Tass has compiled a video showing players a walk through of Civiballs, Christmas Edition, Outdoors. Players are shown how to 'cut' certain strings in order to achieve maximum points and divert the balls and objects into areas at specific timing for the best results. The balls are supposed to land into gift boxes that Santa can then deliver on Christmas. Maneuvering objects in the game such as swings, cannons, slopes, balls, Mr. Yeti and other various obstacles allows the player to customize w...

This video will go over how to insert a check box in Microsoft Word for printing or for electronic distribution. With just a few clicks you can get a check box. You can even add different symbols or styles for your check box.

Human beings are one of the hardest things to draw. If you are having trouble drawing the female figure, have a look at this tutorial. This tutorial will show you how to split the human body up into 8 different parts, making it easier to focus on a specific area and draw it. This video was made on Photoshop, but you can just as easily follow the same steps in pencil. Follow along and soon you will be drawing realistic looking people easily.

JamesKesn teaches you how to hack a vending machine. You must use a very specific machine and an exact combination of button presses. For this it is: far left Pepsi, near right Mountain Dew, near left Pepsi, far right Mountain Dew. Then far left Pepsi, near right Mountain Dew. Again, far left Pepsi, near left Pepsi, near right Mountain Dew and far right Mountain Dew. This hack will allow you to see the stats, set the price and see error logs.

In this Labrats video tutorial the instructors Andy Walker and Seab Carruthers show how to undelete the deleted files and recover them. When you save data to your computer, the computer stores the data in the binary format on the hard disk. To keep track of the files, the Operating System maintains a file table that shows the location of the data on the hard disk for a specific file. There are many file formats like FAT, NTFS etc. So when you are erasing the file only the entry in the file ta...

A video from PC Mech that shows you how to install application in Sabayon Linux, a Linux flavor that is based on Gentoo Linux and is known for its ease of use.

In this video a young college student shows what you'll need to make marsala steak and mushrooms. She shows what pots you will need along with what kind of steak and mushrooms you need. She shows how to add everything to its specific cooking area. She tells why she is adding the ingredients as she adds them. She goes on to show the seasonings to use. She then shows how to prepare the steak and the sides that she cooked along with it.

This is a condition where the tissue that's supposed to grow inside of your uterus starts growing outside of your uterus on other organs. It's not usually dangerous and doesn't have any side effects, but it can be very painful and also can give you trouble conceiving, if you're trying to have a baby. Adjusting your diet and foods you eat can help with endometriosis. Learn how to adjust your diet to fit your specific health and nutrition needs in this nutrition how-to video.

Kundalini yoga poses are combined with specific breathing exercises that decrease tension in the lower body. Learn how to do Kundalini yoga in this Kundalini video lesson. Take Action: practice in morning, wear white, chant, do warming exercises, open chakras and do cool down exercises. Cindy Mastry, the instructor of this how-to video, has practiced yoga since the age of eight, and also has a background in Jazz and Ballet. Active in the fitness industry for nearly twenty years, she teaches a...

Yoga is great for improving flexibility, but if you are truly stiff and locked up, there are specific poses that can help you move forward more quickly. Flexibility is not hard if you know which poses to practice and how to practice. Many yoga teachers will tell you to take it easy, be safe, and take your time. Yoga can work miracles, but you have to work too. Learn how to do yoga poses to get a more flexible body.

In this how-to video Chef Jason Hill shows you how to make a quesadilla. This chicken quesadilla recipe is the best you'll find out there. It is perfect for a quick snack or light meal. Add some grilled shrimp instead of chicken and you'll have a fantastic shrimp quesadilla recipe. For this specific recipe you will need: one boiled chicken breast, pepper jack cheese, green onions, sea salt, chilies, taco seasoning, cream cheese, cilantro, and flour tortillas.

The Drink Of the Gods. Yerba Mate. Learn how to prepare Yerba Mate and drink it properly with sexy Gianny L! You will enjoy the ceremony and will notice a subtle lift, due to the caffeine (mateine) contained in it. GiannyL demonstrates how it's all done.

For preschoolers a great art and science activity! Lot's of small motor skills are involved with brushing and placing tissue paper. The reaction from the tissue paper and vinegar is the exciting science element of the activity. Art gives your child a chance to express themselves through their imagination. Art allows children to explore and understand their world through creative experiences that emphasize the process of art, not the product. When your child is creating there is no right or wr...

In this series of videos you'll learn how to draw with charcoal from a professional artist. Expert William Cotterell shows you what types of art supplies you'll need to get started, including various types of charcoal, compressed and pencil varieties, types of erasers that work best with charcoal, and the best types of paper for making charcoal drawings. He also shares tips for choosing a subject, understanding light, blending techniques, adding highlights, and using Fixatif to protect your w...

Few things are more important than being well-versed in data analytics and interpretation when it comes to succeeding in today's increasingly data-driven world. As a data scientist, these skills are the key to a high-paying career. For hackers, there's no better way to defeat the enemy than to become the enemy.

When Apple acquired the popular Workflow app in 2017, many were worried that it would either get replaced with something much worse, or just disappear entirely. Thankfully, Apple put these concerns to rest with the launch of Shortcuts. In iOS 13, Shortcuts is becoming more powerful than ever, providing functionality on the iPhone that the original Workflow team could only dream of.

You may not have thought of dorks as powerful, but with the right dorks, you can hack devices just by Googling the password to log in. Because Google is fantastic at indexing everything connected to the internet, it's possible to find files that are exposed accidentally and contain critical information for anyone to see.

Remember when typing without physical keys seemed ridiculous? Now, touch typing is the smartphone norm. That said, mistakes are inevitable on small screens. So before you start hammering on that delete key or shaking your iPhone like a madman, know that there's a better way to undo text you didn't mean to type — no shaking involved.

As a root user, you have a lot of responsibilities to make sure your phone stays secure. Expectedly, some things may slip through the cracks. Remembering to check which apps have been granted root access is extremely important. All it takes is one bad app, so it's good to learn how to avoid that at all cost.

It's been proven that hackers can manipulate your screen with fake taps through specific exploits, so they can potentially hit the "Grant" button when you get a superuser request. This is the last thing you'd want to happen since the malicious app from that point forward has full system privileges. Luckily, using a fingerprint to lock your superuser requests can prevent this.

While modern browsers are robust and provide a lot of functionality, they can be unlocked to do some pretty spectacular things with browser extensions. For hackers and OSINT researchers, these tools can be used to defeat online tracking, log in to SSH devices, and search the internet for clues during an investigation. These are a list of my top ten favorite browser extensions for hackers — and how to use them.

WhatsApp, the popular messaging app owned by Facebook, has several important privacy and security-related features, including end-to-end encryption, screen lock, read receipts, and two-step verification. If you're an avid WhatsApp user, you'll be happy to know there are more privacy features you might not know, such as hiding your profile photo from other users.

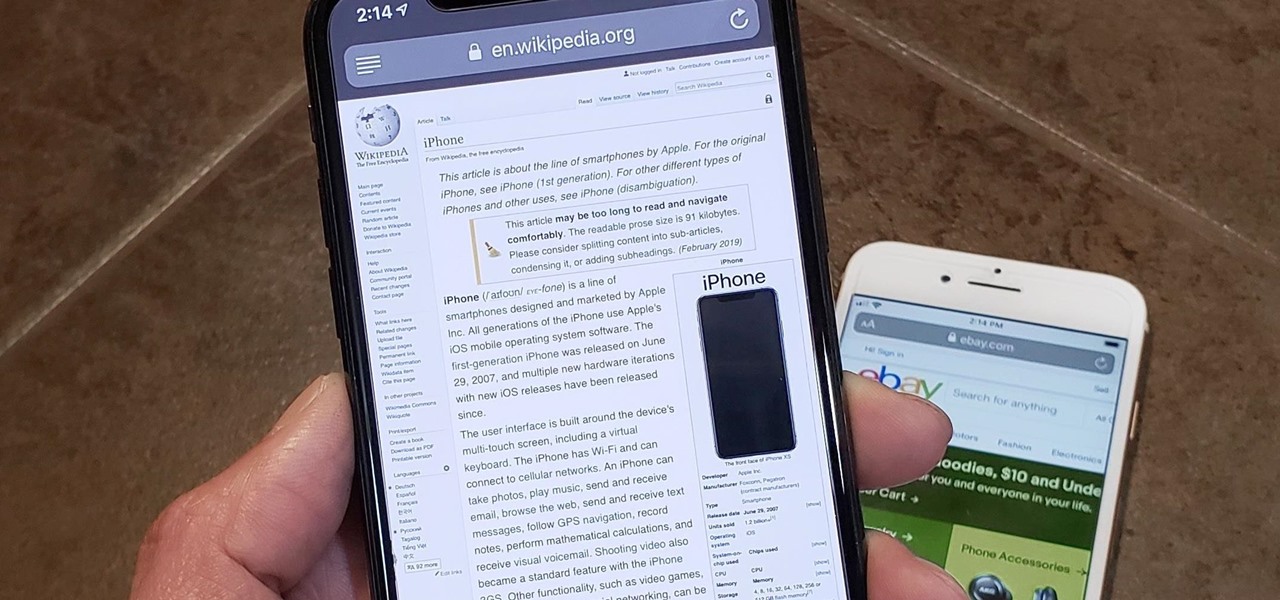
In Safari for iPhone, as far back as iOS 7, you can request the full desktop version of websites. The process was streamlined starting in iOS 9, but the process remains relatively hidden and easily missed. Now, iOS 13 shines a light on it, as well as adds functionality to set the desktop view for individual websites indefinitely.

Gathering information on an online target can be a time-consuming activity, especially if you only need specific pieces of information about a target with a lot of subdomains. We can use a web crawler designed for OSINT called Photon to do the heavy lifting, sifting through URLs on our behalf to retrieve information of value to a hacker.

Just like Instagram, Photoshop Express for Android and iOS has its own set of filters you can quickly apply to any photo. It's simple, fast, and more customizable than using Instagram's pre-made filters. The options in Photoshop Express allow you to edit and change your filters to be exactly to your liking. Then, you can even save those edits as your own custom filters.

Apple just released the sixth beta release for iOS 12.2 today, Monday, March 18. Just as expected, the update to the developer version dropped just past 1 p.m. EDT (10 a.m. PDT), and comes with new changes and features from iOS 12.2 beta 5 and beyond, including a new warranty status in the "About" page in Settings.

Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. To prove it, we'll show how to take a normal command shell and elevate it to a Meterpreter session.

In the world of technology, there's often a trade-off between convenience and security. The Java Remote Method Invocation is a system where that trade-off is all too real. The ability for a program written in Java to communicate with another program remotely can greatly extend the usability of an app, but it can also open up critical vulnerabilities that allow it to be compromised by an attacker.

The rumors are still hot that Apple might include an 18-watt USB Type-C power adapter with the upcoming iPhone lineup so that there's fast-charging capability right out of the box. Leaked photos have surfaced that substantiate this rumor, though, they could also be fake. But how would ditching the old-style 5-watt USB Type-A power cube affect you if it's true?

Voice-activated digital assistants from Amazon, Apple, and Google currently have the upper hand for home automation integrations, but a new augmented reality mobile app promises to give homeowners and renters visual control over their connected appliances.

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

Nearly one year after its announcement, AirPlay 2 has finally landed on iPhones everywhere. Not only can you easily control multiple speakers including Apple TVs and HomePods from your iPhone, but you can use Siri to help you get the job done. It's one of the iOS assistant's best features, and if you're running iOS 11.4 with a compatible speaker, you can try it out right now.

Many operators use elevators to control access to particular floors, whether it be the penthouse at a hotel or a server room in an office building. However, the law requires them all to have a fire service mode, which gives emergency access to restricted floors, and a hacker can use that to bypass security altogether.

For the longest time, the only clickable link you could throw up on Instagram was in your profile's bio, and that's still true for a lot of users. The only way to add a clickable link aside from the aforementioned one is in an Instagram story, where users checking out your story would swipe up to load the webpage before going back to finish your story.

If you installed Android 9.0 Pie, you might have enjoyed trying out some of the new features in the latest version of Google's OS. However, change isn't always a good thing, so you might be wishing you could downgrade back to Oreo right about now. Good news — you can.

Many Samsung fans were excited when the Galaxy S9 kept the 3.5 mm headphone jack. While this is a rare delight in 2018, you also have the option for high quality audio playback over Bluetooth. When used with compatible headphones, the S9's new Bluetooth audio codecs can greatly improve audio quality.

A relatively new feature in Snapchat, having been first introduced in February 2018, is GIF support. These new animated stickers, straight from a partnership with Giphy, came to the app about a month after Instagram received GIF capabilities. If you've used Instagram's version, adding GIFs to snaps is even more intuitive. While they were late to the game, they're doing it better.

Using just a small sticky note, we can trigger a chain of events that ultimately results in complete access to someone's entire digital and personal life.

Apple released the third developer beta for iOS 11.2.5 on Wednesday, Jan. 3, and public beta testers got in on the action the following day. The update comes two full weeks after the release of the second beta, marking an extended update period of Apple. The second beta mostly brought under the hood improvements to 11.2.5.

Proxies can be quicker to use than a VPN for specific applications, like web browsers or torrent clients. Both services will hide your true IP address, but a VPN is slowed down because it encrypts all data through a VPN network, while a proxy just acts as a middleman for fetching and returning requests from a server on your behalf. When speed is needed, go proxy.