Want to disguise your URLs so that they appear suspicious? In the style of websites such as Tiny URL that take your original URL and give you a shortened one to post on your blog or twitter feed, Shady URL takes your original URL and gives you one that might convince people not to click it. Go to Shady URL and paste the URL you wish to disguise. Click submit, and on the next page it will give you a URL that looks, well, shady. It might include something about a mail order bride or an investme...

Vanessa from Tekzilla Daily gives us a very helpful video guide on how to edit or tweak icons in the system tray on Windows 7. Typing "notification area" in the search box of the Start Menu calls up the Notification Area control panel. This control panel shows the different processes and programs that are on the system tray. It is where you can edit the settings for each process or icon, with options of "always appear, never appear or show up only when needed". You can also control the basic ...

This exercise tutorial is the very definition of the statement, "no pain, no gain." Along with completing challenging cardio and strength training routines like jumping jacks and push-ups, you absolutely MUST moniter your diet in order to see fat burning results. Here are a few food habits you need to keep in mind:
If you've ever had a little trouble trying to program your calculator, you may find a little relief with this four-part video tutorial. Here, a Texas Instruments (TI-84 Plus) calculator will be used to explain the programming process. The four parts include:

The newly enhanced focus from Magic Leap on enterprise, announced on Tuesday, also came with a few companies opting to weigh in with their experiences developing for the platform.

Suddenly, Magic Leap's lawsuit against Nreal, as well as its barrier to entry in the Chinese market, appears to be as insurmountable as The Great Wall itself.

Ingress, the godfather of location based-AR games developed by Pokémon GO creator Niantic Labs, is getting a new lease on life via Ingress Prime, a reboot of the game built on the Niantic Real World Platform.

A massive leak appeared the web today, and it's got some huge security implications for every iPhone on the market. On the plus side, it also has some potential for enabling deep-level modifications and jailbreak tweaks.

Before The New York Times brought augmented reality to its iPhone app, the only way Winter Olympics fans could get this close a view to the world's best athletes would be to acquire a press pass.

Apple just pushed out iOS 11.2.5 beta 7 today for iPad, iPhone, and iPod touch to both developers and public beta testers. On Wednesday, Jan. 17, beta 6 was released, and there were two betas the previous week. With Apple promising a patch for "ChaiOS" next week for everyone, it's like iOS 11.2.5 will be that update.

With a new installment of the Saw horror series opening in theaters nationwide this weekend, Lionsgate is betting its ad dollars on immersive advertising to sell tickets.

Included among the many new features in Android L is the new "Heads Up" notification system, showing notifications as interactive floating windows anywhere on your device. Floating windows are nothing new, though, as we've already showed you how to get floating widgets, floating application shortcuts, and even floating notifications.

This guide will cover the SQL Insert statement and how to use it when programming in Delphi.

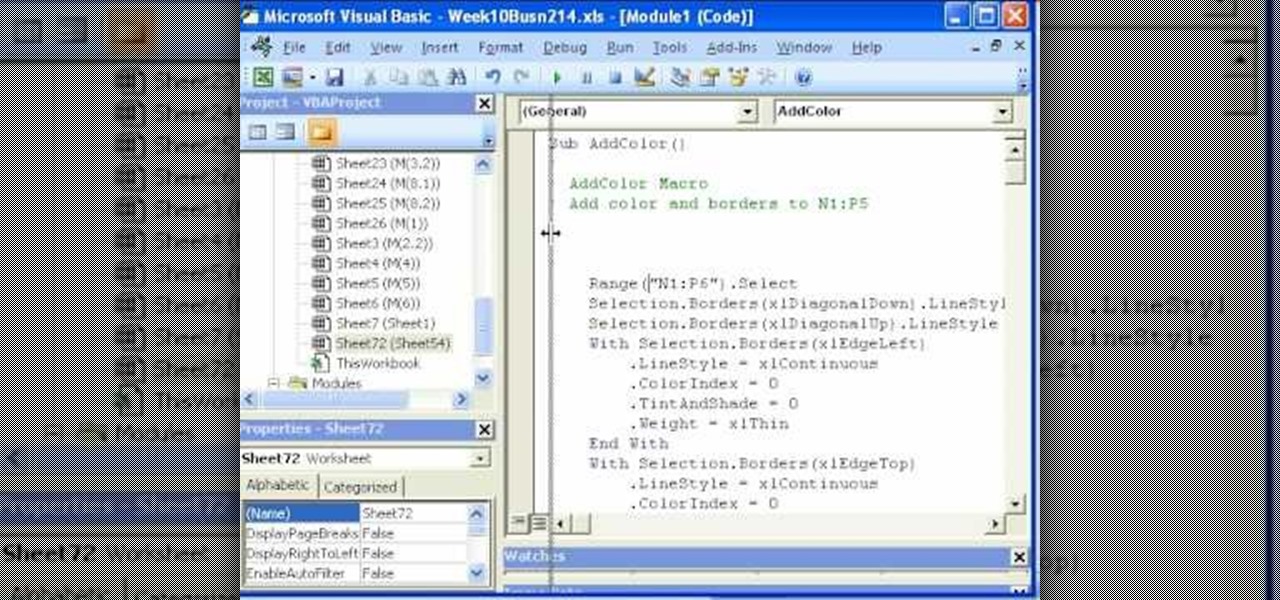
Whether you're interested in learning Microsoft Excel from the bottom up or just looking to pick up a few tips and tricks, you've come to the right place. In this tutorial from everyone's favorite digital spreadsheet guru, ExcelIsFun, the 52nd installment in his "Highline Excel Class" series of free video Excel lessons, you'll learn how to record and use macros in Microsoft Excel 2007.

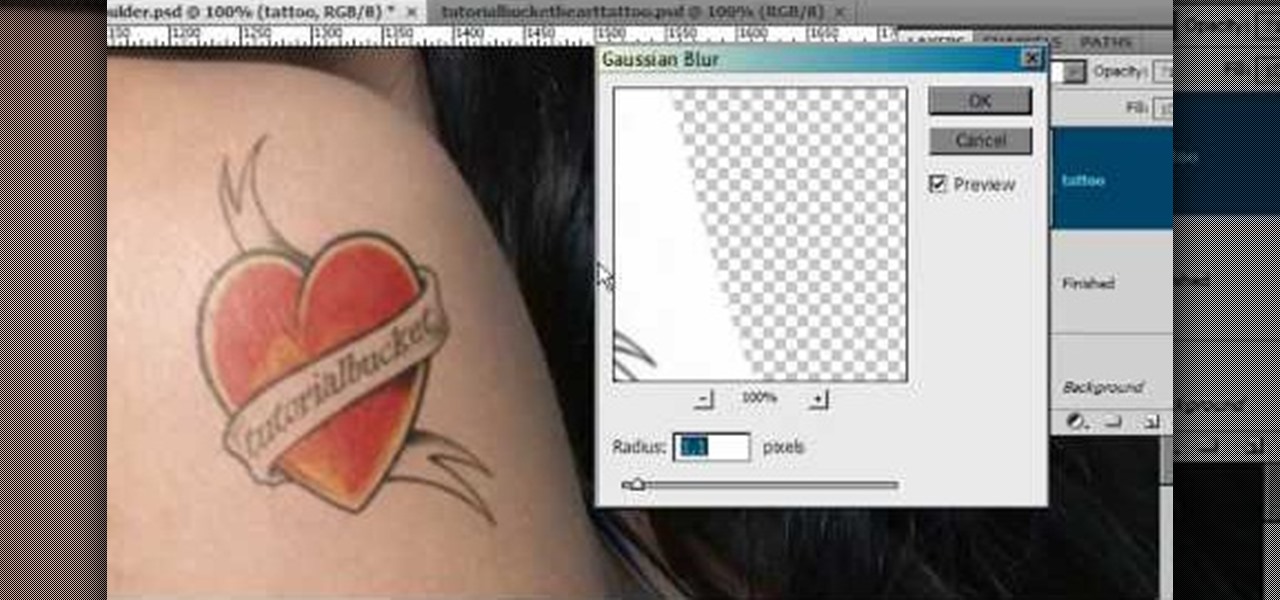
Open another canvas. It doesn't matter what size you make it, as long as it is the same size or bigger than the area you want it to cover on the image. Open a new canvas by going to "File" and clicking "New." Select your dimensions and click "Okay."

ThreadBanger pays homage to the movie "Fame" by showing us how to make the perfect "80's-tastic" duffel bag out of old umbrellas. With this thrifty idea, you will need a few umbrellas (broken is fine), scissors, a square pattern, a sewing machine, a zipper, and anything handy that will work as a strap. Use your new custom duffel bag to carry all your leotards or dance shoes in, or make a statement on your way to the video store to rent "FAME!"

This is a fun little Facebook hack you can use to make floating circles appear on your profile page. Make sure that you don't do this in a text box - just click anywhere on the page and then enter the secret code!

Has it been awhile since you've notice a new voice mail appear in your iPhone inbox? You may need to reset your network settings to ensure that your voicemail appears properly. Follow these steps to fix your missing voicemails on your iPhone.

Learn how to do a magic trick! Yes, learn some magic you can do with all that useless junk lying around your house. This young girl will show you in this video tutorial, how to perform the quarter appearing through a dollar magic trick. It isn't just an illusion, it's deception, it's sleight of hand, it's confidence. Grab your props and learn how to make a quarter appear from a dollar bill... see the reveal.

This video showcases the skills of the demonstrator in cutting a pineapple in an artistic manner. He begins by removing transverse sections, one each from top and bottom with a sharp knife. He then cuts off the remaining skin vertically in eight thin sections to keep wastage to a minimum. He marks off oblique lines one above the other all along the periphery. He cuts off very thin and small oblique slices along the marked lines, rotating the pineapple slowly. The resulting shape is now like a...

In this video tutorial, viewers learn how to reset a frozen iPod Touch after jailbreaking. iPod Touch is a portable media player, personal digital assistant, and Wi-Fi mobile platform. Begin by holding in the Sleep and Home button at the same time. Hold it until a black screen appears. After it appears, let go of the buttons immediately. Now connect you iPod Touch to your computer. Then open i-Tunes and Restore the iPod Touch. Now users are able to try to jailbreak their iPod Touch once again...

In this video tutorial, viewers learn how to turn on and off an iPod Touch. This is very simple, easy and fast to do. It is very basic and essential for those who have an iPod Touch. To turn on the iPod Touch, press and hold the power button until the Apple logo appears. To turn the iPod Touch off, press and hold the power button until the red slider appears. Then slide the slider. This video will benefit those viewers who have just recently purchased an iPod Touch and would like to learn how...

Photoshop is a place where we can edit the image in different styles. One of the features is adjustment layer of a photo that is also called as filter correction. It is an easy step to color filtering of a photo. Open a picture in a Photoshop, and select add layer option that present at the right bottom of the screen, then a pop up menu appears. Select filters from the options available, then dialogue box appears consisting of sub options filters and colors. then select the main color from fi...

While consumer-grade smartglasses are the holy grail for tech companies, smartglasses maker Vuzix knows where its bread is buttered, and that's in the enterprise segment.

Is the augmented reality magic fading down in Plantation, Florida? That's the first question some may be asking following a casual revelation over the weekend that Magic Leap, the maker of the Magic Leap One, has assigned much of its patent portfolio over to JP Morgan Chase as collateral.

Having already solved for functionality and form factor, Nreal appears poised to pull ahead of its consumer smartglasses competition as the third piece of the puzzle now falls into place.

Augmented reality and computer vision company Blippar has a new lease on life, as previous investor Candy Ventures has completed a successful bid to acquire the assets of the beleaguered company.

One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a lesson, we'll be exploiting a simple SQL injection flaw to execute commands and ultimately get a reverse shell on the server.

The road to becoming a skilled white hat is paved with many milestones, one of those being learning how to perform a simple Nmap scan. A little further down that road lies more advanced scanning, along with utilizing a powerful feature of Nmap called the Nmap Scripting Engine. Even further down the road is learning how to modify and write scripts for NSE, which is what we'll be doing today.

If competition in the augmented reality space was a spectator sport, then ARKit, ARCore, and HoloLens dominate the prime-time broadcasts on ESPN.

Hello Guys, Today I have made a script for ddosing sites with VBScript! And I don't know how you guys do it, but I've made a script that refreshes the page in a chosen amout of milliseconds. And if you want it a number of times or if you want it to go on and on. And this is a script to run it on your botnet. But again I don't know if this works on your botnet too.

Welcome back! Sorry for being so quiet, I've been rather busy with this project lately! Anyways, in the last iteration of how to train your python, we covered lists. Today we'll be introducing iteration and the two loops python has to offer, for and while. Also, we'll be covering a couple general use functions. So, let's get started!

Hello fellow training hackers. I do not know if many of you are familiar with ruby, but since it is a useful scripting language, that hasn't been covered too much here on Null Byte, I thought why not do some How-tos about it now and then.

Welcome back, my amateur hackers! Over the course of the next year, we will be developing our own zero-day exploits. In my first article in this series, I introduced you to buffer overflows, which are the source of some of the most lethal exploits, particularly the "remote code execution," so we are focusing our exploit development here on a buffer overflow.

Can you tell when your friends are serving up a bunch of BS, or are you constantly oblivious, unsure if they're spinning a valid story? With so many ways to lie and fake information floating around, it can be impossible to tell what's the truth from what's complete BS. Here's how to sort through what you hear and find the real truth.

These days, phone calls aren't always the best way to communicate with others. Maybe you need to reach people out of the country, or you simply want to have a more visual conversation. Either way, there's a reason why video calling has become so popular.

It may seem impossible to win an argument against an irrational person, but it turns out the tried-and-true techniques that hostage negotiators use against hostage-takers work surprisingly well in everyday situations. You may not ever deal with a real hostage situation personally, but life is full of negotiations with unreasonable people, and those conversations don't always have to end in rage or disappointment. The mental techniques that professional hostage negotiators use can help both pa...

Welcome back, my hacker apprentices! Although there is a multitude of different hacker types, the one target they all share is the database. I often refer to the database as the hacker's Holy Grail, or the ultimate prize for an effective hack.

Welcome back, my hacker apprentices! In recent weeks, the revelation that the NSA has been spying on all of us has many people up in arms. I guess I take it all in stride as I just assume that the NSA is spying on all of us—all of the time. Don't get me wrong, I don't condone it, but I know the NSA.

UPDATE (February 26, 2014) Yesterday, the U.S. House of Representatives passed H.R. 1123 with a 295-114 vote decision. The ruling repeals the 2012 Library of Congress (LOC) decision that limited the ability to legally "unlock" your smartphone (see below).