
How To: Security-Oriented C Tutorial 0x17 - Structs
What's up, peeps? In this quick tutorial, we will be looking at structs, a special kind of data type.


What's up, peeps? In this quick tutorial, we will be looking at structs, a special kind of data type.

Greetings to all geeks, hackers, nerds, and explorers of Null Byte. Welcome to my brand new tutorial, "Using BASH for Computer Forensics". This tutorial will give you a look at how the computer programming language, Bash, can be used to find out details on apple devices for later use.

Welcome to another C tutorial. We will be looking at arrays, discussing what they are, when they are used and their special relationship with the char variable. Let's begin.

Hello NullByte! This will be my first How To series.

Welcome back! In the last round of python training, we talked about tuples and dictionaries. We'll be diverging again and talking about logical operators as well as membership operators. These are used very similiar to booleans, so if you haven't read that, I suggest you do so first.

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Greetings all. Before I get into the tutorial, I would like to mention that I am fairly new to Null Byte (been lurking for some time though), and what really appeals to me about this place is its tight, family-like community where everyone is always willing to help each other and the constant search for knowledge that inhabits this subdomain is a driving motivator for me to join in. I'm glad I arrived at the right time. Anyway, wipes tears (not really)...

Welcome back, my greenhorn hackers! Many new hackers come from a Windows background, but seldom, if ever, use its built-in command-line tools. As a hacker, you will often be forced to control the target system using just Windows commands and no GUI.

WPA Enterprise is widely used in large corporations as it offers individual and centralized control through a server that authenticate the users (RADIUS server). In this tutorial I will show you how to break the barrier and obtain the user credentials.

Ruby is a dynamic, general-purpose programming language created by Yukihiro "Matz" Matsumoto in Japan around the mid-90's. It has many uses but with it's flexibility, it makes a great language to write exploits in. In fact, the entire Metasploit Framework is written in Ruby! The sole purpose of this series is to teach hackers the basics of Ruby, along with some more advanced concepts that are important in hacking.
Do you remember my last article on how to hook any web browser with MITMf and BeEF? Well, we are using the tool once again, but this time for auto-backdooring....
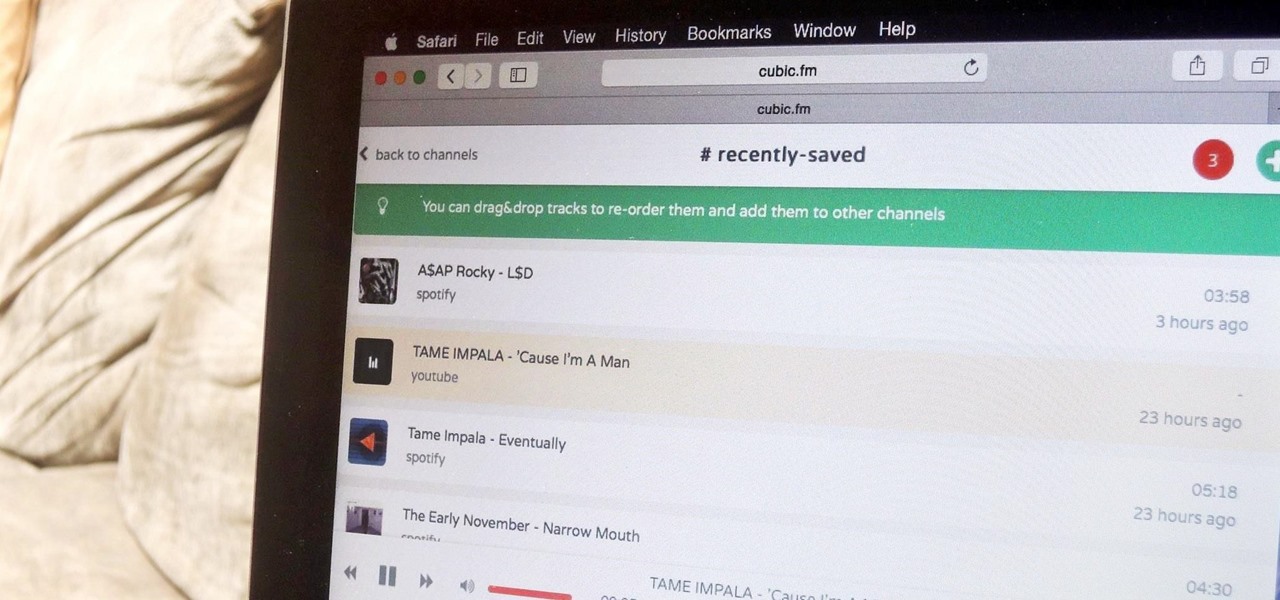
The options for finding random or specific music to listen to are vast. Spotify is excellent for streaming popular music and new releases, while SoundCloud provides a healthy dose of user-generated remixes and originals. And then there's YouTube for everything else.

Smartphone users often wish for a privacy, where no one is able to poke his/her nose in their personal stuff. Unfortunately, none of the smartphones have been able to guard their privacy in this fashion. Smartphones usually come up with none or almost negligible built-in security to serve your purpose.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

If you're a fan of Thai food, I'm sure you're familiar with sticky rice. There is something so special about its chewy texture and sweet flavor. If you have a desire to make it in your own kitchen but don't have the proper tools such as a traditional bamboo basket or stackable steamer, there are several other methods that work just as well. Once you try these alternative methods, I'm sure you'll be "sticking" to them for a while. What Makes Sticky Rice So Sticky?

When it comes to passwords, the longer and more complex they are, the better the security. Even professional hackers say so. But if you've ever tried to type in such a password, you've surely noticed that it can be a bit of a pain. Mistype one character, and you're probably going to have to clear the field and start all over again.

Welcome back, my apprentice hackers! In this series on password cracking, I have been attempting to develop your skills in the age-old art of password cracking. Although it might seem like a simple and straightforward exercise, those of you who have attempted password cracking know that there are many subtleties to this art.

This is the best how-to's website that I've ever seen, and I wanted to join it. It taught me a lot, but, because I'm here to learn too, please correct me if I'm wrong.

Welcome back, my greenhorn hackers! Continuing with my series on how to crack passwords, I now want to introduce you to one of the newest and best designed password crackers out there—hashcat. The beauty of hashcat is in its design, which focuses on speed and versatility. It enables us to crack multiple types of hashes, in multiple ways, very fast.
Android has had predictive text for a while now, both with stock and third-party keyboards such as Fleksy, SwiftKey, TouchPal, et al. Apple is even getting on board, with stock predictive text and third-party keyboards for iOS 8, slated for public release later this year.

Welcome back, my hacker novitiates! In previous guides, we have used one of the most powerful hacking platforms on the planet, Metasploit, to perform numerous hacks. They ranged from exploiting Windows XP and Windows 7/8 vulnerabilities, to installing a keylogger and turning on a webcam remotely. We have even been able to save the world from nuclear annihilation, see if our girlfriend is cheating, spy on suspicious neighbors, evade antivirus detection, and more.

Welcome back, my greenhorn hackers! My preference for Linux as a hacking platform is well documented, and I have even created a series of tutorials to train new hackers. Without being proficient in Linux, you can't really call yourself a hacker.
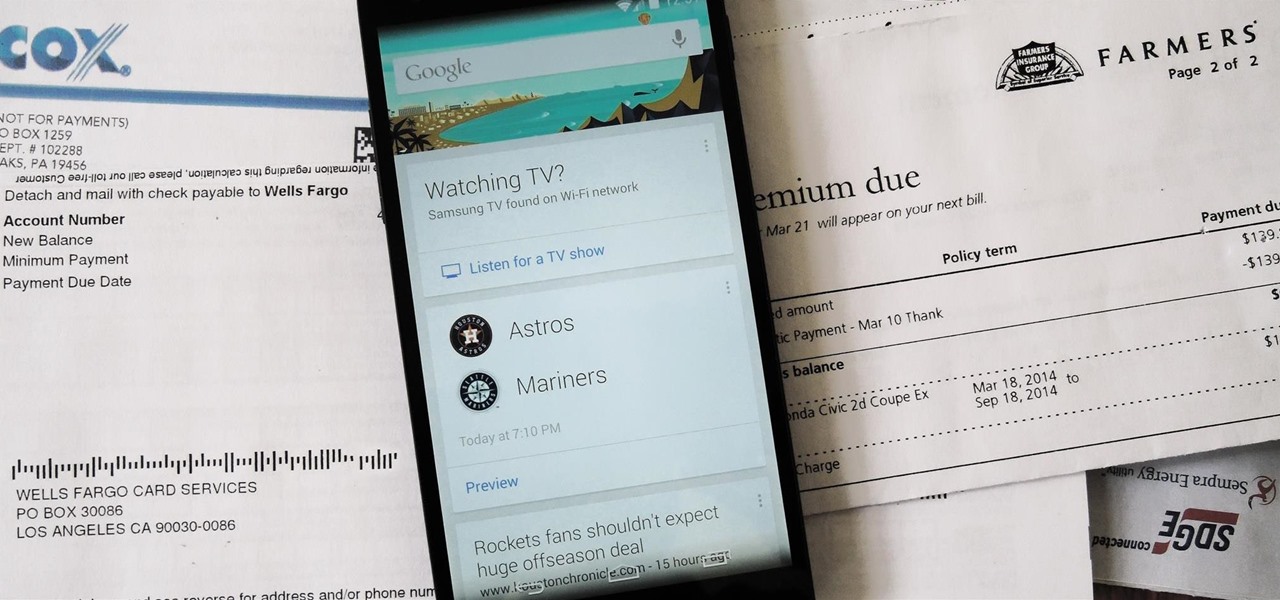
Google is widely renowned for its mastery in using data to tailor specific search results and ads. Their Android and iOS search apps put this ability to use in finding the most relevant pages for your query, and their desktop site is the most-used search engine on the web as a result of it.

Welcome back, my greenhorn hackers! Sometimes, we don't have a specific target in mind, but rather we are simply looking for vulnerable and easy-to-hack targets anywhere on the planet. Wouldn't be great if we had a search engine like Google that could help us find these targets? Well, we do, and it's called Shodan!
What can be said about Spotify that most of us don't already know? It's the most popular digital music streaming service out there, giving you access to millions of songs on your computer. However, the mobile service was once an exclusive feature for paid subscribers. Not anymore, suckers.

Welcome back, my rookie hackers! Many newbie hackers focus upon the technical aspects of hacking and fail to give enough attention to social engineering. In fact, I would say that technical hacks should ONLY be attempted if social engineering attacks fail. Why bother spending hours or days trying to hack a password if someone will simply give it to you?
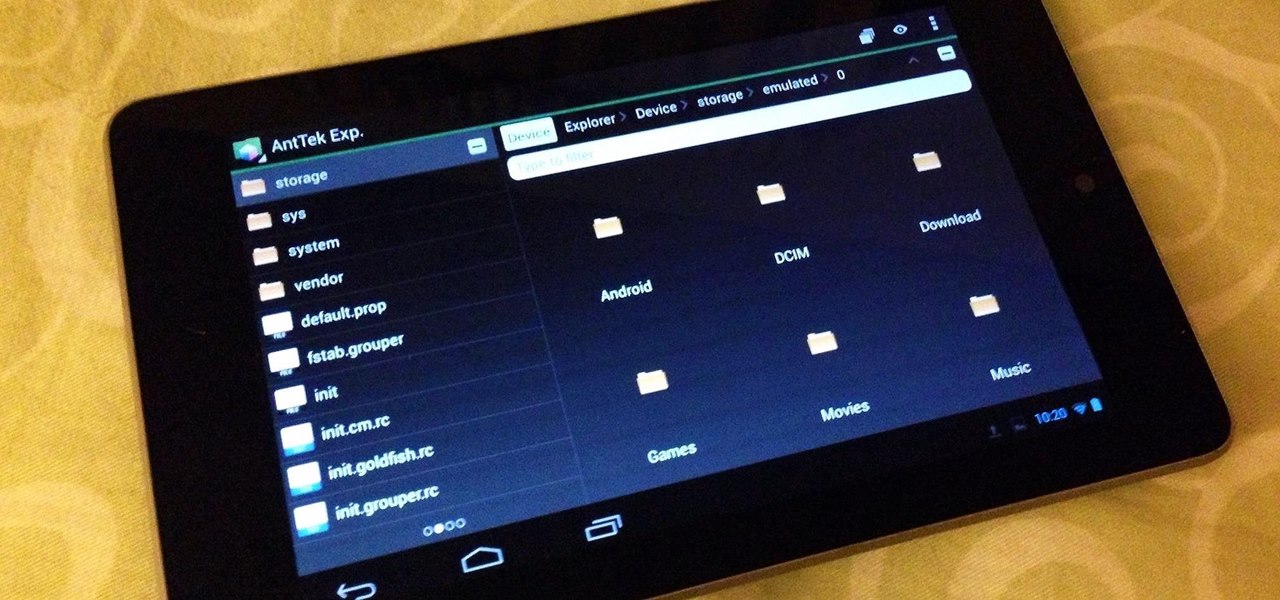
If you're always on the go, the Nexus 7 is a godsend for having everything you need at the tip of your fingers—music, videos, text documents, photos, and more. Unfortunately, as good as that is, it also means one hell of a messy tablet.

Welcome back, my greenhorn hackers! Congratulations on your successful hack that saved the world from nuclear annihilation from our little, bellicose, Twinkie-eating dictator. The rest of world may not know what you did, but I do. Good job! Now that we hacked into the malevolent dictator's computer and temporarily disabled his nuclear launch capability, we have to think about covering our tracks so that he and his minions can't track our good works back to us.

Texting is a godsend to mobile devices, but it also has its caveats. Sending a text to someone requires visual, manual, and cognitive attention—looking at what you're typing, holding the phone steady, and thinking about what you're trying to say. So, texting while doing pretty much anything else is not a wise move.

iOS 5 introduces an incredible feature that isn't very well known called "Shortcuts." It allows you to use automatic text expansion for whatever abbreviations you want. This is a great way to type several letters into your iPhone, iPad, or iPod touch and have them immediately expand into whatever phrase you want. Find out how to configure text expansion in this guide.

Colored contact lenses are becoming more popular these days, and prescription lenses are still seeing more use as well. This guide will walk you through the process of cleaning and maintaining both types of lenses as well as inserting them over your eye.

This guide to replacing the timing belt and water pump on a Ford Escort is for a 95 Escort, but it will likely help with several different types of vehicles. Watch as both the timing belt and the water pump are removed carefully from the car and then replaced with new parts.
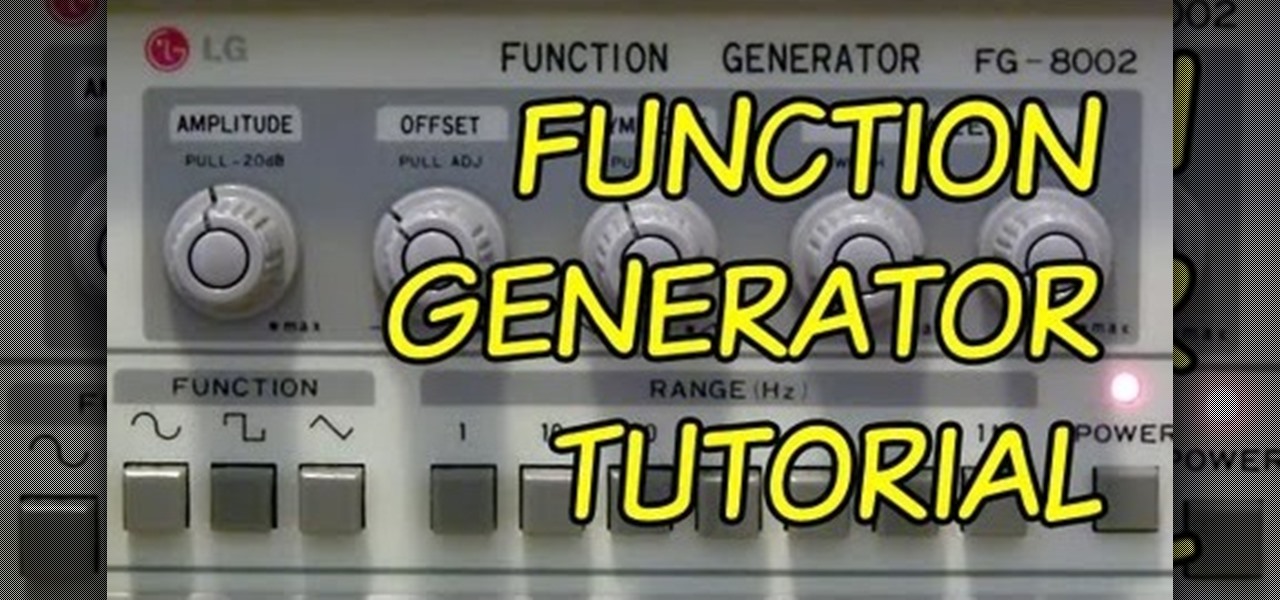
A function or signal generator is an electronic device that can create different types of waves and send them through a circuit without building oscillators. This video will teach you how they work and how to build a basic LED dimmer that uses one as an example.

The Nokia N900 smartphone suffers from a lack of quality games due to Nokia's restrictive OS, but fortunately you can get WebOS games from the Palm Pre loaded onto it pretty easily by following the steps outlined in this video tutorial.

Fatwood is an immense boon for any wilderness survival situation. It's a type of tree that has soaked up tons of nutrients from the ground and is perfect for starting fires. It can be broken down into kindling that will start fires for you time and time again. This video will teach you how to find fatwood and how to use it once you find it.

This bloke has very strong opinions about the different types of Elemental Hero (e-hero) decks in Yu-Gi-Oh! the card game. In this video he breaks down why his e-hero deck and e-hero philosophy in general are superior to others and why Elemental Recharge is a crappy card.

An electrophorus is a type of capacitor that generates electrostatic energy. Most of you probably know this force as static electricity, the domain of door handles and polyester shirts. It can be used for all sorts of other fun science experiments though, and this video will show you how an old hard drive, some plastic, Styrofoam, foil, a cat, and other simple materials can be used to make a a simple functioning electrophorus.

Lasers are one of the coolest things that you can build yourself from a pure sci-fi fantasy standpoint. They're not easy though, but this video will help you somewhat by describing different types of laser diodes and how to connect them to a power supply.
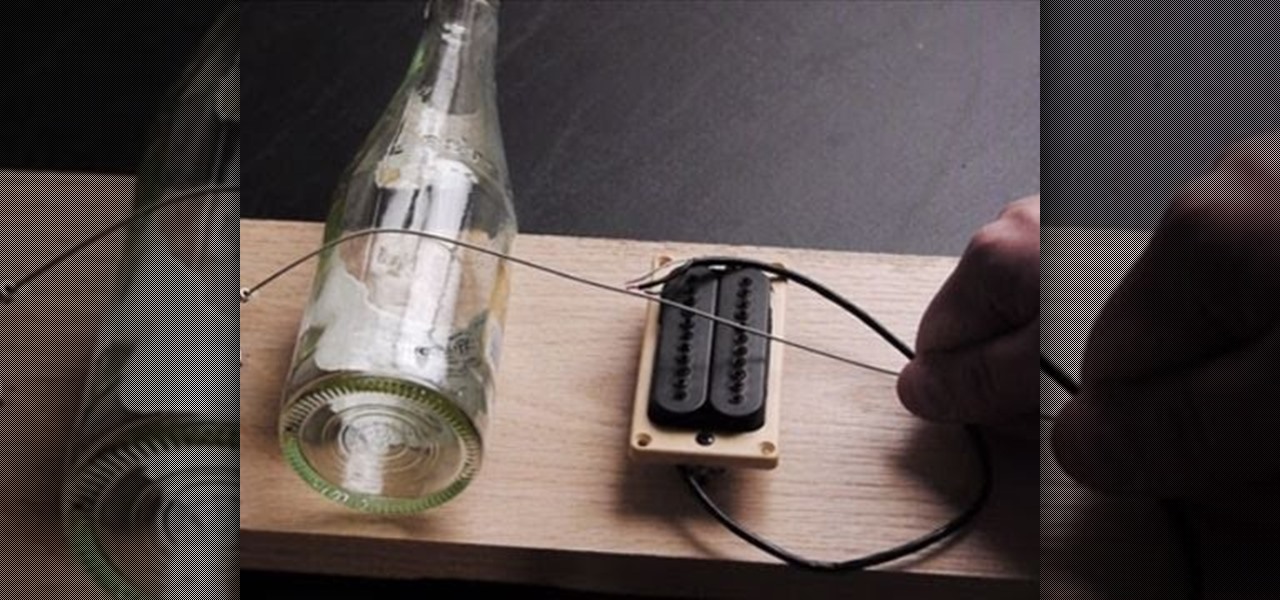
If you've ever seen It Might Get Loud, you probably remember the part where Jack White makes a one-string guitar out of household scraps. This type of guitar is called a Diddley Bow, after Bo Diddley, and is about the simplest and easiest electric guitar you can make. Watch this video to learn how.

The lightsaber is one of the coolest weapons in the history of cinema, and the original props came from a junkyard. Funny how that works right? If you want a lightsaber for your own film, costume, or just because they're awesome, watch this video for a guide to making three types of lightsabers: a cheap one, a medium one, and very expensive professional-quality one.