Jordy with AT&T teaches us how to block your cell phone number when making outgoing calls. By doing this, any person you call cannot read your ten digit cell phone number. It's as simple as entering a code before you dial the desired number. The code is *67 followed by the ten digit number and then placing it as a regular call. This does not allow the person you are calling to see your number. Instead it will show up on their caller ID and read as "Private Caller". Follow Jordy's advice and k...

My kids found an old Spoke-Hedz three digit lock, and wanted my help to crack it open. One of the first things I noticed was that it doesn't function like a normal code lock, where one half of the lock will open, or the lock itself separates. In this lock, the locking bail extends through the lock mechanism, and the lock mechanism itself slides back and forth across the bail.

Since today (11/11/11) is the last 6 digit binary date this century, I thought we should look at some kinetic binary calculators.

The point? I'm not quite sure, I'll admit. But nonetheless, this paper-made iPhone TV set by Trickartt is pretty awesome. Don't miss the video demonstration on Flickr.

Slippery surface plus knife equals danger. No lost digits: It’s one of the cardinal rules of kitchen safety. So keep your cutting board stable. Stabilize a slippery cutting board.

Tommy and Al talk workshop safety and make a table saw push stick to ensure all your digits stay intact. Woohoo!

This cool trick involves a little math, but you won't believe the results! Sometimes we use materials that require adult supervision... like scissors, so make sure you have friends and family around whenever you do magic tricks. You will need

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

Today isn't actually Pi Day, but I was unable to get this article out in time. Pi Day was actually yesterday, March 14th (3.14), so let's call this a post-Pi Day treat!

Have you ever wondered how credit card numbers work? I mean, how they really work? How do they come up with the numbers? Credit cards actually follow a very specific pattern. Let's take a look at how they're set up.

Gone are the days when you had to carry a clunky DynaTAC to make phone calls, pocket phone book for you contact list, Sony Discman for your tunes, and wallet for you cash and credit cards. Today, all you need is your smartphone. To be specific, Google's Nexus S 4G on Sprint.

This kid has an amazing sense of humor and big balls. It takes both to go on national television and breakdance on a gigantic prosthetic erection.

What do you do in those cold weather months, when your hands are warmly gloved and you can't bear exposing your poor fingers to the harsh elements? Apple didn't think of this problem when finessing their iPhone touchscreen, but not to worry, South Korea has the answer to this pesky problem.

Whether it's your credit card, your parents' new zip code, or a new work phone number, number sequences are everywhere. Sometimes it's important to actually remember them instead of always relying on a smartphone or the internet to remind you.
What Is a Rational Number? A rational number is a number that can be written as a ratio and a/b.

Hell, yeah! Play with your food. This android hand is the brainchild of a collaboration including Robo250, the Robotics Institute at Carnegie Mellon University, the Mattress Factory and MAYA Design, Inc.

Got a knack for speeding? Like running red lights? Believe or not, the police have better things to be doing than pulling you over, like catching real criminals. That's why more and more cameras are popping up at known speeding zones and on street corners—so the cops can clean up the streets, compared to just ticketing them.

Think credit card numbers are just a meaningless jumble of digits? A sort of number soup? Think again! Your credit card number isn't even number at all but rather a composite of four separate numbers, each of which plays an important, fixed role.

How did it happen? How did your ultra-secure WPA password on your wireless network get broken into? Well, you might have just found yourself at the mercy of a cracker.

Want to stick it to your mobile carrier by porting your cell number to Google Voice? Now you can! On Wednesday, January 19th, Google Voice began allowing select users to transfer their personal numbers to Google Voice for a one-time fee of $20. Though the feature is still in limited release, Google has stated that they intend to make the feature available to all Google Voice users "in the near future." Terrific, right? Not entirely!

Although there are many great camera apps with filters for the iPhone, Android users should not feel left out. Apps such as Vignette and Retro Camera offer an exciting array of filters to complement any photograph. I've tested out different filters from both apps, and uploaded the samples below.

How did we get to the age of smartphones, ereaders, laptops, and crazy touchscreen displays? Gizmodo covers Steve Wozniak's recent presentation of nine key gadgets that have deeply influenced the tech God's work. A few highlights below; click through for the full survey.

This is the first of two Video's introducing you to your fingers from a Hand Analysis perspective. The Fingers mainly govern the mind and thinking. Somewhere in the vast fabric of time somebody discovered that the length and inclination of each particular finger can bring out certain personality traits. I still find it amazing and satisfying to see somebody with a longer than average 'little finger'(Mercury-communication), that sticks out that can't stop talking and buzzing around all excited...

Attention all iPhone users. Engadget posts a helpful tip on possibly avoiding that painfully long iPhone 4 upgrade wait:

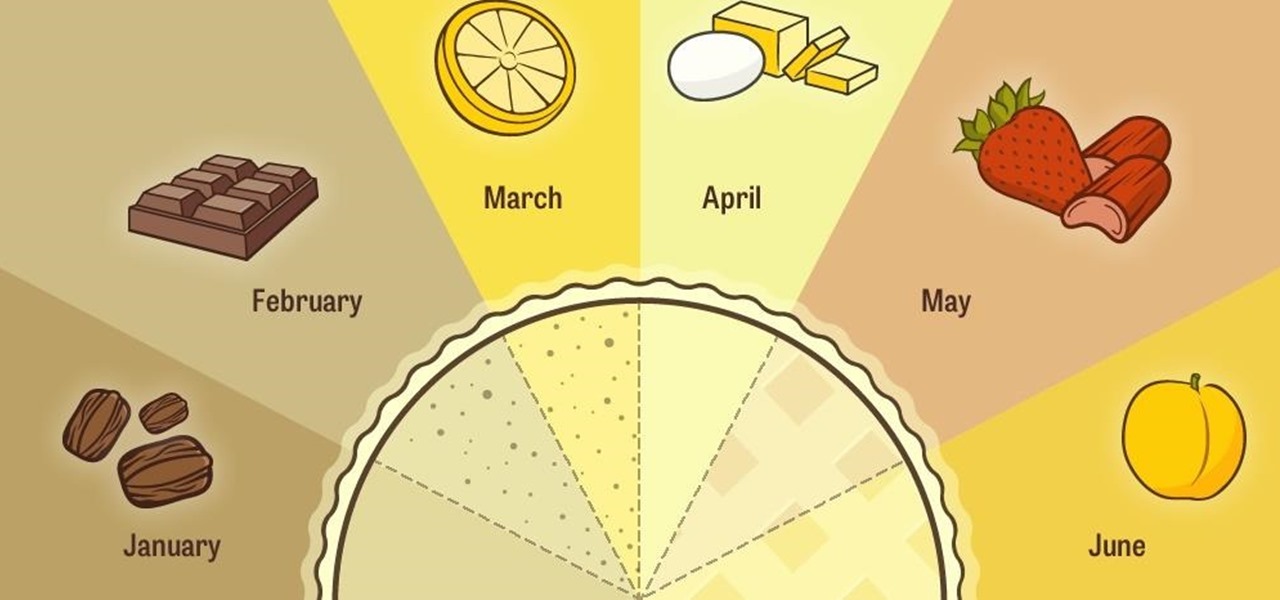
Pie and pi lovers rejoice: whether you like eating pies or calculating their area, 3/14 is your day. March 14 is a holiday for both bakers and math nerds: Pi Day, where the day and month correspond to the first three digits of the most famous mathematical constant.

Security researcher Ravi Borgaonkar from Berlin has discovered that hackers can hide an 11-digit code in a webpage that can wipe out all of the information on your smartphone—contacts, photographs, music, applications, and anything else of importance. The attack takes no more than a few seconds and nothing can be done about it. NOTHING. This begs the question—are you susceptible?

Been hacked once? Twice? Maybe more? You thought abc123 was the only password that is both 6 characters wide and easy to remember? I have some suggestions in store for you. Just read on...

Hello and welcome to another InfoSecurity World tutorial. The intent of this article is to teach one how to encrypt sensitive files. When set up correctly with a strong password, it would be almost impossible to hack. Even the FBI have had issues decrypting this software. I'm here to teach you how to create a general encrypted container—not the complex hidden TrueCrypt volume.

In this article, I'll show you how to send SMS messages with Python. You'll need Python 2.7 or later, urllib and urllib2. The code basically uses an online text messaging service to "POST" html data, as if a person was entering the data themselves. The uses for something like this are unlimited. For example, I modified the basic code so I would receive a text message letting me know every time someone rang my doorbell. The program could interface with Arduino through a serial port, and send d...

We love you. Yes, you, esteemed reader. Your attention is what keeps Indie Games Ichiban World going, and we'd like to thank you for that, every single week. How? With $10!

Lifehacker posts an article on the art of cracking weak passwords, courtesy of Internet standards expert, CEO of web company iFusion Labs, and blogger John Pozadzides. Pozadzides certainly knows a thing or two about password logic. (Note: this information is not intended to hack into accounts, but rather to protect you from using weak passwords).

Guitar Essentials My friends and I would secretly scribble tab in the darkly lit practice rooms in our university even though we were educated musicians. So, being able to read tablature, or tab, is essential for beginning guitarists.

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

Last time, we looked at archaic cryptography, so you should have a basic understanding of some of the concepts and terminology you'll need. Now, we'll discuss one of the most important advances in computer security in the 20th century—public key cryptography.

As per Alex's request, I am posting about generating word-lists in Python. However, this is my FIRST attempt with Python, so please provide me with critiques and any and all comments. I really want to know what you think as there was a little bump here and there seeing as I am transitioning from C#.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

It's called a Quick Response code, but most know it simply as QR code, a matrix barcode dedicated to the world of smartphones. The information contained within the square black modules could be text, a URL, vCard, or some other kind of data. And even though mobile tagging has been around for eight years, it's just now spreading like wildfire across the globe, being incorporated into artistic portraits and wall art. And most recently... "social clothing".

Dactyloscopy isn’t going anywhere. Forensic science has much relied on fingerprinting as a means of identification, largely because of the massive amount of fingerprints stored in the FBI’s biometric database (IAFIS), which houses over 150,000 million prints. And thanks to the departure of messy ink-stained fingertips, biometric analysis isn’t just for solving crimes anymore.

Guitar Essentials My friends and I would secretly scribble tab in the darkly lit practice rooms in our university even though we were educated musicians. So, being able to read tablature, or tab, is essential for beginning guitarists.