How to easily fix the missing tags in your MP3 collection using free software called Fixtunes. The tags on an MP3 file identify things like the Song Title, Recording Artist, Album Name, Genre, Track Number, etc. When you buy songs from places like the iTunes Music Store or MP3.com these tags are complete. Some of the songs in your iTunes library may have incomplete tags. This is how you fix them.

"An older gentleman told me the other day "no one makes any records anymore!" Well, I thought to myself; "millions of people make records every week, just not on vinyl or tape like in the old days..."

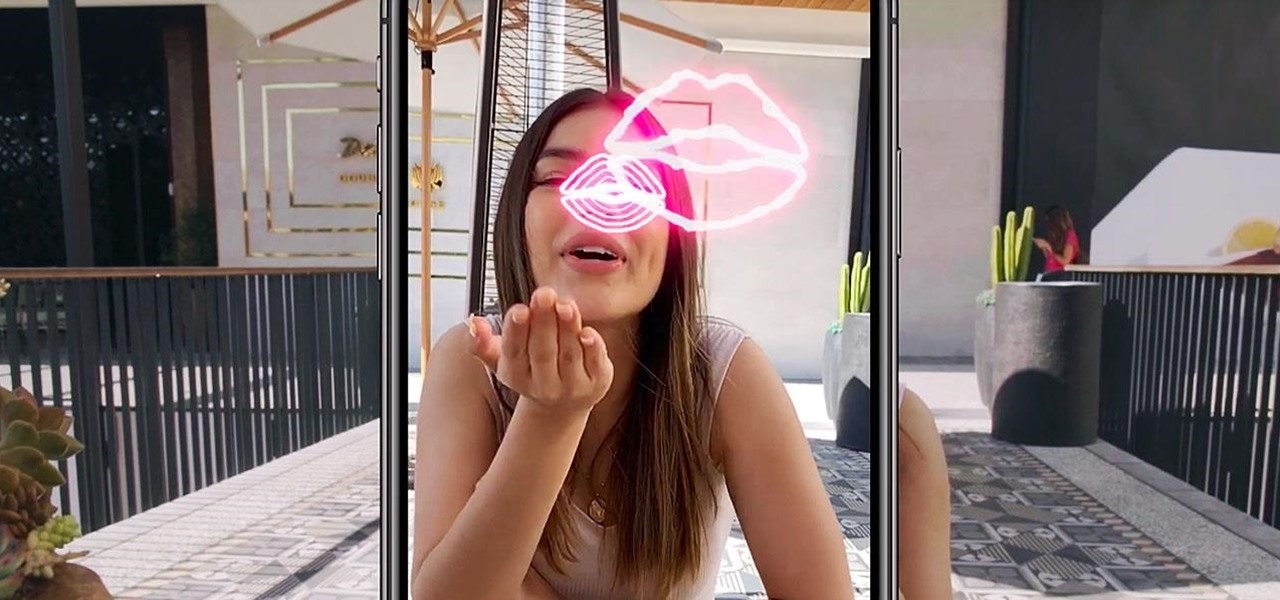
Ever since Snapchat rebuffed its acquisition attempts, Facebook has morphed Instagram with features from Snapchat, such as stories, chat, and, of course, augmented reality.

Apple released the newest update for iPhone, iOS 14.5.1, today, Monday, May 3. The update (build number 18E212) is the first since iOS 14.5, which Apple made available one week earlier on Monday, April 26.

If you've ever wanted to track down the source of a Wi-Fi transmission, doing so can be relatively easy with the right equipment.
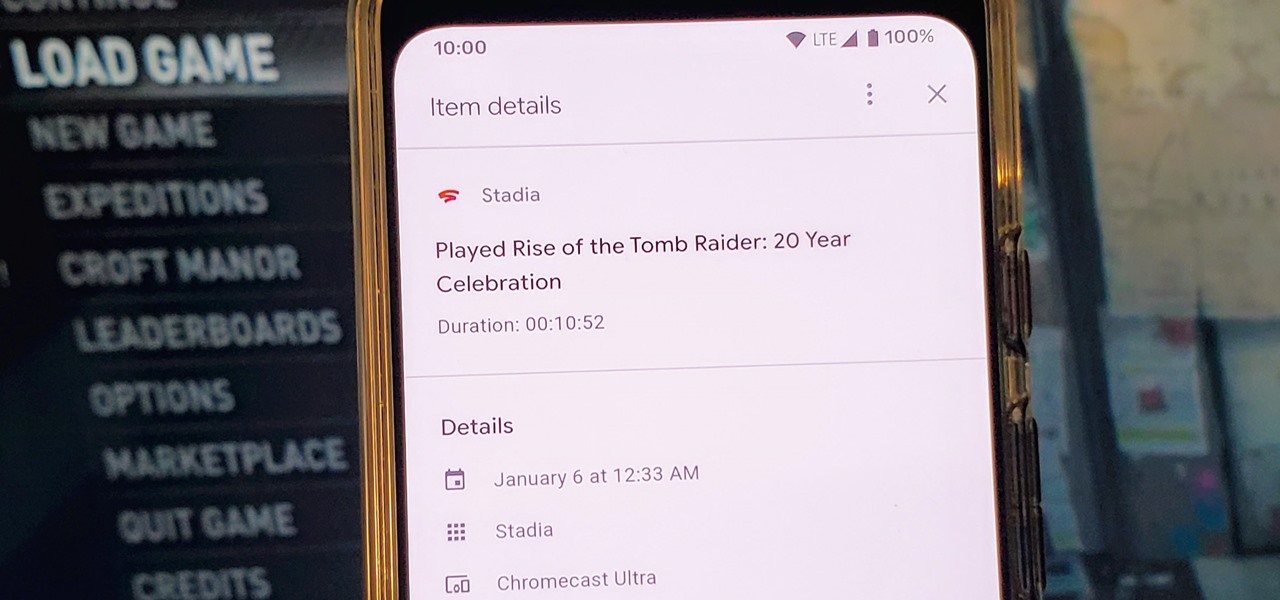
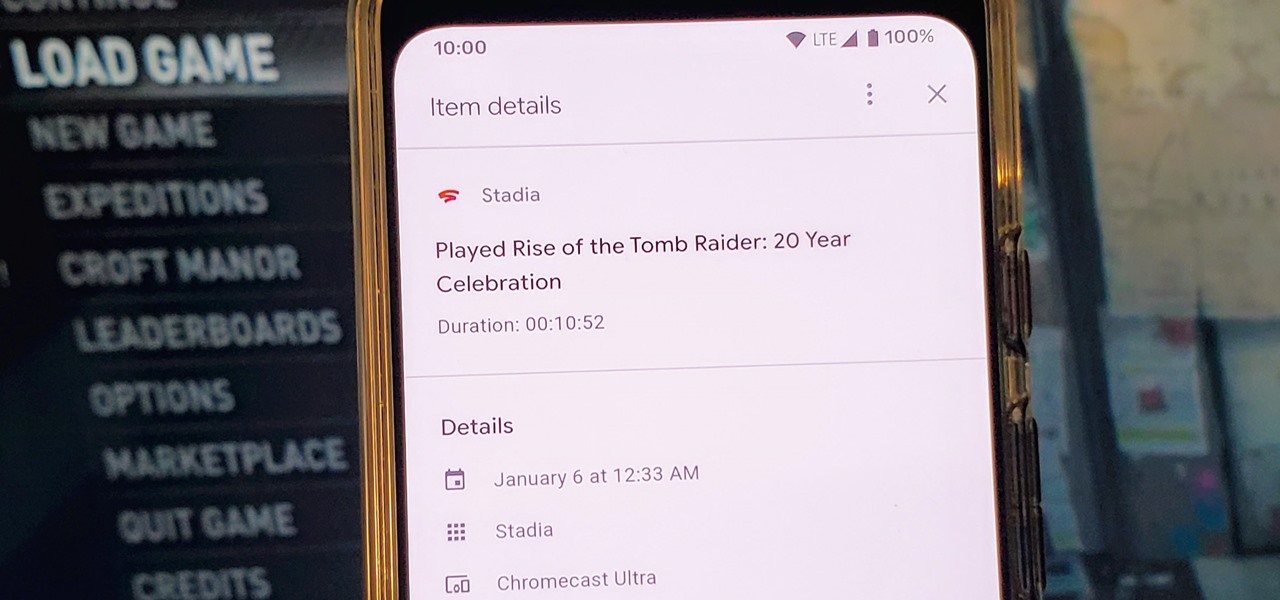
Since Stadia is an early access game streaming platform, Google is still working on bringing big things to the table. You can expect wireless Stadia controller support for many more devices, high-quality 4K gaming on all Chrome web browsers, and more Google Assistant features. They also managed to silently sneak in a way to keep track of your Stadia gaming sessions too, which is pretty handy.

Following its dominance as a provider of silicon for smartphones, Qualcomm is eager to replicate that ubiquity with not only processors for augmented reality headsets but also reference designs to give device makers a head start.

Legendary drum-and-bass artist Squarepusher, the Warp records labelmate of fellow electronic music legend Aphex Twin, is back with his fifteenth album called Be Up a Hello, which is set to drop on Feb. 1.

Brace yourselves: Nreal Light clones are coming. Since the China-based startup wowed the crowd at CES 2019 with its consumer-centric smartglasses, a number of followers from Asia have emerged, and all with very similar aesthetics to Nreal Light.

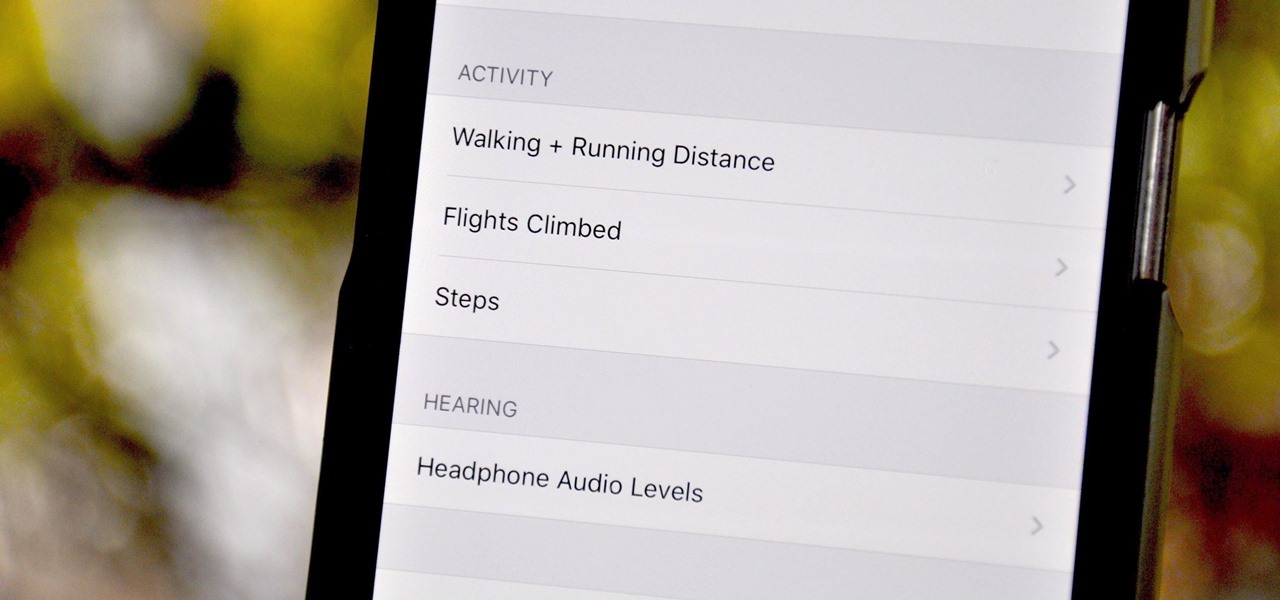
Your iPhone tracks how many steps you take, how far you walk, and how many stairs you climb each day. That may seem a bit frightening, but it's all for a good reason: the Health app stores this data so you can view your progress in one place. But interestingly, opening the Health app isn't the easiest way to view this info.

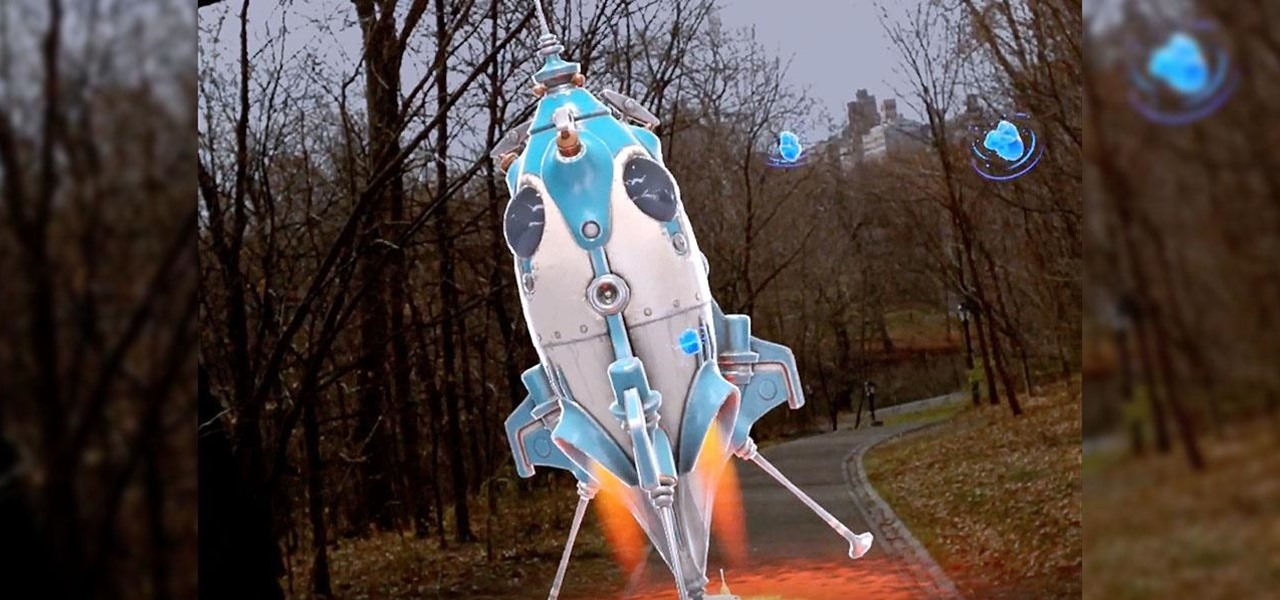
We're a few weeks away from the fireworks associated with New Year's celebrations, but that doesn't mean you can't start a little early — in augmented reality.

The longest-running children's television show in the United States, Sesame Street, hasn't survived 50 years without leveraging new technology along the way.

Facebook and its Oculus subsidiary have been open about their intentions to bring AR wearables into the mainstream for some time now.

While Magic Leap has remained mostly silent regarding its plans for its Magic Leap One successor, the software team continues to makes strides with improvements to the device's Lumin OS and SDK.

When it comes to web-based augmented reality, 8th Wall has emerged as one of the leading platform providers, and the company just cranked up its capabilities another notch for AR marketers.

The first annual Snap Partner Summit kicked off on Thursday in Los Angeles, and with it came some new products announcements, several of which enhance Snapchat's already robust augmented reality powers.

The great thing about augmented reality is that so much is possible using the emerging tools and software, your only real limit is your imagination — that includes making real versions of imagined products.

Canary tokens are customizable tracking links useful for learning about who is clicking on a link and where it's being shared. Thanks to the way many apps fetch a URL preview for links shared in private chats, canary tokens can even phone home when someone checks a private chat without clicking the link. Canary tokens come in several useful types and can be used even through URL shorteners.

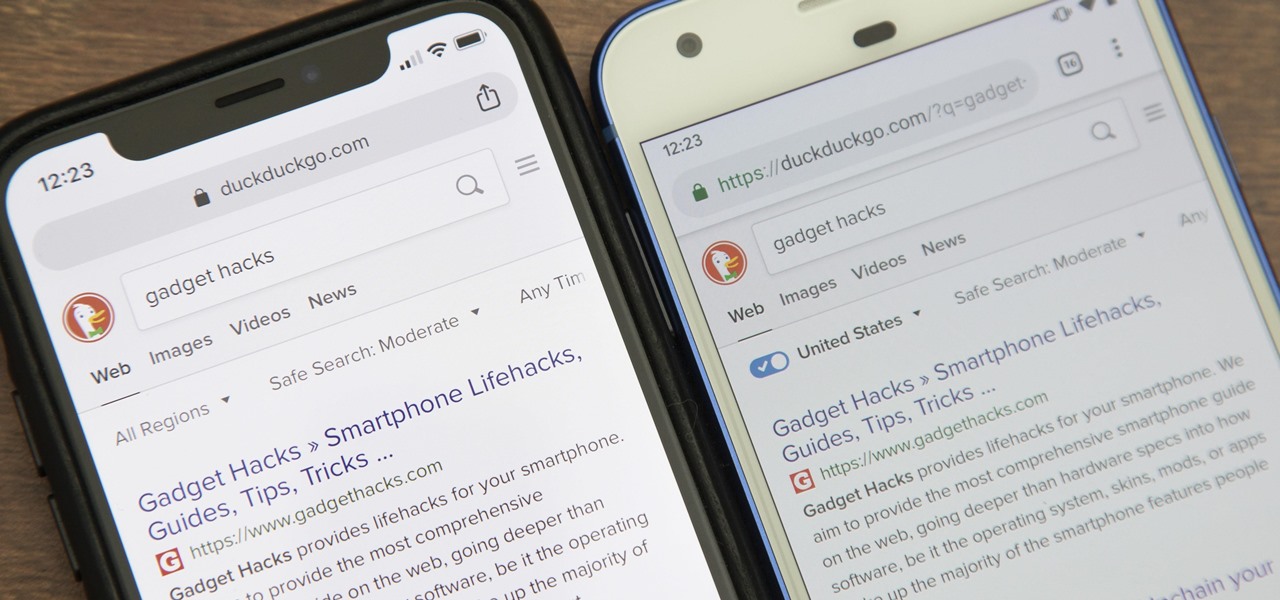
While Google would rather you use Google as the default search engine in Chrome, there's a way to switch to the more privacy-geared DuckDuckGo search engine for all your web browsing needs. With DuckDuckGo, the company does not track anything you search or allow anyone else to track it, so you can effectively search from your iPhone or Android phone anonymously.

Snapchat made augmented reality selfie effects famous, with Facebook copying the feature across its mobile apps. Of course, others have followed, but their face tracking apps often pale in comparison to the original.

The quality and length of your sleep will almost always dictate how the rest of your day unfolds. Sleeping fewer hours increases your chances of spending the day in a tired and cranky state, while having a restful night's sleep contributes greatly to being alert and productive. Luckily, if you want to track your sleep patterns to figure out how you can improve your circadian rhythm, Samsung Health has you covered.

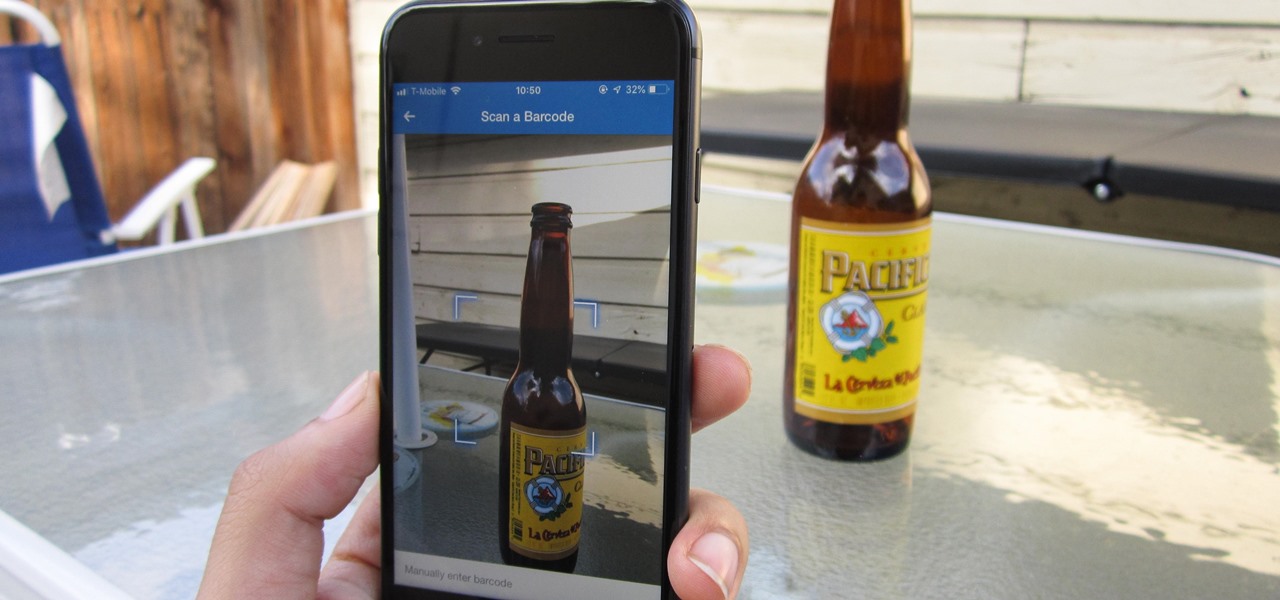
In MyFitnessPal, you can search through a food database to add your meal into the app's diary and track your calories. Unfortunately, the sheer size of the database can make it hard to find exactly what you have just consumed, which is why MFP includes a barcode feature to make the process of adding food much smoother.

Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

French cosmetics giant L'Oréal isn't wasting any time putting its new subsidiary, ModiFace, to work. On Thursday, the company launched a new tool that enables a photo-realistic augmented reality simulation of nail polish shades and textures to be accurately displayed on a user's fingers in real time.

In recent years, Apple has assembled its augmented reality team and supply chain through a series of acquisitions, high-profile hires, and strategic investments, but at least one potentially major deal was recently ditched.

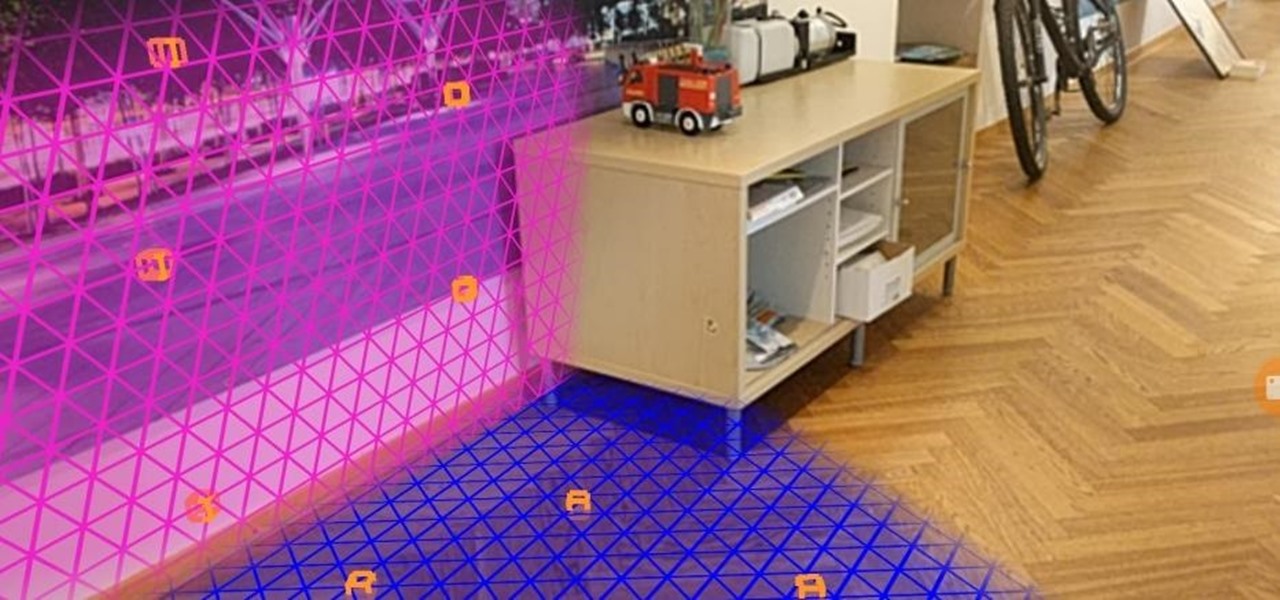
In the latest update to its augmented reality platform, Wikitude has introduced new plane detection capabilities that can anchor virtual content to surfaces at any orientation.

The fortunes of ARKit and ARCore are still in the hands of developers, who have been increasing the number of mobile augmented reality apps on the market, but perhaps not as fast as companies like Apple might have expected. But one new product is looking to literally kickstart mobile AR gaming by introducing a few key components that harness the traditional board game model.

Wi-Fi devices are continually emitting "probe frames," calling out for nearby Wi-Fi networks to connect to. Beyond being a privacy risk, probe frames can also be used to track or take over the data connection of nearby devices. We'll explain how to see nearby devices emitting probe frames using Probequest and what can be done with this information.

Less than two months since unveiling Project North Star, Leap Motion has released the reference design that will allow developers, makers, and even manufacturers to build their own augmented reality headsets based on Leap Motion's work.

It is often said that the best hackers remain unknown, and the greatest attacks are left undiscovered, but it's hard for an up-and-coming penetration tester or white hat to learn anything unless one of those factors is actually known or discovered. But the end goal here in our SQL injection lessons is to make that statement as true as possible for us when performing our hacks.

A newly-filed patent application from Disney Enterprises, Inc. teases more augmented reality lightsaber duels, either for at-home gaming or for the media behemoth's forthcoming Star Wars theme park.

Kitten Planet, a spin-off company that grew up in Samsung's C-Lab incubator, has developed a connected toothbrush that teaches and motivates children to brush their teeth better via augmented reality while tracking their performance.

At its F8 developers conference on Tuesday, Facebook announced new tools and features coming in a new version of AR Studio, including the integration of 3D content aggregator Sketchfab's Download API.

If it had come out just a week earlier, around April 1, no one would have believed it. But it's true, Leap Motion has developed its own prototype augmented reality headset, and it looks pretty wild.

The once blurry and mysterious vision of Magic Leap's future is slowly coming into focus in the present, despite the company's obsessive attempts to keep any and all information under wraps until the next reveal is absolutely necessary. A new tidbit of information hints at an addition to the company's unfolding story that almost no one had accounted for: retail stores.

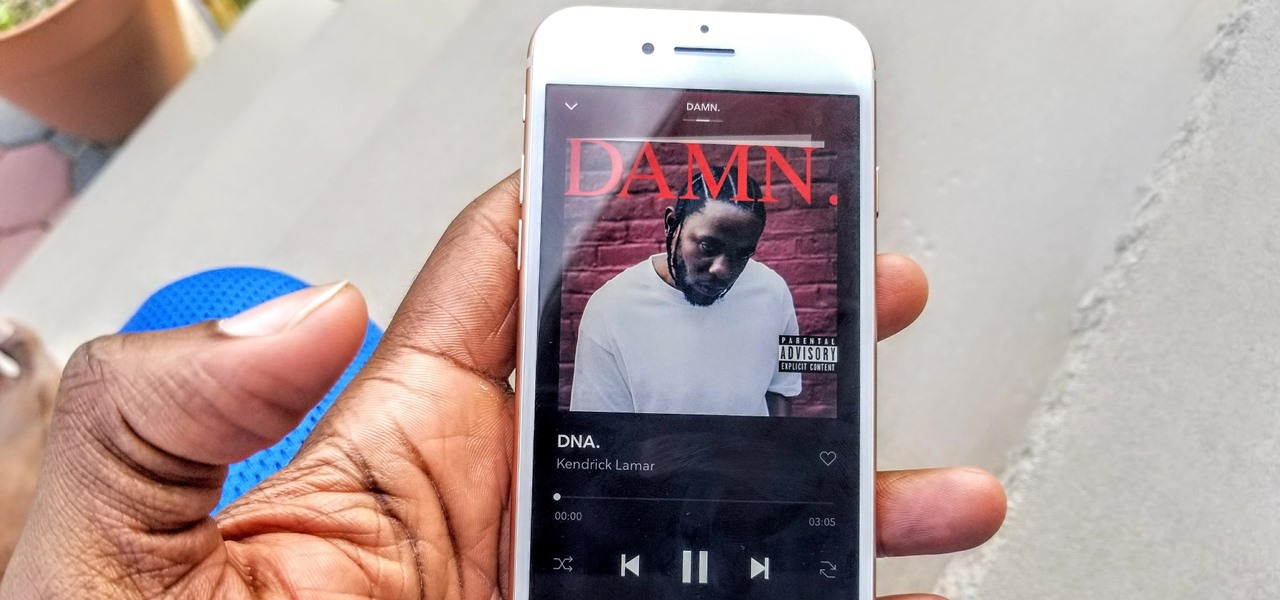
Jay-Z's Tidal streaming service provides Hi-Fi music to a mainstream audience. Even better, Tidal can do this without blowing out your eardrums, because it's easy to enable volume normalization so that one track isn't louder than the next.

During Google Developer Days, taking place now at the ICE Congress Center in Krakow, Poland, an introductory session on ARCore provides some insights on how the platform operates.

With Apple ready to unleash ARKit to millions of iPhones and iPads and ARCore on its way to supporting millions of Android devices, is there room in the world for a cross-platform mobile AR platform?

When Disney teased an augmented reality game called Star Wars: Jedi Challenges running on a headset from Lenovo, fans had more questions than Disney had answers. When? How much? Can I be a real Jedi?

The new battlefield AR game announced by Skyrocket Toys today is similar to the childhood game "Tag", except the stakes are much, much higher.