Super Mario Run was released for iOS on December 15, 2016. Even though it debuted as a "free" app, almost all of the playable content was hidden behind a ridiculous $10 unlocking package. Despite coming with such a hefty price tag and receiving a two-star rating on the day of its release for iOS, Android users are still very much interested in giving this game a whirl.

When the "Just another day in the office at Magic Leap" video was released last year, it was called a mind-blowing, stunning, and breathtaking take on mixed reality gaming. It was a great presentation of what the technology could be, but not for a second did I think it was anything other than a concept video, and I'm not the only one who thought that. This was a goal to reach for mixed reality, not the reality.

I don't know about you, but visions of pumpkin pie and cornbread stuffing and big, juicy turkeys are constantly dancing through my head right now. I'm sorry, healthy eating habits, but it's Thanksgiving week, and all I can do is think about food.

A new hack has reopened an 8-year-old iPhone security loophole that Apple thought it had fixed back with iPhone OS 2.2. This is not one of those times when a theoretical attack gets identified and blocked quickly by Apple. On the contrary, it's a hack that actually exists right now, and it can have some serious real-world repercussions, so this is something all iPhone users need to be aware of.

God, chili is amazing this time of year. It's hearty, filling, freaking easy to make, and it warms you from the inside out.

When your day sucks, all you want is a tall, ice-cold glass of beer at the end of it all. Nothing complicated about having some booze to temporarily drown your sorrows.

When a craving for crunchy tacos hits, it's undeniable. Don't Miss:

Dried spices and herbs seem to be immortal; a peek in your parents or grandparents' cupboards will likely unveil cinnamon, basil, and oregano older than you.

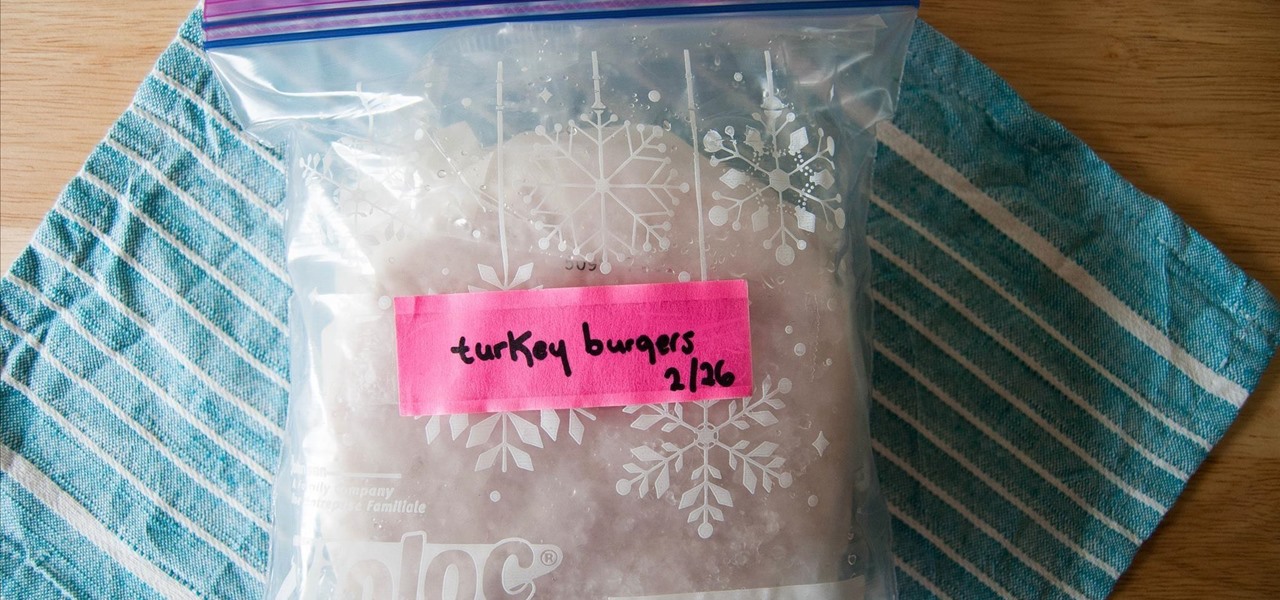
Frozen meat is a saving grace for weeknight meals. Whenever I crave a certain protein, all I need to do is defrost it. Sometimes, I don't even need to defrost it in order to use it.

SentrySafe puts all sorts of measures in place to protect your valuables and important documents. This particular SentrySafe has an electronic lock, four 1-inch bolts to keep the door firmly in place, pry-resistant hinges, and it's able to withstand drops of up to 15 feet. That all sounds great, until you find out that you can open this safe—and pretty much every safe like it—in a matter of seconds using only a magnet. A rare earth magnet, to be precise.

Samsung trademarked the name Gear 360 a few weeks ago, and today it has been confirmed that the Gear 360 is a spherical virtual reality camera that will accompany the much-anticipated Galaxy S7.

When roast chicken is concerned, perfection is hard to attain. The reason for this is surprisingly simple: the light meat and the dark meat should be cooked to different temperatures. Ideally, chicken legs should be cooked to at least 170°F, while breasts should be cooked to 150°F. Naturally, this poses a conundrum: how can you cook two parts of the chicken to two different temperatures, without taking the bird apart?

Smelly foods are what make my culinary world "go 'round," so to speak. I grew up with fish sauce, learned to cook with and love fermented beans and veggies, and am one of the biggest garlic advocates I know... other than my husband, who thankfully shares the same smelly food sensibilities. (Let's put it this way: anyone that can stomach stinky tofu can handle anything I could possibly cook up.)

Microsoft's "Fall Update" to Windows 10, code named Threshold 2, has a lot of new tricks up its sleeve. It's the biggest update we've seen since Windows 10 was released this summer, and it's rolling out to all users right now.

Bubble, bubble, toil, and trouble... it's time for another Halloween-themed food hack. This time, we'll be tackling the pumpkin cooler—an idea that has been done to death on DIY blogs around the internet. And there's no point in reposting something that everyone else has done, so I decided to change things up a little bit.

Sadness won over the worried world with her downtrodden, mopey attitude in Inside Out, the widely popular animated film from Pixar and Disney. She's relatable, helping us to connect with all of our bouts of tears, sour attitudes, and blue feelings—and this Halloween, you can embody Sadness with this easy DIY makeup tutorial via Rotoscopers.

Butter is one of the most versatile ingredients in the world: its variety of uses range from brightening a morning piece of toast to finishing a beautiful rib-eye steak with decadent flair.

My French press is one of the most important tools in my kitchen. It's indispensable, and it's no small exaggeration when I say that I use it on a daily basis thanks to my coffee addiction. However, it gets used for a lot more than just my morning cuppa (and my second morning cuppa, and my late morning cuppa, and my... well, you get the picture).

If there's a better way to impress your friends than with cocktails, I don't know what it is. Some nice glasses, quality spirits, and a recipe that doesn't involve pre-made margarita mix, and you'll automatically look suave. However, the most overlooked cocktail accoutrement (and the coolest, in both senses) is the ice.

This decadent dessert is inspired and created by marrying tiramisu and s'mores. It's a moan-worthy version of that classic English dessert, trifle, that combines the soft, creamy layers of tiramisu with the gooey, sticky goodness of s'mores. You can make it as easy as you wish, with store-bought whipped cream and pound cake, or you can make everything from scratch for a special company-ready dessert.

When summer rolls around, I think of two things: grilling and ice-cold beverages. To me, nothing beats loading up the grill with charcoal, letting the smell of smoke get stuck to your clothing, and imbibing the most refreshing drink you can find.

Most primary cocktail ingredients just sound delicious. Lime and tonic water? Yes, please. Bitters and simple syrup? Sign me up. Egg whites and... wait... egg whites? In a cocktail?

Here's a fact that everyone knows: avocados are delicious in guacamole, salads, and sandwiches. Here's a fact that's less commonly known: avocados are delicious in desserts, too.

Welcome back, friends! Many times, businesses, friends, and family will lock their zip files with a password to keep their files secure. It is reasonable, and understandable. Well, thanks to hackers, there are many ways to get past this wall of security.

Like most food lovers, I adore sushi. And like anyone who is a living, breathing human being, I'm a pretty big fan of sriracha sauce.

Every year, when summer rolls around, I get excited because it's grilling season. And every year, when summer comes to a close, I get sad because grilling season is ending.

You can make a pretty strong case for pancakes being the ultimate breakfast food. They taste like a treat for a special occasion, yet they're not bad for you (presuming you don't share my whipped cream and maple syrup habits). They can be customized and accessorized, and they cook up in just a few minutes.

Rather than reaching for aspirin the next time a headache strikes, try grabbing a drink of lemonade instead. Not only can it help ease your head pain, but it can also help relieve stress, anxiety, and depression. But not just any old lemonade will do the trick—reach for the lavender lemonade.

It happens to even the most avid cereal eaters: sooner or later you open a box, unfurl the crinkled plastic bag, and find that the cereal inside is stale. Maybe you forgot about it, maybe you ate it too slowly, or maybe you just found a new, better cereal and left it behind like Andy left Woody. Either way, the crunchy goodness is now stale, and you grab the box and walk to the trash can. Stop!

There are a lot of frustrations when you're dealing with cramped living quarters, but you can do a lot of good cooking in your tiny kitchen if you make the most of your space. These storage hacks will make it easy to cook delicious meals, no matter how limited your square footage.

Samsung included an "SOS" feature for its phones since the Galaxy S6 that could literally be a lifesaver should you ever find yourself in an emergency situation. It's one of those things that we hope to never have to use but will be very thankful for if a need ever arises.

It can be pretty tough to fall asleep when your brain is thinking nonstop or anxiety has gotten the best of you, and it seems to only get harder when you're lying in bed listening to yourself breathe. Yet paying attention to that breathing may be exactly what you need in order to find a calm, easy entry into a good night's rest.

Inspiration for tutorial: Foxtrot's "How to Trap a Tracker"

Hops have always been known as the driving force behind beer, but now they're starting to grow their own culinary wings. Slowly but surely, this bizarre and bitter plant is showing up on more and more menus across the country as it catches on as a trendy and up-and-coming ingredient. What Are Hops?

There are lots of great reasons for going out to a fantastic coffee shop for a cuppa. Coffee shops have a lovely ambiance, are a perfect place to meet with friends or do some work, and are a great excuse to get out of the house. Seeking out a perfect cup of coffee, however, shouldn't be one of the reasons that you hit up your local café.

When you have a parent who cooks—and has you act as sous chef—the kitchen automatically becomes a less intimidating place. In other words, kids who know their way around the kitchen will most likely become adults who cook for themselves, which also means that they'll eat more unprocessed whole foods, save money, and maintain a healthy weight.

Laminate floor planks look beautiful and add elegance to a home. However, if a plank gets damaged, it detracts from the beauty of the flooring. Do you call in a professional and pay tons of money to replace the plank? Thankfully, no. There actually is an easy way to replace a damaged laminate plank if you are ready to spend some time and have a little bit of patience.

Shopping: you either love it or hate it. With a tight budget, shopping can become a huge headache for even the biggest shopaholic. We've all been there, and we've all given in to our impulses and bought something we probably shouldn't have. Yet strolling through the mall doesn't have to require a strong will to keep your credit card from entering a downward spiral. You just need to keep your hands to yourself.

Most of you already know that a zero-day exploit is an exploit that has not yet been revealed to the software vendor or the public. As a result, the vulnerability that enables the exploit hasn't been patched. This means that someone with a zero-day exploit can hack into any system that has that particular configuration or software, giving them free reign to steal information, identities, credit card info, and spy on victims.

We never have a wealth of cheese leftovers in my house since we love the stuff so much, but I'm always happy after a cocktail party if we do, because I know I can turn it quickly and easily into fromage fort. To create this incredible French spread, all you need to add to your cheese scraps is a clove of garlic and some white wine.