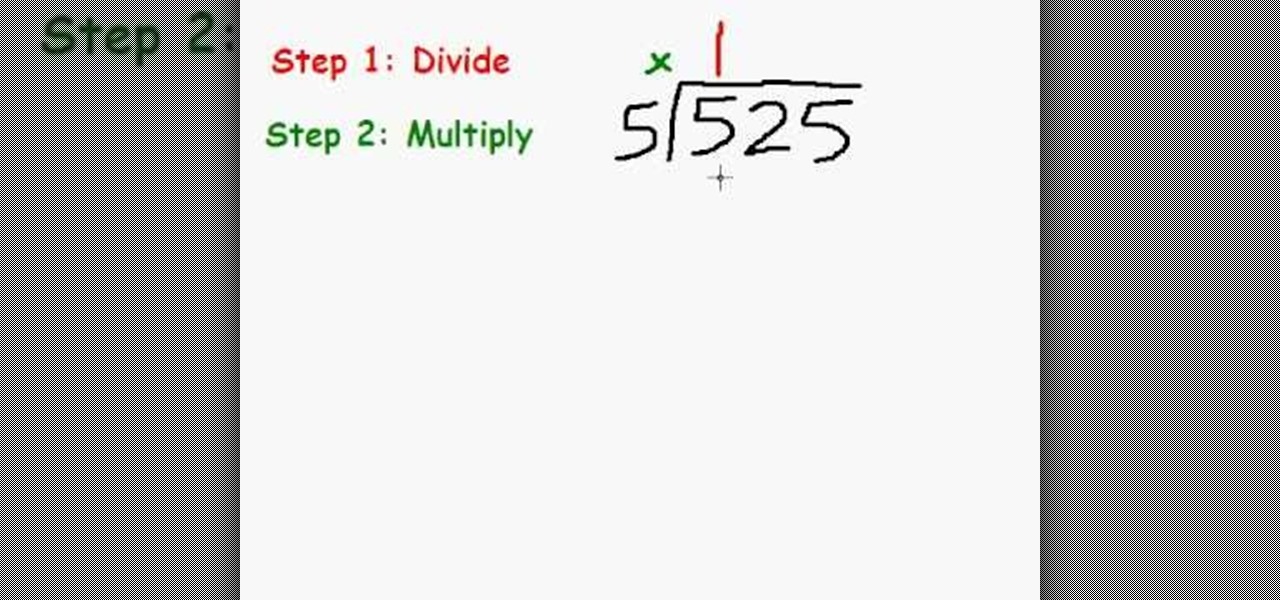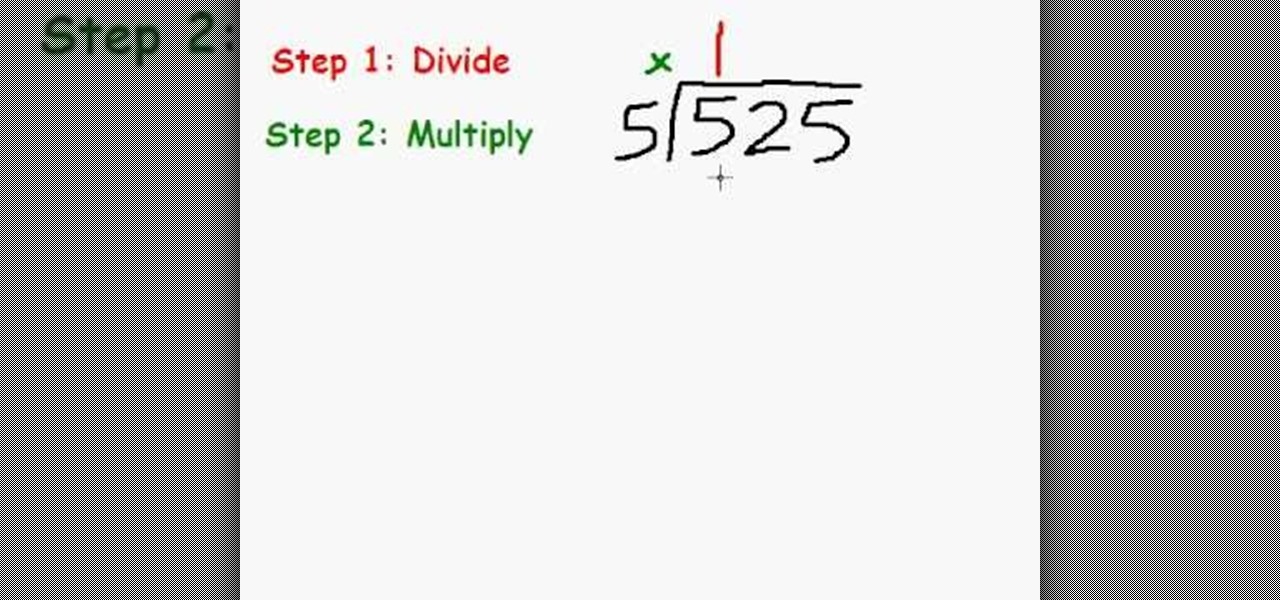
In this `Math Made Easy' tutorial the instructor shows how to perform Long Division. He gives a simple four step approach where in the first step he shows to divide the first left most number by the divisor and this gives the quotient. Now he shows to multiply the quotient with the divisor to get a value which is to be subtracted from the original divided number. Now in the third step he shows how to bring down the next digit and finally in the last step he asks to perform the same procedure ...
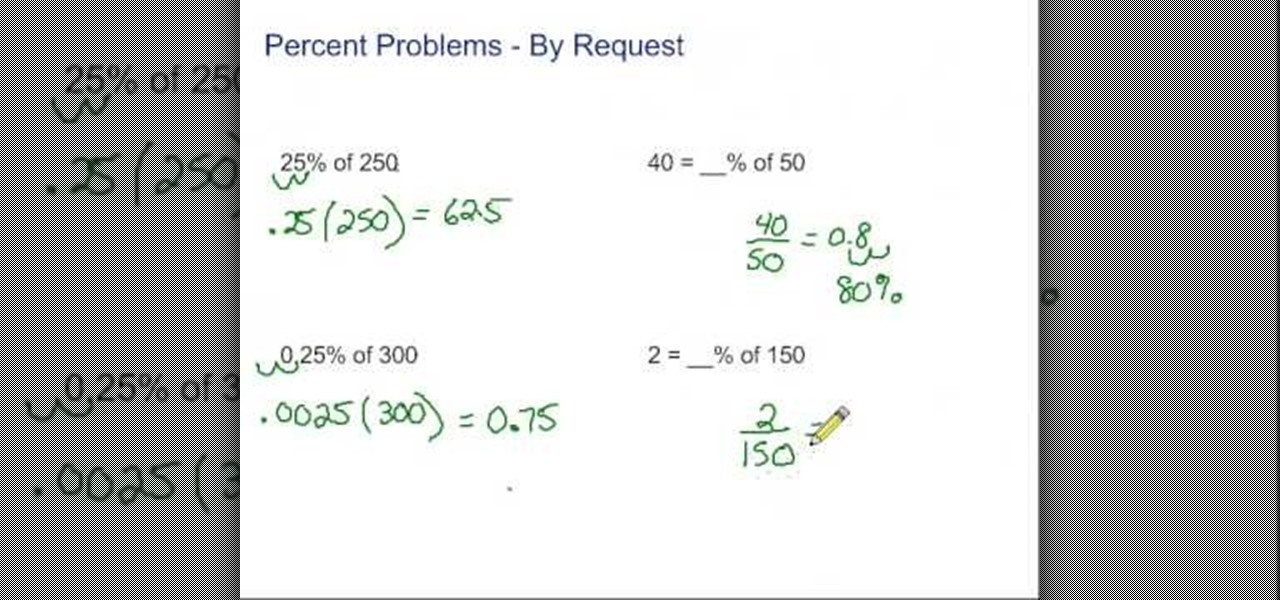
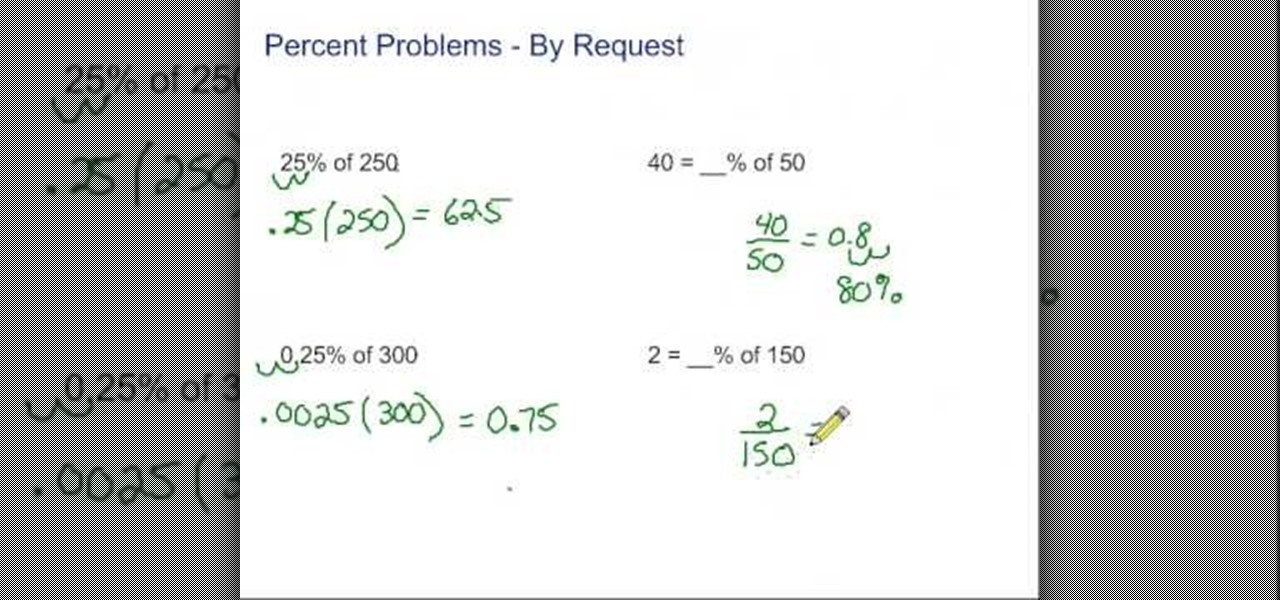
In this tutorial the author explains of how to find percentages using examples. He explains that x percent of some number y is x multiplied by y and divided by 100. He goes on and explains this concept with numerous examples. He suggests a short cut to movie the decimal point of a number two digits to the left to divide that number by 100. The author demonstrates many more similar tricks and short cuts using which one can easily solve percentage problems. So if you are looking for a good tuto...
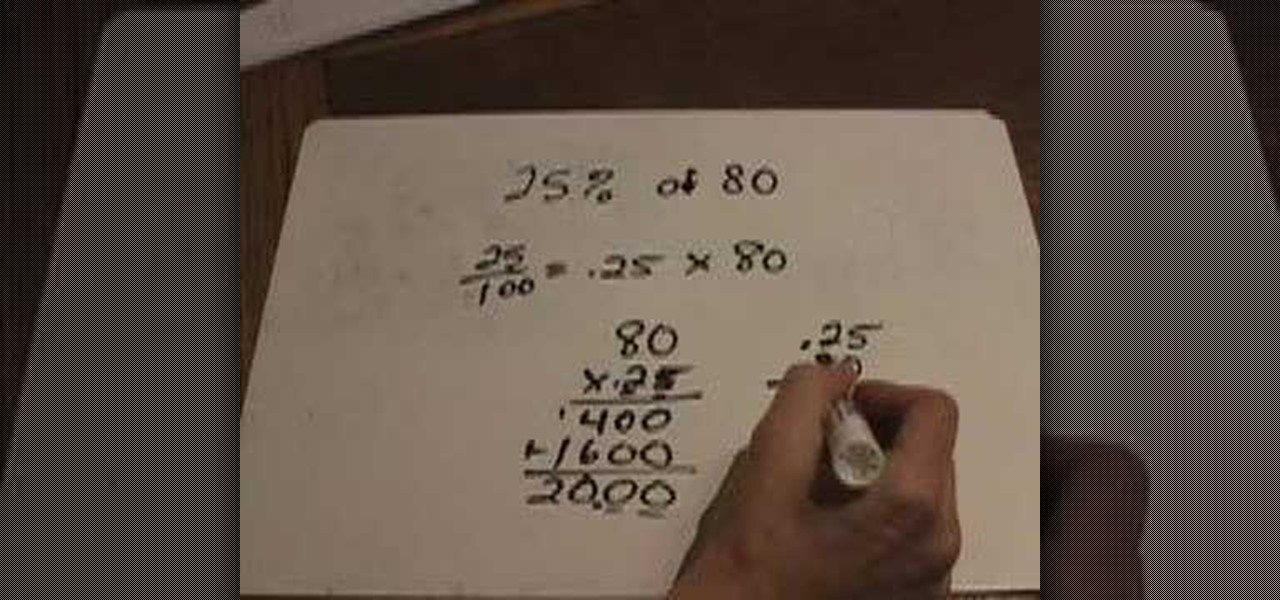
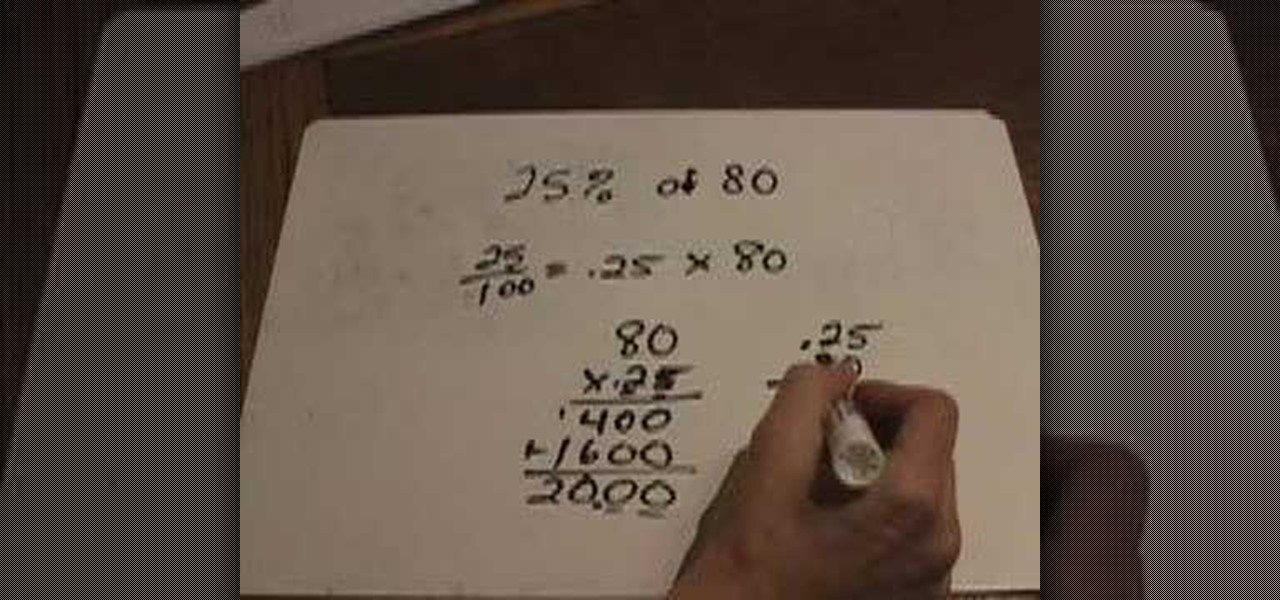
In this tutorial the author explains of how to compute percentages of a given number. He explains that x percent of some number y is x multiplied by y and divided by 100. He says that of means multiply and percentage means for hundred. He goes on and explains this concept with numerous examples. He suggests a small trick to move the decimal point of a number two digits to the left to get it divided by hundred. The author demonstrates many more similar tricks and short cuts using which one can...
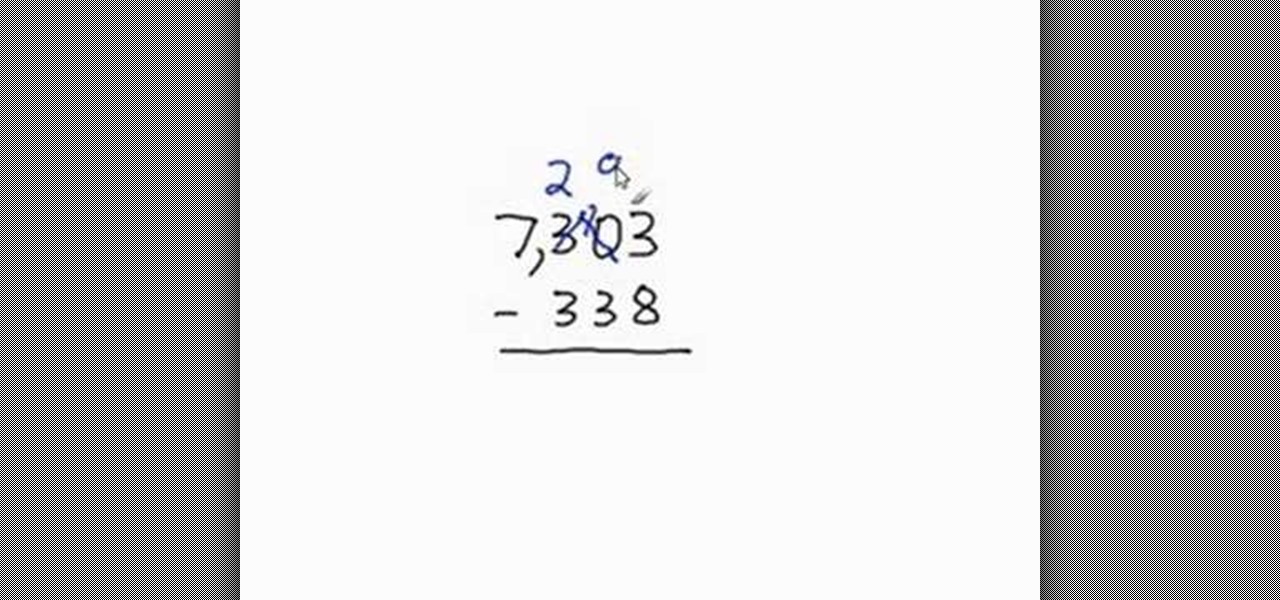
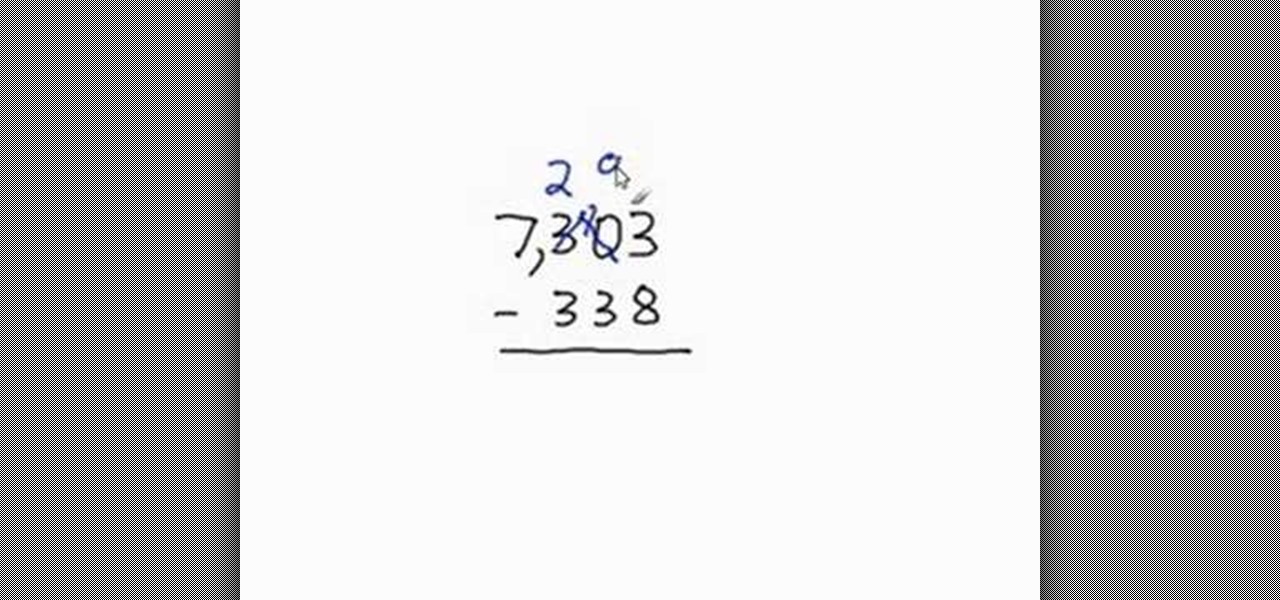
For people who are learning basic math skills, this video will show you how to subtract larger numbers which involve borrowing. If the top number on your rightmost digit is smaller than the number before it, you will need to borrow from the column before it. To do this, you will have to cross out the left hand number, subtracting one from its value. You can then add 10 to your original number and continue with your subtraction. If the left hand number is 0 and too small to be borrow from, you...

Addition got you down? An expert instructor from Khan Academy walks you through the mysteries of adding two numbers together by breaking it down into easy to understand terms. Fun animated chalkboard examples make it easy for kids and adults alike to learn how to add. Also demonstrates how to add using the number line. Introduces the concept of numbers less than zero. Includes addition of both large and small numbers, and how to carry over the numbers on more complex problems.
Check out this video tutorial on how to Solve a ten digit number math problem. This video will show you the key to solving the puzzle to find a 10 digit number, such that 10 digits are divisible by 10, and the first 9 are divisible by 9, and so on.

This dark use of purples and blacks equate to a heavy goth look. Learn how by watching this video. ****PRODUCTS USED****

Let's say you're using your iPhone's Calculator app, and you're knee-deep into a complicated calculation with many steps. You type in a large number, for example, "123,466,789," but mess up. You meant to type "5" midway through but accidentally typed "6" instead. The only thing to do now is start over, no matter how far along you are, right? Wrong.

For lack of a better word, a missing iPhone sucks. Not only do you lose a physical device that cost you a small fortune, but there's also the probability you'll never see your precious data again. Hackers and thieves might, just not you. To keep this from ever happening, there are preventative measures you should take, and the sooner you do them the better.

In response to the success of Apple Pay and an attempt to stave off the appealing Samsung Pay service, Google is completely revamping Android's mobile payments system. Instead of just using Google Wallet as an app to make payments with your phone, a new service called Android Pay, with an extensive underlying framework and API, will soon make its debut—and maybe even sooner than you'd think.

Hi there, Crackers, Welcome to my 7th post (Part-1), this tutorial will explain about the basics of Batch Scripting.

Skype is a great way to stay in contact with friends and family over the internet, and people tend to share a lot in their chats, so why not try and find a way to hack it! Once a Skype account is hacked, you can view all conversations within the last three months, see how long each video call was, and even access files that were shared through chat.

There isn't as much use for old-school four-function calculators anymore since we all have them on our cell phones now. If you've still got one lying around, you can hack it to play recorded sounds, use it to make a metal detector, or turn it into a custom name plate that says anything you want...

Chromecasts can make for some fun nights. Whether you're setting up a collaborative YouTube watch list, letting everyone add to a giant party playlist, or playing games like Cardcast and Big Web Quiz, Google's streaming media stick is a hit by all accounts.

With so many cloud storage services out there, many people are starting to keep their important documents online, especially when they know they'll need to view them when they're away from their computer.

In this video we will learn about algebra SCIENTIFIC NOTATION and STANDARD FORM. Watch the above math video to learn how to change large numbers from standard form to scientific notation.

If you're ever faced with a situation of handing over your iPhone to law enforcement (or getting it taken forcibly), whether by the police, feds, or court system, there are things you can do to prevent them from getting access to all that potentially self-incriminating data. And it takes less than a second.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

Welcome back, my hacker novitiates! A short while ago, I introduced you to regular expressions. Regular expressions are a language that is particularly useful for finding complex text patterns in streams of data.

This video tutorial is for beginner puzzlers who are getting more advanced in their speedsolving of the Rubik's Cube. This 2-Look Method is exactly like taking 57 OLL algorithms and slimming them down to the single digits. First you orient the edges of the Rubiks Cube (or the cross if you prefer), then the corners, hence the name "2-Look OLL".

This is a Computers & Programming video tutorial where you will learn how to change your NAT to OPEN with a Linksys router. Go to your browser and type in 192. 168. 1. 1 and that will take you to the basic set up. The authentication dialog box comes up. Type in ‘admin’ for the username as well as the password. These are default settings. In the Linksys page, go to ‘applications and gaming’ and on the Port Range page fed in these information. Your application you can name anything. Start 80, E...

Have some time to kill between classes? Entertain your friends, or make new ones with this number prediction trick. Just make sure you have a calculator on hand and you’re ready to bring joy and amazement to the table.

This is easier than the divisibility by 3 rule, but still necessary for those starting out with simple division in math class. You can use the divisibility rule to see if a number is divisible by 2, 5 or 10. This video will show you how simple it is!

It’s a game, it involves numbers, it’s fun, it’s KenKen! Understanding the goals and rules of this fun, numbers puzzle will give you the skills you need to win. Have fun working your brain and passing the time with KenKen.

You may not know it, but the IPv4 address of your computer contains tons of useful information about whatever Wi-Fi network you're on. By knowing what your IPv4 address and subnet mask are telling you, you can easily scan the whole network range, locate the router, and discover other devices on the same network.

Back in 2010, iOS developer Daniel Amitay developed a camera security app for iPhones that used an unlock screen almost identical to that of the iPhone.

Here the New Boston shows you some tips about using the Spry Validation Text Field. To begin you will go to the Spry Validation Text Field, on Dreamweaver CS4. Looking at the bottom of the page notice the various options that are available for Properties. You find drop-down boxes for Type, Pattern, Minimum or Maximum values, Required, Enforce pattern, Format, Validate on, Blur or Change and Preview States. You can see the types of text available for validating by left mouse clicking the Type ...

Brian Brushwood teaches you how to do the hot seat card trick. You need a regular deck of cards and the 10th card from the top should be the 3 of spades. The spectator chooses a number between 10 and 20. He takes the cards and deals down that amount of cards from the top. Next, add those two digits and deal that amount of cards. There's a piece of paper in plain view the whole time with the card prediction. Write the 3 of spades on the piece of paper using a regular pen. On top of it write 8 ...

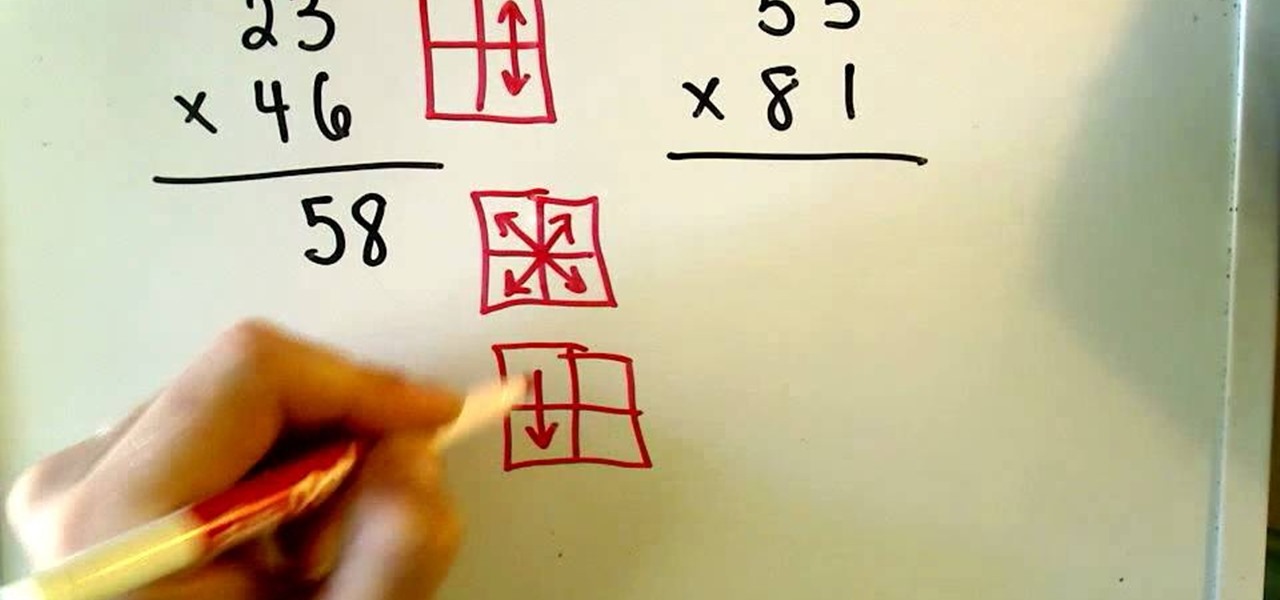
This how-to video is about multiplying numbers in a very quick and in a new manner. Multiplication of two - 2 digit number is explained in this video, To do this multiplication we need to follow three steps, let's follow this method with an example, let's say that we want to multiply 23 with 46, let's write the numbers like this, 23*46 (multiplying 23 with 46), the answer is 1058.

All you need to remotely access your computer's iTunes library is your iPhone. Control itunes with your iPhone with this Howcast guide.

All you need to remotely access your AppleTV library is your iPhone. Learn how to control Apple TV with your iPhone with this Howcast guide.

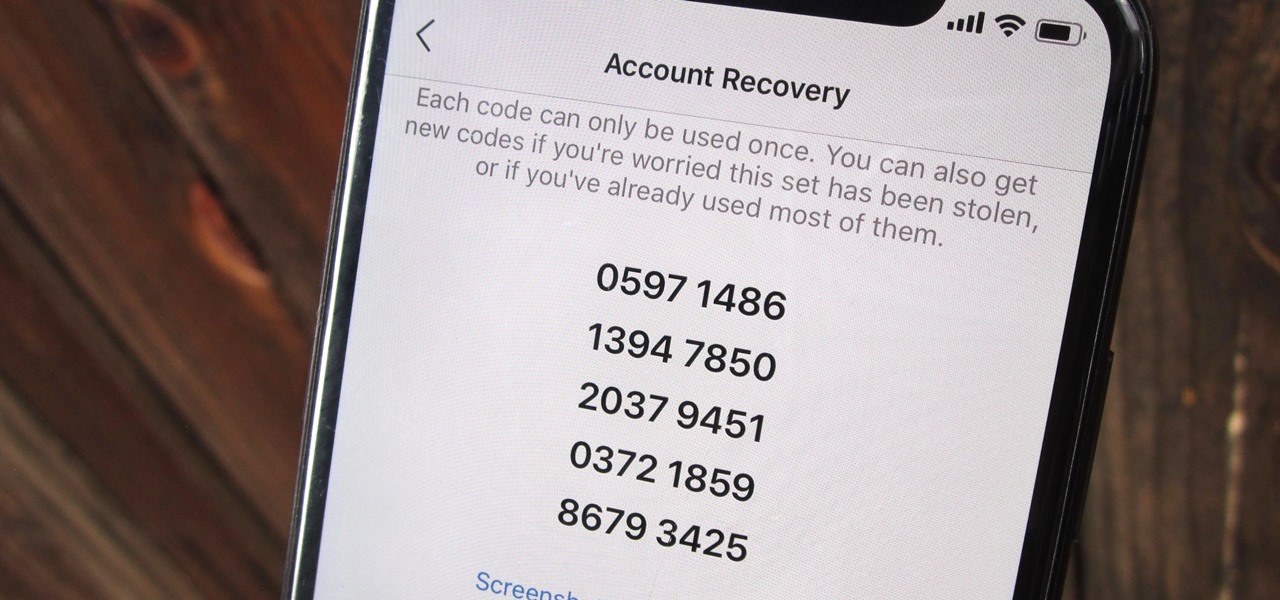
Two-factor authentication (also known as 2FA) adds a necessary additional layer of security to your username and password in many important apps. On Instagram, 2FA requires you to confirm it's you attempting to log in, with a special code sent to you via text message. Enter the code and you're in ... but what happens when you need to log in and don't have access to your phone?

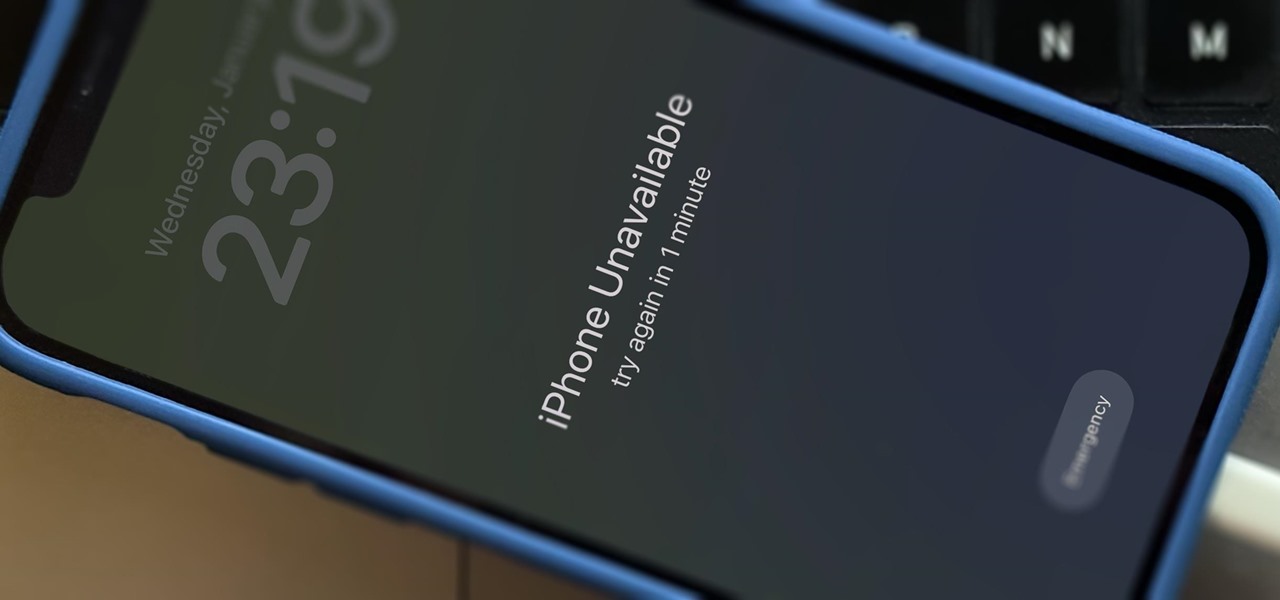
If you've had the pleasure of owning both an iOS and Android device, you may have noticed one subtle difference on each one's PIN unlock screen. Android's lock screen requires you to press "OK" after entering the PIN, whereas iOS's simply unlocks the screen right after the last digit.

There's only one thing keeping hackers, thieves, law enforcement agencies, and maybe even the people you thought you could trust from breaking into your iPhone should they ever get possession of the device. Their odds of bypassing that thing are pretty good, but there's an easy way to make it an almost impossible feat.

Mother Nature's creativity is infinite, especially when it comes to fruit. We've got black sapote, which tastes like chocolate pudding, and Buddha's hand citron, which looks like Freddy Kreuger's digits merged with a lemon. How could she possibly top herself?

With countless images and messages packed into one small device, security is always a high priority amongst iPhone users. For this reason, we've previously shown you how to make your iPhone's passcode match the current time, which made figuring out your passcode a lot more difficult for wandering eyes.

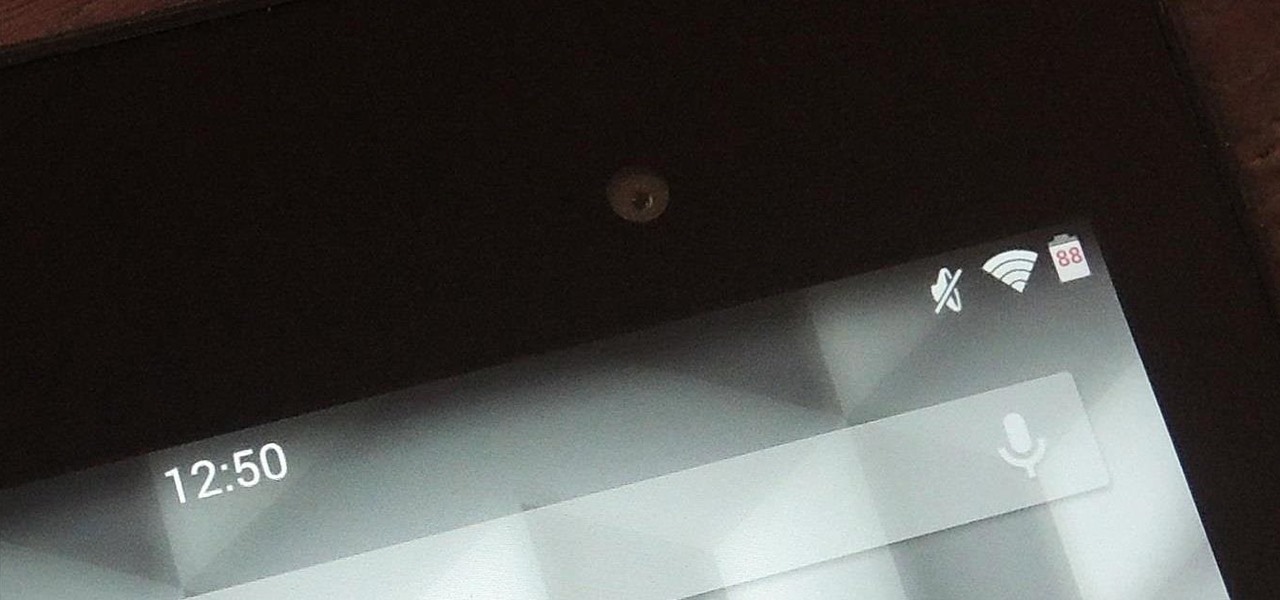
We may all have a Nexus 7 tablet, but we don't all want to have the exact same look and feel, which is why we softMod for a more personalized vibe. There are hundreds of cool mods you can perform on your Nexus 7, whether stock or rooted, but one of my favorites in Android 4.4 KitKat was unlocking the hidden battery percentage icon in the Status bar.

Just days after news spread that Snapchat could be exploited by spammers, an anonymous group of hackers have released the private information of over 4 million users of the popular photo-sharing application.

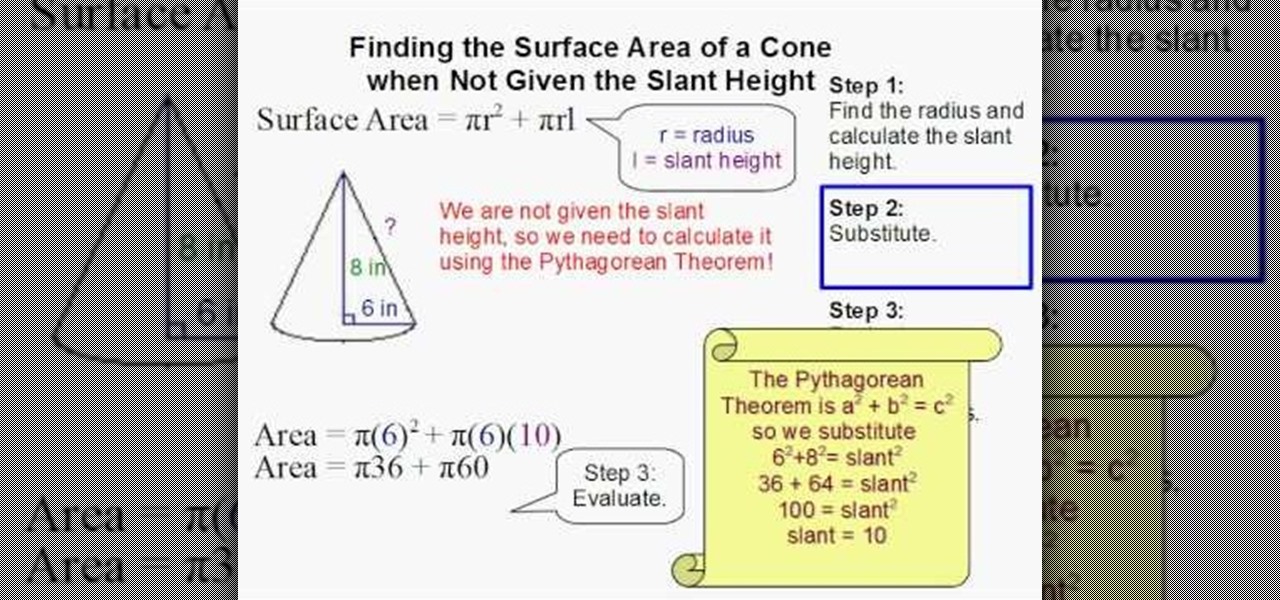
Math always seems hardest until someone shows you how to do the problem and then it all seems just so simple. This video will walk you through the process of finding the surface area of a cone when you also have to derive the slant height. Use this example to help with your other cone problems.

When you don't want somebody you're calling to know the real phone number associated with your iPhone, whether it's for privacy reasons, to avoid being called back, or to prevent being ignored, there are multiple things you can do to block it on their caller ID.