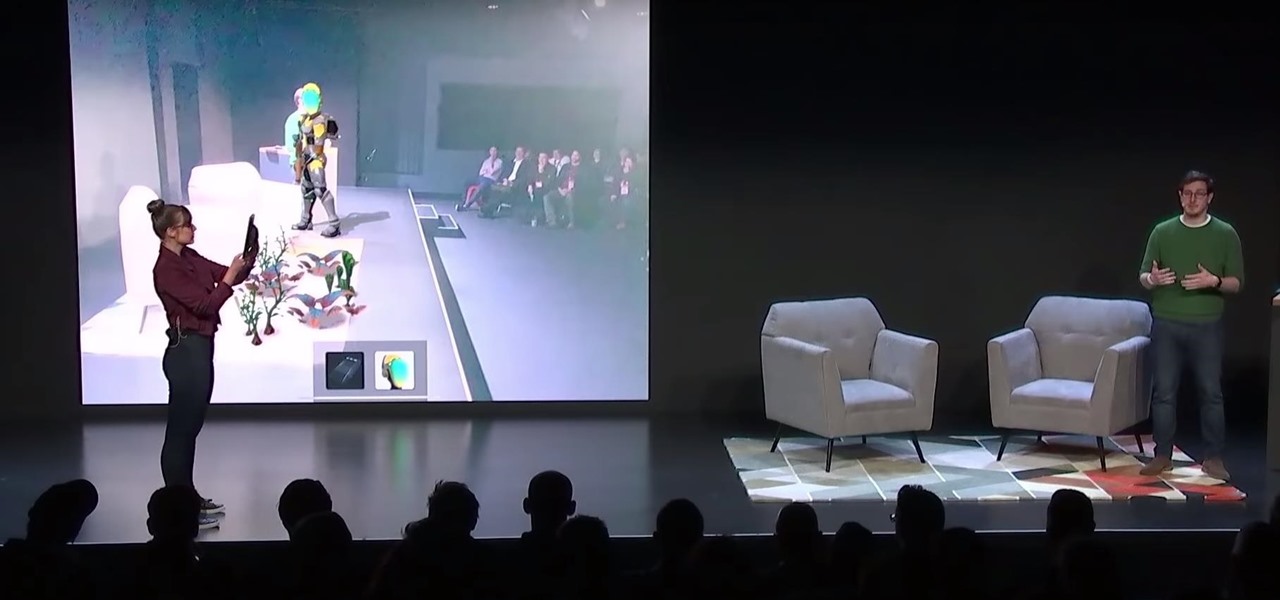
After Apple unveiled ARKit 3 at WWDC on Monday, Unity Technologies wasted little time on ensuring its developers can take advantage of it.

With an inconspicuous Android phone and USB flash drive, an attacker can compromise a Windows 10 computer in less than 15 seconds. Once a root shell has been established, long-term persistence to the backdoor can be configured with just two simple commands — all while bypassing antivirus software and Windows Defender.

If you're ever faced with a situation of handing over your iPhone to law enforcement (or getting it taken forcibly), whether by the police, feds, or court system, there are things you can do to prevent them from getting access to all that potentially self-incriminating data. And it takes less than a second.

With the Galaxy Note 9's 6.4-inch AMOLED display, split screen is far more useful since each half of the screen is relatively large. The problem is that there are some noticeable omissions in the list of apps which support the feature. However, Samsung offers a fix for this.

In order to increase the security and harden the integrity of an email account and its content, you'll want to use PGP on your Windows, macOS, or Linux computer. This is usually the first thing security analysts do to protect communications with encryption, and everyone else should consider it too, especially since there's an easy way to incorporate PGP that anyone can follow.

It looks like Snapchat is becoming the MTV of augmented reality. On Thursday, Ariana Grande, with her new album Sweetner, joined Drake and Nicki Minaj and other artists who are pushing new releases through Snapchat's Shoppable AR e-commerce platform.

The latest preview build for Microsoft HoloLens is packed with new sharing features, including support for the Miracast protocol.

While 3D motion capture via iPhone X is coming soon from Unity, software maker Reallusion offers similar functionality to 3D model animation producers today.

Analysis of photographs and social connections can be a huge component of social engineering. Understanding who a person is, as well as who they know, can establish links within a company. This information could be used by hackers to execute elaborate social engineering attacks.

Apple's iPhone X now has the power to turn anyone into a Japanese anime character, thanks to a new app that harnesses the device's TrueDepth camera.

Screenshots taken from a compromised computer can provide hackers with access to private emails, photographs, and information found in sensitive documents. This data can be used by the attackers to build profiles of a target for social engineering attacks and blackmail or even just to release the information out in the wild.

As a developer, before you can make augmented-reality robots that move around in the real world, controlled by a user's finger, you first need to learn how to harness the basics of designing AR software for a touchscreen interface.

Augmented reality developers are rapidly bringing science fiction tropes into the real world, with the latest example leveraging the TrueDepth camera on the iPhone X to emulate the cloaking technology made famous by movies like Predator and Marvel's The Avengers.

Highways are among the most efficient routes of driving from one place to another. Unfortunately, however, they're also the most used route taken by everyone else resulting in migraine-inducing congestion, especially during rush hour. Thankfully, Apple Maps has a feature that will direct you along lesser known routes that could be faster and/or safer.

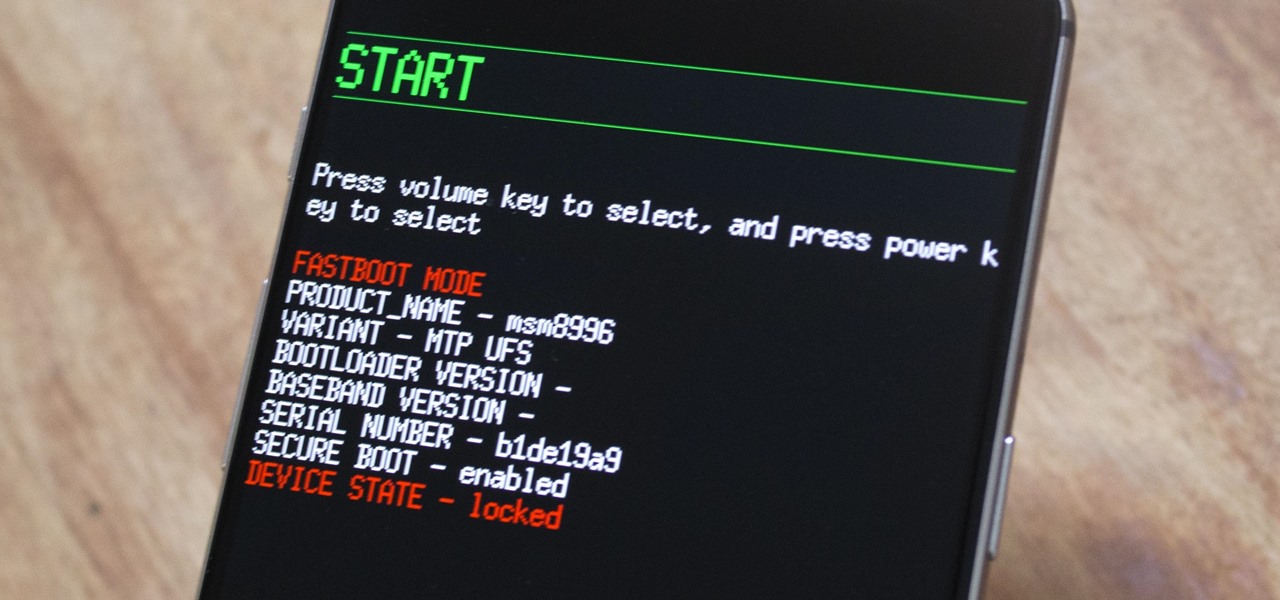
Despite concerns with SafetyNet, Google actually cares about root. Every phone they sell has an unlockable bootloader, so you can toggle a setting and send a Fastboot command, then start flashing custom firmware right away. The Pixel 2 and Pixel 2 XL continue this tradition, and now they have an official root method.

Karen Gillan must have had an absolute blast chewing the scenery as Nebula in Guardians of the Galaxy Vol. 2, seeing as how Nebula is a ball of pure, seething fury pretty much 24/7. Combine that larger-than-life personality with her iconic blue and silver cyborg look, and you have a guaranteed hit for cosplay or Halloween.

If you've spent countless hours scrolling through Instagram feeds full of selfies, then I'm sure you know that some are, well ... better than others. There are so many different things you can do to start taking better selfies to post on social media. One really easy way is to start shooting in VSCO.

Generally speaking, in terms of modern devices, the more simple you make an interface to navigate, the more successful the product is.

At the end of June, Unity 2017.1, the newest version of the popular 3D development engine, went live. And with that release, it brought out some very cool new features like Timeline and Cinemachine, to name a few. Now, for those of us that develop with Unity and follow the beta program closely, these features are not new at all. What is more likely the case is that we have spent a good deal of time using these features for a few months and even possibly helped iron out a few bugs.

Keystroke injection attacks are popular because they exploit the trust computers have in human interface devices (HIDs). One of the most popular and easily accessible keystroke injection tools is the USB Rubber Ducky from Hack5, which has a huge range of uses beyond simple HID attacks. The USB Rubber Ducky can be used to attack any unlocked computer in seconds or to automate processes and save time.

In the nascent AR/VR race, any release news is big news. For augmented reality, those invested in the new technology eagerly await the release of Microsoft's Hololens and any inkling of information that comes with it. If you're one of those folks, you're in luck, as new information has just been disclosed about one of Microsoft's partners on the project, Lenovo, and their Hololens; including its release date and price.

The OnePlus 3 and 3T are two of the most modder-friendly devices to be released in 2016. Not only that, but they're both extremely solid phones which happen to sport a very reasonable price tag. Among the things that make these devices such a joy for tinkerers is the fact that they have an unlockable bootloader, receive timely kernel source releases, and are actually quite easy to root.

In an early morning blog post, Microsoft announced the expansion of the Microsoft HoloLens Agency Readiness Partner Program. This announcement comes on the tail of an expanded HoloLens release over the last few months to many countries outside the initial US and Canada.

If anyone has every told you that they see music they listen to, they have synesthesia. It's a fascinating neurological phenomenon where people experience crossed responses to stimuli, and no one knows exactly how common this is. A rough estimate claims that one in every 5,000 to 100,000 people is a synesthete, but it could be far more common or rare. Nobody really knows.

Any developer working with the HoloLens knows that the fight for polygons is a very real conflict. For all of the magic it creates, the HoloLens is a high-powered mobile device that has all the typical processing limitations of a mobile device.