John Oliver sunk his teeth into Republican presidential candidate Donald Trump during the long segment on the latest Last Week Tonight. The whole 21-minute video is definitely worth a watch, but the real fun starts around the 18-minute mark.

Now that Chromecast has taken the title of top-selling media streaming device and held onto it for well over a year, game developers absolutely have to take Google's $35 streaming stick seriously. As a result, we're starting to see big-time media and game companies throw their hats into the proverbial Chromecast ring, with new interactive offerings that pair your smartphone and your big screen in spectacular fashion.

Mockingjay - Part 2, the final film in the Hunger Games series, hits theaters next month, and what better way to celebrate one of the series' most fabulous characters than with an over-the-top costume this Halloween?

By eliminating the need for hard keys on phones, manufacturers are able to use that extra space for a larger display, which is clearly evident on the bezel-minimal LG G3. In order to replace the physical home, back, and app switcher keys, we now have stylish soft keys.

In 1999, Robin Williams starred in Bicentennial Man, a movie in which Williams played a robot named Andrew Martin, taking care of a family as a their nanny and personal assistant. For almost 15 years, I have waited for my Andrew Martin, but until now, I have been disappointed. Luckily, Jibo is on the job!

They say that behind every joke is a half-truth. If that adage itself contains a grain of verity, the Daily Show's satirical Glass piece should raise a few eyebrows amongst the Glass Explorer community.

A couple of months ago at the Black Hat security conference, hacker Cody Brocious gave the hotel industry a nasty surprise when he figured out how to hack the locks made by Onity that are used in millions of hotels worldwide.

If you bike a lot and live in a small room or apartment, it can be tough to find the space to store your wheels. There are tons of bicycle racks and mounts you can buy, but where's the fun in that when they're so easy to DIY? Here are some of the best inexpensive solutions for your bike storage woes.

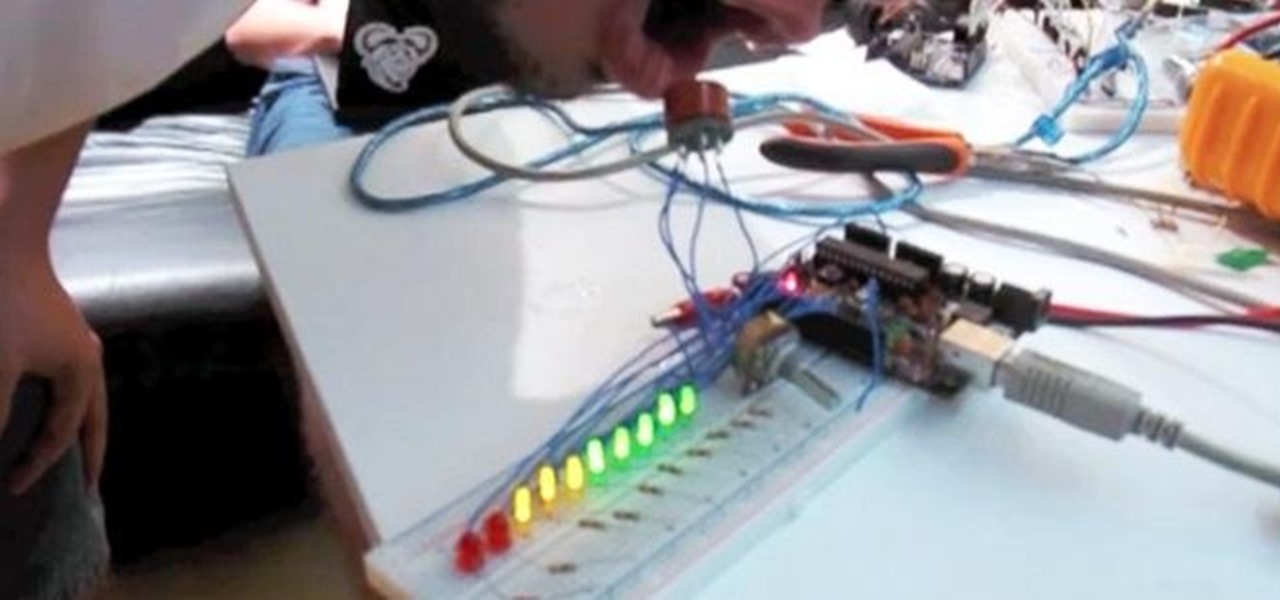
Whether you want to use it to keep your guests safe or just to see who's the most drunk, it's always fun to have your own breathalyzer at a party. We've seen DIY breathalyzers before, like this one by Craig Smith, but how about an Arduino breathalyzer?

Reddit user craigyboy2601 knows a thing or two about airline baggage handlers. After all, he is one. So, when he offers some tips on how to protect your luggage from loss or damage, you should probably pay attention! Here are the highlights from his post.

Some of us use our smartphones for almost everything. Manufacturers know this, so they try to make their devices as convenient as possible to use, but sometimes that convenience comes with a cost to security. The very same technology that allows you to easily share music with friends and make purchases can also put you at risk. Photo by sam_churchill

In this video tutorial, viewers learn how to fold a paper hat. This task is very easy, fast and simple to do. Begin by folding the paper horizontally in half. Then fold it vertically in half. Now open the fold and fold down the top corners to the center to form a triangle top point. Then fold the bottom flap over the edge of the triangle point. Do the same on the other side. Now open the bottom to shape the hat. This video will benefit those viewers who are interested in making origami, and w...

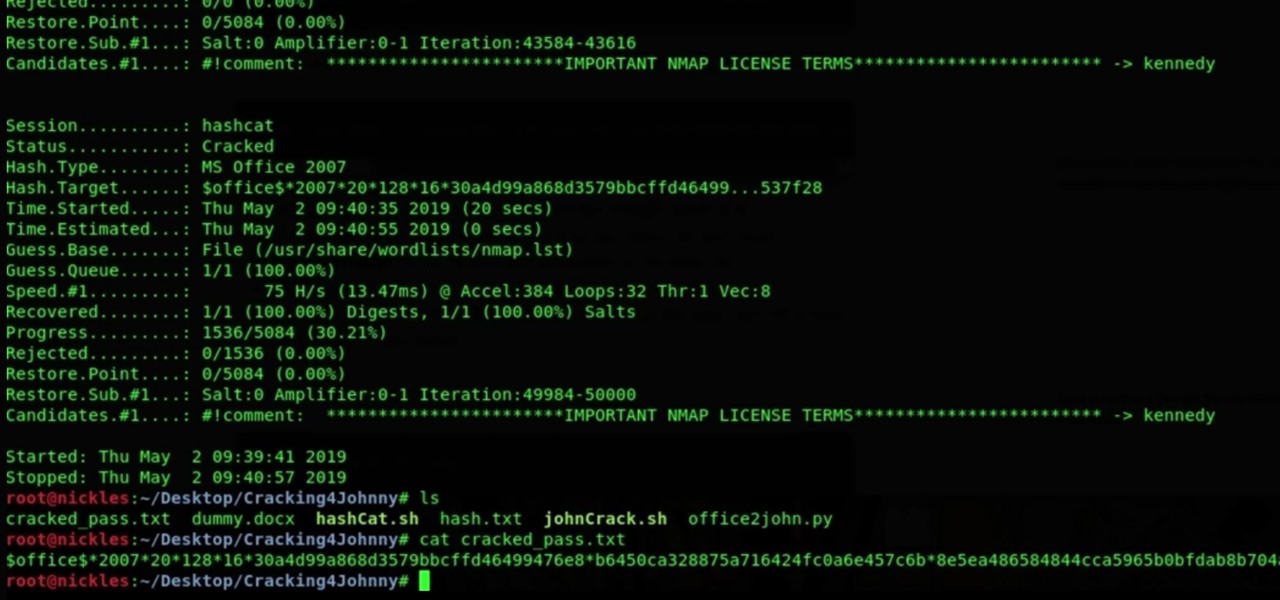
With millions of people working from home as a result of the coronavirus outbreak, hacking is on the rise. Nefarious black hats are taking advantage of the fact that workers have been forced to abandon their secure office networks in favor of home wireless connections. And white hats are spending even more time at home trying to be the next great ethical hacker.

If you've grown bored of day-to-day hacking and need a new toy to experiment with, we've compiled a list of gadgets to help you take password cracking and wireless hacking to the next level. If you're not a white hat or pentester yourself but have one to shop for, whether for a birthday, Christmas present, or other gift-giving reason, these also make great gift ideas.

My first ever post on here was 'Keeping your hacking identity secret' and it did very well, and its not something I see here on null byte. So read along.

This tutorial video will show you how to shave your beard and head for a super stylish look. This beard look is sure to catch the attention of all the ladies.

In this video series, our expert Terry Leafty will teach you about safety equipment including hoods, body protection, sleeves, and welding hats before showing you the different types of welders.

Cybersecurity is an industry that isn't going anywhere. After the mass move to online work, the need for more cybersecurity professionals skyrocketed. That demand isn't going away because more and more industries are keeping online and cloud services going for their workers.

Snapchat popularized personalized stickers for social media and messaging with Bitmoji, followed by walled-garden versions from Apple with Memojis and Samsung with AR Emojis. Even Google has gotten into the game, integrating an emoji generator for Gboard.

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.

Transferring hundreds of screenshots, webcam recordings, keystroke logs, and audio recordings between your VPS and a local Kali machine can be tricky. Services like Dropbox don't always have the best privacy policies and suffer data breaches just like any other website. To mitigate these risks, we'll use a secure, open source, and decentralized alternative.

Something that always brings a tear to my eye is uninspired Instagram stories. When you have a bunch of like-minded friends, you end up with like-minded stories. While it may seem difficult to stand out, stickers were designed so that you can differentiate yourself from other users — and knowing everything there is to know about Instagram stickers will make you a sticker master.

Backdooring a powered-off MacBook is easy when a few minutes of physical access is allowed. That attack works well if the hacker also shares a Wi-Fi network with the victim, but this time, I'll show how to remotely establish a connection to the backdoored MacBook as it moves between different Wi-Fi networks.

No matter what your holiday preference, you're probably aware that Christmas is now just days away. By now, you've already decked your halls with boughs of holly (either physically or virtually), thanks to our last holiday app roundup.

There's no doubt you've heard the old saying, "When life gives you lemons, make lemonade." The phrase was penned in an obituary to a dwarf actor in 1915 by an anarchist named Elbert Hubbard, who lost his life five months later aboard the RMS Lusitania when it was torpedoed by a German submarine.

Hello partners, first of all I would like to thank all those who have sent me positive feedback about my posts, to say that I'm always willing to learn and teach. I'm also open to answer the appropriate questions.

to stay secure, you dont just need Tor, and a VPN. You need good browsing habits. What are Browsing Habits You Ask?
Mostly all hackers like to have a laugh. We like to have fun! We like to troll. And maybe, even cause some havoc once in a while. But, while we do this, we must always stay in the line of the law.

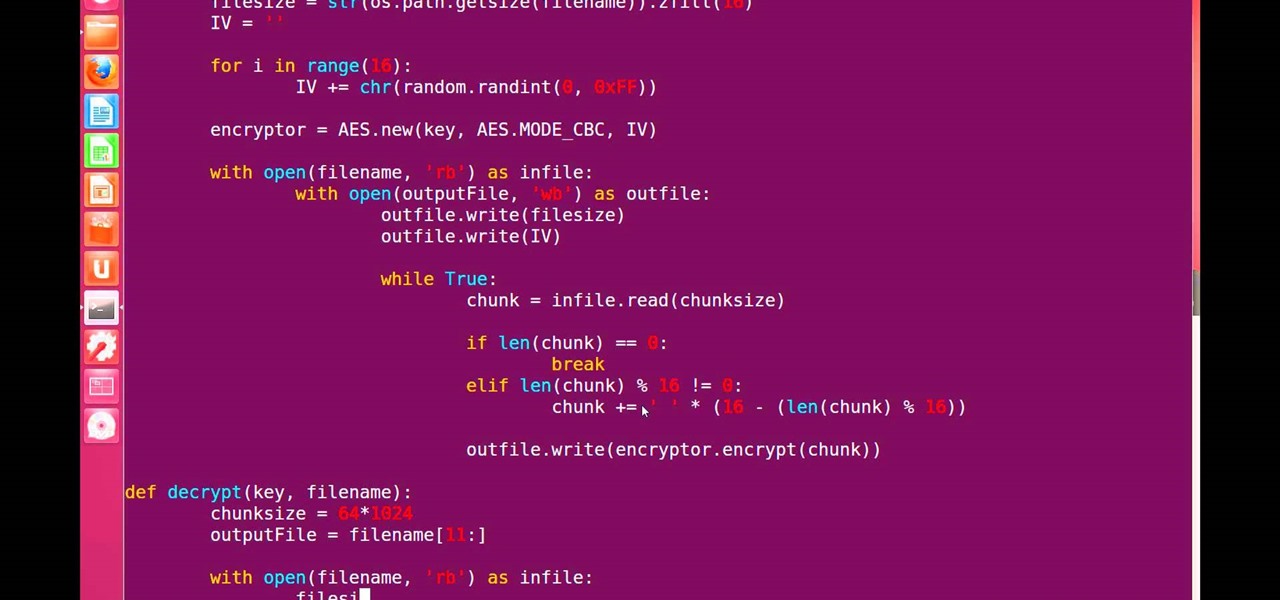
Hello, fellow grey hat hackers and aspiring coders. I'm back again with another python tutorial. Just that this one is gonna be a lot cooler ;-). We gonna make an encryption program, that well you know encrypts all the files on your pendrive or hdd or whatever you want....Also lots of thanks to DrapsTV. They have helped me a lot with Python and making awesome programs. The video is here:

There's only three weeks left until the spookiest holiday of the year, which means stores and costume shops everywhere are bringing out their Halloween inventory full force. So now's a good time to start prepping your Halloween costume—because you really don't want to do it last-minute again, do you?

Enter the game and select Stage 1. Click on the rock above you to make a snake come out. Click on the cactus and drop it on the snake to make a hat. Stage 2: Click and drag the trash to the right and click on the lamp. Click on the taxi that will appear to pass Stage 2. Stage 3: Click and drag the brick to the glass above to break it, open the door, and turn on the lamp. Grab the antenna and put it in the black hole on the edge of the building. Stage 4: Click on the boat and then click on you...

Folding paper into shapes is fun. Folding paper into a toy that you an actually use is even better! Making a paper boat is not only a great rainy day activity but works just as well on a beautiful summer's day.

This video shows you how to turn a 5" crochet headband into a beanie hat. #1 Gather your supplies-embroidery floss, 5 1/2" crochet headband, needle and scissors.

Ever a hacker can have their own business that goes beyond cashing in on profitable bug bounties. With the right skill set and certifications, an ethical hacker could build a cybersecurity firm, become a penetration testing for hire, or even just consult on preventive measures to defend against black hats. But learning how to start and grow a business is rarely easy.

It's nearly impossible not to be at least somewhat familiar with Microsoft Excel. While it's needed for many office jobs and data analysis fields, hackers could also benefit from improving their spreadsheet skills. Many white hats already know some of the essential Excel hacks, such as cracking password-protected spreadsheets, but there's so much more to know from an attack standpoint.

Few things are more important than being well-versed in data analytics and interpretation when it comes to succeeding in today's increasingly data-driven world. As a data scientist, these skills are the key to a high-paying career. For hackers, there's no better way to defeat the enemy than to become the enemy.

Whether you're looking to add a substantial coding foundation to your hacking skill set or want to get a job in programming and development, knowing one or two programming languages just isn't going to cut it.

Unless you've been totally off the grid, there's a good chance you're aware that the Disney Plus streaming video service launched this week. And, if you're on this site, you're likely salivating over the new Star Wars series, The Mandalorian.

For Snapchat users wondering if that selfie is ready to send to their crush, independent Lens Studio creator Andrew Mendez created a handy tool called the Smile Rater.

The perfect promotion for Pokémon: Detective Pikachu has finally come to fruition as Niantic has added some movie-related perks to Pokémon GO.